When the Breach Hits the Fan: Understanding Cyber Insurance
Show original YouTube description
Show transcript [en]
Good afternoon everyone and welcome to Bides Las Vegas's Common Ground. This talk is when the breach hits the fan understanding cyber insurance given by Mia Clif. A few announcements before we begin. We'd like to thank our sponsors especially our diamond sponsors Adobe and Iikido and our gold sponsors Profit and Run Zero. It's their support along with our other sponsors, donors, and volunteers that make this event possible. These talks are being streamed live and as a courtesy to our speakers and audience, we ask that you check to make sure that your cell phones are set to silent. If you do have a question, use the audience mic over there so YouTube can hear you. So, just go ahead and and pick
that up and and and ask them there. As a final reminder, the bid's LV photo policy prohibits taking pictures without the explicit permission of everyone in frame. These talks are all being recorded and will be available on YouTube in the future. With that, let's get started. Please welcome Mia Clif.
All right. Good afternoon. Can everybody hear me in the back now? Is that better than it was? Okay, good. Because I know we tested and was weird. Uh, so, um, as our wonderful host said, this is going to be about cyber insurance. I know you're going to think it's kind of boring. It might be a little bit, but I'm hoping it's going to be a little bit insightful and we will have some insights on what's happening in the landscape. So, maybe by the end you'll be like, "Oh, that's kind of cool." But if you do have questions as we go through, please at the very end, come ask those on the mic and I am always
happy to answer questions, have conversations. Uh, it's an area that I never thought that I would enjoy as much as I do, but I do love talking about it. So, please, um, a couple of things before we get started. I do have to allow everybody to take about 10 seconds to read the disclaimer. I will not do the, uh, car commercial runthrough of this. I have done that before, but I'm not going to, uh, because we have a lot to cover today. But basically, I I did have to apply this disclaimer to my presentation today. Uh, so we're going to talk a little bit about me and what I do. We're going to talk about cyber insurance and what it
is and what it isn't, what it covers. We're going to answer some common questions that have been given to me from other cyber leaders and cyber individuals to help clarify a little bit about what cyber insurance does, how it works, get through some of the myths that we've seen over time, and then how can you do better at working with your insurance carriers. And then um what are we seeing? What are we watching? what are we paying attention to? Because that does kind of play into what we're going to be paying attention to on your questionnaires and how we assess you for underwriting your insurance. And then of course a Q&A session. So a little bit about me if you don't
know who I am. Uh my name is Mia Clif obviously and uh I am considered an executive adviser for cyber risk engineering. What does that mean? That means that I have been a cyber leader. I'm on 28 years in the cyber security and IT fields. Uh I was a CISO in a previous life and uh my organization Liberty Mutual actually brought a whole bunch of cyber leaders in because they wanted to know what was going on inside the brain of a cyber organization. They didn't just want to base it on what they were seeing on what an attack surface management protocol might say. they might just not want to listen to exactly what the questionnaire says because
sometimes it's not the CISO filling out the questionnaire or sometime the questionnaire might be missing an answer or somebody might just put yeses all the way down but not actually mean yes all the way down. So they brought in these cyber leaders because we've lived the worst day of a cyber security person's life and we've lived the best day of a cyber security person's life. But that also means that we understand the back and forth that's going on in the day-to-day of being in a cyber org between having to ask the business for my budget to explaining to our individuals why it's important to do uh awareness training. So I get to advise underwriters on what's going on inside
an organization that is asking for cyber insurance to help figure out what the risk truly is. I don't make those risk decisions. I just get to say here's what we see and here's what's concerning or they look pretty good. This is awesome. Uh me and one of my colleagues who's here uh we tend to send emails going well this looks all right. Here's a couple things they might want to think about to I have grave concerns about the cyber security organization that in this business and that tells our underwriters okay this is okay to maybe we want to increase that premium or not want to write that in the future but we don't ultimately make that decision. In
addition to that, we also get to educate the larger cyber security community because how many of you have actually talked with your cyber leaders or been a cyber leader who is getting cyber insurance. All right, great. You all know what this goes into. Some people don't. And what we found and what I found when I was a CISO is I didn't get to be part of that conversation really. I got to answer the questions on the questionnaire, but sometimes I was like, "Hey, what about this?" or I had found out through another colleague that you know I have great options for partnerships and business relationships with vendors through my carrier and they were like my
