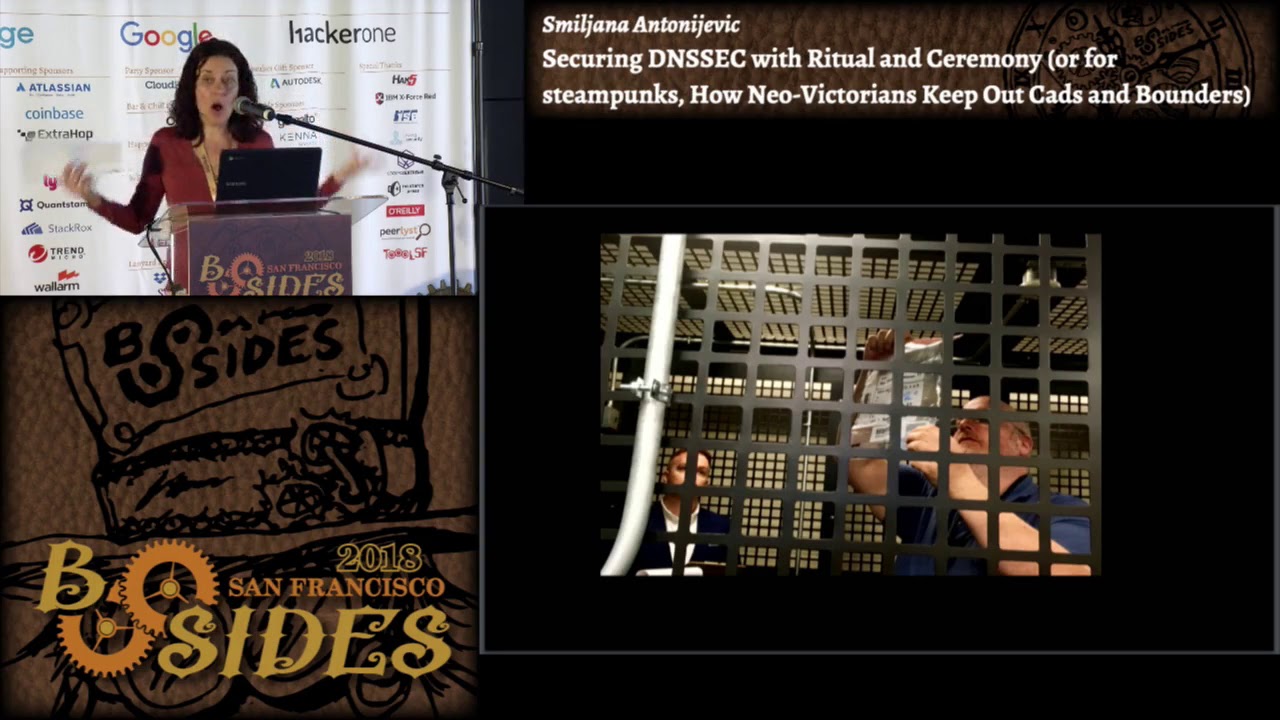
Securing DNSSEC with Ritual and Ceremony
Show transcript [en]
[Music]
hello everyone my name is Milian antonovitch and i have to say right away that I'm an anthropologist so just please keep that in mind while you're listening to my talk this is my first time at the security conference I'm really glad to be here and I'm grateful to all the organizers and people who invited me so I would like to start this talk with a few pictures and with the question what are these people doing so in order to try to answer that question I will look at two case studies of an anthropological ethnographic work that I just completed and those two case studies are packet Clearinghouse which is here in Berkeley and then the
Internet Corporation for Assigned Names and numbers so I've done my topological study and ethnographic work in those two organizations I observed and studied both technical and social aspects of their DNS psyche signing ceremonies so there is you will see that I will use those two terms ceremony which is the term that comes from computer science and ritual that comes from anthropology so let's look a bit more closer into those two terms in computer science as I said they call it a ceremony and this term was coined to basically describe social aspects of a key signing operation it extends the concept of network protocols as to include humans as nodes in the network also while network protocols established standards
for communication among network devices ceremonies regulate human communication with each other and also with other nodes in the network as for DNS a key signing ceremony it is a cryptographic procedure in which unique unique pair of digital keys are generated to sign DNS data verifying their authenticity and integrity I usually give this talk in front of a social science audience where I need to go into much more detail about this I trusted here I do not need to explain that further so let's see what is it the day in computer science call a ceremony we in social sciences in anthropology would call a ritual so basically whenever you are faced with deliberate social behavior whose purpose you cannot readily infer
from participants acts so when you're asking what is it that these people are doing you're usually dealing with a ritual and it can be something as common to us as a wedding ritual that is presented here to us it might might seem pretty clear what is it that these people are doing but try to imagine that you're an alien who just arrived from some exoplanet and you're suddenly looking at you know two people who are exchanging some rings and saying some words and there is another person telling them what to do and what to say so there is no clear instrumental function to that and it makes it unclear what is it these people are doing what
is the purpose of that so that's why that kind of behavior sometimes appears useless or even worse however rituals as we will see have very precise and strong strong social function which is most of all to build and maintain trust among participants in a ceremony and also with those people who are their audience some of the elements which are common to all the rituals whether you're looking at the wedding or a funeral or Bar Mitzvah or anything like that so it is a sequence of synchronized activities which are performed in a special place it can be a church it can be synagogue it can be site intogen Itza and Mayan site or whatever it is commonly with the
use of distinct artifacts like ritual masks or knives and so on then it is also performed according to a strictly formalized sequence of activities which are predefined in the scripture and which are centered around a set of highly regarded values and goals the basically all the participants in the ceremonies share so please keep in mind that each of the rituals has these elements place artifacts scripture values and participants so let's look now how DNS SEC can be observed through the lengths of these elements of ritual so first the ritual place like every other ritual this one is also taking place in a specific location in this case we are looking at a safe room so in
other in other words the key signing ceremony cannot just be organized like okay let's go to a cafe and let's do key signing ceremony it is always an exclusively held in a key signing facility which has controlled access cameras every entrance and exit has to be recorded and and so on and this is only one element of different layers of physical security which are surrounding a key signing ceremony within the key signing facility is a key signing room which is the room which every participant can enter within that room is this cage which we saw here which is a safe room that only people in special roles can access so then within that special safe room our saves which are
hardened against forced entry and which only special people like security controllers can access within those safes are enclosures which are again which have special each of the crypto officers and security controllers has a key to access them and within all of that is a plastic bag now since this is not just a common thing these are not common bags these are temper evident bags which are used to store special artifacts as we will see so altogether we are looking here at all those different layers of physical security from facility to tamper-evident packs so we saw here watch what each of these layers of security contains enclosure is within us saving is within the safe room safe room
