Automagic your attack simulation - JJ Widener
Show transcript [en]
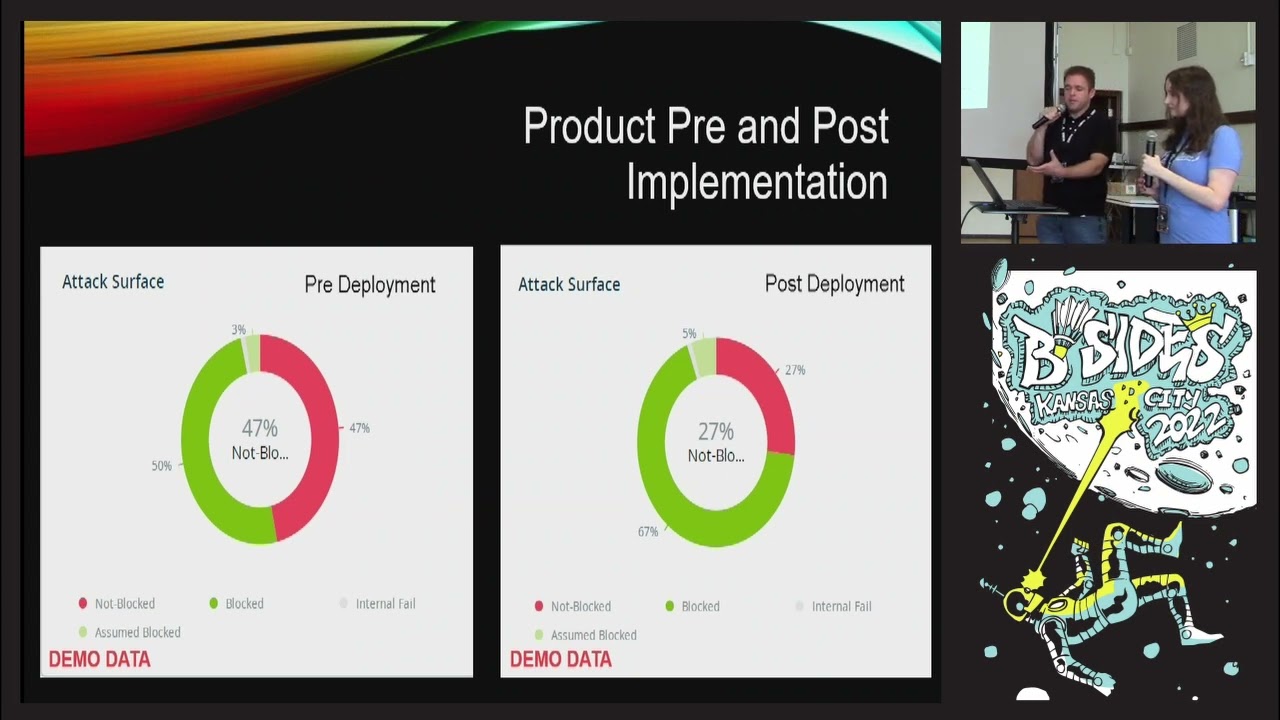
awesome thank you all right Welcome to our topic for coming uh to hear us today this is how you Auto Magic your attack simulation although there's no real Auto Magic to it but my name is JJ Wagner I was a former manager of blue KC of information security currently I'm a data protection architect at chemical Clerk and I'm Amy Harvard I'm a security engineer at the Cross Blue Shield of Kansas City awesome so back to the auto magic of your attack simulation so it's not really Auto magical there issues of the same tactics techniques and procedures that a lot of the threat adversarial groups are using is just packaged up in a system that can run continuously and automated in your environment so the tool that blue KC uses called safe breach it helps whenever you're a smaller team and you can you're wanting to launch something quickly you're able to get in and use an attack simulation software like this other vendors include attack IQ and Tara Veron and save reach so safe reach also provides you know mapping to the miter attack framework and also to investing 153 controls so it provides some good level reporting as well so I already mentioned it why breach and attack simulation software it helps augment some staff you know if you're if you don't have the size and capability of hiring a full red team this could augment some of that functionality where you're getting in and you're setting up the system to run those continuous attacks so whenever you're running that they have pre-made scenarios in there as well that you can do continuous security control validation you can have customized attacks so one of the ones that Amy is going to talk about is the Cisco attack back in August 2022 you know just about two months ago that within 24 hours the attack simulation was in the system so you can run that and provide a report so I'm going to turn it over to Amy that's going to go over some of the more technical details of a safe reach how it's utilized in UKC safe breach offers Integrations for antivirus and detection response vulnerability management threat intelligence and automation with these Integrations in place the simulations can pull the logs from those tools to tell the story of what that control detected in this example logs from Microsoft Defender and Palo Alto Panorama were found for the simulation once the simulations are complete an interactive dashboard is provided to review the findings and control status breakdown there is also direct navigation to detailed simulation results remediation tasks a miter heat map or Mobility data and dashboards shown here is a breakdown of how three security controls performed during a set of simulations so what is this uh graphic here for a Microsoft Defender actually showing this so what this is telling us about our Defender for the simulation is that only seven of the simulations were detected or alerted upon three were completely prevented and about 537 were logged by the security tool Defender but nothing else happened no no alerting no credential safe Reach maps simulations to the minor attack framework here is a look of part of that miter heat map and safe reach it allows for quick view of which tactics were missed detected or prevented this AIDS in determining which tactics need to have more Focus for alerting and Remediation so with a heat map Red's bad right yes green is good yes so if it's red that means we did not detect or alert or prevent that type of activity in green means it was fermented yeah what are the different colors so yeah red means that the attacks were missed green is prevented or stopped and orange would be simply just detected or alerted upon State breach offers analysis remediation of individual stimulators or you can examine the findings that will correct over issues over many platforms for example this finding shows that if we remediate 45 hashes it would affect eight simulators and over 5000 simulations so whatever you have the list of hashes here what would you do with these hashes that are showing up in the system to help prevent or help the simulation software or help the I guess the information security posture so I would take these hashes and set them in our EDR and point detection response and I'd block the hashes and then I would rerun these simulations to confirm that the blocking is taking place okay so so with dumping these 45 hashes saying to Defender EDR or whatever EDR tool you run the simulation again it's going to come up and say you know more are now blocked yeah very cool so the next part of this presentation is going to go over some more use cases how safe reach can be utilized or any you know breach of the tax simulation software can be utilized in a product comparison for pre and post implementation of systems as well so if you wanted to understand how is your system performing or how is it blocking you know you're able to run this type of a taxi in relation to to show that information she's also going to go over some Network segmentation tests that you can perform with with safe reach as well and of course everybody likes the knights who say nice so the nist evaluation if you don't know Monty Python I'm sorry if you know you should it's