Who said that Python was UNIX Best Friend Only?
Show transcript [en]
presentation if you like it then you can Applause so the idea of say that best friend the ID behind this
the idea behind this presentation is so I'm doing a lot of hunting reverse engineering and uh I would like to bring you some kind of a high opener uh be careful about Pyon on into Windows ecosystem a lot of people think that python Works only on Linux system Mac OS all the uni flers but my is available on Windows it works pretty well and even if it's not installed by defa I will show you that it could be install very easily and you have a lot of malware today that perform really nasty stuff on Windows systems quick introduction about myself I will speed up a bit because I realize yes I but I had 30 minutes but normally
this song is one so you have to skip some slides and maybe uh some techniques I will go faster of course if you have questions feel free to come to join me later today I will be happy to some chat and about myself so my name is me I'm coming from Bel where fre security consultant so I have my customers to improve their security posture and basically I'm a booty guy so I have to P people I have to P bad guys and uh when I found some piece of interesting code I like to disate to look at what this besides my I'm a sonor CER I hope that you know theate stor Center all of you listen to the
diary and the podcast you produce every day uh I'm also instructor I'm teaching 4610 and 4710 this training ising so as I said and I'm also about to for C Conference in organizer this talk uh this is not brand new I already presented this other conferen but it's still totally rant why because every day I still find new python malare new p man script uh and techniques AOL all the time so it's still really relevant and the idea was that uh one of my best place to H is from SC for example uh so I have a bunch of Y hes where I try to catch interesting uh script and one day I started to see uh python script I
collect them I them when they're interesting I will investigate them deeper and you see that this is super screenshot coming from spr C that you have a trend it's coming from uh July I think it was July last year until no it was the year before so it's this work is is from last year so we see a trend and I'm pretty sure that if I do the same quy today we will see the same kind of things uh we also produced on the internet Center a lot of uh Diaries regarding Pyon you see it started I think the oldest one was from 2020 uh yeah something like this uh most of them have been written by myself but
you also some one from Rick one from me and we have some fresh so Pyon is definitely very interesting why as I said said I'm using VT VT is definitively my prefer uh location to hunt for for man Cod of course the biggest issue with C is to do this you need a pro account which is really expensive I'm lucky because I have access to V multiple customers organization and so on so I can I can clearly deploy my rules my hules and this is typically what I do very simple if you know y uh you will what it me so basically I'm looking this one yeah perfect I'm looking for specific strings like this
for COD uh sockets return to CH to API blah blah blah blah blah very simple and the idea is to spot python scpt you see that from time to time I disabl some uh some Str because importes if you do importes I get way too much force positive uh uh I don't change this room pretty often I think the last time I Chang it change it it was 3 months ago and it still give me some relevant information first quick introduction about Mal of course um why python is interesting because a malw when when I mention a Mal I need an executable a p file it will never be magically dropped on your computer like
this there is always infiction path that you have to to to follow you see this on the right side of the slide it start with a fishing or social engineering attack then you have a first stage a second stage a third stage and so on and so on and finally take thetic andiz ROM r whatever you want and usually the first stage is based on scripts you have plenty of scripts available in Microsoft Office or Microsoft Microsoft the the ecosystem thank you Microsoft for this uh um you have the good old batch so a b f it works still today so people they just write suspicious and malicious. F of course you have po JavaScript VPS VP
PLT and all these scripts are available by default in any Windows installation so you can have appropriate computer you put computer at home computer used by your kids they all have this uh different s capabilities of course share remains number one because it's so powerful very easy and this is a statistic coming from also it's one or two years ago but 38% of incidents involve B shell 68% of brides involve Bell crazy but I thought is also interesting today and why first it's really popular and easy to Lear um I'm pretty old but I know that all the students universities and uh high school today when they have to learn the programming language most of the time
