Whistleblowing how to by Nikita and Kenny
Show transcript [en]
that's definitely
hello everyone welcome to Oklahoma science Tampa 2023 so I'm excited to introduce our next speaker and Kenny Brown they will be given their presentation all right Transportation titled how to be a whistleblower exfiltrating sensitive materials safely they're going to save about 15 minutes at the end for questions but if you do have any that come up throughout the presentation they said you're welcome to ask them so without further Ado you kind of get started appreciate it thanks guys and again to reiterate if you guys have any questions about the presentation please feel free just to interrupt as needed everything so again the topic is going to be how to do a whistleblower um extra training sensitive material today please
open the Denture here kind of a disclaimer too think of this as the red team exploration type of exercise they're not telling you how to do it but we're just looking at it from the eyes and the Optics of being the best I don't know what to look out for um what we have to do this with documents as well as audio visual material
let's get ready some documents right very exciting so first thing that's important to remember is that every document does the Tracer every contact is inventory no matter what you do I mean this is a digital world so just assume that anything that you touch and interactions that you have with it is logged somewhere I'm not a person that looks too loud if it's not the system in fact a minute ago and they say that people do that and I'm not that guy but somebody is so don't worry it's out there so maybe this could be anything from access logs you know whatever somebody touches a file whenever you come through or anything it's not just you know just documents
it's a lot of different things print logs whenever you print anything even if it doesn't print it sits in school or forever it'll still have a lot of that so that's a good one um and then any other sort of miscellaneous thing if you edit a document if you have version tracking or anything on Microsoft Word they'll have your name everything associated with it so just assume that anytime you touch something let alone look at it there's going to be some sort of tree respondent out there and then again saving and moving stuff so if we save a document it'll have your name on it if you move it off if you want to copy it off of
your computer put it somewhere onto an external hard drive that's there every time you upload it USB device name that's not so I mean somebody can always dig back in and find out whose device it was once you're copied off so you're dumping a lot of data off your name I assume that everything doesn't Trace and on top of that things do even leave physical choices in the digital world so you know there's all sorts of things to stray marketing so if you look at highlighting the paper or anybody that has something highlighted by looked out for staple markets if there were Staples in there that's something that identified down the road if you had to look back forward and then
even like straight Printing and prevention so you use the crafting knockoffs donor to your printer I believe all the junk on there that sometimes a hugely effective footprint you can come back and find later next thing is micro dots anybody didn't expect that but that's the thing that is out there um there's an article here we'll sit inside afterwards but talking about micro dots and I'll run through just a quick little exercise about micro dots and then just to kind of demo it for people you can see okay ice cream um so we're gonna talk about this yes so six years ago or so there's this online newspaper article that came out um that leads the infernal NSA documents
if you scroll down a little bit we'll see that folks who produced the document there's some reactions there to you know the API um I know there's a problem here I didn't even see it yet let's try zooming in a little bit let's go to a little bit let's see 400 percent
not quite yet let's you know in this tradition of all CSI shows let's enhance [Laughter] don't take a screen capture of it and then we'll pop it over into Photoshop okay this is and those shows when they show digital forensics this is what it actually looks like taking a screenshot popping it into Photoshop soundtrack
these are the colors still can't see much of anything you can go and do some adjustments and mess with the brightness and contrast and the brightness yeah
so a bunch of little blue dots out there these are the real world example of what micro dots look like whenever you use uh generally any consumer grade color printer we're now even black and white printers they will have tiny little dot imperfections on the printed page and it's kind of amazing it's kind of like it's over and over and over spot one take it away it actually fills the entire quarter or sorry the header of the page but what do these dots actually mean it's about so the eff the Electronic Frontier Foundation actually taking any website if you scroll down to the code these kind of things and really all you do is pop it into