a lot of fun but then this reporting this evaluation for your security controls and then she's going to go into how you can create uh customized attacks within the system all right so not only can you attack your attack simulation systems help validate your current security controls but you can actually use them to test out and compare new security controls in this example one simulator was set up with antivirus a and the other with antivirus fee the same simulations were ran on both simulators and added and sorry we're at monopole simulators and added sorry I ran the same simulations on both simulators and added both to our scorecard as you can see here the results were pretty close between these two products this is why we always pair these tests with a well thought out scorecard to determine which product will serve Us best so with this this output from the system the scores are fairly similar what other criteria I mean if if you're doing a product comparison and it looks this close what other criteria would you use before making a recommendation on selection of a product right so in the scenario the products were EDR and point detection and response so you want to take into consideration ease of use of the platform what kind of hashes will the platform accept the biggest thing probably is cost and just usability for your analysts in another case we wanted to see how our environment would improve once a security control was implemented I ran a set of simulations on one simulator without the new control and then I ran the same simulations with the new control in place as you can see on the right chart the security posture was greatly improved you can see originally we only had we had 47 percent of our simulations were not blocked but after the new Patrol 27 percent were not blocked so that this information is gold if you're responsible for implementation of a of a product and you're wanting to show Roi and return on investment or your product that you just implemented and you're able to run a tax simulation beforehand and then afterwards and you're showing this type of data you know to any management or you know or anybody I mean it just makes you feel better that the product you've implemented is actually blocking board right yeah another great use case for attack simulation is Network segmentation monitoring I set up lateral movement simulations to run regularly to ensure our offshore segment has not had any network changes that would allow for lateral movement so in this uh in this picture you can see that 100 of the 20 over 23 000 simulations were stopped or prevented should I ever have this run and I see things are missed or logged only or detected I know something's changed in my network and I need to take action to remediate that since we are we cannot have data going to our offshore segment in in that activity could be maybe a misconfiguration or you know nobody's ever had somebody that just you know opens up ports or opens up access without going through proper change control and vetting so so this type of simulation might alert to that right or it could also move to malicious activity is that right exactly so yeah if you're if you're running this and all of a sudden something pop so how would this alert you would it send you an alert through the Sim or yeah you can integrate and have alert set up through your uh you know servicenow ticketing or you can get Gibson a recent use case for a tax simulation was the Cisco Network breach stay free stay free chat a scenario prepped and ready to run within 24 hours this allowed me to configure and run the test and provide a report to my CSO pretty quickly in this picture I show you how each scenario is broken at the steps that are configurable to whatever data assets or simulated simulators you want to test with on the right you can see some of the individual simulations that make up the scenario these include command and control malware drops configuration changes and malware transfer so the same tactics techniques and procedures for this apt I don't know how to pronounce that ransomware gang so this would actually be the the itemized list of the steps that you know for at least from say for each perspective that this threat actor in this adversary is going through to attack using this apt yes exactly okay so with these tactics and procedures so you were able to provide this to the CSO uh was it I mean it was like the next day right I remember I remember on a Saturday y'all for this report yeah we will see so right whatever happens on a Saturday so because you know so let's say Friday you know the scene the big CSO breach was announced and then you're getting in because you got pinged by the CSO and you hopped in here and like oh I think it was actually email they notified us and said hey The Cisco attack reach simulations within the system so you're just able to go in there and kick it off yeah it's easy to just click a button and run it yeah it doesn't provide you like a report like like a really nice uh management level report nice with graphs and like the speed zones and the greens [Music] yeah colors colors are good yeah all right safe breach offers fantastic recording that allows me to use all my data to create purposeful dashboards one area of focus for us is nist 