Next Generation Red Teaming Robert Wood Security BSides Boston 2014
Show transcript [en]
thank you thank you can everyone hear me okay move this up down all right fantastic so uh as was mentioned my name is Robert Wood I work with sigal uh we're primarily a security consulting firm we specialize in software security uh for those that don't know us um this is me in a nutshell so I run our red team assessment prce oh no worries we good all right stand by here it all right um so I run our red team assessment practice as digital um I've done all sorts of crazy things as I'm sure uh everyone in this room has have has uh you know work on software assessments Network stuff you broken into buildings run social engineering
stuff work on mobile uh security architecture things uh help build Out Security Programs all sorts of all sorts of stuff um and it's really all of that types of experience and Consulting has kind of led me into uh developing this this approach that uh that we're going to talk about today so our agenda uh high level we're going to talk about you know what is red teaming and in our perception and how I would kind of hopefully urge all of you to to think about red teaming uh what the currently what the current industry standard approach is um you know why that is clawed in a few cases and you know where we can improve it um and a part of that
is a Reliance an over Reliance on point TCT risk uh scenarios when you're conducting assessments um elements of building up a successful red team whether you're a company and you you're trying to bring in a vendor to do a red team you know what you want to look for to make that uh to make that successful so you're not just dropping money down the toilet or if you're standing one up internally the kinds of skills that you're uh that you're going to want to bring together um bringing software into the mix so you know as I'm sure everyone here knows uh in a lot of cases software is what's actually handling a lot of our
assets um so our bank account information our health records all of that stuff and if we completely neglect that that application layer then we're not testing and evaluating the security posture of you know ultimately what's handling our our most sensitive stuff and we're going to talk about the the concept of continuous red team which is kind of a it's still in a very rough brainstorm uh concept right now but we've just started developing a a framework or platform uh to conduct threed teams on a continuous uh on a continuous basis uh much in the same way that you have uh you know Network assessments continually running uh you have folks like verico continually running binary scans things like that um
so we're going to talk about our idea for that and you know why it might be helpful so moving right into things um so does anyone hear uh and feel free to just raise your hand real quick does anyone uh have any experience with red teams ever done a red team awesome awesome so uh real quick I'll uh just one person who raised their hand um you know can you tell me what uh in like 30 seconds or less what uh the capacity uh you played on your red team
p we have the course of a week to break in and do whatever we can kind of show the impact of real world threats uh the spoke was wiress application Network perimeter physical uh weekly really open SM awesome awesome so uh so for anyone who missed the beginning of that it was essentially uh it was a time box assessment uh real world adversary emulation uh open scope type of scenario where uh you know you're driven by something you know some kind of attack or motivation and you're just going uh you know throw the kitchen sink at whatever your target is and attemp to accomplish whatever um so how is red teaming different from any other kind of
just pentest um so a lot of pentests as I'm sure you guys know end up just being a very boiled down bug so we're looking at a Target whether it's a network infrastructure a web app a mobile app something and it it turns out just to be a bug up so we're trying to find everything that is wrong with whatever our Target is whether it's acne bank.com whether it's acne bank's Network infrastructure whether it's some shiny new mobile app they just put out in the iOS or Android store whatever whatever the case may be we're just trying to find as much wrong with that that thing as we can so red teaming on the flip
side is a goal-based adversarial testing process um red teaming in as a term developed way way back when um uh back in uh it had its roots in like military war game scenarios so you know generals and commanders all of these guys would use it to you know they would lay out a military strategy of attacking some thing or you know accomplishing some goal whether it's transport goods from A to B whether it's take down some enemy that's hiding over there and essentially they would put this up on a big board um and essentially play out a chess leg match where they would say we're going to do this we know our adversary or we think our adversary
might respond this way what are we going to do after that and it's it's K level thinking where you're trying to think uh you know several steps out in advance um so that translated all the way into uh into you know our information security world and pentesting where now we have these these gold driven uh adversarial testing processes so we're thinking about everything in terms of how are how an actual adversary is going to do it we're going to emulate an adversary um in most cases uh we try to push our customers into doing this as an organizational assessment as opposed to testing a very specific Target in a very specific setting so you know testing acne
