Rootkit Kernel: Game Over for Security? #shorts
Show transcript [en]
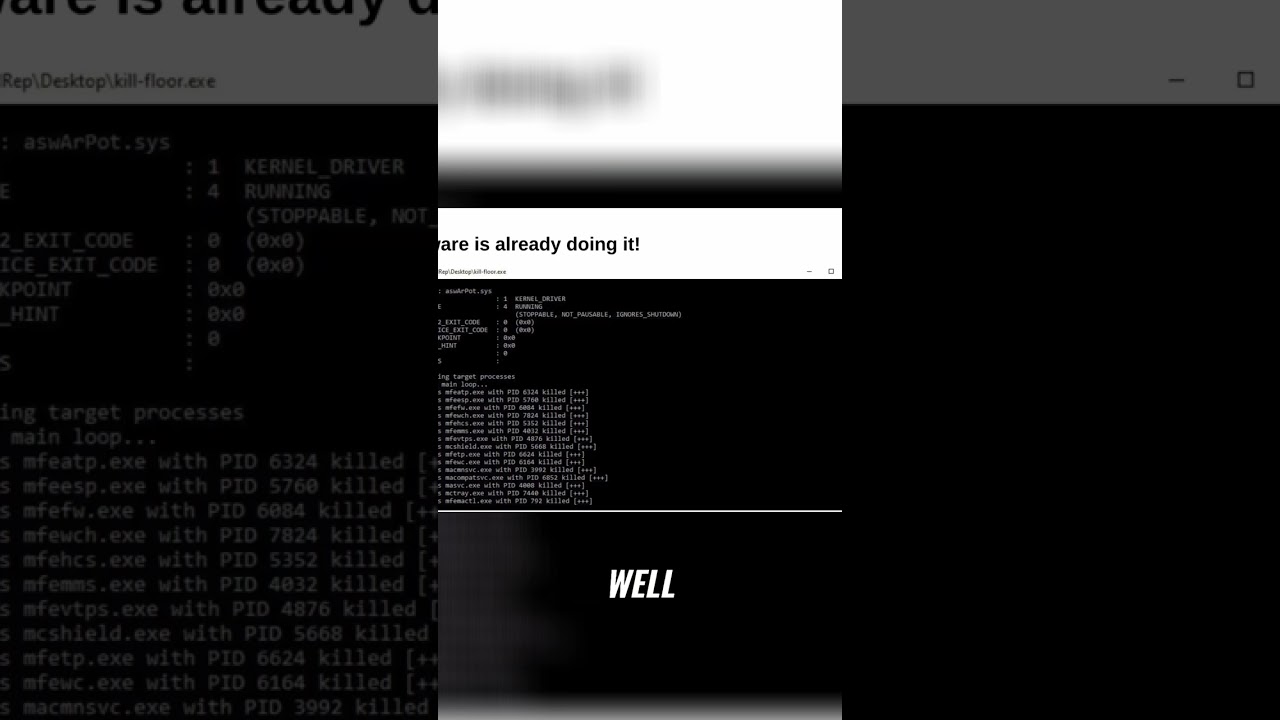
That's why uh a rootkit on the on the kernel is basically game over. You have full power of the computer. There is nothing else besides that. Balware is already using it. This is like six months, eight months ago. Um and it's going for long. It's not just now. Um this is from the Abbas uh anti-rootkit uh driver and you see that is the driver and then what this malware does. So basically it's a malware that you get infected and then this remember I should say that you can only load trusted signet drivers right well the Abas is trusted and is signet and is installed in a lot of computers so that's why they they bring
their own driver it's called a bring your own driver uh that's a technique so basically the malware would load that driver yeah it's a little bit of a malware deast but it's going to use the anti-root kit from abust the driver to run terminate process from the kernel using the ABS driver right and this ABS driver is able to terminate the process at the kernel level effortlessly bypassing the temper protection mechanisms of most antivirus and edr solutions





