Falling Off the Edge, And How to Help

Show transcript [en]
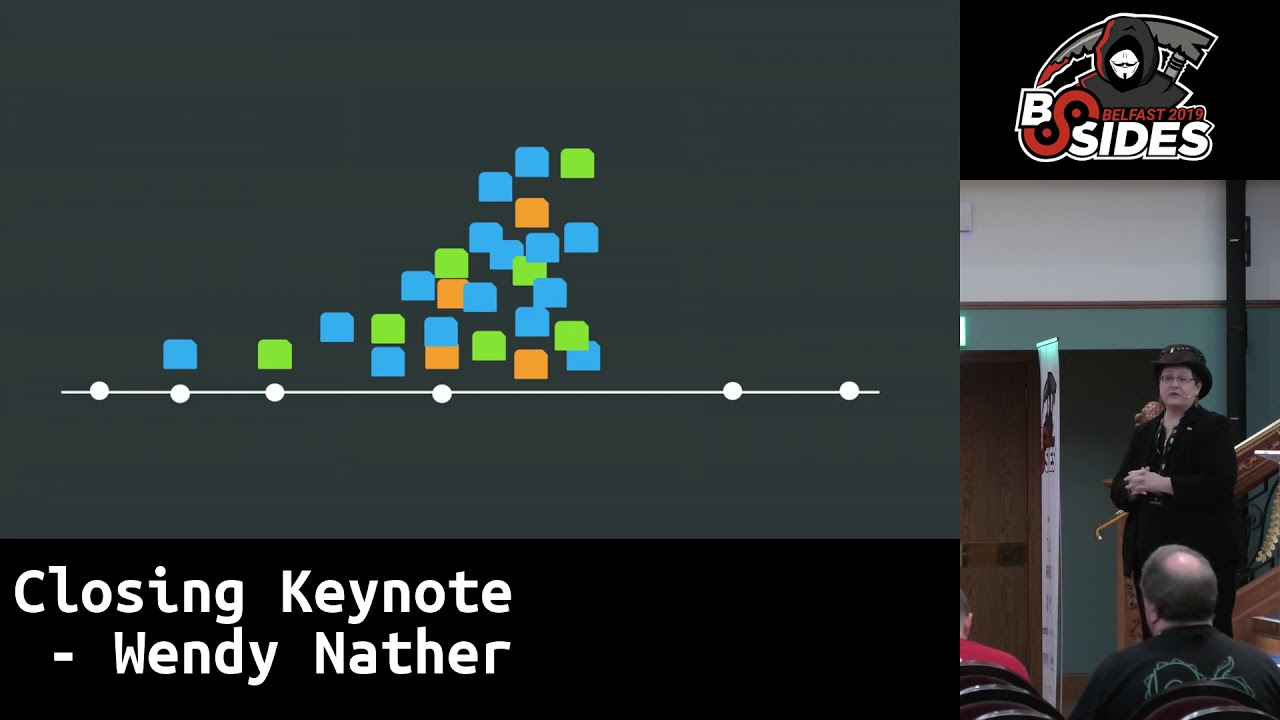
technology. What are you gonna do? All right. Is this better now? Can people hear me? Okay. Awesome. You sure you want to? Okay. All right. Let's figure this out. Um, yeah. I'm gonna How many people saw Tara Wheeler's wonderful talk yesterday? Okay. What she said? I'm done. Now, she gave a really, really good talk about the struggles in particular with SMBs and security as somebody who is trying to help them. And so, I'm going to expand on that some more and talk about some other aspects of why so many organizations and people just cannot secure themselves. And the most important two two messages that I want to leave you with. I'll just do them up
front so that then you can get up and leave. No, the Yes, I did. I did. I haven't I haven't clicked yet. Okay. Sorry. Sorry. Yeah. Um, so the the two most important messages that I want to leave you with so that you can go ahead and leave now are most people in organizations cannot secure themselves and two, it's not their fault. It is not their fault. If anything, it's our fault. And so, we're we're going to do some some naval gazing uh today. Most people in organizations can't secure themselves and you will not see them up here on the stage going, "Yeah, we can't patch." Nobody's going to do that. So I feel it's incumbent
upon me and incumbent upon the other people who are trying to help to speak on their behalf because you know they're they're not going to get up and talk about their problems. However, when I give a talk like this, people do come up to me afterwards and go, "Yeah, that's us. Don't tell anybody." So it it is an endemic problem. It's one that does not necessarily make headlines. It doesn't make the keynote stage at all. Well, okay, it did make the keynote stage one time uh because that was me. But, um it it does not make the keynote stage. It, you know, it's not sexy. People don't talk about it. Uh but I think we really
need to and especially the fact that it's not their fault. Um why should we care about this? First of all, you know the old joke about the two the two hikers and one of them says, "I just I don't have to unra outrun the bear. I just have to to outrun you." No, that is not true because there is more than enough bear to go around. Um there there is thanks to automation, thanks to scaling, everybody is subject to opportunistic attacks even if they believe they can't be targeted or they won't be. and they may be right, but that does not cover opportunistic attacks where they just happen to leave that one port open and you know
somebody's looking for all of them. This is an important thing to explain to your management if you're trying to get past the argument that well who would want to target us? The answer is they may not but they may get you anyway. So this is this is really important. Another important reason is that breaches affect more than just the target organization. Uh the Scientia Institute, if you've heard of them, they are fantastic writers and researchers. They some of them also uh created the Verizon DBIR. So you'll hear the same voice in in their writings and it's makes it incredibly readable. They did some great research together with Risk Recon, which was a spin-off of Mastercard, and they
determined different ripple effects from breaches, including the ransomware attack on Blackbod. Who had heard of Blackbod before this ransomware attack? A few people. Yeah, it's um it serves a ton of nonprofits and health care and it affected over 800 organizations. Actually, the last time I talked to those folks, they'd got it up to a thousand. A thousand organizations were affected by this provider that you'd never heard of before. So, this is this is the world we live in now. And more than that, here's a a a statistic that really got to me. One in four receivers of those effects ended up paying all the costs associated with that breach on them. So it wasn't their
breach and it still cost them money. They still had to pay for it. It wasn't that the breached organization paid their costs. No, they had to cover it themselves. So this is this is why we have to care because you know different links in the supply chain whether you've heard of them or not will still cost you money from their breach. So this is why we need to care. All right. Uh Tara did a wonderful introduction of this yesterday but I'll talk about it again of the security poverty line. I came up with this line in 2011. Uh I went from doing security for a Swiss bank to I I moved back to Texas to take care of my parents. And so I