is within the facility so now what is within temporal evidence bags the artifacts so again like every ritual and every ceremony that has special artifacts the same is also the case with key signing ceremony in this case those are technological artifacts that are the core of that ceremony HSM smart cards and laptop without hard days you probably all know that HSM is used to generate the store the key smart cards are used to unlock and operate the HSM and laptop is used connected with HSM during the ceremony and it has to be without hard disk so that no keys cannot leave HSM so now all of these special artifacts can be accessed and operated by special participants as you can see
here there is a whole group of people who basically have to come together to participate in that ceremony of generating it the case of and safeguarding particularly important are people entrusted roles crypto officers and security controllers you can think about them again like in every ritual where you have priests and so on so people who have those particular roles the same is the case here with crypto officers and security controllers they have their that their position is particularly important because they have the ability to affect generation and use of the keys so that's why those roles are particularly important what's important is that those roles cannot be held simultaneously by the same person so no one person can at the same time be
a crypto officer and a security controller the reason for that is that there is a very strict separation of duties and privileges more who has access to what in other words crypto officers have access to smart cards which are needed to operate the HSM but they do not have access to the HSM security controllers on the other hand have access to the HSM but not to the smart card so in that way even those people in trusted roles are not entrusted a full and complete control over all of these important technological elements and it is also important to mention here that crypt officers cannot be members of either PC age of I can neither of those ceremonies
which are organizing those organizations that are organizing the ceremonies and the main reason for that is that they cannot be subordinated and that's influenced by anyone from those organizations in other words they need to keep their complete independence and ability to act independently and to represent the community so crypt officers since they are not from those organizations how are they selected they are basically volunteers from the community of experts that are trusted by both peers and the constituency their knowledge of the DNS and cryptography is particularly important so that they can act fast and make real-time decisions during the ceremony however what what often came out during my study is that even more important that their
professional expertise and knowledge of cryptography is their personal character and integrity and reputation that they had in the community one of the reasons is that it is often believed that people who have particular prominence in the community can be difficult to coerce or to incentivize to breach trust that is put in their hands also important for crypt officers is to have passion for the Internet security the public good and for serving the community so here we see again all of those participants I will just go briefly to this ceremony administrator who operates the hsm in laptop during the ceremony and also really important develops and exactly the ceremony script about which I will talk in a minute in external witness
usually appointed by a law firm so it's a person who needs to verify everything participants identities serial numbers on the equipment on temper evident bags and and so on facility operator who provides entire logistics and also insures functioning of the audio/video system and representatives basically anyone can become a registered representative at the ceremony so it is very open a tendency policy which also brings us to another element of rituals and key signing ceremony in this case which is the values what are those values that all of these members share and are trying to convey through the way in which they are performing this key signing ceremony participants style and transparency those are really two of the
most important social aspect so basically as I said everyone can participate everyone can there are also a lot of people who are observing the ceremony online it is being live stream anyone can rise a question and say hey listen I think that I see a problem here can you please pause the ceremony and tell me what is it that has just happened here and everyone's considerations will be taken seriously and will be answered now I have to say that it is Impulse important to not to mention that only crypto officers can actually make the decisions if something needs to be changed in the ceremony if an exception to the script needs to be made so in