my general counsel was like no you can't do that and you can't have a conversation with our insurance that's controlled by us and we were like hold on a second so I'm trying to raise awareness on what cyber insurance can and can't do to help cyber understand insurance and help insurance understand cyber so we kind of run the gamut on all of those things we also do look at lots and lots and lots of businesses uh for cyber insurance on the regular. Uh as I said, I've been a cyber leader for a really long time. I'm a mentor. I'm an educator. Clearly, I'm a speaker. Um I've been doing this a while. I teach a
GRC course and I mentor for cyber and Isaka and Whisus at times. So, and I'm mentoring somebody here for the ground truth or the ground floor track at Bsides. Uh back home, I have three wonderful greyhounds, Napper, Nelly, and Nia. As you can see on the screen, I live in the Twin Cities of Minnesota, but I travel pretty much everywhere. And uh feel free to ask me about my quilts. For anybody who was here last year, I did talk about how quilting made me a better cyber security professional. And you can find that on YouTube. So, let's talk a little bit about cyber insurance, what it covers, what it doesn't cover, and the different coverages that kind of fall in in
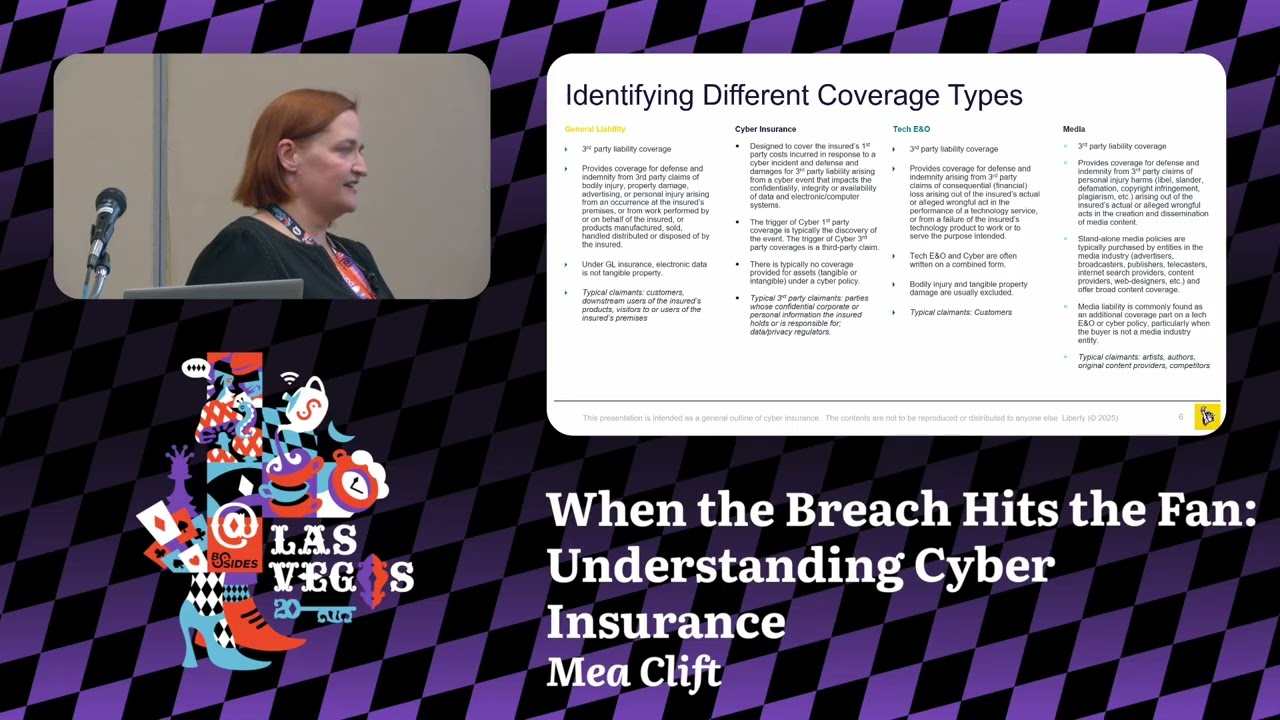
addition to just cyber because it really does kind of run a a larger swath than you might anticipate. So, when we're thinking about insurance for cyber security or for IT resources in a business, there's really four types that we're looking at. The first is your general liability and that's kind of your coverage for third party claims of bodily immor uh injury, property damage, all those kinds of personal injury kinds of things. Every organization needs general insurance. you know, they that's if somebody trips on your sidewalk, if somebody trips in your manufacturing plant, if somebody gets electrocuted, that's kind of all your general liability stuff. Under general uh liability, your electronic data is not tangible property. It's still, you know,
it's like we think about in the cloud, it's ethereal. Even though we know data has value, general liability doesn't consider it having value. That's for your customers, the users of your products, visitors to your sites, those kinds of activities. You know, your employees are going to be covered under workman's comp and under your casualty insurance. But here, that's where your general lines comes in. Then we get into cyber. And cyber is designed for first party costs incurred in response to a cyber incident. It also covers the damages from a third party liability. So if if you have a vendor that vendor allows you to be compromised in some way your cyber insurance can take part in
that recovery and recompense for that situation. The trigger of cyber first part party is typically the discovery of the event and then the third party coverage is a third-party claim. So you say that your vend your vendor makes an announcement that they've had this breach then you can put in a third party claim and that'll start your claim process. There's no coverage provided for tangible assets. It's mostly data. It can be a little bit of like if if your server melted for some random reason, but a lot of time it's not that tangible property that would be covered under general liability. Um, and then your third party claimments there are going to be if you lost someone's data, they
they could come after you for that. Uh, and then data privacy regulations kind of issues as well. Another uh aspect and this is a lot for our vendor friends is tech eno. So you're providing services. You need this eno coverage to protect you if you get breached. That's where when the third parties that you're supporting come and say, "Hey, this company has been breached and it affected our business." The ENO comes in to take care of it. So if we're looking at a managed service provider, for example, we need to make sure that they're going to have that ENO coverage. Otherwise, they could be out all of the loss if they have to pay for uh
notifications, if they have to pay for credit monitoring, if they have to pay to fix someone's system because we have seen recently a lot of incidents where a third party was breached or a third party was used to breach an organization. You think about a lot that's in the news today. It was several of them were because someone used a help desk who was a third party to contact the to reset passwords to allow the threat actor into the systems. Then finally media. Media is typically covered as part of cyber these days even though it's a separate kind of coverage but it's really to make sure that you you aren't um having to pay out for
liel slander defamation copyright infringement because we all do those kinds of things. I remember there was one job once where I couldn't use music without like express approval of the artists or things like that. So I had to like go through all of the teams in legal to be like is this covered? Is this not covered? And that would be where media would come in where it would be like oops I used uh banned and and did their title in my presentation and they found out and they were upset and they tried to sue us. That would be where media coverage would come in. Of course artists authors original content providers, even competitors can come in and and go against that media
coverage. But again, today we're going to talk mostly about cyber insurance and a little bit of tech, you know. So, let's talk about what cyber insurance coverage and that's going to be both first party and third party. So, you can see it covers different things depending on if you were the direct person or if you were the indirect person. So, of course, event management costs. So, all of your breach investigations that covered your business interruption. You know, this is really important to understand. So, it's the net profit or loss. It's not if your if your people can't work, it's if you're actually experiencing a loss of income because you're interrupted in operations. So, if your people are still