it's p even te they Learn Python because it's so easy to use yeah uh so I'm using python 2 so I switch from per to p as I said I'm an old guy so I started to develop years ago and one of my objective time was to move to Python and I did yeah uh so whiteon is really powerful even if the script which the the the the sytax is pretty easy to understand it's really workful the very good point and you can see this the few minut you have a lot of libraries don't try to re the if you something Pyon probably somebody in the world wrote a piece of code a library to do what you
are trying to achieve so do not remember do it it can be compined so python by default is an interpreter interpreted language when you execute it it will be a compiled live and executed in the sand box but you can generate a def5 a really that you can drop your victim and you can work probably the two most interesting points are less attraction from Defenders that's the propose of the talk I would like to open your house and also no MSI support in Microsoft what does it mean MSI means anti-al SC interface from time to time I have a LEL relationship with Microsoft because they do some shitty stuff but honestly MSI is a great format so really cool without
going too deep it's a framework that helps you to interface your script with the Microsoft Defender and as the name says you will be able to detect if some piece of is man but I don't use msci usually in my investigations when I do some reversing I don't use it for the anti manare capabilities I use it because it can lock all the actions performed by scripts on windows so basically you run you you you have to specify a command I will not describe it because it's pretty big it's to this side on the screenshot it will look all the instruction everything executed by script so if you have a piece of over shell that is H
skated it you run this command then you run over sh of course you have to do this in your sand box toet try this corate computer and you will see in details all the actions performed by the the the script it works with JavaScript PS but guess what not python so if you run the python script on Windows by default you have no way to track it and to see what is going on what's going on the first thing that's the first step that must be uh uh solved by the attacker is to install python because python is not inst by default in window Microsoft Windows so when you try to type when you start to type python you will see that
python is not recognized good news is if Pyon is not installed just install it if you don't want to install it maybe it's only install in obscure sub territory and you have some specific of ion if you use open Office open Office on Windows include python interpreter if you deploy some sprun tools on your windows they also provide a python interpreter pretty cool so don't have to install it thank you Microsoft Windows subsystem Linux WSS know you have python capabilities so if you use this feature you have python by default another point also from Attack point of view is this one because python is normally not installed by default if python is installed the computer it
means probably that this computer is used by a high Lev profile a system me a developer wellers are not high profile so but could be a need that that's could me uh a RSE engineer could be a why is it also very interesting to check if python is running if I'm a good guy so I don't write M but if I was some developer think about some sandboxes like K or cuckoo they rely on the python AG so if you see an agenty running it means that you are running prop so there are multiple ways this let's go switch to some practical example and funny example uh the first one if you would like to execute
uh Python and python is not available just download it this piece of power shell so this is um a VPS it will execute a run object it will execute a PO shell po shell will download from HP FR G pay Python 3 blah blah blah in a specific file then treat objection application and it will execute it so using this single piece of code you have from GPS you run a portion this portion download and install Pyon for you why is it so easy because python by default has a very small uh enironment or release for window that you can download and it contain it just a z file so you can downlo python 31
blahd and you have everything so the basic stuff to exe python this is coming from the python.org website so probably Beed by your firewall it will beable r e to install by once you install python you will have to run some python Cod and here like every type of competely W on Windows you have a lot ofation it's very sometimes you find a very dumb script most of the time they arec question if we have a very good quality forcation it means that we have good quality of code maybe we can have a look at the developer skills sometimes just by having a look at the techniques implemented to the code you can say this
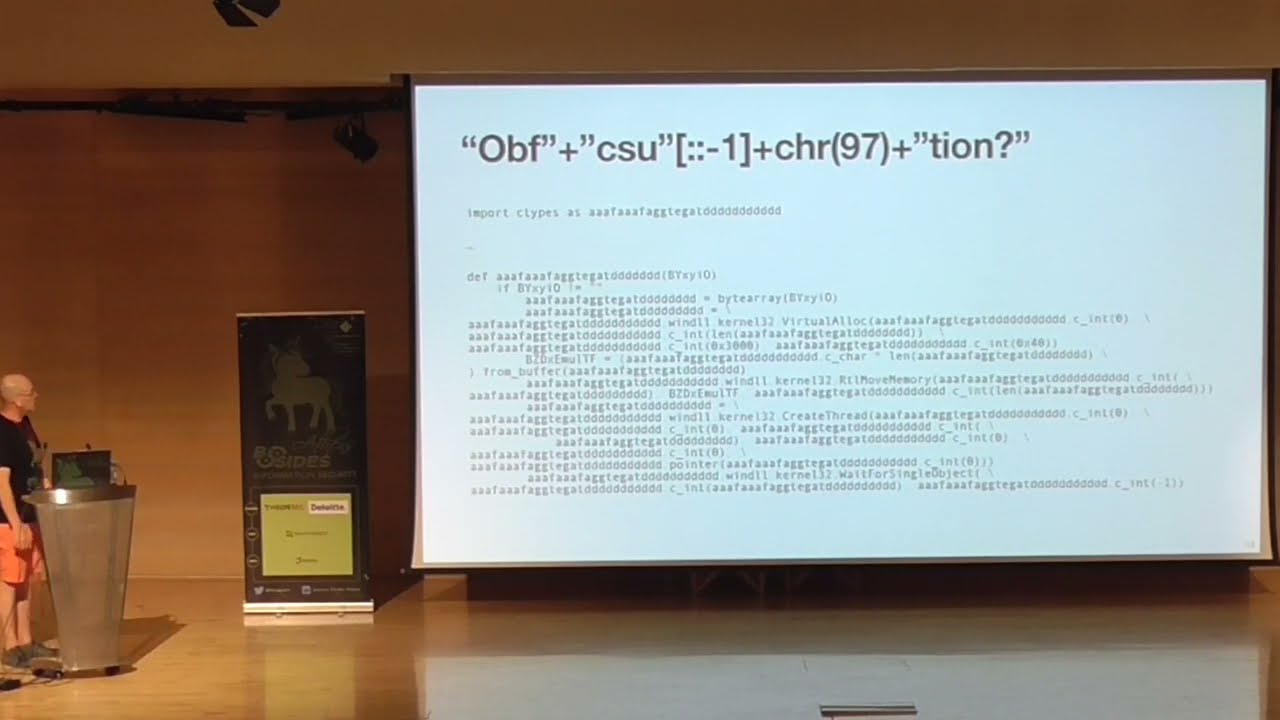
