Data Appropriation Through Org Infiltration Using Enh Integration & Truth Manipulation - Sash Rigby
Show transcript [en]
thanks very much so it's pretty impressive introduction yeah quick thanks to the organizers and volunteers for getting besides Bristol off the ground pretty impressive today I'm going to be talking about this stuff or physical red teaming and realistic attack scenarios so in truth what that really is is dressing up breaking in telling fibs and hacking as much as you can so today I'll be talking about kind of how we get into the buildings and warehouses and different properties and less so much about the techie bit about what we do once we're in so I'm the technical director and co-founder of modok's we are a boutique consultancy based out Bristol delivering pen testing check testing technical
research but we were lucky enough to work across telecoms finance UK gov and we kind of hack all sorts of things from servers to boats to 4G networks to bank ATMs shop kiosks voting machines whatever we're trusted with we kind of get in and have a good time so this is two of our guys tom and ben with big smiles on their faces afterwards spent ten days up in north of Scotland hacking an automated ship which I'm sure you can guess was amazing so that was naturally a Red Team and that was more of the technical penetration testing what we could do with the ship so if we could hack it so if we could take it somewhere
so this is meet technical director so I started out as a software developer after finishing University yesterday music legal on up and I realized pretty early on that there weren't any jobs writing music for film so I decided to learn how to code while I was in university got some freelance work and the company I was working for got hacked and I was really interested in how that happened and surely after moved into security and I've been working in security for well over ten years now I lose count yeah same as a lot of people here kind of it helps to have a bit of a cheeky side as well and yeah I'm sure as you know
there's a quarry a lot of hackers in the room kind of helps if you can build a career out of it so this is me last slide is poori obvious that passes a bit photoshopped that's okay so is that one and so is that one and so is that one so it doesn't really matter how good your photoshopping skills are you can kind of use a lot of pretty loose techniques to kind of appear like you're where you're supposed to be just with a simple pass and a lanyard so I like to carry quite a few it's a four on site obviously distraction as you can so when we're going on site we do take as many of
these as we can get so missing a purple one if anyone's got perform in the market for a purple lanyard mum for a job that's coming up so this pass actually I did tell a lie is not photoshopped this pass was made on a machine in the clients reception and they were kind enough to put a camera in so it's supposed to take your photo and print out the past and I held up my phone with a picture of Super Mario on it as it took the photo and then entered my details in and because the guys on the security desk is so used to just seeing these visitor passes sure enough when you walk up and you say our youngs
and hits a superior whoever they just swing the gate then you go on in and kind of starting to work so again it's not it's not crazy technical hacking but it's just being a bit cheeky and with this pass has certainly happened to us twice were security guards have actually approached us and said excuse me you kind of seem to be in the wrong area with this pass we were sat outside the CEOs office in a couch area and we thought it was a breakout area just for all staff and we had kind of antennas trying to get pick up the wireless signal and the receptionist for the CEO asked us you know what why you sat here and called
security over and the security guard first thing doesn't grabs the pass and he sees the name and the logo that was in the top left it says oh it's no problem yeah they're with us and just let us go about making the wireless faster so red teaming I'm sure you've all heard of it so why do we do it so it's important for us to really highlight key areas for improvement in the organization so a lot of organizations are going to have policies on how they secure their systems how they secure access to buildings and how they segregate privilege within their organizations it's really important that we can highlight those vulnerabilities but also we're going to be focused on
the gaps and everyone continually is getting focused on the controls and everyone's proud about the controls that they put in but it's our job to kind of rip up the rulebook and just say well actually you're smokers leave the door open every time on a Monday between 11:00 and we can just get in through that door so it doesn't matter necessarily about the policies and the processes it's really important for us to go and highlight those gaps that we see on the day we can change our abilities as well so a lot of pen tests are really quite tightly scoped so if we're given free rein over an organization and if that's globally maybe we can travel as well we're able