able to come into the office, that's not really a business interruption. If you can find a way for them to work differently, it's not a business interruption. If your manufacturing plant goes down and you can't manufacture widget A, that's a business interruption. That is going to cost you revenue over time. Uh it also can cause outages if you like your server goes down for multiple days. We've seen that in multiple attacks. Um I know of a hospital system that just went down for like two weeks. The business interruption of that operation would have been covered under that insurance cost. data restoration, any cost to bring that data back, to work with your restoration experts to do your
forensics, to get whatever data you can get back, especially if you couldn't restore it from backup for some reason or if you had to go through extra steps to get the data back, that's covered. And then cost incurred to investigate, mitigate, or end a cyber extortion event. This includes the payment of ransom. A lot of people don't know that, but if your organization and your country are okay with you paying the ransom, because some countries don't allow it, and some organizations have a no ransom policy, cyber insurance in many cases will pay that. Uh they will also have negotiators, professional negotiators to work with the ransomware request. They also have this the crypto wallet, so you
don't have to set up a crypto wallet, which is really great because sometimes that can be complicated. And they also have the investigators and the people who have worked with these people to make sure that, you know, one of the questions we've had on a lot of cases is are they going to come back and take our are they going to just ransom our data again? And it's possible in some cases, we've seen that. But with the ransom negotiators, because they've worked with the different threat actors, they'll be like, "No, they're legit. They're honorable. They have morals or whatever." And other times it might be like, "Well, you may not want to work with them so so handily because they're
going to come back on you in the end. on the third party side, you know, any defense and damages for claims from any failure breach or compromise to the security of the system. So, if you have a managed service provider and they allow somebody to come in, that third party uh breach is covered under your cyber insurance. Privacy liability, there's a lot of privacy laws happening. You know, every state in north in the United States has different privacy laws right now. Internationally, we're seeing a lot of privacy changes and uh there are certain places where we are exceedingly latigious about suing for privacy loss. And so this helps with that as well. And you'll see when we
talk about what we're seeing in the landscape some of those things that we're seeing and how we're how we're tracking those claims because we are seeing a bunch of claims around certain activities. Regulatory liability. Sometimes regulatory will come into play and you'll get sued or you'll get fined. Sometimes if it's in action in regards to cyber security and it depends on the coverage and it depends on the carrier there will be some coverage of those proceedings of hiring new legal counsel working through that process and in some cases and I won't say that's ubiquitous they may be able to help compensate for some of the loss that you're going to incur for those fines. Then of course
media and liability again defense and indemnity for personal injury harms that we were talking about with the media coverage where you know you say so and so sucks and they go well I'm going to sue you and it's cyber related it could be covered under media liability like if you post to YouTube or something. One of the things that I tend to see people talk about and ask about a lot is exclusions. They say oh cyber excludes everything. I can't do this. I can't do that. Somebody came and said, I heard somebody was looking to do a crowd strike exclusion. So, if you had CrowdStrike, you couldn't get insurance. And I was like, okay, hold up. That's a
bit crazy. Um, it's a little bit of a misconception. I think when we think about insurance, a lot of times we think, oh, we can't have insurance because we have a pre-existing coverage or, you know, we have a 25-year-old and we're giving them a Corvette for their birthday. you know, not that I would do that, but uh you know, we think that we're going to have these these issues with that situation. There's really not a ton of exclusions. And if they are exclusions, it's because something in the environment is so challenging that we have to say, "Hey, we're not going to cover that because we know that that is a cause of a breach or
we know that that is going to be a problem in the future." And that's just because, you know, we want organizations to do the right thing. Again, if you give a 25-year-old a Porsche, that's why their premiums are so high because 25 year olds are going to drive that Porsche into dangerous situations. I mean, I'm 45 and I would drive a Porsche into some dangerous situations once in a while because it's a Porsche. Uh, and now my insurance will go up. But, uh, thankfully I don't have a Porsche. 75% of our claims in the last year were paid out. And that's a pretty large number, especially when you consider consider when we analyze the other 25%. Not all