853 not only do we have scenarios set up to regularly test nist controls but we also have the results on a dashboard that can be used in management reporting you can see an example on the left of the results for a configuration management scenario and on the right you can see those results broken down further into specific controls so so for implementing nist controls and we get a report like this and we want to go through and say you know we're gonna we're gonna Shore up our configuration settings we're going to get some config Management in here and we're we're going to implement some changes and we're wanting to get better at this nist control you implement the changes you know it's all going through change and controlling remove the changes and then you could say show show me what changes you Aid according to this attack simulation and how this you know this system is actually pulling up that nist data and it'll show you okay yeah now now we're we've configured the system better we're showing less red uh you know less orange or more green that these have been configured yeah and it allows management to present that to even higher management to say this is how we build programming I'm just saying we did it we can show that we did it company of the CIS like top 20. there are there are scenarios around CIS benchmarking and we do reporting on that as well okay very cool finally one of my favorite things about safe reach is that it allows me to clone an attack and make it my own many times we receive threat intelligence before it hits public and I can add those indicators of compromise to my controls build a simulation with those controls with those indicators and then I can run the simulation to ensure my controls are truly detecting or blocking some of the things you can Vigor within an attack would be hashes IP addresses ports protocols wait time and action such as opening modifying deleting okay so uh on the slide we looked at earlier where it listed out the APT list of things so could you copy one of those apts and make your own customized attack from them yeah absolutely can and let's say some new uh front intelligence comes out about oh here's some fresh hashes um it's not fully out yet to the public I can just take and add those hashes to the simulation once I've added them to my own EDR and ensured I set it to block and then I can prove out that we have prepared detecting or blocking okay so like if we're paying attention to the threat Intel Channel and they say this attack is similar to you know lapsis you know ransomware game or some other type of well-known apt but we added these hashes to that and maybe they have a team that's doing it you're able to get in to Safe Regents you know team doesn't exist to do this type of work and add those additional iocs hashes whatever and then run that in that attack yeah I can and it's it's so easy safe reach makes it so easy you don't need to have any coding knowledge I certainly don't it's a very easy interface to use it's simply uh click the field and add the hashes you want to you want to test is it a wysiwyg oh yeah that's cool so you can drag and drop and configure from that aspect yep so in summary you know small teams can benefit from a breach attack simulation software if you don't have the full-blown team to to go do red teaming a lot of organizations don't have the funding for that so it does allow you to you know expand the capability to run those automated and continuous attacks modify you know some apts modify some of the customize or create your own uh to run those uh those automated attacks as well it has a lot of reporting options which is great you know if you want to know you know how your system is performing against these attack simulations there's a lot of excellent reporting options out of that so I know from doing Red Team engagements or others performing red team engages the report writing as a significant portion of that so if you still need the reports from there or you're wanting your red team and you want to you know perform your own type of customized attacks that you're going to create and then it spits out that report that you can incorporate in your own type of recording I'm sure it can be utilized for that as well and then using those actionable findings to improve uh you know the security posture so from an implementation standpoint how quick and easy was it to to set up uh it's been a few years but it's quite easy you can even you can either set up a specific simulators in your environment specific machines or you can install the simulator on your machine or any active server without harm to those devices and you can kick off simulations right away walk around with your laptop and kick off a simulation and wherever it's cool all right well that is our talk so I appreciate every everybody coming out and listening again this is Jamie's first time so I'm excited to be here uh with her as we gave this talk as well so I will turn it over to Amy I just want to thank everyone also for being kind to my first talk and you can find us wander around the conference or on LinkedIn if you have any questions at all about how it we did with our implementation of breach and attack simulation awesome and here's the feedback slide so it helps us get better