this interactive Matrix on the site you click submit and it spits out what we can see above in the sample and review we're not going to take the half hour it will take to type in all the little dots I did that once I'm not doing it again today but if you were to do it a Serial Network that also includes the main problems and the reason this is important of course is because if you are when we talked about access lines right and printer logs so now you have the date and time a document was printed out and you have the printer logs up who printed it at that particular time and there you
go you have your source the anonymous right and that's actually unfortunately what happened um in this story six years ago is the person who provided the documents ostensibly or arguably was de-anonymized um they may not have been used by Michael Doss here was a show of other evidence before example of how this kind of stuff that happens and to tie it back into the you know leaving the trace so just because you print something out they found were able to find out the timestamp of women printer logs to see who created something that should have given time to the time printed the documents possibly be the first doctor so watch out for things um maintaining possibilities if they
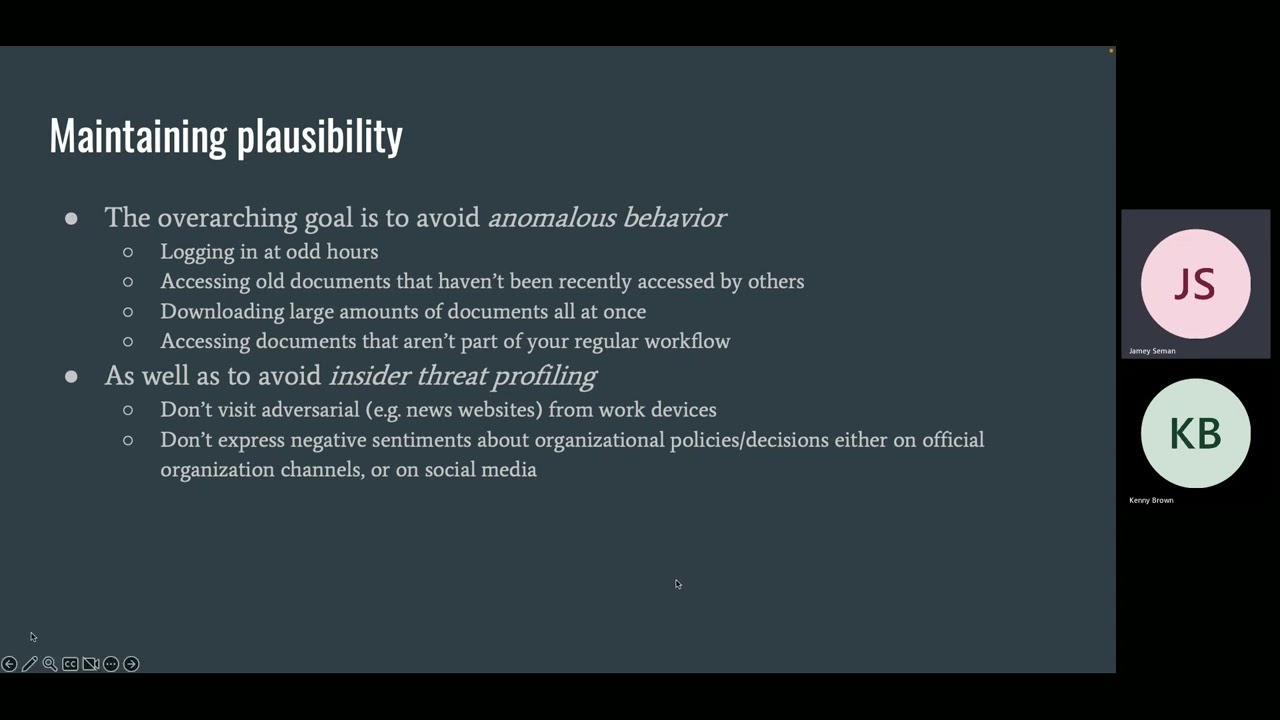
segue into that so the overarching goal is to avoid anomalous Behavior so don't do something absolutely it kind of sounds hard if you're trying to do this or whatever you're going to be one just kind of keep it within your regular day-to-day activities so you know don't try to log into things at 3am when you're at home you want to be popular but it's radar don't try to go dig up on documents or something that's out there and they're downloading large amounts of data like I said trying to copy things onto a USB version copy 30 000 documents that's probably going to raise uh accessing documents that aren't part of your regular workload so let's say
you're just a normal it guy and you're over there trying to open up you know Finance documents I kind of avoid that you're trying to be not promoting your promotions at all this is the red team [Music] so also working an Insider threat um so don't be adversarial so somebody just try to come and talk to you about it don't be the aggressive person if anything you just want to be your normal person you know himself be as calm as you can yeah when you're working your way through a regular system during the course of your work right everything like you open up your dots whatever you open up whatever files you need there are a slew of
secret tripwires hidden everywhere around the system that you're navigating that you're not seeing as long as you're not tripping them for even if you are tripping them we'll talk about that in a little bit as well and that's something you keep in mind is imagine that you're let's say looking through the paper filing cabinet right imagine the digital version of that there are a set of lasers pointed at that cabinet wherever you open a door closer take a file I put a file back in from photocopy have filed everything that you do in a controlled system that has a sophisticated intrusion detection system a loss prevention system an entire threat modeling system is tracking every little
piece that you do of sophisticated Insider threat systems do they track sentiment analysis if your company just had layoffs and you go on Twitter you know you these layoffs your stuff you're now flagged in an Insider threat system with a risk score that's the way these systems operate right if you express a sentiment in a private message on slack guess what your slack admin can read all your PMS likely has an automated sentiment analysis system that now flags that you and this person you talk to on your workers really don't like this new policy that was implemented right you're never going to find out about the shadow profile you have in your risk score unless something else happens that also
escalates that so for instance if if the printer logs show that you know someone printed out a document and let's say 10 people printed it out on that date and the document didn't have Micro dots but they did have printer access logs 10 people printed out a document that ended up in the Press of those 10 people one person went on slack and messaged five co-workers earlier on about the fact that gosh they really paid the Steve policy document right guess who's now the number one suspect for having paid that document that's that's just something to keep in mind is to avoid tripping all these sophisticated tripwires that I lost prevent your intrusion detection or an
Insider threat detection system would be attacked so don't do anything outside your normal behavior you've got to act your normal self and we're doing things honey documents are also worth mentioning something that has been added security people can grow up through your network across your different files and name it something that sounds enticing so kind of like a Honey Pop for you know browsing on the web so if you have any document name it something crazy like private employee salary negotiations or you know something anything top secret or whatever it's going to entice somebody to click on it and then you can at least have a list of people who go to double click on the documents that might be