of those were denials. Sometimes what will happen is an organization will call in and they will say, "Hey, we've had an incident. We're not sure what's going on, but we wanted to give you a heads up." Cool. We're going to put that in. We're gonna we're going to notate it and we're going to say, "Hey, this is possible that we're going to get a claim. There's also the option that we get a claim in, but they don't actually take any money. So, we don't pay anything out or it's below the limit of uh deductible or um where we go where we would come into play. So, sometimes we know about a situation and it doesn't meet our our
level of that insurance. So, that's what we call a zero dollar claim. The majority of that 25% were those kinds of situations. So really the number of how many claims we actually pay out is much higher than you might think. And that's one of those things that people are like, "Oh, well you had this thing and somebody didn't get a claim and d" and it's like we're not trying to be out to get anybody. We're just trying to make sure that people are telling us what they need to do and or what they are doing and we're assessing that risk appropriately to make sure that we are compensated to make sure that we can cover it in the event of a larger
situation that takes out more than just one organization. The other thing that's come up in a lot of discussions is the war exclusion. So I put waring quotes because this is an evolving exclusion. So for the longest time a war exclusion meant kinetic warfare. One country comes after another country. They go to war. Anything that comes out of that war is excluded from getting a claim put on it. Right? We're not going to pay out for somebody bombing a manufacturing plant in another company during a war. just that was the exclusion because that would have been disastrous. Um, now we're starting to see things evolve because we're seeing war change from just kinetic to be the
non-kinetic like cyber warfare and scops and disinformation and things like that. What's happening in that landscape? We're watching closely. I don't have a direct answer, but uh the best thing I recommend people to do is talk to your carrier and say, "Hey, what is covered? What's not covered?" And that's really if it affects your organization. You know, not everybody's going to ideally be affected by that kind of in situation, but they could be. But what about this? And these are common questions that I received from some of my colleagues in cyber. I put it out to a Slack channel. I said, "So, what do you want to know before I did this presentation?" because I can I can
talk about this all day and I can get very long-winded and boring about the coverage, but really what do you want to know when it comes to coverage and cyber? The biggest question I got was how can an organization know they're getting the coverage they need? That's kind of on you as an organization. There's a lot of ways to figure that out. you know, um, for any of you who work in GRC, we know that there's the risk algebra, there's SLO, there's AL, there's even FAR, and there's organizations that are happy to help you with that and do that analyzation. There's a lot of applications out there that are trying to help figure out what is the risk from
a financial perspective of this incident potentially happening. doing a business impact analysis. I know this is something that organizations are not happy to do and they don't tend to do them with any regularity which is very very sad. I know you know what I'm talking about and I love it. I love the smile. I'm like yeah no totally preaching to the choir but it's a great way to say what are my critical systems and how bad is it if they go offline. I think back to, you know, there was a compromise last year was a little tiny company that ended up giving away everybody's social security numbers. Little tiny $5 million company gave away billions of dollars in privacy
information. That that should have been something in someone's business impact analysis going, "Hold on a second. Why does this little tiny company have so much data?" And there's a lot of those situations where we just depend on this one little widget. And I'll have a comic in a few slides about that. But we really we have so much stuff that we have to look at and go this is a critical system. It may seem tiny in comparison, but if this goes down, we've lost the farm. So thinking about that, how long can your operations run before you actually incur a financial loss? you know, if if you have multiple manufacturing sites, can you roll your site over to one of the
other manufacturing sites or a production site or even a cloud site until you can get your your primary systems back online? It's very similar to just thinking about risk analysis with like flood and fire. What would you do if your server room caught fire tomorrow? How would you continue operations? You have to be able to do that from a cyber attack perspective just as much. And then also add in the cost cost of all your consultants and partners. You're going to have to bring in consultants. You're going to have to bring in your vendor partners to help bring things back online. People don't account for that a lot of the time. And they're just like, "Well, I didn't
realize I was going to have to pay an extra $300,000 to bring somebody in to fix my problems." And I'm like, "No, seriously. Come on. We all know how this works now." Then your your notification costs. Based on our information, we estimate about a dollar per person based on our claims data about how much it costs for notification of a breach. And that's for your postage. That's for sending out your paper, printing your paper, sending your emails. So, it's about a dollar per person. So, if you have a million people that you need to email or send a letter to, that's a million stamps. That's that gets pretty pretty significant. And we know most organizations underestimate how much PII