bank.com in uat under you know tightly monitored conditions all that stuff it's not you can kind of extrapolate the findings that you get in that scenario to real world situations but it's not a real world situation at the end of the day um another big thing is we're going to be able to measure how an organization so I'll I'll keep using AC Bank um just to protect all the banks that I actually work with um to measure how acne Bank responds to a real world attack or at least a simulated one in this case so we're because we're going to be using the exact same attack uh attack techniques we're going to be driven by the same
goals that an attacker is going to be driven by uh we'll see if if AC bank or whatever client can detect whatever attacks we're doing and subsequently how they respond to those attacks do they lock us out do they just just remove the asset from uh from existence or you know you know there are a number of things you can do to respond but we want to we want to see if we can quantify that um we're also going to be able to incorporate a lot of different components of an organization so components have they have networks they have apps they have buildings they have people supporting all that stuff they have business processes supporting
different components of their business uh so we're going to get to evaluate all those different things or at least we're going to consider all those different things when we're going after our Target so I like this little graphic um in describing how a red team assessment relates to other security Assessment Services um so essentially uh consider this uh consider all of these silos as any one given type of security assessment so you know we can do a test on an embedded or thick client technology we could uh do a mobile app test we could do a wireless network test and you can do everything from the very basic assessments where it's more or less just you know automated tools scan
generate XML form XML into your own report and deliver it into whoever kind of consumer and you can do very very Advanced assessments where you you do that stuff and you do a little bit more and a little bit more and it's very very manual process and you know you really dive deep into whatever your target is here I like to think of a red team assessment as sitting on top of all these things driven by a goal so where whever you are uh in relation to accomplishing your goal so you know you lay out an attack path where you know your goal is over here and accomplishing the goal is over here and all the steps
along the way of getting to that attack path um you may use any one of these techniques and this is not an all-inclusive uh graph I just you know ran out screen in real estate um but you may use any one of these techniques to accomplish your uh accomplish your goal so uh don't think of it in terms of it has to be a network it has to include Network testing it has to include app testing or social engineering whatever the case may be it's likely that you may go in One Direction or another but it doesn't have to you're not restricted to that and so uh some basic elements of a red team anyone who's uh you know watched a talk
on red teaming or gone to YouTube and and saw a talk there uh you've probably seen the very basic V diagram of electronic social physical um I splash up a little recounted more because you know personally I think there's there's a little bit more that we can do than just uh considering the electronic social physical aspects and just doing bug hunts you're essentially just doing a wider bug hunt if you just consider those kinds um so really quickly the electronic space you know it's it's software it's Network it's wireless uh you know all the stuff that we would expect it to be uh social this is where you get um you know the human element
into things so you have attacks like fishing coming coming into play uh you know you're calling up somebody on the phone and you know trying to get them to diol confidential company information or uh password something like that um I am your chat functionality and of course the foolish stuff that you know we know a lot of people put out on social media so their Facebook accounts are LinkedIn all that good stuff um so physical uh this is where you get into Access Control technology so all the badges that we're using to get into our buildings the blocks that we used to secure our more sensitive stuff um you know guard uh guard duties so you know
do you Outsource your your guards or you had a shared facility um do you even have fac uh physical facility security or do you do you rely on police until you get suspicious um also all of the the processes that go into obtaining access badges um and of course none of these lists are all inclusive you could probably add to them uh you know until the end of time but you know how do how do people get access badges uh if some forgets their access badge for a day what do they do then you know do they just not come to work for that day or you know all things to consider um so some of the other activities uh you know
any good red team is usually any any good assessment really but but primarily red teams are driven and kind of glued together by the reconnaissance that you do in those in those uh situations so usually they always start with with some element of reconnaissance and you're always Gathering and learning more information about your Target and as you go through out you're kind of piecing all that together and that's like a glue to your um business processes so I mentioned before uh you know a lot of customer or not just customers but any any business has certain processes that they use to support you things or you know process within their organization so maybe it's a new employee onboarding