that way it is a participatory but yet controlled task everything in the ceremony other than the keys and credentials needs to be as transparent and as possible and there are different ways in which that is being done one is that each of the ceremonies steps is read out loud each of the temper evident bank numbers serial numbers of the equipment hash and so on so everything is read out loud and recorded the entire ceremony is fully audio/video recorded with several cameras that cover different elements live stream and recording is also made publicly available after the ceremony so here for example we see a camera that is showing us security controllers accessing the safe or here you can see
the the table has marked spaces where equipment needs to be placed used in the ceremony so that it has the best position for cameras here we are seeing as soon as those people who do have access to temper evident bags they are reading the back numbers out loud and then showing to the camera so that everyone can see the number and verified here we see that the ceremony administrator who is operating the HSM you see the camera which is recording each of his movements and what is happening with with the HSM so they're really trying to capture each and every element and to make it as transparent as possible you serve only script and the
scripture as I mentioned is one important element and the ceremony script is a vital document and one of the crucial elements of this ceremony it formulates each of the ceremony steps it really mimic details if you have ever looked at those scripts you will see that it's like pretty amazing how every step is described so it is really important because the ceremony is a complex process and it could be difficult to forget a step or to forget a sequence of steps and so on so following the script really ensures that all the steps are done and done in a correct order it also gives the standards to verify that each of the steps was really included and followed
in the procedure as it should have been and finally it formalize the ceremony activities which is another important element so true that formalization technical aspects of the key signing ceremony are structured and it's acted in that really highly formalized manner which arises from meticulous preparation and execution of the script so each of the ceremony steps roles and rules is carefully formulated and religiously enacted by the ceremony participants that creates so it's basically you cannot just come to the ceremony and act in their in a random way doing something that you believe should be done at that moment or in a way that you believe it should be done so each of the steps is pre formulated and you need to follow it
that basically creates a context which transforms individual behavior into a meaningful social action and that's something that helps us answer this question that we had at the beginning of this stop what are these people doing in my view as a as an anthropologist I believe that they're fulfilling the main social function of a ritual which is to embody and to enhance cooperation and Trust through that formalized and synchronize set of actions which are focused on shared values and goals in that way we see that those instrumental technical functions of the ceremony actually assume a clear social function this is also a very important point the second point so all the participants are actually performing those prescribed
roles and roles so it is not enough just to acknowledge ok I understand these are the rules that we need to follow and these are our goals and values the really important thing is to act them out and that's why the ritual is often described as the basic social act but because it is not just a symbolic representation of a social contract it is actually the enactment of that contract so finally I would like to end with this I hope that studies like this can show us I know that in security industry humans are often viewed as the source of all trouble so had it only not been for users everything would be great however I believe that we can also see
humans as a potent power for the enhancements of internet security thank you if you have any questions I would be more than glad to answer
so we have some time so if you have any questions please raise your hand
thank you enjoyed the talk there's a lot of it seems like there's a lot of transparency for the key rotation ceremonies and all of that is they're similar transparency for the use of the private keys once they've been generated you know when they're when they're signing the top-level domains and things like that when they create a new top-level domain is there a similar ceremony that that is used in order to authorize that to my knowledge of their ceremonies are enacted in the same way and they really keep that they kept telling me that really everything bought the keys and credentials or like the safe combination and so so that everything else needs to be really very
transparent because they want to create a situation in which like nothing is you know opaque to the community and that also everyone who is interested can verify their ceremony and can redo that sequence of effects okay I thank you