totally empty but at least you then have a list of the names of people that are interested in that indicate this point you can kind of start to leave it into a narrative of all these other different items and things get down to a closing you know Source exactly like let's say you're browsing around your corporate Network and you see the spot called salary negotiations and you're at like take a peek right you take a peek whatever you think nothing of it you'll get alerted you know you don't get a note from security that hey why are you looking at this document really nothing happens but it get your risk score in that Insider threat modeling tool
whatever is going to be using the back end just goes up right and eventually the high risk individuals when the leak happens will be the ones who will be looking and scrutinize further and the scrutiny again keep in mind that we're talking about corporate networks here but the security oftentimes it extends into your personal life as well um sentiment analysis like I mentioned earlier is done on your private social media feeds um companies can subpoena other companies for your records right they can subpoena rule for your access cost to your private Gmail they can subpoena whatever phone carrier you have for phone carrier logs and now the private companies sometimes can deny those subpoenas but sometimes they can grant
them right the point is to never make yourself a target for them in the first place already and then we'll talk a little bit about watermarks so what Kenny just showed you guys the micro dots that's an example of a watermark right watermarks are these tiny big little beacons they can be text spaces numbers letters fonts anything the point of a watermark is to uniquely identify a copy of the digital item or a physical item for that matter and there's lots of broad tiers of watermark in the first one is white space monarching so this is very straightforward um musk famously um in the Twitter post I think a few months ago claiming that this has
happened catches Tesla leaders and what he claims to do is he puts either one or two spaces after a period right so you know a sentence can start either one or one space or two spaces and given the unique permutation done cleaning we'll talk a little bit about that in a second you can form a binary signature right like if one sentence has only one space that's a zero but that's just two spaces that's a one you have let's say a ten sentence email and slowly build a binary and identify right like zero one whatever and from that point on every individual email can be identified that's an example of white space farmer and we'll talk about how super all these
systems in a second said the next kind of broad class of honors are stylistic monomers these are things that change the style of a given one or sorry the given document that this means is one version of a document can have one sized font another version of a document kind of second sized font and you know you're thinking like oh like I'll be able to notice like if I look at someone's screen they have like a point eight size document 9 it was 16 science document that's not how the fighting how this works it's more it will be a one-tenth of an iteration right or 100th right these will be new imperfections that you're designed not
to be able to spot that whatever editing software you might not even spot but let's say you're trying to be sneaky um you open the document in Word and you check the font size right and it still says 12. what you're not seeing is that it's actually 12.001 as opposed to another version of a document that's 12.007 right and all these unique imperfections when taken together form and once again a unique signature that's kind of the purpose of all waterwork instant form this unique signature in whatever language you want to use whether it's actual code or if either it's the syntax the semantics of a document spacing it in the style of an audience and I'm not knowing kind of the
third big group of wine works are syntactic water works so what we call structural a lot of parts these are our watermarks that now begin to impact the actual text the document itself syntactic watermarks literally insert extra extraneous syntax into a document so you all know what Oxford commodious rate that third comment in a list after the word ends some editors love it some editors hate it some don't care about it watermarking systems level right because you could have a unique combination of commas in a document that would still be syntactically correct when we run through a part of grammatic parser let's be fingerprinted and then finally into the most pernicious class of one of us and what
we call nlw you want to work for natural language monomers so it was broadly known as semantic or just words responder marks and the way that this system works is it changes the actual sentence structure and these changes are made to kind of be meaning Less in the sense of they don't impact the meaning of their document right so the human meaning intact but we changed the actual word order so you know if you're watermarking at home right or even a novel this probably will not fly right but on the other hand if you're moderating uh it's General Corporate email they're very easy to do too I mean a trivial example that I always like to use something as basic as
the word order common sentence like yesterday they went to the park versus I went to the park yesterday right repeat those kinds of differences throughout the whole document and eventually you have an automated system for traffic so now that we've talked about the actual name is one thing so don't forget about Amazon delivery watermarks so let's do it in the middle characters there I don't think it carried over within the Powerpoints so um people can type letters and documents and things using different forms of us there it was originally uh it's okay anyone tell the difference between these three O's recipes with different sizes no no here I mean they may look different side you're
