SMS-based MFA isn't keeping you safe

Show original YouTube description
Show transcript [en]
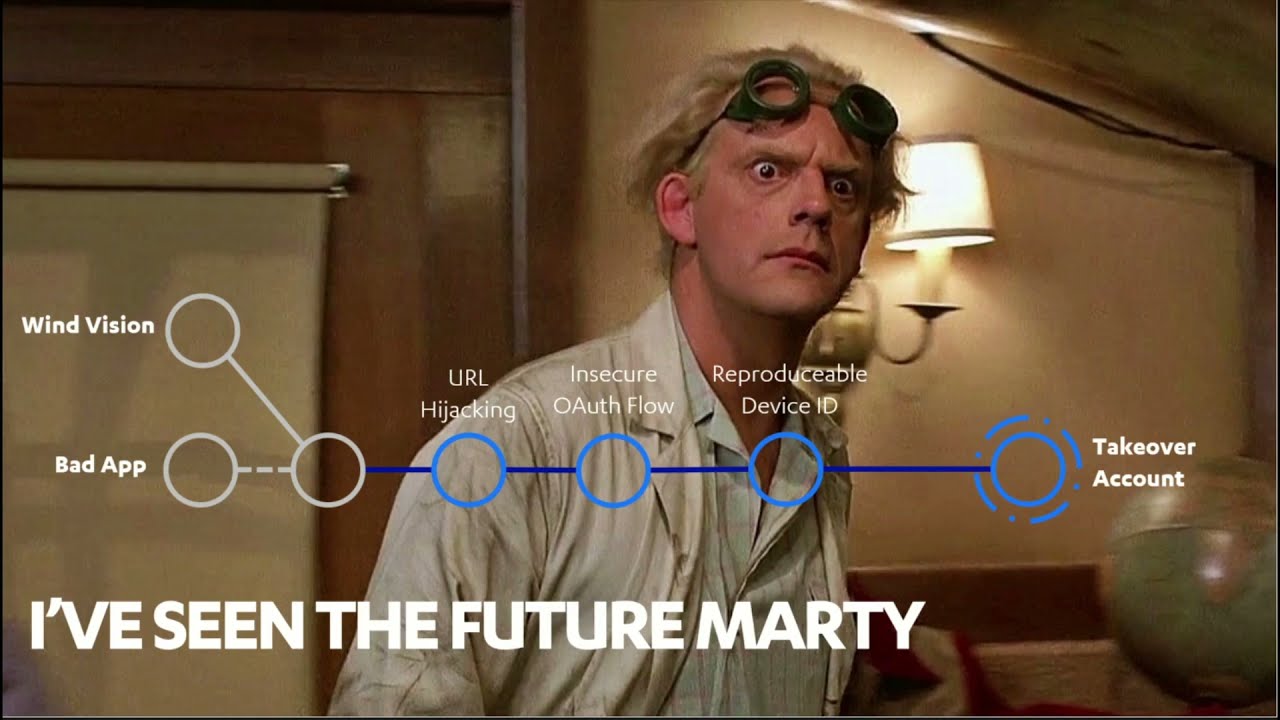
[Music] hi I'm Jonah Boone a super penetration tester at Cyber CX and I hate sms-based MFA okay I'm here to explain why I've been screaming at friends family and colleagues to change their login methods ever since doing this research uh now I'm not here to talk about MFA bypasses which is common enough as an attack path that there are now Labs teaching you how to do it this is about Sim swapping and for anyone that might not know Sim swapping otherwise traditionally known as the poured out scan is the act of taking control of a victim SIM card by convincing a Telco to switch the service for you now why well because for just about every account that most of us own
especially important ones like email there's always a way to recover the account in the event that you've lost the password often via verificationtext.com which means that as a hacker all I need is access to your mobile number and I can comfortably reset your password and let myself into your online life an adversary can also happen to know your password and just need your sim card to complete the sign-in process now this SMS verification is only as secure as the phone or for our purposes the SIM card that receives it um now you may have seen Sim swapping in the news recently uh primarily in the United States as it's still running rampant as an attack Vector this is
solely because it is over time proven to be one of the most effective and easily performable attacks my introduction to sim swapping was many years ago in Minecraft of all places I was a variety of nerds thought it'd be really fun to make my own server and build a community and I quickly learned however that these servers can actually be really profitable as players would pay for in-game perks and role assignments because which 12 year old doesn't want to pay 10 bucks and be an administrator and get their first group on power but what I didn't account for at the time was just how profitable these servers are so much so that it was worth taking out
the competition my server was quickly met with ddos's left right and Center some of the sharper kids in the community would deface websites or other servers I mean keep in mind we're talking about a player base that was anywhere from 12 to 16 years old um but the best of them they would Sim swap the owner's phone reset the password on the server host and then delete all of their files brilliant um and that was then at the age of 14 I moved on to much more important things like discovering girls exist and that the graphics are much better outside um my reintroduction however to sim swapping was Through The Dark Knight Diaries podcast any fans of The Dark
Knight Diaries podcast would have loved there we go uh episode 112 where we heard stories from the younger hacking community and their exploits with synth shopping uh this was nothing like it was when I was doing it I mean when other people were doing it to me um but the Next Generation were going so much further they were kidnapping um and committing arson as if life was just some sort of off-brand gangster movie uh and they were doing this in the name of getting your SMS based multi-factor authentication code okay like why for the average person you'd argue that taking over our online profile is a great hack but it's certainly not worth assaulting cryptocurrency
sweet sweet juicy cryptocurrency um while hacking someone's email and then using that to join their bank account and laundering the money before being caught is possible it is so much easier to find a frat bro talking about crypto on Twitter hunting down their phone number and Sim swapping them in order to steal it now when they started ramping up it became bigger problem quicker than when my first hand a blackjack turned into all-nighters on sportsbet betting on Russian ping pong and someone had to stop it entered the ACM a uh otherwise known as akma which is short for the Australian media and Communications Authority that took a really long time to animate um akma released a determination in
April of this year that would guide telcos and how they validate customer identities now I could sit here and show you about the boring text and make you read subsections and notes and cross-references but I already did that and I'll save you the trouble the key phrase and point of this determination is high risk customer interactions now high risk does not mean high risk in the traditional sense like taking out billions of dollars in loans to buy your favorite social media platform and then running it into the ground or Pi risk like locking out all your clients domain admins because you accidentally sprayed 33 passwords instead of three uh no this represents the high risk is anything
that could result in loss of service or data confidentiality for Telco users and knowing how easy Sim shopping has been traditionally I figured I had to find out how effective the determination was uh my Approach To This research was very similar to the way I handled School tests and pickup lines if I eventually tried enough methods I'll get one right and given the increased difficulty of sim shopping I decided I'm not talking about effective methods for compromising you and I my Approach To This research was uh but the next to the extent that someone might go through to compromise a high value Target such as rich people and politicians and celebrities if you really wanted to what could you