or PHI they have dramatically dramatically. But ultimately, you know, you do all of this stuff, you think, hey, I'm in this ballpark. Your broker will also be able to help. Um carriers don't typically directly converse with our clients until we become their insurance partner. Our brokers are the partners that uh you would interface with and they're helping to get your best deal to figure out who can cover you, who can't cover you, and they're going to know what's best in your environment. They're going to be working with you for extended periods of time, and they know kind of what it looks like from the landscape perspective, and they'll be able to help you confirm that in the long run.
Another question that's come up before is what is a betterment clause, and how does that work? So let's go back to oh my gosh the server room exploded and okay that's covered and it was a cyber event that did it. Now generally you know we have to see that the cyber event has to occur. So a cyber event has to have happened before betterment can come into play. So let's say you have a legacy system that was taken out by a threat actor and in order to get it back you have to upgrade that system. So that cyber event occurred, took it out and in order to eliminate the vulnerability that was the source of the problem, you
have to upgrade. So a firewall is a great example. Firewall goes down, firewall goes out because it had this vulnerability. You need to upgrade that firewall because if not, the thread after is going to come right back in and take you out again. Obviously um if that event occurred and you have costs to upgrade that system or add a new firmware or you need to buy the new software that is what a betterment clause is for. The cost can also be incurred to avoid or minimize the risk of the recurrence. So again you have a certain firewall vendor and you're like this firewall vendor has been the source of several issues. Perhaps I need to
replace it with a different firewall vendor. The betterment clause would come into play to a certain extent. Again, you would look at what your clause covers and doesn't cover and work with your insurer to make that happen. It will not replace an entire manufacturing plant. It will not replace an entire OT system, but it will help in those those smaller situations to bring things back online and improve to a certain extent. You're not getting a whole new environment just because of one cyber incident because the whole cyber incident may not have destroyed everything. So, when should you notify your carrier of an event? So, there's going to be a notice clause in your policy and that's the obligation
that you have to meet. However, in many organizations, they recommend calling as soon as the incident happens and that's because you have access to breach response minute one. In many policies, the second you call, you get a direct line to an incident response team. you get in you get a direct call back from a breach coach and they are working with you from minute one and in some co in some coverages that's covered from minute one. You don't have to meet your deductible or whatever reserve to get to that. So you really want to get into that conversation as soon as possible to recoup your losses and to be able to recover from it quickly. You want those
breach coaches in. You want that incident responder on time and and working with you to get things back as soon as possible. You want that ransom negotiator to be like, "All right, what do you need? What are we doing here?" You know, because they know and they can work quickly. It's also some costs in addition to that are absorbed when carriages are engaged immediately. And then, you know, all concerning events should be contacted. It isn't like car insurance. You know, if I call and say I have a fender bender, it's going to raise my premium because I had a fender bender. But um it's not always going to directly correlate to a premium increase in the in the cyber world. And I say
that knowing that sometimes it does and sometimes it doesn't. So it's really it it it depends on the severity of the incident as always. But it's also just being communicative is always the best policy really. I mean just communicate. How many times do we say communication is the best policy and we all just need to do better with it. So, does cyber insurance cover fines and penalties as a result of a breach? What's the cyber security answer to everything? It depends. Generally, fines are for privacy and government security violations. Most to data, not to poor hygiene of the environment. And so, coverage is tied to the violations of the privacy laws as result of a cyber incident. Somebody
hacks in, the data gets leached, you're now in violation of that regulation. But occasionally a regulator could require an invent could require that investigation of that event and then the policy might come into play then. And of course sometimes in certain cases they may actually say you cannot pay your regulatory fines with your cyber insurance. I know there are some international uh coverages that will not allow you to pay your fines with your cyber insurance. So again, it's going to really depend on your policy uh and what was going on in that situation. So what can we do better to help our cyber carriers understand our environment and how do we partner better with them? Because that's really