um so how does that process look from a workflow perspective uh is it all handled by technology is there a lot of people intervention uh password resets for customers versus employ emplo es for remote access you know is it all handled through you know I submit my my email address through some online form and get some onetime uh token email to me or can I call up a CSR and try to convince them to reset my password um so understanding how those things work in the various Avenues you can accomplish them may lead you down the road of you know missing or weak controls in one route versus another um Gathering some element or doing some element of threat and threat
modeling so this is really where we're emulating a very specific adversary or a category of adversaries so if we have um if we if we're working with defense uh defense contractors or government contract or uh government agencies in some cases uh we may be considering you know not just the script Kitty uh type of threat but maybe uh you know the organized nation state or the organized crime uh threat actor who are going to have much more enhanced capabilities and obviously very different adversarial objectives um incident response capabilities we touched on that just a little bit ago um so how does an organization respond to any given type of attack um can they detect it and how
do they respond and of course risk managements I'm going to talk about risk management in a little bit different context than you may be used to but it's essentially flipping how an organization does risk management um on its side and using it against itself so um I'll talk about this in a little bit more detail in a you know composite attack War Story I guess U if you will but essentially so we'll use acne bank again as an organization so acne bank.com consider uh you know any big Bank their primary Flagship website is going to be at the very top of their risk ranking um so it it gets the most attention the most money gets sunk into protecting it uh
you know from a network app perspective that's where all the money goes but subdomains of acne bank.com may not get ne nearly as much money in defense and uh attention throughout the sdlc with regards to bug management bug identification and stuff like that so you may be able to use those um those lower priority apps against the active Bank organization um and role-based social engineering is a concept that we're uh that we're flushing out and it's essentially instead of targeting the point in time risk social engineering where you're emailing Joe Mo in finance or Mary over in HR and trying to get them to divulge information it's social engineering a role within the company so this kind of ties into the
business process analysis where we're going to social engineer a CSR as it fits into the password reset process so are there weaknesses in that password reset flow that allow any given human who's who fits in that role to be susceptible to social engineering or are there technical controls in place to help protect people from themselves uh cuz ultimately uh you know anyone could be susceptible no matter how smart we all think we are to social engineering at any given time so if we have technical controls in place that allow us or that that prevent us from shooting ourselves in the foot then that's going to be that's going to be better uh for folks who who may not be as well trained
in the in the art of security and the you know the hacker dark arts um which our csrs are not so uh so ultimately we want to help protect people so tying all this together uh we're going to walk through a a little composite ATT tax in area that uses a lot of these different things uh so a while ago we were working on a uh defense contractor um so it was a full open scope engagement several months long so we really had um you know a lot of budget to work with a lot of time to work with and they were worried about you know terrorist organizations and organized crime with regards to their uh
their corporate IP um so from the uh from the perimeter everything was very very secure um so we did a lot of different network testing a lot of different app testing and anything we could find everything was pretty well locked down um that all changed as soon as you actually showed up on their front on their front step uh so gaining access gaining physical access into their facility was pretty easy um you know we were able to tailgate we you know did a few different things but ultimately where you were able to tailgate from you had to you had to do a lot more uh you either like lift cards or clone cards or something to get further to the
facilities uh so what we ended up doing and the reason um you know FedEx is up there is we got FedEx uniforms we got these big uh you know pelican cases that I'm sure you guys have seen you know it was probably like this big you know it it was pretty big I was big enough to put somebody in I'll I'll uh I'll leave with that so we took it to a machine shop uh we put l you know dummy locks on the inside or dummy locks on the outside real locks on the inside so somebody couldn't open it up and uh see our guy hanging hang out in there uh we got him a company uniform made up um put a