has been developed by this group of attacker this group of attacker and so pay attention that most of the time ofation is not perform manually there are tools framework tocate scrip so the malware developer it just write a noral script and then it pass this for Tool which will aate everything what type of command ofation Technique we have very basic always the same random and unpronouncable variable name function names basic coding ex but also different type of encoding head shars and and so R 13 is pretty common this is an example uh which is pretty unreadable well unreadable the first time you see this basically your eyes will cry but you you can really spot interesting
information you have here so we have an import and the import has been imported using a very nice name and then you see that you have the class variable names function everything has been replicated but you can already see some interesting strings wi t can do virtual anlog pretty cool uh RL move memory wait for single objects uh create thread so basically this simple piece of code will inject a Shell Code something else into memory and Trigg your a neutr uh sometimes officiation is also really cool I'm a big fan of cyers Chef probably you know cyber Chef the tool really nice and uh sometime it's just simple change in the code which makes which will make your life pretty
difficult some can try the V reverser or when they see some some code like this they yeah this piece of code is just basic C4 let's try to decode it using cyber Chef so you put it in cyber Chef you use from B and does not work why because when you read the Str it's B4 no it's not basic4 have a look at the code we have a bunch of data so we have the base C4 chunk but how is it used we skip two First characters because they are not part of the B if you don't no this if you don't notice this you will break because but I can't it just use this wonderful syntax in
Python and then your data will contain a real J of B all by by the way all the example that I will give all the screenshots all the script and so on I found them so I did not WR anything it's really really uh found in the light so we have python available on our Windows system we know how to obious get Cod now what I said is don't re so attackers what they will do they will try to use third party Libras and using third party Libras you will expand your ttps and you will be a able to do a lot of interesting stuff the python uh developers Community is really crazy I found a lot of PR for
almost anything you can write files decode stuff connect to some website do inter API and so on and in this very simple uh example we have a library to Simply access the registration so don't forget that my talk is related to python in the windows ecosystem so will try to abuse and to access all the classic Windows resources and you see here that using the the import we we can just specify a key we can read a key we can read the content of a key we can set the content of the key so we can Implement persistence we have Fess capabilities and stuff like this very easy you can call any Microsoft API Cod
from python we already saw this the previous uh purpose SL if you see virtual you allocate some memory to contain your shell code then you fil the memory with your shell code you create a thread you have common execution so you may check something so some executable code inside you probably you could do that using python but it's so powerful to use the windows API so you have for example if you if you call C types you can then call C types can do the look and you allocate interesting memory and of course you have the windows API so if you have some skills in generate you can learn all the parameters you can see for
example if you have and the memory uh the protection bit as means page read we will have execut the code this location in uh you can Implement very interesting piece of code a few lines for example here we have uh no that's this one we have here a kilog so you implement a kilog in 1 2 3 4 5 six less than 10 Kil in Python on the right side of the slide on the left side of the slide you can report any type of information from the microphone in also less than or 10 15 lines so basically you will call in this you do import wave import some device and not you can access the microphone the
computer and you you record some uh some noise for a few second you will create a test and we have a recording if you run this discussing information you have a web file and then the web file you can just infate it using Ed you interes uh but wait you need to have you have access to multiple libraries but what if the library is not installed because when you see that you install the basic python environment you don't have all this in piece of cake if it's not available just inst so you see here we have an exception so we try to import a lot of libraries except module not F if we don't have for example
uh pi and on you can do something you you you have a list of the missing modules and then you call be install blah blah blah and Pon will itself deod the libraries if the SC has access to the internet minut this I need to speak uh I will speak then another way to to uh have a lot of interesting right Nets you can interact python and net so you can have all the net capabilities from python any API as I said instead of using C types you can use win32 API andle w32 API open process blah blah blah you create a process C types you have the same V another C you can also