to chain those vulnerabilities to get into that first server and we're able to escalate up through the organization and really prove the concept that we can go from a real low access level to turning the whole company and of course it's a bit silly and we love it and it's great that we get to sell this kind of work so the approach is to focus on high risks so we're not really interested in cross-site scripting and a TLS certificate that's out of date on a server or you know maybe there's a barrier that lets you into the carpark we don't really care about this kind of stuff we're only going to focus and report on stuff that gets us in
to the company so a lot of the time we'll be throwing away stuff that we don't care about so we'll see a lot and it might be a security risk and it could be great to pad out a report but we're not interested in that stuff we're only interested in the stuff that gets us the quickest route into controlling the organization and is sample based as well so we're not sampling every door in an organization not sampling every server it's really just about picking where we think that we can use technology and weaknesses to get as into the organization and it helps us identify really weak corporate structure so a lot of these gaps in policy due to people
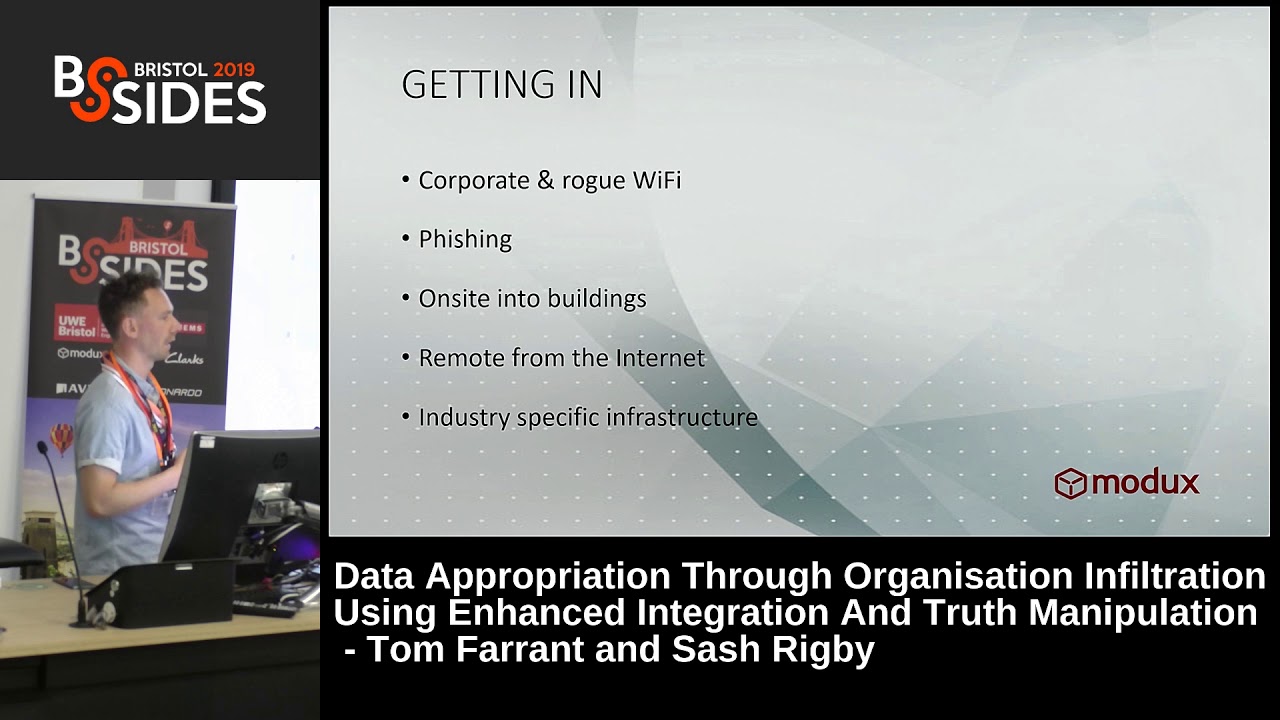
not communicating properly or people not following process that's the boring bit so getting in we can go in through Wi-Fi obviously we can try and hack the wireless crack hashes and the rest of it we can try fishing which is really successful we can go on site into buildings and we can go in through the internet and through industry specific stuff so like I mentioned ATMs and kiosks and the rescue it so problems with Wi-Fi it's quite time-consuming so on a Monday you walk around you've got to start collecting packets you've got to hope that people are connected to the right access points it can also be secured so using it can be secured with
a conversation you know we can ask the client bar using certificates using WPA enterprise and if they are then we can oh it's probably fairly secure up to a point but if they're not doing that then there's probably a way into the wireless network so that doesn't necessarily need a full-on red team but it can yeah why this can definitely be secured and actually why this is one of the main things that slows us up on the red team if there aren't any Ethernet ports and the secure wireless that can make it really really difficult to get access into an organization once we're in the building well come on how we do that lady phishing it works so inevitably if
you've got a large organization you're gonna get in through fishing so again we don't necessarily have to put that in our Red Team methodology because no it's gonna work and we can work with the client to understand how they're going to potentially be fished and what things that they can have their email boundary that's going to help stop them getting fish we were running a job two weeks ago for a very strange financial investment firm out of Paris and they were a company of only about 150 people and even within that 150 people we had two people finally open the final payload so you know if you've got that is approximately you know 1/2 percent of people opening
it in a larger organization that's definitely going to get you in so time well-spent compromised through buildings again we've got a hundred percent success rate of getting into buildings and then getting onto the network following that web applications for larger organization this is a really really brilliant way in because you can start to fingerprint the organization from the internet and there's no real way that you're gonna get caught or detected in that initial fingerprinting stage so you can spend a lot of time just crawling the web sites understanding the technology they have and again eventually you will get in and through industry specific technology so we one of the most alarming projects that we did in 2017 we were able to
compromise a large organization through the 4G network that they provide and we were able to do that globally as well so going in through the user equipment through the core network and onto the enterprise network and we got domain admin ultimately through the user of Gooden and again a lot of these things is about persistence so if you can kind of spend enough time trying to get in through something eventually if you've got enough knowledge you will eventually be able to get in so today I'm going to be focused on physical security so we're looking at getting into head offices branches and shops data centers and third parties so head office obviously this is often more secure than a lot of