went to work for a Texas state agency. And on my very first day, I walked in there and I was the only security person. And they said, "By the end of the day, we need your budget request." So I was like, "Okay." So I wrote down I asked for $2,000. I wanted a logging server and a couple of books. And the person I was reporting to scribbled it out and she said, "Where do you think you are in the private sector?" So, I went from having a $50 million budget to having a zero budget and no people. And uh so it was really important to me. I saw all sorts of commentary, you know, on social media
about, "Oh, I can't believe they got popped, you know, how stupid must they be. how lazy, how apathetic, how unaware. And that's not the case at all. If somebody like me can walk into an organization and have to struggle to to secure it because of all sorts of other factors besides money, um then it can happen to anybody. And it's not that these folks are lazy. It's not that they're stupid. I hate hearing that. until you have tried to do this in a real world environment, don't go ragging on them. So, uh, and the other thing is I know some people don't like it calling it a poverty line. Uh, and that's fair. Some people think that the word poverty
is derogatory. I don't think so, but I can see how somebody might believe that. But I chose it very deliberately because I believe that the factors leading to this and keeping organizations under this line are every bit as complicated as regular poverty is. So I want you to think about this. It's not just the case of oh they just need to follow NIST or they just need to do this. We just need to give them more money and it'll be fine. They need to have these different factors or or thought about the other way. These different factors are the ones that are keeping them from being able to secure themselves. First of all, budget. Yes. Uh budget is an issue. And
can they actually afford the financial cost of tools and people? I don't believe that we know what it should cost for any given organization to secure themselves. We can talk about very minimum baseline, but I actually did research on this when I was an analyst at 451 and I went around and asked a bunch of security professionals. I let's say I have a thousand person organization and I'm a CISO and it's my first day on the job. What should I buy? Because that's the thing you do, right? And the first day on the job, you sit there with your blank Excel spreadsheet and you start making a budget and figuring out, okay, what do I need? How
many different people do I need to run it? All these other costs. And I don't think that we can do it. First of all, I got so many different answers from all these professionals. I did not do a survey. I just said, "What should I buy?" And then I wrote down what they told me. Some people named four different technologies as a minimum baseline. Some people named 31. And you can bet that the people who named 31 worked for a bank because you can buy one of everything there. But nobody could really agree on what we needed. So I normalized it all and it ended up kind of matching pretty well with PCIDSS, you know, or pick your shopping
list. And then I went out to try to price it. And most vendors do not put prices on their web page. And if you call them and say, "I have a 10,000 person organization and I need to buy this. What what will it cost?" It'll say, "Well, we we need a 2-hour sales call with you first to determine your requirements." So, there is no way to know. I I gathered a bunch of data. Again, I normalized it and I found that you could be off by as much as a factor of four guessing how much it would cost you to secure an organization based on depending on whether you were using open-source software, you'd still need
people to run it. um you know depending on what you were trying to do the vertical the geographic distribution uh you know what kind of branch offices you had and everything you could be off by a factor of four so if we don't know what it would cost how do we know if these organizations can even afford it and yes you know as as Tara suggested starting with really really basic questions and just starting with one thing is a great idea SIZA did this too like if you can't do anything else, just do MFA. That'll bring you some of the best stuff. But I'm sure nobody is going to say, "Oh, yeah, that's that's fine.