do and I wanted to consider everything from shoulder surfing MFA codes in the streets to plainly stealing mobile phones but I had to make sure that all the hacks I pulled off were repeatable and didn't require direct access to the victim so I settled on the following options promise there's five even though it looks like ten behind door number one was the traditional method of syn shopping otherwise known as the port out scheme now the original method of student shopping was as easy as giving your victims name number and date of birth to the company you wanted to switch their service to and they would handle a rest sometimes that also involved an address and in
very rare cases an account number but for the most of the most part it was very straightforward so to align with the new Acme determination all major telcos have now implemented significantly stricter processes for porting numbers uh as a legitimate customer there are two parts we can take with access to the phone and without now if you do have access to the phone your road reporting your number is beautiful and lovely and quick your new Telco will send you a code they enter this into their own system which unlocks the option for staff to perform the port out uh and you'll leave a very happy camper however if you don't have access to the phone because you either broke it and
the SIM card be on repair or because you've lost it entirely the road to putting a number is terrifying um it involves sending your Telco 100 points of identification or more which is entered into a system for DVS verification it can take up to two or three days given that this could generate unwanted communication of the victim as well as taking far too long I decided to reject traditional Sim shopping as a valid method of attack in 2020. moving on I pivoted to door number two which animated a lot like door number one but canceling the victim service and quickly buying this service out from underneath them this idea only has Merit as the number of telcos will allow you
to cancel your service having only verified your name date of birth and phone number this process can also be completed very very quickly online using their support teams however the idea was shut down quicker than Liz truss's career when I discovered that canceled numbers at all major telcos enter a six-month quarantine process this is to prevent new number holders having to deal with nonsense from previous number holders admittedly the idea was a bit silly but I had to try uh and behind door number three however was my best idea to date this was to request a replacement scene now if I can't Port the number out of the Telco why not just rip it out from
underneath them in theory this is very simple and a test run as follows walk into my friendly local Telco put on a big smile and ask nicely if they'll hand me an activated SIM card over the counter which actually worked uh now you might be wondering okay well that's fine what sort of verification they asked for before you did this um on a few too many occasions at some unnamed telcos none they asked for my name my number and then just handed me an activated SIM card um on one occasion at a different unnamed Telco they visually cited my ID faster than you could say kachow which led me to believe they weren't actually checking anything at all
uh well I I don't know about all of you but contrary to what my ex-girlfriend might think Replacements should not be that easy so what should start be checking I won't pretend that it's the best security measure but I would love if before handing out a replacement Sim they would at least check specific details like the license number and the license card number uh these are fields that necessary might have a little bit more trouble finding but when I asked all major talkers to see my file they never even stored that license information only ever keeping my name date of birth and address uh now in about two hours you'll hear from one of my colleagues Harrison
Mitchell about the about the pitfalls of DNS alongside some of our peers in security research Harrison demonstrated that it's far too easy to forge Service New South Wales licenses despite attempts to obfuscate the code base and protect the application and if you only only ever need to know your victim's name date of birth and occasionally their address ordering a replacement SIM card over the counter is a very strong and repeatable attack path now of course you then have the problem of in-store cameras but you and me for the moment but the attack path itself is functional it's also very important to note here that this exclusively works on telcos with a storefront as the excuse I lost
my sim is met by smaller telcos with send us every identity document you've ever had um but behind on number four I wanted to try something a little bit ridiculous forging a power of attorney alongside a sob story you know that the account holder could not uh get their phone or their incapacitated or something along those lines and seeing it whether a Telco would accept that uh in case anyone doesn't know a power of attorney is a document that gives another person or a collection of people the ability to act on your behalf in all matters Financial legal and sometimes Health in the event that you can no longer make those decisions for yourself now prior to the Optus hack this attack
had some serious Merit because after all it is very easy to create a power attorney document that is legally binding there are two types of these documents there's the registered in the unregistered both of them are legally binding power of attorney documents that in order to interact with some government bodies like the land registry Services the document has to be registered before you can do anything now obviously I wasn't going to actually Forge a legal document in the name of research because I really like my job and I really don't like jail um so I actually went and made one a real power of attorney letter that someone could use in order to either pull my phone number or get a