little Periscope on the top so he could see outside everything um and we showed up with uh you know Custom Critical uh FedEx van that we obtained and uh you know we showed up while the actual FedEx guy and UPS guy were there and we had our little handheld we wheel the guy in and uh you know they're like oh you know Custom Critical box you know this is this is fascinating we've never ever received anything from Custom Critical uh where going to put this thing we're like you know I don't know we don't know who the recipient is apparently uh we're our our instructions were you're getting a separate set of keys tomorrow to
actually open up this thing um and that will have the recipient like all right you know that doesn't seem suspicious so they brought them in uh brought them in past everything and that was past uh their storage room was actually up by all the Executive offices where there was the security was a lot more lacks around that section of the office so they put him in a storage room uh not locked or anything and uh you know went home for the day so as soon as uh and this was towards the end of the day as well so you know he waits 30 minutes our guy gets out of the gets out of the crate and uh he had a bunch of the P
plugs on him as I'm sure you saw the P plugs you guys are probably all familiar with him um had a bunch of P plugs with him and so he went into each of the Executive offices plugged them into uh into their Network Jacks it didn't have any kind of uh you know MAC address filtering anything like that so we were able to have our team who was sitting out in the parking lot you know now have shells on we had like four or five shells on on their internal Network at this point um so that was fun uh he got out nobody nobody called for anything because he was just an an employee and
of course getting out of a building is a lot easier than getting in so you know he got out you know easy peasy so a little bit of network scanning didn't really reveal too much for us um you know they they were locked down in a few cases but we did identify one uh one application that was it appeared to be homegrown um just based on how it looked and so you know we we decided we wanted to zero in on that it had some kind of very um it had some kind of name that was that kind of led us to believe that that was where they were housing a lot of their a lot of their sensitive stuff
um so of course we uh we get on the login page and it's protected by username password uh so the first thing we try of course is username admin and uh you know basic SQL injection string and of course it works uh sweet so we get in it had all their you know it it was handling it was a front end for all their uh all their source code it had all their uh you know data analytics algorithms and stuff all the stuff that you really would not have wanted to fall into the hands of their competitors uh because they were kind of the leading uh the leading company in that space and it also had uh based on how their company
worked they they embedded engineers in Military and other government groups around the world to help with data collection um and so they also had all of those operational employees who are out working alongside you know special forces units helping collect information and stuff they had the locations names dates all you know all sorts of stuff stored in this application that we were able to access uh so that was really bad um that was a fun job and uh on that note we are hiring um if anyone wants to uh be shipped around on a Fed Xbox um so the existing industry approach um this is for anyone who's you know again watched any kind of YouTube video
anything like that um it's very rudimentary a lot of it is just basic Network pen testing uh maybe a little bit of social engineering with the you know with fishing all that uh maybe some phone calls maybe some physical pet testing and by that I mean maybe they show up maybe they try to get into your building by tailgating maybe they drop a few us USBS with something on it and then then they you know maybe pop a few shells in some employees boxes and then they write you a report and run away and send you a new voice that's that's pretty much the the approach um so I'm sure you guys see where this is going
it's flaw in a few different major ways um as we mentioned before a lot of stuff is taking place at the app layer so if we're not doing anything at the app layer all that stuff is completely neglected so in the composite attack scenario we just discussed you know if we're just working on the network layer and physical pentesting stuff like that maybe we would have gotten in maybe we would have gotten to the point where we got to that core app but if we're not even considering application layer attacks then you know we would have fallen short of of achieving our goal um also the Reliance on very quick-win techniques doesn't really tell us much
about how it how the organization you know acne Bank whatever the the company is you know how how their overall security posture really works um and also doesn't of course tell us how that organization responds to an attack so if I'm launching one single uh fishing attack on one single employee or I'm doing just a couple of basic Network scans and you know not really working with their instant response teams anything like that then we don't really know if they're detecting us how they're responding to us things like that because ultimately as consultants we want to help our customers improve their security posture we don't want to just you know make ourselves feel cool uh