You're done." You never know when you're done. There's always something new to come out here. And the other thing is that even large organizations can fall under this line. Uh if you're looking at things like convenience stores, um their profit margins are around 1%. you know, when you buy your little hot dog and coffee, uh, while you're while you're gassing up your car. Uh, that's different from the tech sector, which the last figures I saw, their profit margins about 12%. You cannot afford to buy security if your profit margins are 1%. That's that's just the way it is. The next one is expertise. Do they know what constitutes essential security and how to go about
implementing it? Now, this is not necessarily just awareness. Oh, we're we're going to teach everybody about this standard and then they'll be fine. Um, expertise is also the skills and experience to know what to do with something that you've never seen before because let's face it, this is like everyday insecurity where you're looking and going, "Oh, wow. That just happened. Okay, now what do we do?" So, you can't send somebody to a training class on a security tool and then go, "Great, you're done." Uh, you can't have them do a CISSP and then they're done. Because the real world is so different. Learning how to recognize things in your particular environment, what a particular type of incident looks
like, and then figuring out what you can do about it requires a lot of experience that, you know, people just don't have. The the other problem is that um this sort of expertise costs so much money that most organizations are fighting with the security vendors to hire those people. I know a lot of people who bounce back and forth between vendors and and uh other other institutions and then they come back and then they go forward again. Uh but if you're trying to compete with some incident response organization that can pay 500,000 a year for a senior incident response person, there's no way you're going to be able to hire them for your uh institution,
which is what drives organizations into outsourcing whether they want it or not. The next one is the next factor is capability. even if they know what to do, can they do it because there's so many different constraints in the environment. Do we have anybody here in aviation security? I just want to say kind of um yeah, I mean fail fast will not fly in in aviation so to speak. You cannot do fail. You cannot afford to get it wrong. Um Dan Glass who was CISO for American Airlines gave a really good talk at RSA one year where he laid a lot of things out including what the patching process is and at that point he described where you had to have
one person in the front of the plane, one in the back of the plane and one down on the tarmac in order to be able to patch. So um now these sorts of constraints in health care I once heard a doctor saying on the stage he said I do not want to see my patient die on the gurnie with his privacy intact. You cannot fail closed in, you know, a lot of circumstances in healthcare. It's just it's just not a thing. You can't do that. In telco, the cultural imperative is to keep those packets moving. You cannot block them. Um that that is a decision that is very controversial in an area like a telco
um where if even if that's the right answer for dealing with something, no, you shouldn't be blocking that. all sorts of different issues and constraints. I'm sure you can all tell me about the particular constraints that you're under in your organization. Uh but there are a lot of things they can't carry out. In the private in the public sector, for example, the practice is to use your infrastructure until it wears out and falls over and then you can't provide your services to the citizens anymore. And then you can go to the legislature and say we need new hardware, we need new software, we need this. But it has to come to that point. Otherwise, until then, you have to pile
everything on to the few instances that you have that you can afford. I remember when I started at this agency, we were sourcing our spare parts for our hardware from eBay because that's how old the hardware was. Uh, and that's just good stewardship of taxpayer money. you know, use it as long as you can until it wears down. That is exactly the opposite from our imperative in the industry to keep upgrading, keep upgrading. Things are obsolete, things are eol. Um, how many breaches have we seen these days as a result of endof life hardware that um, you know, these organizations never intended to do another capital outlay for this. Uh, I was getting a CT scan one time and I
