Fantastic AWS Attacks and Where to Find Them
Show transcript [en]
due to technical difficulties a portion of this presentation was not recorded we are joining the program already in progress alright oh okay the tactics essentially are a goal of the attacker like based on the step of the acute saying the attacker is the goal might be the initial axis right or the goal might be to establish persistence and then the drop down is a specific technique being used for that particular attack so actually this is pretty recent we didn't have a cloud matrix as before October but October as you see over ninth this year might have actually published this it's a really good start and I really want to actually contribute to build it more so jamming
writing the code that you see with p1 1 9 0 or the T 1 1 1 1 3 3 6 is essentially the reference code to the attack matrix to be attack matrix and is a we're gonna go through it and I'm gonna give you some of the attacks that we see based on the the tactic and then a specific technique the specific technique is gonna be the specific reference code that you see so for initial axis I mean the first thing that you're gonna seen in in an attack it's gonna be initial axis right how they're gonna get in and what happens actually is that even though we might have the best tools in a cloud security to
protect our environment we're still gonna have issues on a horse Bay on the host level so you're gonna see all the time are you're gonna see our CSS arrives you name it anything that you can get a code execution or a command line execution on a server can actually give you the initial foothold in the AWS account and how you do that actually such there's a new feature now for my W is that might that tries to stop that but right now it's a little bit slow in adoption and most of the people still use the version 1 of the metadata service and essentially if you can get a chimeric security on serve on a wet on an on a public-facing
application then you can request the credentials the secure AWS security credentials for this particular account next we have a technique with through valid accounts which can be for example if you there are the having cases of people having exposed credentials over AWS in github repos or other places and then attack you can just grab these and just go in like a valid user then I have so the next up I have here it's based on the attack metrics framework it's persistence but I'm gonna skip it and I'm gonna come back to it because what I think is the next phase of the attack kill chain is discovery or reconnaissance you call it what you say
what do you want to call it because right after when we see an attacker gaining credential access to our it'll use environment the next thing that we're gonna see is he more hair try to do discover in our environment try to release trolls try to see the specific role that they got what access they have because they don't know usually if it has got some AWS credentials and they try to figure out what can I do with this right they're not really sure what to do with this they're gonna do the account discovery the permissions group discovery and we map all of these in different techniques and you're gonna see why this important on the next
session with discovery so next after discovery we have persistence and then what if you get access to an account that essentially you want to get different ways that you can access again or continue your access right you can create new accounts if you have the permissions you can attach existing policies and something are really cool also is that if you have the permissions to make changes to security groups you can essentially open up a specific port for you to open to get to access through you're attacking machine then the defensive vision I don't have a specific technique attached here because there was not one already in the matrix framework that they that matter have published and I'm planning actually to
see how can I contribute to it to add this so if the attacker has the permissions and if there good at what they do they're gonna essentially stop try to stop logging and stop the security services like they're gonna stop cloud so we're gonna see what cultural ease right after they're gonna start guard duty if you have it because they don't want us to catch them and the last one cadet Alexis were here this SSL it goes maps back to the initial axis and it's the way how they're gonna get the metadata API to get the credentials brilliance creation essentially overlaps a little bit with persistence it's a little bit about the same techniques but
I'm gonna go more about it on the detection side we talked about discovery and lastly detection last but not least right because this can be essentially the goals of the attacker I mean they can have other goals as well like an I don't know potentially have want to establish it to to have a crypto mining service and your AWS account and cost you a lot of money but something that we look for is if they if the attacker can get access to a role that has access to our confidential s3 buckets for example let's say they might try to get those files exfiltrate those files and we're gonna see how we can catch that actually
so cloud shell I cannot see everybody but please can you tell me if you are familiar with cloud shell and what it is all right so it's like 3/4 of the room really quickly essentially cloud trail is the service that records all the API calls and AWS actions in AWS it's gonna record everything that happens on the API level and essentially that's everything that happens in AWS everything all the different services connect with each other through API calls and all of that is logged in cloud trail so it's really it's our holy grail of artifacts you want to say logs you want to call it whatever you want to call it is really important for us defenders to understand
