Hacking Acorn Machines: Security in 1980s–90s Educational Computing
Show original YouTube description
Show transcript [en]
this is a talk about hacking acorn machines or the bad old days or my misspent youth and is all about what I got upped a teenager so first of all what do I mean by hacking there are two schools of thought on whether the versus crack no debate which I am absolutely not going to get into it but given that this is a security conference there will be supplies so does anyone remember these guys if you did not grow up in the UK in the edges of 90s you may not have run into these but these would be BC micros they were in primary schools to help the land and a lot of people cut
their teeth from them as an introduction to computers and ACON where they come word that competed made the BBC micro but they were also plan is the field of networking and they had a thing called a kinetic Annette I am not sure if I think given that sir this was one of their promotional materials that they were probably going for the Eco part the low-cost but in my world it has always been a cadet so I do not know what they were playing with this from the early 80s they were playing they were developing this in like 1980 1981 before even the BBC micro existed you'll note that these little schematic machines at the bottom were not in fact BBC might
hood micros they were acorn atoms which was the predecessor to the BBC micro so change we're doing networking before people knew what networking was and because they were big in education a lot of schools also had networks of these machines and I got to play with them and doing this this is how they did networking in the 80s these are a bunch of what are called immediate packets which you could send from one station to another and it would do anything and if you look this command list you will think this doesn't look like the command list for any Network protocol you know this looks more like the command list for a debugger you shall peek and poke
pipes on a remote machine that's jsr you see there is jump to cebu T so you can execute arbitrary code by poking bytes into your machine your target and stopping it also has pathologies for stopping the sting of stepping and so on which I'm sure was incredibly useful when they were developing all of this but arguably has no place in a classroom full of girls but it was fun they had things they had built-in facilities that allowed you to take remote control of another computer hips keyboard can be locked out and your keyboard will send input to it and you'd get to see the speed that it produced and the way that they did this is they did not have the
wrong space to implement any of this on the Machinists themselves instead they use this remote code execution to send over code and have it running on the remote machine and the only way that you were expected to keep your classroom chaos free is by declining to host the utilities that did this on the shared network wowza he pulled networks work that the concept that you would introduce things from outside either I mean machines did not have disk drives the entire point of having a network is that you did not need a describe her machine of death drives were expensive so you basically had one single shared file store and if the utilities to do all of the fun stuff were not available
on it then you were basically out of luck unless you were to do things like tell your woman all to class and uh float things from tech but this is just a sign now I am NOT going to talk about a kinetically the big because it is before my time I did get to play with it a little bit but this is just an indication to set the scene this is what they were doing in ages this is what they were doing in the 90s they had moved on from the 8-bit machines as you may know acorn were different the ARM architecture and this was the risk PC introduced in 1984 which was a 32-bit machine wearing a comm 610
which was on the we know on before and these things to really have to fight megabytes of RAM and a couple hundred makes a hard disk and when I was boarding school I returned from summer break in 1994 defines that we had acquired a room full of ten of them and I thought they were better than bread be is sliced or otherwise and I had a whole lot of fun with them over the years and I am going to show you so first of all these things were networked they a cause the original econet Oreca net was basically a glorified serial link they had moved on from this by then they had seed that direction that industry
was headed and everything was now running over boxed under 10base2 at the link layer at this flew a layer they were still using the ethernet vertical tunnels over UDP I believe well certainly they did have a plumbing over UDP they may also have Hadley tooling or overbought Ethernet I don't know I actually understand that layer at the time so instead I'm going to talk about some of the highlights such cuz the file server so first things first this is a quote from the level 4 file server managers died which was the software that's beautiful plan to provide a file store or users well we disapp it says to prevent unauthorized people tampering with information stored on the file