right in the absolutely PowerPoint present them but ideally there imagine movers same size there's something else off of yeah um it looks like uh space in the middle you think is smaller alone again all those kinds of physical permutations we're seeing is probably due to the way PowerPoint described it and that could be an example of a spacing Monarch but not in this case so the kind of Water Works up here are the hummus liquid Farmers so anyone else back there um
the character sets that we use that second o is from the Greek character set and that third o is from Cyrillic character set and that's what a homoglyphic attack is right is an attack where the letters look like Common Grounds like identical to each other and again if you have a unique combination of these for that signature yeah and in fact uh the very famous large tech company is known to use this method when sending company emails to catch potential leaders we'll get to talking about how to support the 2D systems in a second but of course you want to address like a couple falsehoods that people have about monitors so the first kind of thing that people
very very often tell me is like okay you're concerned about like if I get a copy of a document it's individually marked but what if I get a group email right what if again email that's set to my whole team my whole department or even all staff right surely that's fine to leave because it'll be identical right by definition it's sent to everyone not quite we're dealing with a sophisticated Watermark system remember that a group email is just an email Alias right an email Alias usually points to a list right you can have anyone you want in that list the less sophisticated Watermark system would do is it would remove everyone except that first recipient Watermark the email send it
subtract first recipient adds second recipient to the all staff list Etc et cetera iterating until every employee gets an offset email that is individually Tagged so this is kind of really key awesome everyone addresses don't assume just because something was sent to everyone that's no longer individually dead it's so very very doable to individually tag out because I'll remember an email list you don't actually see everyone right you're just seeing that all staff and you don't know the contents the membership of that all staff and another faucet too to kind of go back to what Nikita was talking about the different permutations of how we can do all the different watermarking things so it doesn't need to be complex in
order to find something to be really simple like he was talking about just the binary stuff in spaces more things and it's interesting how quickly this can kind of escalate in terms of the different permutations there are so in order to figure out how many of them can be it's basically x to the Y where X is the number of ways Watermark can be added in and then why is the number of objects that are being watermarked so for example we have one or two spaces like he was talking about we had 10 sentences you know and anybody I know we said it's a security thing but now you're now you're in a math class how
many permutations it would be uh 99 keep going not great so remember
how many different permutations can you have you have one or two spaces right so your X is two and if you have ten sentences it's 10 so 2 to the power of 10 exactly as you said so just for this so you can add on other things like you know micro dots or anything else that just keeps going out from there exactly and so we have the point bringing this up is people are like oh you know if you only have one or two spaces after a sentence if you can't Watermark exactly versions and if you have 5 000 people in your company and actually the scales very very quickly because if you add 11
sentences in Step 10 you gotta double it right and you have 2048 permutations and so on and so forth yep this one brings us to how you bypass some of the watermarks pretty obviously so we've talked about these different types of watermarks some are more sophisticated than others the good news is that some are very very easy to bypass they just require manual work that people sometimes are not very wanting to do so for the first two tiers of water where it's called blind space and stylistic polymers all one has to do to get rid of this is simply retype the text notably not copy and paste the text right because that would Preserve at
least some of the differences like spaces after it after periods and also depending on where you're pasting things in would preserve the different character sets right so when we retype the text we do mean retype the text we don't mean copy and paste and text but actually manually resent it and that's the thing is that these things are easy to do but they're time intensive which is what people are not thrilled to do that but it's also worth learning if anybody attended our class yesterday or our second session another tech individual uh it's worth noting if you do type something or retype it make sure the font that you're using is something that was within the time frame that you're