how cloud what cloud chilis and addition the scheme of it so we can put detections we're gonna see right after so here is what it looks like essentially in the beginning we have the user identity which essentially the entity that performs any action then we have additional information about the event like this is from initiative in from basic to service and the event name are you see over here let me see the event name essentially says what was the action that happened right then really important to make attribution is the user agent and the source IP address believe me I've been able to actually find like specific activity and attributed back to some pen testers through just unique user agent
you were just that simple it's really some people may say that I don't want to look for user agents it's like really neat like something old we look at all in the old days but it's really important to make attribution here and then lastly really important you have the request and response elements so it's the request parameters and response elements or I don't have it here in detail essentially the request parameters she's gonna have all the information that your request is asking the service to do and for example if you would change the security group you would have the changes of a security group that you request like open up port 80 and then in the response elements
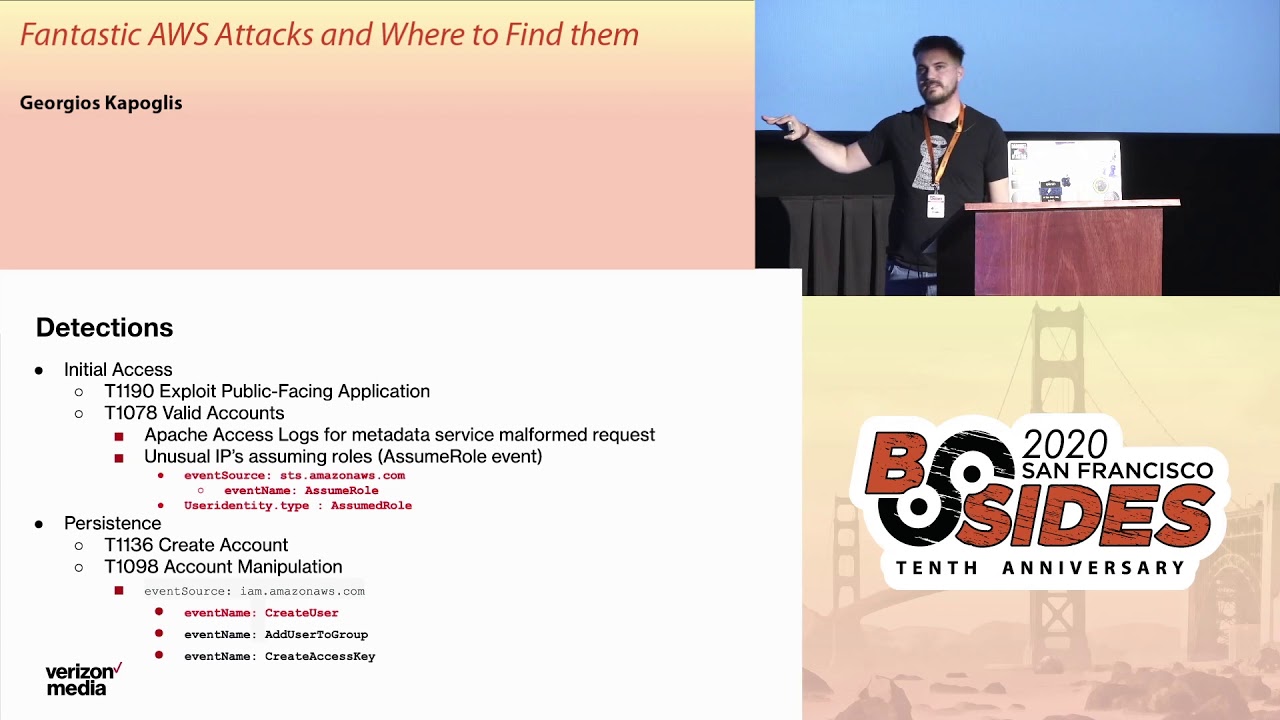
you're gonna have every time if there was a change that was successful you're gonna have that on the response elements all the time so now let's jump right into the detection saying I think I have ok time so for the initial axis I so let me explain that I have on red I have the event names that you need to look for in cloud trail that have high fidelity and really really good signal so for example on this first slide I told you in the beginning that an attacker can get the credentials through through the metadata service if you they get access to your instance right but what do they get they get the STS simple token service keys
which are like 1 to 6 hours usually they and then they refresh and they're gonna get these keys but what happens and actually this is a really good paper from Netflix I have a reference at the end that they describe this technique in detail they don't give you as I'll give you over here the query exactly but they describe it so much in detail that you can build your own data analysis and query to hunt for that essentially what happens that whenever you get a creation of these credentials you're gonna have a cloud Sherlock with an adventurous STS and then an event named assume role that's gonna come only from the ec2 instance that requires these credentials
and the thing that is really important is that these credentials are only supposed to be used by Verity to instance they're not supposed to be used by anything else so then whenever bespoke sorry let me go back whenever these keys are being used you're gonna see a cloud show log with a user identity that type assumed role like let me go back right over here and the user identity type assumed role now if we see that from very c2 instance that is normal right but if we see that through any other resource like a really good signal would be external IP but even even through like within a it obvious because they may like it might be using
any c2 instance then that is a really good detection for you guys I'm telling you and you can go up and read a Netflix paper or have more time to discuss about it it's really you can build a really high fidelity detection then on the persistence side of things on the create account and occur manipulation something that has a really good signal is the create user because from what I've seen it doesn't happen too often and the rest add user to group and create access key they have a little bit more noise but if you if you can hand for these and like let's say look for unique IPS or abnormal user agents that you don't see
in your environment that is also a really good signal next for persistence again I discussed before about how someone can make changes to the security group or the ingress or the egrets and essentially you would hunt for these looking for adventures easy to do easy to service and then authorize security group ingress then one of the best ways to hunt for and put detections for an attack in your environment is when they are on the privilege escalation phase because most of the time they're going to I mean and they're gonna get access to it like probably a low-level account hopefully so they're gonna try to get higher privileges so the ones that I have here in black the event names are a
little bit noisy but if you see a attachable policy or as usual policy with on the right over here oh is that on the right with administrator access well then that's something that you need to look for like your user shouldn't be attaching to this policy normally then something really cool that I found out actually this past month is this thing over here so said people policy version what happens here is that if you create a policy for your role or your instance and you create multiple versions of that and let's say sometime during your development phase you're devs wanted to get admin access because they couldn't figure out what access they needed to create something then that's a
version stored for that and if they attacker if the role that the attacker got access has the permissions to change the default policy version they can roll it back to the administrator access policy that you that your developer thought that had deleted in the past so this is really important to look for this this has really good signal really good signal moving on so on the discovery phase in general reconnaissance this is these are really noisy but again if you see any like an assumed reduction that we discussed before from an external IP or an abnormal IP and right after you see discovery artifacts then this is 100% an attacker or a pen tester or your red