server keep the file server stationed in a locked room even if you run the file server on the station without the keyboard in mind it it's a sensible to take this precaution to prevent anyone attaching a keyboard or monitor and so gaining access to files did they do this no they did not have these had computers as I mentioned they were all in the same room they all had keyboards the monitors in fact a court did not even sell service so the file server had more memories and all of the others it had more discs the others all of which were useful it all sounded larger monitor after meals which was entirely unused because they just sat that because if
you used it this course was a cooperative multitasking system so if you decided that you wanted to use the file server for something more mild serving would stop while you were doing something else so the file server was off-limits but I should mention this is a boarding school I was at it was possible to get in after yes so I got to claim that the file server and when you load up the file server you can get to all of people's files but you can also get to all the people's accounts as there is an application or manager that lets you manage the it capsule there is what it looks like and you will notice there
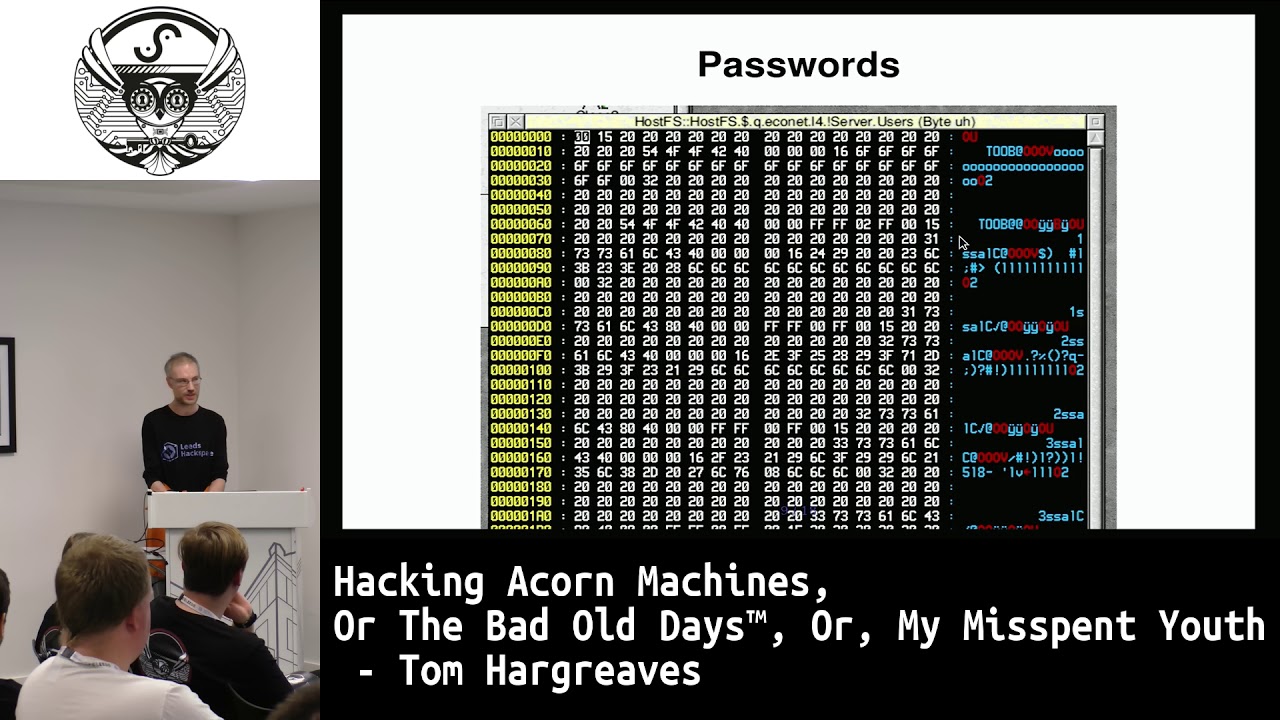
that the password is displayed as a whole bunch of dashes I guess they didn't like asterisks but it turns out they were actually storing plus they were actually not cashier passwords they had to be plain text passwords available and they were lying on the GUI to rip splice the characters in the password with dashes so approximately two minutes with a window editor says it'll do this snow that is all that one good and I promptly brought a list of people's passwords suit two minutes for the two minutes with a window editor to get at I decided that I wanted to be able to get the passwords off without actually having access to the machine because you
know people will change the passwords and it's possible that I will not get the machine again so that will say facility for sharing a drive read-only so I went back to all of the machines in the room and got them to share their entire hard drives over the network including the file servers unfortunately this manager program would not run over the network it needed to be run on the file server which means that if I were to get the passwords out I would have to crack the password I suppose I was like this those of you who follow me on Twitter and there are here to be a few more of you than there were a few weeks
ago as a result of this talk which is good because I haven't had you posted it on too ages except this which I posted yesterday I don't know I had a chance to look at but if you did then enough you will have a head start on what I'm about to say this is the password file font a level 4 file server and you will see that it has some user names that are backwards and it has a whole bunch of other rubbish in what do you do with such ethic it's turns out they are using encryption what encryption are they using they are using XOR with a constant bite I should point out this was 1995 UNIX crypt have
been around for 20 years why exactly did they do it this way I have no freaking idea acorn was notorious for living in their own little world not taking notice of where the rest of the industry was headed but is also work worth pointing out that acorn actually sold UNIX workstations they had themselves portage or quickly BSD to the ARM architecture so it is not like they didn't know how to do this they just didn't care clearly they didn't care about defense-in-depth they assume that if you're learning a file server you will keep it laptop but I have not looked into this but I would bet good money the passwords are transmitted in plaintext or some equally
for real encryption over the network
so that was before FAFSA or have we got next this is FS lock this is what they did to ensure that all of the client computers remain usable and that people did not look up I'm on this prevented people from writing to the hard-disk except for a single public directory where people would store files and promptly have them deleted by the next person that came along it was being mischievous so if I actually wanted to stop things and as a 15 year old by and large the thing that I was interested in his playing games and not having been deleted by the administration so I wanted somewhere to store stuff out of public scrutiny but I couldn't write to
the hard-disk also if did it prevented access to the NVRAM or CMOS ROM in a conference so you could not recall bigger than machine in any way which again was annoying so it turns out that there was a utility that will ship with RISC OS which was a block happy that we are not doing on that first we are doing method is first the acorn worth had a big presence in the UK that had ambitions of selling overseas which meant that all user built visible strings needed to be translatable so they have a messages file that you could edit that would allow the translations elsewhere so this is a copy of FS locks messages file and it shows the strings
at the top you can see on the path to there is dollar dot public hwah scoffs used dots as have separators and dollar means route directly so this was the top directive the hard disk and paste some dirt on public and it looked at this message to find out what the translated name of public was Haley your particular look off now I should point out the FS what was involved and so you couldn't just go up short but it had four visions to make sure that you did not copy it to RAM and run it now but the messages file did not so what you could do is take the original UK messages file viv place the