the other locations because people think that's where their crown jewels are also forgetting the fact that network kind of leaves the building branches and shops can be a great one because then you're up against staff that maybe haven't been trained in the same way as people in head offices so we've been able to get into the backroom caps of different companies that have shops and going through kiosks and things like this and get access to the enterprise network and get domain admin whilst the SAC you know in hive is in the back of shop and then it's I mean it's not necessarily a fair assessment of training and awareness but it's because you know maybe because I knew that day
or but actually it helps highlight the network's to get the segregation from the shops and it's kind of highlights a lot of the different layers within the organization and potentially need fixing data centers are getting harder and harder to get into I mean you can dress like a techie but still a lot of the time you'll have barriers that are kind of weighing you or they're using iris scanners and the rest of it so they're getting harder and third parties is a great way to compromise an organization if you can get it signed off that the third party's in scope and get that agreed then that can be a brilliant way so there is stages again if any of you
are pen testers or you know you've seen pen test reports there's a lot of the similar stages of how we're getting into the network when we're using physical means so from our point of view we're often working with large organizations that based out the UK but they are global as well so for us when we're picking a target we like to pick if we can at least some of the countries that are maybe not as advanced technologically or necessarily in their security attitudes so even a country such as Portugal their attitudes can still be quite different South Africa has been an amazing country that we've worked in multiple times for different companies and in those kind of countries
you can kind of walk up you've got the English accent and you walk up and you just say oh hi I'm from head office I forgot my pad can I get in today and they'll just open the barrier and send you up to security to get your temporary pass so I was I've actually had a pass issued I needed it for a week and they issued it for a month just in case the culture can be really different as well so people are often a lot more relaxed in these developing countries where maybe they they've seen that they can just send reports back to the UK and say everything's a-okay and actually on the ground everyone's chilling out the
barriers are permanently open everyone's just saying hey yeah come on in and you have a good time in advanced countries especially in northern Europe people are a lot more polite so even if you have got your past lives touched away because you haven't managed to print it or even if you have got something that's a little bit of mist maybe you're landing on to the wrong colour or maybe you are in the wrong area people are still a bit too polite so in Germany and Netherlands we see this a lot where people won't confront you and you can kind of ride on that subsidiaries and acquisitions are our favourites so any company that's been recently bought in the last few
years they'll really have a lot of cultural pushback and they won't want to integrate culturally into the organisation but their parent company would have still wanted to plug every one in put them on the same email account to get the branding sorted but at the personnel level everyone kind of thinks they know better and they know that you know what these rules that are coming down from head office aren't necessarily right fit for their company so again maybe you are from head office or whatever your back story might be you can definitely use that where the the subsidiary hasn't quite adopted to the security policies in the way of working that head office would prefer and again
with the subsidiaries point productivity is the main goal right often so you know it's really important that everyone's just getting plugged in and we can get working everyone on the same system so productivity is probably one of the main things as we all know that actually slows up security and people might say it's the other way around sometimes so another way to do recon we've all done it before we go meeting or we go on site we're using Google Maps or Google Earth to kind of give us a heads up so this was a bit of recon that I did for a hobby job on the weekend is poori not fair that I put up
videos of recon from any of our clients so this is a landmark in London that was actually able to get access to out of hours on the weekend and it's these kind of things you can just use a bit of open-source information it's kind of just guide you before you're on site to give you an idea and it's not necessarily gonna tell you how you're gonna get in it's just gonna help familiarize you with the building and give you a sense of what to expect when you're there and then this little video friends don't do this but you can if you but sure we can do what you want so another really really decent source of