looking to use it for so if you're trying to link an order document make sure that the font that you have added is something that is time sensitive to them like when it's creating release exactly and so now we get to kind of the more convoluted wire marks like the semantic and syntactic ones so retyping the document will preserve it over these models right if they're what are known in watermarking surface let's be robust right robust means that you could kick it cover it with mud whatever it will survive and the same thing is true with stylistic in natural language modern works is if you retake everything you keep preserving the differences so kind of the point of attack here is to
do with some is a comparison analysis those of you who are comfortable over the terminal right you just do this diff ideally you know you would do a diff three which would there are three different versions of a document and the reason for this is let's say you have two versions of a document you do a diff analysis which is just comparing two different versions they're identical and so you think that's great my document doesn't have any watermarks what's wrong with that the issue that could be is that that document was watermarked not to an individual but to a particular team right or a particular subset of people oftentimes what Insider threat detectors will do is they will have a pool of
suspects let's say start off with you have a 5 000 person company you have a quote 100 people for your suspense why aren't they your suspense because going back to everything we talked about earlier they've tripped up multiple Extrusion detection and anomaly detection yeah that's right the access files out of work the access files an erratic number of times at around the amount of times they post negative things about the company on Twitter and now they're a high threat individual what that happens is that that group gets its own particular document right and when that group Compares that document within their own group they'll get the match right because the watermarks would be identical to that
one group but if they were to compare that with a third document from some from another department they would then find that difference that's why I said sometimes when if you're using the diff command in terminal use the diff3 is that you have three different versions that you're comparing from abroad a sample size as you can and a mid-star contrast to the Home Group then Canary traps is another thing that you should watch out for so an example of the whole hands email and you could get an email that says all hands and delivered to you with an attachment and assume that everybody got it but is the only single person again it looks like a larger group so you feel like
you're safe to link it out but then you're not because you're really the only one that has a copy of the document so kind of keep that in the back of your mind so you might just the only person that could sell dancing at the place that you know we've talked about different methods that a document can be watermarked but that document itself and on the meta level also functioned as the monitor um alrighty so we talked a little bit about documents and now we want to touch upon what to do if you're leaking let's say conference recordings so especially now if we've all had our share of Zoom beans right sometimes they were less great than others you know
maybe there was an Impulse to the assumed reporting right you're recording it on your screen maybe you're recording on your phone maybe you're using zoom's built-in it's important feature whatever there's a number of concerns about this report the first is if you're just writing reporting a two-hour meeting and you step away for a second you're recording your whole screen maybe there was a split second where your mail app sent a notification right and you don't catch that because you looked away and then you upload the file somewhere you share it you see my delete the recording and then a careful friends like analyst what they will do is they will break the part of the video frame by frame right very easy
to do Empire just export every frame to a PhD file and then run an analysis to instantly you know a standard hour-long video will be hundreds of thousands of frames you'll read a simple program to detect any major changes between frames and that notification that you get that you would have missed will stand out like a red flag right so that's something you can find your recordings to be cognizant of any straight signals and by that we don't just mean visuals for instance set notifications of any sounds right if you get a ding that you got an email at that instant what someone could do let's go back check the company email server and check who got an email at
precisely this timestamp are you and now suddenly you know who recorded that video I mean that's the points that you need to be cognizant of all these little factors for you to be cognizant of is there any straight sound is there any straight video um something as innocuous as a mouse pointer can give you a wait see our mask when you're here but you saw that it was a black mouse right with a white outline because we're on a Windows system yeah I system they always get those accused on the flip side if you were on a Windows system you would see a white mouse with a black outline right why does this matter let's say you're in a