string and dollar public with dollar dot remove the public and suddenly it thinks the entire hard drive is the drive that you can is that directory that you can now write so this is how you dirt that is a very small amount of code it finds the first of all they're copies the messages file to run it pulls out the location of the messages file it changes one single byte which that number ten is ASCII new line so it puts a new line in place of the heat of public so you now have the string dollar dot and it reinitialize a--'s the messages and that workflow thing other than the fact that it took approximately three you look at
that because you have to copy the entire messages mm-hmm this was on a machine with like five megabytes typically and I thought that was it's a little bit so I went looking for other approaches and the other approach a second approach I came up with was long patch it turns out that there is a file shipped with discussed that fixes of all of the there had actual math ones at this point they weren't flash or Yvonne's they were actual math ones and the lead timer must ones is large so by the time the OS ships they had found a whole bunch of books into ROM and they needed to fix the lobster and this is how they
did it I have no idea how it works I had no idea that's fine I had no documentation to speak of I basically was figuring this out with a disassembler a hex editor and a copy of basic well it's not too hard to figure out what is going on and what is going on is this you have to three fields you have the location you have the before and you have after and they fight that the location contains the contents before and it will change it to after using some magic mhm I'll help me to do the messages I'll hack with using a lot easier most bit also I would need to do a different hack
because now I could patch the S lock module in its entirety I could just make it be killable because normally if you try to kill it it refuses because that would defeat the entire point the business of course except the incredibly version specific doing this way but it turns out that there was an even simpler way I ended up doing which is this see what yes there were two ways to kill her module risk loss and my module think kernel module there was not a big separation between kernel and user space that there was a separation of sorts they had an MMU but they didn't use it much as evidenced by the fact that I
could write a simple basic program to poke into a module have it work without to do anything so what we have have is that what when you've tried to kill a module and into that mess lock is the module that we are trying to kill that is a flag that the operating system sets when it calls the finalization code of the module and if the flag is set it is a promise by the operating system that this is a temporary shutdown I am going to show you down briefly I'm going to move you around I'm going to defragment the heap and I'm going to set you all right back up again this is because there heap was
terrible and they had a command called I'm trying which allowed you to we initialize all the modules move things down and reclaim the memory that you are otherwise losing to fragmentation this turned out to be a terrible idea in fact it was a very terrible that they later turned it in to ignore it later versions but the flag remains so it was possible to be tennis to do video s ly 2 FS lock say I'm going to shoot you down temporarily and never actually follow through on that so FS lock thought it had being killed the OS thought it was still running albeit that it had removed all its hooks from all of the SIS calls
and things and so you ended up with a zombie and it was very otherwise to do anything at all with a zombie interacting with it in any way would almost certainly mock up the machine but that was ok but more to the point this was incredibly portable they would work on any version ever and I think I had a version that was less not and advise that code but this is not it but yes now I have solved the formula I can store them at others mutiny but I wanted more it is what else we got yes I had not heard of the word rootkit at this point but that is approximately what I ended up writing because it turns
out that people actually go looking through directory structures especially if they take up lots of space so what I did was I made a way to hide things so the OS no longer acknowledged their existence and I have a little demo and see - and we'll see what is going on so I'll explain afterwards ok so you see I have a little dirty here which is the multiplication sign in which I store my super secret stuff I bet well if that I'm going to run the yup a special kidney utility now I hope in the directory again and it has vanished and the here is the fun part either to open the character map I'm ready to create a