that doesn't really help anyone EX for our EOS um we also have no idea how uh so a lot of organizations will have anywhere from like one to several thousand applications in their you know in their portfolio uh so this this current approach doesn't really it doesn't really tell us how all those things fit together uh with regards to you know risk ranking where certain things may be vulnerable um and all that so uh you know this is a very basic point in time risk scenario um again just I I kind of alluded to this before but a lot of it's just targeted fishing attacks uh you know maybe I get access to a to a person to a certain person's
system maybe I don't um even if I'm allowed pivoting uh it's usually it's usually all just at the network player um so it's only sometimes uh interesting depending on what I can get and of course with that point too I also need to be able to uh to exil trate data so getting access to data is only half of that um figuring out how to exfiltrate it is a whole another thing because there's a lot of money that goes into not only protecting stuff but protecting stuff after it's already been found so uh so this this kind of shortsighted approach also doesn't tell us if that data yes maybe I can get access to a system where it's
stored but did I you know break the encryption or did I find the key that allowed me to decrypt the sensitive data to actually get that data out um where it could be seen and used against the company we don't know so uh some elements for Success so uh going into success with red teaming we need to scale we need to expand and we need to uh you know obviously hopefully secure things so setting up a successful red team um so I'm going to use threat model here um you know threat modeling in a lot of places means a lot of different things essentially what I what I mean by threat modeling in the context
of red teaming is considering the adversary that you're trying to emulate so whether it's the script K which is just foolish just do a normal pent test um you don't want to emulate a script Kitty and a red team it doesn't really make sense um but maybe it's a maybe it's a sophisticated criminal organization maybe it's a nation state maybe it's a malicious user or a malicious Insight or something like that um and different adversaries different thread actors have very different objectives very different capabilities and essentially what you can do uh or what we've started to do uh as sort of a a predictive tool is we'll do our thread analysis so we have you know thread actor a thread
actor B thread actor C each thread actor has their own set of goals whether it's get access to customer data whether it's bring this service down whether it's uh break in somewhere and just you know post something on the Internet that I did something cool whatever the case is each of these thread actors also has a set of capabilities so you know whether it's money to spend skills at their disposal um you know the nerve to actually go break into a build building because somebody over in you know a script Kitty located over in Russia or just a script Kitty in general may not have the nerve or the wherewithal to go and break into a facility um so physical
pen testing might be completely out of you know out of their element they're just they're not going to be involved in that kind of thing it's all going to be remote attacks um and essentially what we do with those is we map those in kind of a matrix format to actual Technical and business risks that we identify in the um throughout the course of the engagement and this is kind of produced as a as a deliverable so essentially what we have here is a set of antecedent conditions that we can use and say this thread actor they they want to do this they can do this and these risks are real we've identified them uh that tie
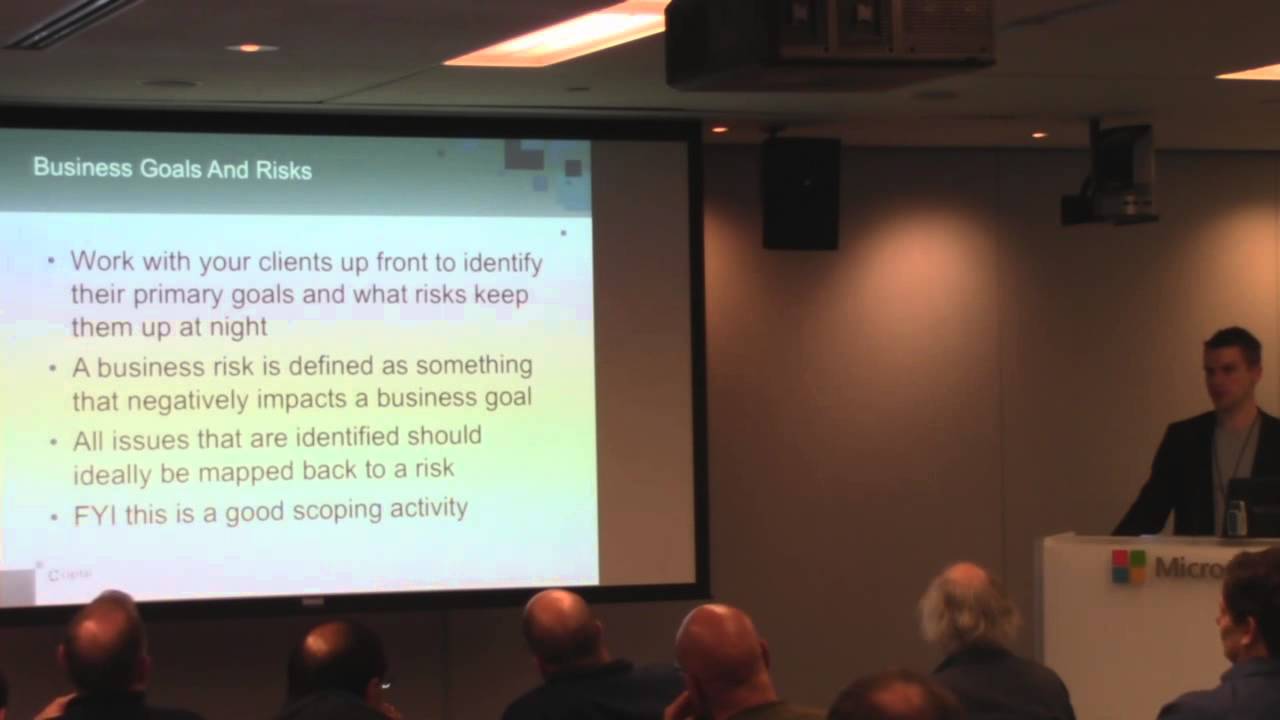
back into those so this is a very likely attack path um in your organization right now uh given all these things um another thing you also want to do up front is uh you know work with your client or work internally to identify what your business goals are what your business risks to those goals are um so ultimately if we're not tying everything back into the context of your organization then the results are going to be much less helpful um and with any risk that you identify throughout an assessment whether it's a single cross-site scripting instance or uh you know whether it's every single system that you scan on the network seems to be out
of patch uh or you know have an older have an older patch or an older version and it's always this version you you can kind of extrapolate those findings into bigger security themes across the organization so you know if you if you find these things consistently whether it's you know missing framework for preventing against injection attacks or missing patch Management Systems stuff like that you know what is what is actually happening underneath that that or on the back end of that you know do you guys not have a patch management system and if it's happening here on these systems is it also going to happen on that side of the organization where we didn't look um but if it's if this
process proc is just inherently flawed or missing then it's probably you know you probably also have issues over here so we can we can fix much broader problems or help our clients fix much broader problems in this case all right so uh so we kind of already discussed this very uh very briefly so I won't really touch on any of this um but essentially you know I I assume we're releasing these slides so in case you guys want uh just the content so uh again with business goals and risks um this is a this is an activity that's best done right up front so that way you can actually use the business goals and risks to guide uh you know to