corporate environment where 95 percent of the years and you happen to be in that five percent because of Windows user and your mouse appears on the lead recording the people doing the investigation now know that you're a Windows user and when they correlate with all the other threat factors that they may have identified earlier guess what there's only two windows users in that early high-risk group right so that helps narrow it down and then one other thing to worry about especially with zoom reportings and other video conferencing platform as we started this is zoom actually has the function to enable audio watermarking and recordings what the speed is what this means is each attendee in a zoom
meeting gets a unique audio stream that's water and large so yeah the good thing is that for now it's possible Zoom or you're going to use on the top left of your scene window you'll see this little sound icon for the lock and if you hover over it it'll say something vague like audio signature enabled you know like what does that mean audio signature is assumes kind of obfuscated language for saying that the video is one so that the audio is want to work right so audio signature means audio water marketing
and then in terms of images we looked at this a little bit earlier right when we looked at the micro dots on the printer that's something to keep in mind is that any imperfection in an image can potentially reveal the source like let's say you take a screenshot of your laptop or let's say you're worried about taking a screenshot because we just talk about everything you do in corporate asset is mired so when you hit print screen that action goes to an audit log somewhere so you're very hesitant to do that if you don't do that instead you take out your phone take a photo of the screen with your phone post it up you think that's
good because all you did was take a photo with your phone you didn't do anything on your work computer that you shouldn't have right and your phone happens to have a dead pixel just one okay and let's say that you're on that risk of high threat individuals that we talked about earlier what the investigators will do is cruise over to your Instagram cruise over to your Facebook look through the photos that you've uploaded run an automated [ __ ] script to see if you have that same dead pixel in other public photos that you've pasted if you do then that's now a pretty good identifier that you really the same person who took that photo and
you know dead pixel is just a very trivial obvious example there are many many many other minute Perfections that a camera sensor will have that you will not be able to detect this whole field in forensics if you want to dig into it it's called SCI or Source camera identification and there are basically every single camera that you guys have right now has a unique identifier based on imperfections in the image sensor based on miners microscopic scratches in the lens that will not show up on a photo but when they're combined with the image sensor it will produce a particular noise footprint that digital photo that will then be possible to link descript photos taken in different
context together um the field is rapidly expanding to the point where now the purpose you need to train to be able to identify a photo is only one other photo right so if you have only one other photo that you suspect like let's say I suspect that Kenny something I look at look at his Instagram pull one photo from his Instagram I look at the leaked image SCI algorithms are sophisticated to be able to make that match off of one photo years ago it used to be hundreds of photo you need to train the data set um based on different camera models and so on it's Advanced at this point where you no longer need to do that
so the point is any little thing can leave a Trace and also back to the thing like if you take a picture of your screen or something you have smudges on your screen and your personal insurance fingerprints or did we catch the bottom corner or something if you have to get that you can limit the type of last offer whatever experience so it's be cognizant of what you're doing a picture of and what you're taking it well and then all the metadata that's included on your phone to hear about location tonight all that stuff I'm familiar again of another case of a very popular let's say foreign owned social media company that's really invoke right now that had
an unflattering news story come out about them that had a screenshot of an employee's screen in the news story What I Hear till happened at said social media company is their security staff after hours went around everyone's desk and tried to find the computer that had that same smudge in the corner so again when Kenny can actually mention smudges most of the things we're mentioning aren't from the actual real world examples that you can't Name by name but that have actually transpired so keep that in mind that something is innocuous as a smudge Department stickers seriously so that kind of brings us to another principles you should be aware of is a one-time use thing so if you're doing