new directory with a division symbol and hey presto its back but this is not the division I created a do directly with a division symbol but that never happened and now we've got that thing with the multiplication symbol back so what's happened to the division symbol and the way this works is I wanted to do this the source codes in the background by the way again there is very very little of it this hooked the operating systems redirect the entry Cisco which is read in Linux powers but it turned out the list is sorted its directory entries alphabetically so when you called reader or its equivalent you would get back a sorted list so if you
pick something near the end of the route map I initially picked a ski to 5/5 which I'll check which I later changed for reasons I will tell you shortly then the idea is you walk through the list to see if the thing at the end is your special file name and if it is you simply subtract one from the number the availeth so that saves you actually having to do any modification of the directory entries themselves you can't just change the length field which was really nice and made the code very small but it turned out this acorn did actual local aware string comparison and so I don't know if anyone knows that 255 in
Latin one is a wire with an umlaut over it which was sorted along with the wise and so Zed came after that so I picked something else that was further up that was not an alphabetical symbol that would not be confused and I ended up with us not ASCII Latin 1 2 - 1 5 which is the motivation symbol first I picked up at random turns out there were later ones such as the division symbol nobody ever used any of these in file names so it was perfectly safe but it turned out is really useful to the debugging because if you're trying to debug something like this when it's working you can't actually see the thing so that
made life easier to debug so I now had a way of storing small of my stuff album of scrutiny and this was one on boot-up but I wanted more so I do not suddenly have code for this still but I was able to I have basically zero documentation on any of this but I was I had a list of API calls for a canet and after much experimentation I figured out a way to send a point just one bite but that was all you needed and I ended up implementing what was approximately a the mote shop so you could have a test window open on a remote machine that would not appear in the process lift and
you could send right to his and get rights back from it and the latency was terrible it was about a new milliseconds especially if you had lots of output command this did not have any kind tcp was just a glimmer in people's eye at this point so if the network was congested if there was packet we are doing if packets were lost then your session would behave strangely but that was all okay and I was basically able to run commands on a machine room which was all well and good because by enlarge I is not trying to be malicious until other people got hold of the program that lets human commands on other people's machines and
by far the most popular thing that people found it amusing to do to other people's machines was to remotely reboot them which was single command basic it was cysts who thinks a and there were people who did not know any basic other than that one command for this precise reason and someone I think it may have been my friend K I do not know I don't think it was me ended up distributing a version of this that looked as though it was sending commands to a remote machine but in fact executed the commands on your local machine which put out to that so yeah what else we got that is what life was like it was very different for my
security perspective it was clear the acorns priorities were making work and make it robust and make it user friendly and maybe possibly make it secure as very much an afterthought and I would like to offer a lifetime supply of aspirin for all of the headaches that I caused the administrator of the computer who is dr. who attack and yeah how long we got okay okay I'm gonna call it that does anyone have anything to ask if this was about 95 96 so between 95 to 98 I had over okay Northcote I saw this sort come to I showed you this off a two and a half inch hard drive to an average IDE hard drive that I had on my own acorn machine
that I had a get sooner half inch to three and a half inch cable that I was able to transfer it onto an IDE machine in about 2001 but ironically I lost that or that data to a disk crash later but the original drive in 1996 was still alive and just last week I was able to load it up and pull the entire 720 megabytes of it and that is where the code comes the network screenshots are all from the this software is all available for download stuff so I was able to set it up and in fact I have it running on my laptop because it is very annoying to them this guy's on a laptop
because it needs all the function keys and all of the math boxes so this hidden video for example is something that I created on this machine a couple of days ago does that answer your question [Music] anywhere else
this rule over 500 yes and I was saying before is have got to meet two minutes with a window Maya to reveal the passwords it was approximately half an hour where the hex editor to decode the password format telling the admin his password with Judith priceless turns out it was his wife's name I did not know that could save me a bunch of time lesson here don't have don't use your nearest interests names as passwords [Music] there else [Music]