important. We aren't just an it's not it shouldn't be an us against them kind of situation and it shouldn't be just a thing that like you aren't going to tell what's going on and you're not going to have the conversation. and you're just going to have once a year your legal team's going to be like, "All right, what do we got to do?" Or you have you fill out the form and then you continue on. This has to be a partnership. It has to be a back and forth in order for both both people to succeed in both organizations. What I like to say is that we need to be authentic. I know in cyber security we
talk about transparency. Transparency isn't viable. What I like to say is I don't need to know where the bodies are buried. I just need to know you have a graveyard and that you're taking care of it. You know, you have a mower come in once a week, you put some put some nice flowers out, whatever. Just know that you're maintaining the environment and you're continually improving it. If I see the questionnaire hasn't changed in three years or I see the same vulnerability year after year after year, I'm going to ask questions. I'm going to be like, what's going on here? And that is going to tell me a story. Whereas if you tell me, hey, we're
working on this thing or we're moving to advance this or we're changing this thing up, then I have the understanding and we have an authentic conversation. It's it's really that honest reporting of the environment that we're looking for. And I can't tell you how much more valuable it is to me when somebody is honest compared to yeses, everything's in place and then I go out and I go no. or I just look on Google and I see you got you got hacked last week and it was this opening and you're like no seriously friends come on. So let's talk about questionnaires. How many of us have filled out many many questionnaires? Yes we know unfortunately this may be the only
insight we get. Um please ensure that a cyber security person is part of that discussion and is contributing to the answers. I talked to a CISO at RSA this year and she said she saw the questionnaire. Her general counsel had answered it and she ended up writing a six-page addendum to the questionnaire about what was really going on. And the legal counsel called her and said, "So, you're telling me I was lying?" And she goes, "You weren't lying, but you weren't telling everything that needed to be told to understand what was happening." And I've heard a couple of people be like, "Well, can't you just come into my environment and look things over?" I'm like, I'm
never going to be able to plug something in like the progressive car thing. That's just not a reality. Not only because your legal counsel is going to be like, "No, that's one, no, because legal is going to be like absolutely not." Two, why would I put an extra potential vulnerability into your environment? And then three, with segmentation and authentication to get everywhere, I'm never going to get a full spectrum of your environment in this modern day. So, it's kind of a challenge on how best to assess that risk and what can we do to better find ways to assess what's going on in an environment. So, really, we want you to be as vocal in those questionnaires as
you can. If it if there's a common space, fill it. Please tell us what's going on. Even if it's we're working on moving into this direction or we are moving into this thing in this date, that helps us understand that you actually understand what's going on. That helps us understand where your end of life is. That helps us know that you have an awareness of your environment. And there are many organizations that don't have complete awareness of their orgs or what the important risk profile is. How many times have I heard, you know, I've asked on calls, I've said, "So, what's going on in your OT environment?" And they're like, "Well, that's a work in process." And I'm like,
"That tells me that you're not securing it, so that makes me a little nervous." Or, um, you know, that's on our 2026 road map or last year it was on our 2025 road map. We come to 2025 and we go, "So, did you do it?" Well, it's now on our 2026 road map. Okay. we might want to advise you or we might want to recommend that you kind of prioritize that because it's going to be a threat profile kind of problem in the future. So please make sure that there's a cyber security leader who understands the roadmap and the strategy and fills the comment section with all the details that you and your legal team are
comfortable with. I know sometimes they're a bit difficult about telling everything, but there are ways to just say we're working on this or we're moving in the right direction or we have this partnership and we're looking to enable these things. It really does help in the long run. A couple of other tips and tricks. If you have the availability to provide your road map on what you're working on in the next year, that's wonderful. A lot of brokers will organize underwriter calls. So the way cyber insurance works is you don't get one carrier. You get what's called a tower. So there's going to be multiple carriers. Whoever gets primary controls the narrative of how everything works with the relationship,
but everybody comes to these underwriter calls and you do a presentation on what's going on in the environment, what the revenue looks like, and all of that kind of stuff. If there's an opportunity to do that with your organization, please take advantage of it because that's a great opportunity to be as open and authentic as you can be within the confines of a one-hour presentation that we come in, we ask a couple of questions, but it really gives us wonderful insight, communication, communication, communication. This is a relationship just like every other business relationship and that back and forth is going to be what's most successful. And then let's talk a little bit about this this opportunity called