information is the planning office so you'll get floor plans for most modern buildings from a planning office and even if this office has restricted areas or areas that don't necessarily need to be in the plans architects want to get those plans through and that's what they're good at so they'll provide as much information as they can to really help set the scene for what developments are going to happen in that building so this is one from actually Huey I didn't have time to find anything juice juicy unfortunately but you can see the architects love just putting as much detail as they can in so stuff that might not even be relevant you can help get a lot of information before you
arrive on site and again in the past it has helped us a lot maybe we see a fire escape connects to a door that goes to a basement and we found that some basements are connected to other buildings so we have learned stuff from planning offices that we didn't know being an outsider I'm not really sure what the remedy for this is because again productivity is important so it's important these companies are getting their buildings modified in getting the plans through but from a Red Team perspective yet just be aware that you can get a lot of information from planning offices another thing cameras more than 2.5 meters in height require planning permission so again this is from Yui
and they're planning on putting new cameras up so you can see the location and the direction that the cameras going to be pointing and again you might think well this is this getting bit unrealistic now but actually we do have security guards that are following us on cameras and we've spent up to 45 minutes before in fire escapes hiding from the cameras waiting for them to forget about us and hoping that we can kind of get out fire escape and yeah we've had some close shaves but finding areas that aren't covered by cameras has definitely helped us another brilliant source of information for getting inside buildings that you don't necessarily have a lot of information about architects and
interior designers they really want to promote their work on Instagram or on their website whereas the client our client and their client has Velen they might want to keep that stuff a bit secret so this is from a real job where there was no way of finding out the layout or the interior of the client's building but with a bit of research we were able to find the interior design and this this these shots did actually really help us get access to the building because what we've got here we've got a shared meeting space but we can see at the front entrance we've got receptionists so if we want to get into this part of the building we're
going to have to have a pretty good story of why we want to be in this space and this meeting room specifically connected to buildings via a glass walkway and we were trying to get onto the other side of this glass walkway and at that point we didn't know that there was another way in which we later found but we were very focused on this area so we knew that we would definitely need a producing backstory if we found ourselves here anyway we did find ourselves there and sure enough the security guard asked us where our password we've been able to get into the building without a pass and yeah this is kind of where it led to us hiding in the stairs
because we said our passes are on our desk we're just going to get them yeah and as I'm hammering the lift too close he's walking up saying oh yeah I'll come with you I'll come with you it's like no no it's fine we're going up to the fifth floor we'll be back we'll be back and then we ran down the stairs and hid for 45 minutes but at least we kind of knew that we were going to expect to be questioned whether you make a plan around that or not so I guess it's entirely up to you the same building from the outside again Google Earth we can see that the stairs are going to
lead up and from the shape of the windows we can see the windows are different on each floor so we kind of could somewhat surmise that maybe these windows are from that first floor and sure enough we understood where that room was going to be in the building before we were even there yep and shaking classic classic corporate vibes another thing is really important from these kind of things so we can see there we can really get a sense of the dress code in that building and again you want to blend in you if you turn up in a suit in some buildings you're gonna look massively out of place this is Ben and Dmitry when we were