create the process so keep in mind that any API code available in Microsoft Windows and want to back door in 1 2 3 4 5 in seven lines to implement a back door the last time I checked this code on VT have looked at the score only two AVS were able to detect this as malicious and it works perfectly and it really do a great job because it redirect so you really have a re shell and you can interact with your vitim computer than shell C injection as I said you can just inject uh everything what we have here uh just to give you some h we download some muchal stuff from URL you see that we prepare we prep
request then we have a wonderful vog 40 patient we the memory we create and object called injection another example so all these all these slides that that have been grabbed from uh live and real example found in the uh I like this one b steer very classic if you can access any feature of the operating system you can also set boort you can do uh you have set you have uh also the get board somewhere where is it anyway you can monitor the bbard and every time using a regular expression you see that in the cboard you have a Bitcoin address a wallet you can replace it by your own so if the guy trying to go small paying
Bitcoin wallet the destination will be replaced by the one of the attacker it's pretty cool and you see that sometimes not only they check for Bitcoin but they check for a lot of cryptocurrencies Bitcoin Sol TR bbb2 Litecoin and so extion Dropbox because you can interact with any tool why not use the Dropbox API because Dropbox developed a python module and then you can easily for and exfiltrate some data using your Dropbox account crypto Miner as I said you can run the crypto Miner you can run a appication I found some red somewhere written in Python honestly very basic very easy to spot very basic but why not it works the picture is real really the
picture was encoded in the in the script and I decoded it so the picture is real uh you see what it works you have a list of extenstions the interesting files and basically we browse all the directories one by one if the file is interesting it's encrypted we create the the r cont on today what I see more and more is an interaction with Discord I every day I found a SCP talking to Discord it's very nice way to implement the C2 because who can drop this part in your organization you have to Sol this with go uh some Steelers in this case this script exfiltrate uh the the wireless password from your computer uh yes oning technique because
if you have to write some Mal C you can also try to defeat the attackers The Defenders sorry and here you see we have a lot of uh interesting processes and what we do we verify in the process list running on the computer if we have one of these processes if we have one process like this it probably it's a it's a secret analyst Compu like this DNL hunting you have a lot of tools what they do they inject the into every process the best is an a every antivirus works like this they inject TN in every process so here we have the same we open the process we enumerate all the DLS loaded inside the process and if one of
them is one of these dnls it means probably that we already the sandbox or in a sensitive system so we not Che I like this one onti techniques CICS when youor youor the script you have a look at the time then at the end of the function you check again the time if you have a huge difference for example in a function uh 10 seconds happen or Al hour it means probably the script is is De and the time between the function has been started in the end maybe the security is grab some coffee had a zoom and so on so the is too big and it's a nice way to detect that we are we are
under de you can of course get the mouse so you can verify in Python if the mous is moving if the mous did not move for a few minutes probably there is nobody between the keyboard and a chair so it's good to eat from the computer you can also detect a keyboard lout could be interesting if you are nation states and you would like to infect only specific tets I will not mention Ukraine r and some but think about gree trying to attack better if I'm not if I'm using keybard maybe I Target if I was I not Target something like this by the way you see in this example here that we try to get also the system uh language
page 2052 simp by Chinese you can also interact with the go you can create window you can create very fancy uh uh so interface in this case you see interesting strings inan basically it's fake AV and the script open the window and want you oh your computer has beened with viruses so please click on this link and I will protect you by installer as I said you can compile your script so it's very easy to once you develop your mware and python you generate an execut and just Dr ex to VI of course some people they develop tools to hand other attackers so you can have a r generator uh you just run the script you specify your secret token you
specify the IP address of your C2 server and so on and boom you get a very interesting python script which is crafted for you contain your in spre I had to speed up but it's over so I think
I'm not