replacement SIM card but these documents require a recipient and I needed someone I could trust to legally have control over my entire life please let me introduce you to my team leader Abhijit if there's anyone I could trust with the ability to take all eight dollars out of my bank account and send me spiraling to debt it was out of you as an aside I thought it would be quite funny to give Arbor Street the power to hand out gifts on my behalf as well as cover his own living expenses which is a joke the Cyber CX legal counsel did not enjoy um but through other research I spoke to a lot of employees from a variety of
telcos and was informed very plainly that these documents are taken seriously because they're only ever used in times of grieving families or people are really struggling and need to use a power of attorney however this was in the weeks leading up to the Optus app because when we went to test this after the hack Abhijit was ushered out of the store the moment he walked in and told to deal with the advanced supporters how much impact the Optus hack had on that attack path I couldn't tell you there is still significant Merit in uh considering how incredibly easy these documents are to create and the implicate implications I can have on other attacks further on the line but
that's for the next time cyber CX mistakenly gives me a budget for r d before we move on to the last serious option I want to give some honorable mentions to the idea that the ideas that never made the cut namely faking my own death um and using the death certificate to transfer the account now this doesn't work as bereavement processes at telcos offer require a full transfer to another person which means you would have had to compromise someone's identity to do it it's doable but it's very difficult um intercepting a port out SMS message to validate on the spot now this wasn't considered as I have no idea how to do it if you do please come
and find me after the presentation um and the third one is robbing the telcos of their iPads that actually do the software actually do the transfer um now we know it doesn't work to transfer because the process isn't unlocked until after you have your verification code but you could use it to activate a new replacement SIM card this was the method used in the dark net Diaries podcast or anyone that did listen to it I ruled this out for my research as I had no intention of robbing your Telco and I figured if you're willing to Rob one then you're probably willing to Rob other places and make a lot more money um but that's it for the honorable
mentions on to my final method here without further Ado my fifth seemingly valid idea is bribery um while I did rule out the ability for everyday staff to override the putting out process there's absolutely nothing to stop them handing over replacement SIM cards or transferring whole accounts this method has been documented extensively here just as it has for all Industries and it's terribly understandable for an employer making approximately minimum wage to accept a lump sum of money for a momentary lapse of judgment or to suggest they did check the ID documents and when paydays are pulling off the successful Sim swaps are in the millions of dollars giving it a 16 year old Telco employee 20 000 isn't even close to out
of the question so this is all good and well to suggest but forgery and bribery is the best you can do well yeah it kind of is but it's important to note two factors here firstly Atmos determination and definition of high-risk customer interactions is being ignored by all major telcos outside of porting numbers secondly as all Security Consultants can test sms-based MFA is frustratingly used to protect some seriously sensitive accounts and material the right Sim swap on the right Target in 2022 could be all that's required for state-sponsored hacks and corporate Espionage and given that this only requires a little bit of forgery it's not out of the question so what do you do well Begin by changing
all sms-based MFA protections you have to application or device based while you might not be a target for bragging about all your sweet Dogecoin most of you here today are in industry and have access to sensitive customer or government details now even though as an example cybercx has application-based MFA adversaries aren't just targeting your corporate accounts no one's afraid to go after you personally um and I seem to be missing some notes um but I didn't just come here to complain um about this problem and not offer a solution I do enough of that every time my mom registers a new account with a password summer 2022. please don't hack my mum um but the idea comes to me could a
super friend Trevor long who suggested centralized cryptographic identity verification and this concept is in nowhere new but it hasn't been deployed widely enough in Australia um across either government or consumer and it works very similarly to the way that you can scan a license using the QR code and the service New South Wales app this process needs to be extended out to passports to Medicaid cards any form of identification should require a cryptographic response and there is no reason that in 2022 uh your companies need to store this identity documents on a small scale and much more practically all we can do is report the issue to the major telcos and wait patiently for either them to align with
the legislation or for someone important enough to get hacked and I can keep I can stop desperately trying to convince my colleagues to let me raise SMS based MFA is a critical issue in every pen test that I do uh thank you very much
foreign