guide your attack path generation guide your reconnaissance guide you know if if you're if your companies are very very worried about uh securing uh you know Bank information then as opposed to maintaining customer availability then you're going to want to look for issues that relate to that as opposed to you know denial the service that Serv it all makes sense um nothing revolutionary so uh the software attack Service uh so again as I as we mentioned before software is actually what's handling a lot of our sensitive stuff so whether it's you know interacting with acne bank.com and you've got uh you know SQL queries and stuff actually retrieving and displaying the data that we're uh the bank account data that
we're working with um if we don't consider the application layer then we're not going to be you know that's that's usually the easiest the path the least resistance to the data uh to the sensitive data and again in a lot of big organizations we've got application portfolios ranging from anywhere from like 1 to 10 you know just a handful of apps and I've seen places with over like 3,000 applications in organization so how do they manage that mess um how do they secure it all how do they know where assets lie uh what applications are using those assets in a lot of cases they don't they have no idea um and that is an ad that's an advantage for the
average city um and again just scanning the network Just Doing Network layer stuff um is not going to give you the big picture here so doing both gets you a little bit closer but just doing the network unfortunately it's just one piece of the puzzle it's important but it's not the complete uh it's not the complete solution so uh so leading into the next uh composite of tax scenario we'll talk about uh real quick about the highrisk of low-risk applications so I alluded to a little while ago with acne bank.com the flagship application of acne Bank um where they spend all their time and money depending uh consider for a second and this is actually a very real
scenario a subdomain of AC Bank uh let's call it promotions so promotions. acne Bank um also has uh it uses all the same cookies it uses all the same uh it has the same a similar CSR backend that Acme bank.com this um but promotions. Acme bank.com doesn't get any money in terms of security funding uh you know bug management any of that it doesn't it doesn't even go through a pent test before it gets pushed out on uh onto production so uh if you if you think about like you know attacks like cross scripting for instance um if I can find a cross crypting uh instance on which you know cross crypting is very basic bug it's
very easy to find it's very easy to exploit it's very easy to create very real world payloads um launching a fishing attack on a customer's actual domain so not trying to redirect them to some some weird cob job URL that you went out to go Daddy and bought um but launching those attacks on a customer's actual URL um so all the things that we normally tell people to to watch out for when when they come to fishing or when it comes to fishing attacks you know F the URL do this do that it doesn't apply in this case so I can rewrite the entire page to include anything I want which as you'll see in this uh in this next case
we actually did this so uh so this was a red team for a for a very large uh multinational financial institution um we call Active Bank as usual um and they had a a marketing esque uh application uh just as I described that had you know there was using shared cookies um and none of those cookies they were it was all tied back into SSO so they were all scoped to the parent domain none of them were protected with HTTP only or secure anything like that um so we did a lot of reconnaissance uh we found that you know their normal bpn required uh uh you know two Factor off so that was going to be a tough not to crack um
they did have an admin bpn that was only single Factor so it was just username password and it was all of course domain credentials um we found a bunch of employee email addresses uh coincidentally also some of them admins uh we found out on LinkedIn um you know jigsaw stuff like that so we did a lot of network testing a lot of application testing and we got to this um we got to this promotion site and so we we found cross and scripting all over this thing like pretty much every parameter that this thing used um so we put together a an attack and we sent it into our employ redirected or redirect sent them sent
the attack to the targets redirected them to this page and so we we put together this ruise it was you know we're rolling out some bonus pilot uh if you want to be a part of it you know you're going to have to give us your domain credentials blah blah blah um and of course you'll get like a 25% bonus at the end of the quarter sweet so a lot of people came into our site um you know at at the time when they came into it uh we did a basic process scripting attack posted all cookies which of course some of those were the uh the internal uh because it was all tied to
SSO it was you know AC Bank ASO C you know and then the value so it posted those back and then we presented them with a logon page uh to collect their domain credentials so once we went through here uh we went to that admin BPA logged in with a few of the admin credentials that we obtained and we found that in in some cases there was separate authentication um but we could get into internal applic that also leverage those that same cookie so since we had valid cookies from our cross-site scripting attack and VPN access we had access to all these internal administrative applications that allowed us to transfer money uh get access to you know customer