team someone that is trying to do something bad I wouldn't expect to see assumed role from a new IP the rather in relation to instance and in discovery like listing roles we generating reports about credentials I wouldn't expect that to see as a normal use case at all whatsoever and then last over here as general detections what a really good thing is that if you have specific roles or users or go that should always be going through your single sign-on to go to AWS and using multi-factor authentication then you can look for this tag there's a tag MFA authenticated and if it's false but it shouldn't be false then in social another red flag and then something
really important is to look for the error code because any of although they've been names that I already showed you that have access denied' of an author unauthorized operation and failed access that should also be something to investigate I mean it happens especially in the discovery it happens from developers but with some data analyses you can really easily clear those the cases that are normal for your day to day out and lastly we have the defense evasion which is actually something with really high fidelity if you see and act like someone trying to stop your cloud real logs why they're doing that even more if they delete your trail then if you have got duty which is actually
really awesome in the beginning I didn't thought I would like it but I like while being using it and seeing the alerts that they deny rate that thing is pretty cool because it actually detects all the behavioral stuff based on what I already showed you on the specific techniques they try to determine if there is a different behavior and those techniques from a particular resource so if someone tries to stop that from monitoring why they would do that this is really good - deleted detections that you can pull right away in your ALW environment so in the last one is collection and something I want to mention here is that when you when you get object level logging
because you need to have object level logging in the cloud trail to series this I'm not really a big fan of the server access lodging because it doesn't give you the video that I want on cloud trail and you can look for let's say that an attacker is already downloading something you can look for the eventual size 3 event name get object and then request parameters you're gonna have the file names download it so you can see any of your confidential files secret files for downloaded or also in the additional event data you're gonna see the total amount of data X which a so you can see like if you were success not because right when we do IR or
forensics we need to report what was stolen right is one of the major questions of our process so this is gonna help you a lot of figuring out oh okay they got access here but we're able to download anything if I see zero one additional I've been dead or maybe they filled that I'm good maybe I'm sorry that I'm running because I just have another five minutes I'm gonna go over here I was gonna put that whole scenario into place but I'm gonna keep on skipping this because I don't have time and I want to jump right in to operationalise detections so okay really quickly I showed you some examples of what to look for for the specific on the
specific technique and tactic to find an attacker in your environment now in order to start thinking about how to operationalize and put it on your soak in your incident response team the first thing that you need to do with centralized aw looks you shouldn't have them in the different accounts that you have in your environment you should send it to your own security account and if that difficult I'm going to tell you we have at version media we have about more than 1,000 AK a unique AWS accounts and we send them all all the clouds we logs to a specific account that we the security team have access to and we can secure these logs then choose you to sit
right there are some amazing open source tools like stream alert from Airbnb or I found another one that I haven't Alice on the reference and you went from endgame that you can essentially streamline your cloud trail logs put rules and detections with lambda functions essentially they tell you how this would work it will be that you would have a lambda function logic and your cloud tree logs and based on some rules you generate alerts and then you can either send it I can email it to your distro or send it to a slack board or to your Splunk or whatever you want to send it to and create detections that way then of course you realize the
attack framework to build the detections because it's really easy to build a really good picture of the whole attack rather than just having directions here and there the the attack matter framework helps you a lot on figuring out what are your gaps what can you take what do you have defenses on and so on and lastly yeah I start with the workflow from the alert and action on detection sieve you want to so here my reference is I have the first one is on the Netflix pay the Netflix paper about the density they sell compromising it'll yes I definitely recommend reading on that if you want to build a really amazing data analysis detection here
then Rhino labs does an amazing job on posting a lot of really cool information about AWS then we have the two open source tools by Airbnb endgame similar in varna now swim alert is a little bit is amazing by it's a little bit complicated you need someone to maintain it I believe then varna from endgame I've seen risk just recently it's a little bit simpler does it do all the things that try maletas but i think it's really good to put what try one of these and consider them for your sock and to put detections and alerting if you don't have a service like guard duty for my double years that was it thank you have
any time for questions we have to meet for questions yes so that's a great question I'm gonna first of all I'm gonna post the slides right after but I'm planning to also publish a github repo with sig Sigma rules that are going to have all the techniques and then have queries that you can put your own your plan or your open source tool to a personalizes yes dick about goose I have it on the first you got yeah let me code the first yeah please I mean we have a pretty big team hey