loss control. um loss control or proactive risk services or a lot of other terms for it in different organizations is partnerships that we as the carrier have made with cyber brokers or cyber providers or cyber vendors and you could potentially have discounts. You could potentially get access to services that you may not have access to that will help improve your environment. So I know at one point it in my last role if I was if I talk if I used this carrier and I used their incident response provider as my MDR I got my incident response retainer waved which for us would have been a $50,000 savings on annual and that's a big revenue saver. So then you
go hey look cyber security saved us all this money this year by partnering with our insurance carrier and then that's great for everybody. But there's a lot of those kinds of benefits that really do help and we recommend that you do that. Um, there's going to be other partner benefits and it depends on the carrier and it depends on, you know, what you want and what you have. Sometimes they're great. Sometimes it's going to depend on your environment, your size, your uh your maturity. You may not need much of them, but there's always probably one that you're like, "Oh, that's really great." So, now for what everybody came for. What are we watching? and and what's
trending in the in the world this year. So, thanks to one of our incident response partners, uh I was able to get some insights from this year alone. And so, our incident response partner does have a a small set of businesses that they work with and a certain business size. But to date, as of writing this presentation, they tend to deal with three different areas: forensic investigation, business email compromise, and ransomware. Now you can see 15% of their opportunities are forensic investigation and that can just be anything from you know somebody sent an email to someone and shouldn't have to somebody is committing fraud to being part of a business email compromise or ransomware. So in their report they list
off all the different industries that they've had access to working with over the p or in the past seven eight months and these are the top five that they've come up with uh by percentages. So healthcare and social assistance, professional technical services, manufacturing, public administration and education are the ones that have been hit with ransomware this year with this uh organiz with this organization as an incident response provider. That doesn't mean no one else is being hit. We all know that a lot of other organizations are being hit. This is just what the data is showing us from this uh partner and from their volume. That doesn't mean you're not you should forget about it if
you're not in one of these five. Please still be diligent. But it is interesting where we're seeing the cases. And for business email compromise, whether it's a fishing or a vishing or some kind of fraud, um we're seeing professional services being one of the biggest, finance and insurance as well. We know um I got an email this morning saying hey if uh if it calls you it's not IT uh public administration healthcare and social assistance and manufacturing as well. Again this is just this year this is just through our one partner but it is kind of fascinating to see where everything is kind of falling out and what what organizations uh are really being targeted.
So I'm going to take a second here before talking about our claims trends to talk about the legal and regulatory landscape because a lot of what we do see is the regulatory landscape and legal landscape being part of our claims histories. So a few years ago Illinois set up the biometric and genetic information and privacy acts. Um well Illinois had biometric and then there's the genetic information and privacy act. So this basically means if you are using fingerprints or retinal scans or any sort of biometric data and you're storing it somehow, you have to be protecting that data. And if you're not, Illinois is going to come after you. And in the future, you know, if you're
protecting genetic data like certain vendors who we look at family history on who might have had a breach, uh they could be fined as well. Uh there was also this law in New Jersey called Daniel's law. Unfortunately um an individual found a judge's contact information through public info and went to their house and killed her son after a case. So they imported this Daniel's law which means that any law enforcement individual or a judge, any public officer, their information cannot be shared publicly in New Jersey. And if you do share it, you can be sued for that. There's also at least 20 in counting state privacy laws and we're seeing more privacy laws coming into
effect globally. So those are going to be taking effect. And then of course our fragmented regulatory space. We know the SEC put out regulations. We know that's changing uh state and national regulations are changing. And then of course our industry specific things which are also in constant flux is what we know. So we watch all of that very closely because those things come in as claims in the future. And so to date, since we've started tracking these different claims, these are the claims histories that we've seen. So for BIPA, which is that biometric one, we've seen 163 claims, which is not a small number. For tracking technology, for your your Metapixels, all of those things where