trying to break into the 4G network hi this can go a long way but again as soon as you find yourself on a corporate floor with everyone in a suit is that really the most appropriate thing to be wearing I find that a suit with high vis it's kind of puts you right at the top because then you're that you're this you're the boss of the guy that's wearing high vis and you're probably doing something that no one else needs to know about so you can just go about your day full casual more and more that's pretty common dress code in offices especially you know if there's a technical company so again don't go turning up to a technical company
wearing a suit because no one's going to greet you with a friendly face and everyone's going to be questioning who you are and why you sat at their hot desk so on-site prep at the time is anyone give me a shout on time I'm good thanks so this is pretty much all we need to take as well as a laptop of course so we've got the Selphy printer so this is the printer that I print out classes so most of the passes that I take have been printed out in a cafe so this is about 100 quid and it will print out you can actually buy the the card shaped paper that will just stick directly onto a
blank then we've got the proxmark three again between 100 and 200 pounds you can clone passes with this so once you are in a building maybe you want to start bumping into people then we've got a Raspberry Pi for them by passing on a network or maybe we can create a bridge with that and then the classic Alfa another bit that is important if you do get into a meeting room and maybe you settle down you might want to lock your laptop up because we've had it before where we've not want to leave a meeting room because we've got a decent place to sit we've gone to get a bite to eat in the canteen and come back and our
laptops have gone missing so yeah lock them up if you can more importantly take your time so I say to everyone that's on the team it's Monday we're not getting in today whether we do get in or not on the Monday it's important to really dial it back and take your time and just watch how the organization works watch how people operate watch where security guards go and just have a coffee and just just become part of the space and just really chill out because if you go rushing in there and full of energy and full of hype you're gonna screw up this is a fire escape that we got in through and this was opposite a
coffee shop so we were sat just having a coffee and from the floor plans we already knew that these two doors went to different parts of the building but security guard on the right door with the uniform of the company we were trying to get into kept coming in and out and doing as from this door so we knew if we try and tailgate someone in a smoker or the rest of it on the left side we're going to end up in the wrong part of the building another thing we do is walk round and we take photos of people's passes so before we're actually in a restricted area we just walk around again taking our time
with a cup of tea and just take so many photos as you can of people and their passes hey yeah yeah yeah of course yeah I'll come onto this one in a bit yeah this is this is very very important photo actually yet so this guy's called Dean he was head of security at a company that we're trying to break into and unfortunately he's been tipped off that we were coming he hadn't hired us the word got around that there's some people there trying to break into the building and I have to put him in because it was hilarious watching him on the walkie-talkie operating trying to spot these hackers that are coming and I
managed to get pretty close and when he had no idea what a hacker actually looks like when they're trying to break into a building so this is Alex I asked Alex to send me a photo of him looking smart so I could make him a fake pass so thanks Alex so in the cafe I decided to smarten Alex up a little bit find a guy in a suit if I could so I mean not every suits appropriate when you're trying to break into a building but ya can smile now takes up here a little bit was a bit of Ryan Gosling so this was done from a cafe and unfortunately so this was using an
online program called Pixlr which is kind of an online photoshop so there's you know again it doesn't have to be perfect the work you're doing it's not going in vogue although this could it just has to pass the kind of passing eye test where someone glances down they're kind of like oh oh you work for us yeah he's a bit of jazzy guy as well and again so what we see in corporate offices as well a lot of the passes of really really simple because they don't need to be a complex design so more often than not they're pretty easy to forge and there we go that that was printed out on this printer and it got us into the building