anything sensitive you want to have some sort of one-time use document like maybe I'll stealing akita's phone and use that to take a picture but don't use work devices that's kind of obvious I mean don't just make sure we'll go on their own networks but also don't use your personal devices that has your metadata it has other things you've been tracking back to other pictures you've taken like you kind of said I mean there's a myriad of things that can be tied back to your other devices so point being is just take a single device go buy a burner phone go steal somebody's phone for a little while and send it or do whatever it wants to get rid of it and move on
with life so yeah
things like that but really the problem is using your personal level can be just as identifiable especially keep in mind like I said earlier about when these investigations happen if they're a sufficient level to have warrant that depth of Investigation the company that you work for will attempt to subpoena your private documents right they will attempt to subpoena your private Google Drive your private WhatsApp blogs right or call logs anything that they can get the hands enhance a legal attempt okay that's the truth from you thank you and this brings us to our conclusion for kind of really the overarching point is there are many many many things to watch out for like when leaking you have to be cognizant of all
of them and you have to lose your critical reasoning skills sometimes think through okay I have this how could it possibly be traced back to you
periods and periods of time to think about okay I did this but what about this and really the main takeaway also is don't trust others to do this for you right you have this tendency if you leak something you know they'll take care of it um as we've seen earlier journalists for instance we try their best they have the most tech savvy folks so don't trust the journalists who saw that story which led to the arrest of the leaker you have to do the sport yourself before you package it up and send it by no means are we've been donating any of this getting ready to go out and start your own right no again just just to
reiterate this is a red team exercise early under the auspices of a fictional scenario me either I have a question on it and this may be somewhat naive question where you you referenced threat modeling tools to give any sense of how many companies actually can play those types of tools and I mean obviously talking about different sizes different shapes different companies but how how prevalent are they if your company is larger than let's say 500 people chances are probably 99 that they do some form or other um the reason being is that most Standard Security and IDs systems IDF systems are now actually transitioning to also do a combination of stress well that's what that's the point right so
there's tools that may not necessarily be used as quote threat modern they will do other other things but it can also kind of be exactly because remember like if you have a sophisticated audit logging system it's a very short in a way into just transitioning that into a sophisticated Insider threat system right so even if you have an audit alert system right like that being hashed right into intrusion system yeah um you're talking about like Zoom or audio are they like doing like ultrasonic um more than zeros basically or okay yeah in zoom's case that's you know I'm not going to say literally the case that is very close to the being the case is
zooming points ultrasonic um audio wire works but that being said consumes watermarks though are not super sophisticated you could defeat ultrasonic workspace setting off of a bigger point for the highest rate that you want the audio to go but there are more sophisticated Watermark audio alarm work systems out there um some for instance work not by adding data but by subtracting data and that might mean that there might be a tiny tiny 0.01 like the point thousands of a silent Tron balance right and when these combine all those silent dropouts you then get the Monitor and the reason I bring those systems up is that they're much more resilient and robust to tampering and modification and so the
takeaway from that is if you're dealing with an audio Watermark the best step would actually to be the same thing that we talked about when dealing the texture watermarks is retype the text right there's not a real reason to leak the actual audio file you can just leave the transcript of the conversation right and that would completely neutralize any kind of sophisticated wire works and that's kind of the I find that symmetry here really really awesome right these systems cost Millions to develop sometimes hundreds of thousands to maintain on an annual basis and all you have to do to defeat a multi-million dollar audio water work system is type out the text yeah but like a text to speech could be
speech to text uh be detectable because I mean those people are going to be lazy and so basically you hit audio and you just put your phone so the the problem with using speech text and really it's kind of a general point that applies to much of this is make sure that it's not cloud-based right because what can happen is let's say you use that text-to-speech um at a later Point your company subpoena's Google for your private loans which again they do do and if let's react yes to that request and they now have your browse history and chrome that you went to this text-to-speech site the next step is to subpoenaed the text-to-speech site right and request