bank account information so it was a really bad situation for this uh for this organization based on a couple of what would appear to be very minor flaws so you know if we were to just report cross scripting on promotions. acb.com to them they wouldn't have cared they would never address it um same with the cookie issue you know you can tell somebody a thousand times that yes your cookies can be stolen by any domain on the on the or by any application on that on that domain if there's scope to the parent or yes HTTP only is important you know they're not really going to care until they see something as eye popping as
this um so that's exactly what we did um it was a bad day for them so so continuous red teaming so I'll fly through this really quick and then uh leave it up to some questions for you guys but essentially um why we want to why we want to try to push our way into this uh or you know try to wrap our heads around doing this as a as a solution is you know we have already in place we have a lot of network and application continuous scanning Solutions and it's really just you know running uh you know some tool against some Target you know it's it's the targeted bug hunt type approach um just
run on a continuous uh like CR job whatever just runs and runs and normalizes data presents it to you in a nice little dashboard um so essentially the idea um that we're wrestling with is rolling all of that up into uh into one single solution so the network part the application part and then automating some element of Open Source recones so there's there's a lot of Frameworks out there that exist to to help with open open source Recs whether it's Volo whether it's uh the Recon NG framework and there's a few other uh really really good ones that are extensible out there um using those to collect very similar types of data normalizing that and tying
it back into the types of issues we're identifying here um is the first step uh Second Step is you know evaluating all these risks over time so you know how things change throughout an organization over uh you know over the course of several weeks several months several years um we can we can identify changes in an environment closer to real time as opposed to waiting for the next annual pen test to happen before you know even though they've gone through 18 18 code pushes and network big changes prior to that um we can also appliation functionality um one of the big things here as well is uh is looking at the entire portfolio the entire organization
with regards to this process we can start to quantify the entire attack surface into one big picture so we can look at the at issues like the sh shared cookies the shared CSR functionality things like that and tie that back into you know we know that that this subset of your entire portfolio is using the same uh the same components for whether it's authorization authentication um support things like that tie that all into this big picture we and we can kind of group applications into this uh into a little bit more useful at least from our perspective risk rankings um so that's that's our idea um it's still like I said being very very much flushed
out and we we've just started design work and a little bit of coding on on some parts of it but of course there's a lot that uh that still needs to be uh that still need to be flushed out but I figured I'd uh introduce it to you guys and let you uh pull it over so uh so thank you for your time um you know if anyone wants to uh you know shoot me any questions anything like that I'm always happy to talk about this kind of stuff um as I'm a security and Technology junky so um yeah thank you hope you enjoyed it and
uh questions H yes how can you simulate a inser tech attack so uh so with regards to sim so the question was uh simulating an Insider attack so it's really about uh the capabilities so with an Insider attack you have a certain uh you know you have an initial capability of I have inside access um The Insider may have certain goals whether it's to bring down uh bring down a customer uh as a result of being pissed off or something that they're fired for um or slight It Up R something you know think office um so they have certain uh right so they have they have certain grudges against uh an organization so try to figure out what they what they
their objectives are their capability is they have that internal access so it's really you would just instead of starting from the external perspective we start from the external perspective in most cases just because that's that's the threat actor that everyone is most concerned about is the you know the guys sitting over at Russia the guy sitting over in China or you know wherever in the world coming after the organization because the perimeter is just it's very visible it's very it's like the default setting for what I want to secure first but here we would just start with that internal access would start with a base level employee account maybe and then we would just go from there so it's really
about you know determining what the capabilities are and then uh what your goals are and then starting your
test so actually uh so I did a red team a while ago where uh you know it was actually up to me to uh to gain access as that employee and uh so I went in and I didn't even apply to the company or anything I kind of just I I tailgated in for like a week straight just kind of told everyone I I you know grabbed a cube and uh at the end of the week I was like I kicked somebody out of it the cube that I was stealing what are you get out of here my Cube you see my name on the thing um and so I was hanging out there and you know I was there for uh