asked the technician, you know, how many times do you patch this thing? And he said, 'Oh, we we can't patch it anymore. It's so old that it won't even hold functional patches anymore, much less security ones. And you know, if you're paying a couple of million dollars for a CT scanner, you're going to use it as long as you can. So, there are all of these things that are just facts of life for people who are dealing with this. And then finally, influence. Can you get your suppliers to fix things? If you are a really large corporation like American Airlines, you can say to your suppliers, "Yeah, we're going to need you to fix that." And they will. But if you're
working for a state agency, they'll go, "Well, you're the only one who's asked about this, so no, we're not going to fix it." Or, "Well, if you pay us to fix it, we'll fix it." So, what kind of influence can you have on your suppliers? We know supply chain security is an important thing. We just talked about it with Blackbod. But um can you actually cause something to happen? Now I want to talk about how it's not just organizations but it's also individuals who are falling off the edge who are falling below this line. I do not ever want to hear this line again. Users are the weakest link. Wow, Adam, the grapa is really working.
Um, I do not want to hear this anymore. First of all, why are we depending on users to be the front lines of defense? Why why do we think this was a good idea? Well, I kind of know why. I kind of know why it started. Because when I started in this in the 80s, we all had the same general background. We all understood the same things. You could say something was intuitively obvious because to everybody it was. That is not the case anymore. And it is unfair to expect people to know the same things that we know or to figure it out or to RTFM. Nobody has time to RTFM. They they got work to do. So, and the other thing
is that users can also be your greatest strength in your organization. they can be the best source of intel especially you know if you're doing ro specific training and going look if you're a CIS admin these are the sort of things you should be on the lookout for these are things that you might see and I want to hear about them there is nothing as valuable as somebody coming into your office and closing the door and saying I think there's something you should know so uh users are also our greatest strength but I like flipping tables anyway another aspect ect to this this wonderful article by Maggie Angler who talked to the unhoused who really run into problems
doing what we now expect everyone to do online like applying for jobs or anything if you don't have a mobile phone or you do not have an internet um something to use on the internet except at the library and you're always using a different device with a different IP zero trust is not going to work with that real well this is a really big problem. It's not just a problem uh for people who let's say you know in a family they're sharing one phone and one person takes it to work that day and so you cannot do MFA with that phone um or many many countries around the world where they do not use smartphones
uh all sorts of things uh we are creating these sorts of of architectures and best practices I hate that one too. But best practices for security that are locking out people who do not have the technological privileges that we have. Also, I love Lee Honeywell. Um she talks about securing what she calls the cognitively vulnerable among us, the people who are she means the ones that are most likely to be caught up in fishing or other scams, BC, uh that sort of thing. But um it's easy to think of this as old people and um yeah uh my kids complained to me when when they were younger that I knew too much about tech and I wasn't
supposed to because I was the wrong generation. And I said, "Honey, who do you think built the internet?" So, please stop saying your mom, you know, or my mom can't do this as a shortorthhand for saying people who are not in our field and therefore don't know what we know because I'm old enough to be the mom of a lot of you people and I'm just here to say don't do [Applause] that. So, what is but it's still a really valid point. Who is the cognitively vulnerable? I'm going to argue that all of us can be cognitively vulnerable at some point or another for a lot of different reasons. It can be a permanent state, you know, where