their logs and their potential for that file right so the point is you could use assistant tools but make sure that they're all local based right you're not using and this applies not just for text to speeches applies to anything if you're using an image editor you're using a document editor do not use cloud-based tools don't use Google Docs don't use your award 365 synced up to your whatever Drive Right local base tools for all of us really what it boils down to it is such a glib point but it is also so so important so my question is like we just listened to you guys for like 35 minutes and you wanted to pull off the perfect ice
what would you guys do this [Laughter] it's just for learning purposes don't be lazy I mean cover Your Tracks go back and stuff it's a matter of following kind of the principles that people eat out like the principle of one time you use is super important right people who use their own phones for everything and reuse them and every time you reuse something you're leading the same kind of trace this is the same kind of issue that you know physical forensics has had since September Memorial right like the person drives the same car that they drove to do something that more into investigation right leaving the same exact tire Treads they use the same gun
right all of this is very very basic physical forensic and material evidence stuff except just applying to the digital realm and really that's what we're finding is that lots of this stuff is not new in terms of the you know the actual technical processes are new but the actual nitty-gritty investigation is the same thing that materials investigators have been doing for years right yeah how do you how do you properly go about adding a burner phone like when you write whatever isn't that tied to your name address again that kind of gets into the question of like actual in-depth threat modeling of who your adversary is right let's assume that it's anyone below state level for now like less than state
level adversary they will probably not be able to figure out that you went down to the corner store okay so basically there's there's we could the risk of going down that rabbit hole is that eventually you know you scare yourself to complete an action like I can't do anything anything I do is tracked and of course there are limits if we talk about the extent that corporate actors can do is they can request subpoenas if they know who your providers are right if they don't know yeah it makes sense that being said with state level adversaries
virtual numbers but also going with your burnified idea you could also get someone else to go get it and kind of get it back so also not tracing it back to you back to that person yeah I just want to like could you could you is there like a back-end database where you can identify the registrants name yeah their name to the phone number
all right you got 30 seconds so stuff like that microwave whatever oh yeah kind of two questions and one are you on out of curiosity is it were you more of a fan of like you know all the files you can at once and then get out or like I'll keep dropping little documents multiple times over using different phones and why not second question is has anyone have you done any cases for anyone actively kind of like sabotage someone by taking the watermarks so I'll answer your second question too because that is a funny story that I'm aware of someone working at an intelligence agency was it happy with her co-worker because their co-worker got a nicer desk that
had a window they were a junior staff member and they had a nicer none of them had offices but they were sitting next to a window this person is very very hurtful at that what they did isilia totally went out to lunch got on their computer took documents while logged in that stuff and then linked them to a random Museum so to your point that kind of framing does actually happen the issue with it though is that it is very trivial to stop according to decide to prevent further on because when I talked about that earlier okay he was talking about The Insider threat profiling right a huge sector for Insider threats is employing graduates right a
sophisticated Insider threat program which government agency will have will have an internal database of inter Regency grudges right so employees don't registered each other and that's what happened in this case uh the person who leaked those documents from someone else's computer even though you use someone else's computer he was caught within a week and the reason is because his garage was very very open and known about in the offices right so when self in fact that was based on you know interviews in this case what happened is when that leak happened people didn't even suspect that the person who's name was attached to them they instantly suspected the other person because his animosity was still on them is that
something to keep in mind as well when doing um sort of broadly known as impersonation text right just have to make sure there's nothing to actually link the perpetrator to the person any other questions thoughts I just wanted to share that I listened to a great privacy podcast mid mobile apparently is the is the highly suggested um carrier yeah Moe was owned by this oh so the reason I think is Smith mobile offers trials SIM cards that yeah on Amazon or whatever that cost a dollar and then worked for a full week
fun fact thanks guys [Applause]