and just helped us operate and just look a little bit more well maybe not a lights but I mean who wouldn't want that guy working for them maybe head of sales or something so yeah the reason it's that photo see if we got audio here hi Luke I've been the office and mother yeah okay yeah just with Luke up in the office and he's saying there's a 95 it needs to custom look at the printer can you give him access to behind the desk we'll give him whatever he needs okay pointy round in maybe five minutes I guess these are point engine printer and yeah just tell them that wherever needs it yeah okay cool very much so yeah at that
point we tried to get in through the back entrance and security said our maybe you guys aren't supposed to be here so I made that call so hence me taking the actual photo of Lucy's past and just called the main number of the office has to be put through to Lucy and the guy that answered said oh hi yeah Luke here having a health and then so he patched me through and I'm coming from the internal number to Lucy and said hi is that Lucy dams coming down basically and Danny was there for three hours just plugged into the printer and just doing what he needed to do and sure enough who's on corporate office network at that point
another way in a lot of you would have seen these keypads the if you ever see this keypad it's really really easy to bypass the same as you would on one of those combination locks of a bike if you put the pressure on the turn knob whichever is the hardest to push pin that's the foot the next one that you should push push so if you fully lock it on obviously press see first lock the dial fully on give it some pressure and just press whichever button is the next hardest in your workout the combination and the thing about those combinations is that doesn't matter which order they go in so people often or list is three
nine six wherever that one was it doesn't matter the order you press them in so you just lock it on and just find whichever is the most firm and it will the next one two pushes it'll be really really different to all than the others so yeah that's pretty typical either if there are no locks that you can easily bypass again a hotel card or some other card that you don't really care about can be used to shim the lock so this was in a car park in the basement of an office in Munich again luckily I don't know if it's Germany or the privacy thing but there was no CCTV in the car park so just spend five minutes trying
to bypass this door and got in through a fire escape door and then we were in the office and then once we're in we spend a lot of time in basements poking around looking for things that might be of interest and again a lot of these really large buildings have quite industrial basements where they go through air and water and the rest of it which is so yeah of course so this network did actually give us corporate access but what we were also able to do this the red roots are there that had internet access so we were able to bridge the corporate network to the Internet if we wanted to to give us decent persistent
access that way these boxes were all empty cardboard boxes in the basement on another job and again what we were able to do here is take Mack address from that Mack and clone the MAC address and of course Maxon attached to the domain as easy as Windows PCs and so that helped us authenticate to the wireless just on a Mac whitelist so you got once you're in keep your eyes pealed right and keep your technical mind on and be like oh well yeah we've this might come abuse yeah more basements can be a bit boring so we really want to be where everyone else is just upstairs smiling and getting a cup of tea it feels really
good once you're in but it comes at a bit of a cost this was Danny's heart rate after a security guard had been chasing his round Danny hadn't run at this point whatsoever I'm sure he has in his life but at this point we still just walking around the building and his heart rates up at 140 so even though we're kind of allowed to be there you've got so many doubled lies going on in your head it's hard to keep track of what's going to happen when you do actually get caught so the main challenges once we're in for the techies it's going to be obvious so Ethernet access network access control and kind of drifting into the wrong area
the biggest problem is food so prep and make sure you got snacks in your bag because you're gonna get hungry and once you're in maybe you get into an area that you can't leave or if you do leave it's going to be difficult to get back in that area so take snacks and settle down somewhere and make sure you've got enough for lunch and a decent afternoon snack so getting around the ethernet security a little bit of techie stuff before we wrap up so often printers are a bit more done than the rest of the devices on the network so we're going to have you know mschap wealth education and network access control on the