somebody is um let's say someone uh with Down syndrome, you know, is learns well enough to navigate things online. Uh but there are some things that they need help with. Or it could be periodic. As my parents were declining, they had good days and they had bad days. And so I couldn't just take things over from them because they I wanted to help them keep their autonomy as soon as as long as possible. So I had a a durable power of attorney that was already in effect and I could say to them, you know, "Mom, you look tired today. Do you want me to log in and pay this for you?" So I'd have to
be prepared to step in at different times. And we don't do digital delegation very well at all because half of our uh half of our stuff requires us to be able to share a password with somebody for an emergency or for an event like this. Can you log in and do this? And the other half of our security is trying to detect those people who to see if they're the same person we gave the password to. So, you know, there's a lot of conflict there that we have to we have to revise. We have to think about this. It could be our co-workers, somebody who's, you know, not doing well, somebody who's in a crisis. Uh
could be our loved ones, could be our partners, somebody who is having a psychotic break or a hypomomania episode and they just can't handle what they normally do. And you have to be able to help them through that. And then there's also, you know, ourselves. No matter how old we are, no matter how much experience we have, we can be cognitively vulnerable at different times. This is the tough part of the presentation. I haven't talked about this in public before, so but I think with this this crowd, I can get through it. This is my husband, Marcus Vber. He died in 2023, two weeks after he was diagnosed with brain cancer. He by the time he got into the
ER, he was not able to speak anymore. He was barely responsive. There was no time for us to talk about anything. When he passed away, the only thing he left me was the the password to his password manager database on a little piece of paper in a secure location. But he didn't tell me where it was and he had he had like 10 laptops. I never had any access to that stuff for we met when we were both CIS admins. We met on IRC in 1990 for 30 years. He built and ran our infrastructure at home. I didn't touch it because it was his. I did not get any have any access to his stuff because I
respected his privacy. So I just never had any loginins. So this was his the infrastructure he left behind. And actually there's another there's another row of machines that you can't see out of frame here. Um all all of this stuff. And you know I've I've been in I've been in security for 30 years. I've been in tech for 40 years. Once I found this password, I should have been able to work my way to figure out what to do with this stuff. I should have, but I couldn't. My mind I was suffering from long co. My mind just went blank. I had to deal with my kids' grief. I had to deal with mine. And I I
just could not bring myself to start. So I I messaged a friend and I said, you know, hey, is there anyone at Austin Hackers Anonymous who I could hire to help come help me with this? And he said, 'Oh, I can come over on Thursday. That friend was HD Moore. And thank you, HD. Thank you so much. Um, he came over and I fed him pizza and he went brow on all of the keyboards and broke into everything. Reset the passwords. He mapped everything with run zero. Turns out we had a cluster of 12 Raspberry Pies. I don't know why. I don't know. So, I have I had no idea. There were actually I think four laptops in
this picture. I don't know if you could spot them because some of them are like under other things. But, you know, there was all this stuff. He did all this for me. Wrote down everything. He said, "I've set up a VPN for you." Because by then I moved the kids to Colorado and I had to to get into this. Uh, he did all this stuff. I still could not touch it. I could not lay hands on it. You know, if you build something for that long, for that many years, it it's like it's a reflection of you. It's a reflection of your brain. It's a reflection of your soul. And it was the last part of him
that existed. So, I couldn't touch it. And a year went by and I was coming every month to clear things out of the house. This was all still running in an empty house for a year. I still could not my mind would just blank when I would sit down to try to do it. So finally another friend of mine, Pablo Brewer, came down to uh Austin and he just started he put his hands on the keyboard and started doing backups for me. And that was what I needed to, you know, get there and do what needed to be done so that I could shut down this last part of it. So, as you can see, I I should have