like Meta puts a cookie in and tracks you wherever you're going. We've seen a large claim volume for that. A few years ago, we know about the Move It vulnerability. Can you believe people still haven't patched that? Fun fact. Um, we've had 154 claims. Uh, we thought and as everybody did, CrowdStrike was going to be a big problem. It has not been as big as we anticipated, thankfully, as well. We all know. Uh, but we have seen 99 claims to date on that since it happened last year. Um, and then Snowflake happened. We thought that one was going to be a bigger deal. And I think a lot of that was much more people are going after the individual
vendors, which is great. Um, and then CD Clay Global was an auto company. They do the loan processing paperwork for um for uh many many car dealerships, but they also do it services and a whole bunch of other things. That was a big outage. They paid a very large ransom. Um, but we haven't seen a ton of claims out of that either. Change healthcare, another one we thought was going to be big. It's sizable but not crazy. And then Daniel's law, we've seen about 11 claims on, which for a small state like New Jersey is still not a tiny amount. Of course, other things we're paying attention to is supply chain attacks. Um, I think we've all thought that it's
just the vulnerabilities in our our applications, but really it's even our managed service providers not doing their due diligence. And of course, who doesn't love XKCD? It's kind of the best comic about this where again a project some random person in Nebraska has been thankless me and maintaining since 2003 could go down and take the entire business out and that happens a lot which is why again go back to the business impact analysis not just for your on-rem stuff but all of your managed service providers as well and then it's 2025 so I have to talk about AI for a moment u everybody's watching AI I think one of my biggest things that I've noted noticed is we're
still in that governance phase. We're still trying to figure out how to educate [clears throat] our people and set the guardrails. So, this is kind of a best practices that I had put together about, you know, watch for hallucinations, don't use AI generated images because that can be a legal regulatory problem with media, be transparent, look for bias. Um, I think next year we'll see we're starting to see where vulnerabilities are starting to come into play. We're seeing injection attacks happening. OASP has their top 10 for AI vulnerabilities. So, this may not be the slide that I would use for this in the future, but it is something that we're paying attention to because it is going to change the threat
landscape in the future. Even though AI in many cases is just another piece of software in your environment that you need to protect. So, that's cyber insurance in a nutshell. And again, ask me about my quilts. Um, do you have any questions? Please feel free to use the mic if you do.
>> Okay. >> Hello. >> There you go. >> Okay. >> Yeah. >> Uh, so I'm that guy with way too many questions, so you can just tell me to stop whenever whenever needed. >> Uh, okay. Three things. All of these are what makes a bad cyber policy, what makes a bad customer and what makes a bad defer provider like a vendor. >> Okay. So what makes what bad? >> Uh so in your your opinion uh just let's take a cyber policy. So if I'm if I'm working with a new customer >> and they already have a carrier >> and we're looking over their policies, right? What are things we should be looking for in your opinion that make a
bad cyber policy? >> So in order to get good rates, it's not really about the policy coverage. It's more about, you know, getting good good premiums and and getting a good coverage. Um, one, you know, we start with purchasable ways in. Are you doing MFA? Because not everybody is. Uh, are you patching your systems? Are you taking care of the things that people are using to come in? Um, and it's not just, you know, we're not going to say you have 400 vulnerabilities. We're saying, do you have 400 vulnerabilities and 300 of them are being actively exploited. So really understanding what's going on and taking care of that kind of stuff. Know where your assets
are. Know how you're protecting all your assets. Uh, then we look at, you know, what's going on culturally in your environment, how you're, if you're resilient to an attack, like if you have an outage that, you know, if somebody tripped over a power cable tomorrow, how would you respond to that if you didn't know it was a power cable? How fast can you recover? That's going to be a very important question that we're going to ask. Then are you managing your vendor risk is another thing that we look at. You know, if you aren't managing your vendor risk, you're going to be in a whole world of hurt, especially now when we all rely on
people and people rely on us. So, we we have five lenses that we look at a company under. And those are some of the big high points that I would recommend taking a look at. >> Appreciate that. Uh, also, what makes a bad customer? firm. You kind of touched on some of those things, but how do you know when you're walking into a new customer that it's just all the red flags are there, things are going to go off the rails? >> Oh, that's a great question. Um, I think it's going to be dependent on what we're seeing in the landscape. Again, looking at all of those factors, but also if I ask a question and you say none of your
business, that's going to be concerning. or if you think that's not a concern for you and you can't justify why that's not a concern from a risk perspective, that's also concerning. I think if um depending on the size of an organization, if they don't have somebody taking accountability for cyber, that's also very concerning. And then if I see year after year you're not making improvements, that's also crazy. So, I have to stop now. But, uh here's my contact information. should you like to an ask and answer any more questions. Thank you so much. >> Thank you.