network that's going to slow us up from plugging our own laptops in what we can do is plug into a printer port often clone the MAC address of the printer and it's going to help fast trackers on to the network and of course people need to see that printer so we're going to have direct access to if nothing else at least workstations so there we were plugged in and on that printer luckily in that area there was an out-of-order sign just knocking around so we just put that on the printer and people coming up trying to print and because they thought we were the print team we were getting roped into helping people print their
work from the other printer and the hours really held my bets at 14 trying to print a word documents down hard so yeah you can see we're just plugged in and we're kind of happy as Larry another way getting around port security so you can actually configure a Raspberry Pi pretty easily to act as a bridge and that will help you get packets on the network whilst you're looking like a computer that's supposed to be on the network so you can put this in between a router and a computer that will authenticate to the Mac and you can inject packets onto that Raspberry Pi and they'll put it onto the network as a as the computer that you've you've had
authenticated to the port there's a we have our own scripts to do that and they'll power up the Raspberry Pi and look for a Gateway and look for packets but I'm pretty sure there's some stuff on github that all just put you in the right spot with that being in the right place so again a meeting room if you can book a meeting room out get it for as long as you can so just put the meeting room out for the week and you're good and because we're in such polite countries no one's gonna pop their head in no one's going to do anything so for this meeting room here we did it actually go
in through the conference system and we have this TV off the wall we have the cable splayed out for the whole week just so if you get access onto the network and no one disturbed there's no one said hey what you do in and the rest of it so we were all good building persistence so once you're in what you want to do so you can start cloning the easier cards that are left secure you can steal visitor passes if you can so if you can get to behind reception or if you can get to a spot in the building maybe there's a bin where people dump their passes at the end of the day just keep your eyes peeled for
any passes they're going to help you later in the week because that first time getting in can often be the hardest and once you know the building just keep looking out for ways that you're gonna get in on Tuesday and through the rest of the week signing in and friends as a visitor so if you can get one guy in and the other guys still stood in the coffee shop you can just walk to the barrier and just say hey Steve yeah come on in yeah oh yeah yeah can we get this guy in the rest of it maybe he's carrying something and we just get him in that way this is a video another funny story there was no
one in reception and we'd been in this building until about half 10:00 at night just taking out open computer so obviously everyone's laptops encrypted so we stayed in the office till out of hours desktops on traditionally encrypted so we just took our time hang around the office till they people start going home 9 10 and at 10 we know there's no one left so we just start going through the floor and just taking desktops apart plug the desktop hard drive in your computer and start getting hashes off the computer that way before we left the building I was like I'll just get some passes so I'm scoping out the reception and little did I know it
on the other side of the glass there's the night security just smoking watching me through the glass and I can't see her and she's just there like just smoking watching I don't know where she was stood anyway she comes bawling in like can I help you like oh yeah just looking for the exit and she's like okay yeah the exits here thanks very much thanks yeah yes yeah oh yeah and again no alarms will raise no nothing keep your eyes peeled because this girl left her pass in the food hop-up machine again thanks very much helps us out for the rest of the week so once we've got network access secured it's up to us
then go and do the techie pit the traditional pentesting and start you know running necess and you know what as pen testers do run their cisco cup of tea now what's actually going on there's a lot hard work trying to find vulnerabilities on the enterprise network we're scanning brain mapping we're trying to find those services again same approach we're looking for those really high impact high risk vulnerabilities that are going to get as into a server and then we can start to escalate privileges throughout and we want to prove further persistence so we want to take control of that domain and stay there as long as we can we want to be able to leave and prove that we got
in got some data and we got some access as well that we could take with us and make sure you get the evidence so that's me and Danny up there with two big smiles on in an office that we shouldn't be in so that was me any questions we've got time for questions questions okay