like three to four months and I was doing Network testing and stuff every single day you know just kind of probing and finding things it was very low and slow uh I did a lot of Googling during that time because I didn't want to raise any alarms you know um so it was just uh very low and slow attack working on um you know working on getting access I think it was it was some element of customer data I can't remember exactly what it was it was a few years ago um but at the end of it you know I was I was essentially an employee like I went down to the security office had them
give me a badge um people were inviting me to potler lunches like um so you know in in that case you know the admins uh and a couple of the managers were the only ones that knew about me um and so every you know they would see me in the hall and just shake their heads and because they knew what I was really doing there and uh you know but they were they were monitoring my activity of just not telling anyone about it so you know they they could see that everyone was immediately trusting of Me based on how I acted and of course they didn't have the network controls in place that attack anything I was doing technical
attack wise so yes can you give some examples of things that would trip up a red team so process oriented things that would trip up a red team uh it's usually very very needy clients um or very just needy managers that want to have insight into every little thing that's going on um that's often times what we want to what we run into or it's like you know you can only attack during these these windows or you have to tell us every single time before you can do something actually the question is um what kind of things did you run into that caused the red team to fail so I'm not sure that I've actually ever
had a red team that has just ultimately failed um run into a system that's totally encrypted you can't so in those in I mean you run into a situation there's always there's always another way so you know in in most red team situations like if you like if I run into a if I run into a lock for instance that's very like I I don't know how to pick it or something like that I'm just going to you know as an attacker would do instead of focusing all my time on that um especially in the case of the Consulting engagement time box scenario I'm just going to go find another way or I'm going to talk somebody into breaking
it for me uh whether it's an admin or like unlocking it or something like that
so i' say a funny but I mean something that from the outside
that's been putte my time hours on it day yeah so I mean I guess in the context of the Consulting engagement um you know time is your biggest enemy um like you know you mentioned with your red tea if you had a week um which a week is just I mean a week is crazy if you have enough guys and it's open a week's plenty of time to get a week is plenty of time to get in but if you so any time that you lose is very valuable so if you lose a day then it's 20% of your engagement out the window um well you know less than that if you're going to work on the weekends but we'll say
20% um assuming we're up not all Workaholics and uh so yeah I mean time is time is your biggest enemy but you know it's usually like things aren't usually showstoppers they're usually just obstacles that you know you run into and and then you just find another way around once you learn about it um that's that's usually been my experience at this what about honey you ever situation when the yeah so for you and yeah so I've I've run into honeypots before and it's uh you can usually you can usually figure them out if they're just so you kind of cross reference it with like how sophisticated you know the company is so you know with some of the
very large banks that that I work with I know they're they're doing perment or scanning and stuff on a regular basis so if I find something that's like too good to be true then then it's
probably indicat yep and uh and in some cases like that you can use uh you know just stand up like a very basic henta server that's not going to be tied back to your IPS or anything and just test it really quickly from that and then you know try to do a pivot attack and uh you know if it doesn't lead anywhere then you can kind of just make the Assumption yeah exactly just yeah there was actually a talkish mov on from for the attack talk he went over like some of the specific things we saw Cent so like identifying honey PS and such I mean yeah not even just like honey system kind like Hy
accounts yeah yeah there's yeah there's usually a lot of uh too good to be true type scenarios but I mean none of them none of them are still they're usually tied back into some kind of uh alerting or identification mechanism um sometimes a de giveway is stack
window yeah but even even like accounts uh like easy accounts that are uh that are able you're able to break into it's um you know most of those things are not again showstoppers in any way shape or form um they're just another obstacle and those it's actually a way for you know the the client or the organization to you know identify you or or know your NE um but even if they can identify you it doesn't necessarily stop you so you you just go find another way any other questions well I will be uh hanging around here today and tomorrow if uh anyone wants to come up and
uh