been able to do this. I couldn't. I was cognitively vulnerable. Um, oh, and by the way, he also ran our email server at home. And in a great burst of irony when I was being interviewed about this, our email service was in the bookcase right behind. So I was like, "Yeah, you know, email servers, they're a thing." And and CNN never called me again. I don't know why, but um yeah, so you know, taking care of all that and then pulling it down. I know there are a lot of you out there who have had to deal with this with the digital state of a loved one and you have all sorts of mixed complicated
feelings. Feelings and security are not inseparable and yet we pretend that they are. Um the military understands this really well. When you're having a very bad day, what you need is very clear instructions. This is not because soldiers are stupid. They are not. It's because when you're having the worst day of your life, you know, you're you're injured, you're cold, you're terrified, you just saw your best friend get killed, you need something that is very very clear and and easy to understand. So they make things you know whe whether there are procedures that are written one sentence at a time you do the one sentence and then you go to the next sentence and then you do the next
sentence you know even and also you're trained on these things too but it's very easy to forget all of that training uh when you're in a crisis which is another reason why we should not be expecting users to remember you know their their annual awareness training or anything like that. I mean, the other thing that bugs me about awareness training, I'm sorry if there are people who who make a living off of this, but what we're essentially doing with awareness training is we are trying to install block lists, dynamic block lists that change all the time in the poetry generating custard between our ears and we expect them to remember this stuff when they have many, many other
things to do. Who thought that was a good idea and why are we still trying it? Over and over and over again. For decades, we are trying to do these block lists in the brains of our users. We need to examine what else we could do instead. Uh here's the back. Uh by the way, you know, it said, if you can't read it, it says um explosives are poisonous if eaten, do not burn, and produces toxic gases. It's not that people are trying to eat the lines, but I learned that in in Vietnam, a lot of soldiers would burn these to heat their rations. And so this is an example of giving very plain language and
explaining why you should not do it. Not just don't do it, but this is why. Um, this is the sort of thing we should be doing in our security designs as well. So the other big point that I want to leave you with is security has to usable on your worst day, not just your best day. And we have to account for that. And what is somebody one person's worst day is going to be, you know, they're all going to be different for everybody. So we have to keep driving towards simplification and empathy and understanding when we're designing these things. So now, how can we help? The really great thing is, you know, when I
was talking about this in 2011, nobody was really listening, but now there are a lot of organizations and people that are willing to come out and talk about it and understand. And this is great. Uh we need a lot more of this. Uh let's start with the fundamentals. First of all, addressing the money problem. If you know the government could just throw money at people, as I've just explained, it won't solve everything because unless you can afford to hire senior security people, you're going to have to do a lot of work training up and upskilling the people that you do have, assuming you have enough people, which you probably don't. Um, expertise, not awareness. Let's stop
the awareness training. Most organizations do know that there's a theoretical risk out there. They won't agree with you on the probability though. They will agree with you on the impact. Yes, we may have a breach. We may lose 11 billion in federal funding. But they just don't think it's going to happen. And that's the argument that I see going on a lot between security people and management is that argument over probability. And you can't go, oh, I think this is a probability of five. Well, I think it's probability of three. Um, but if you do talk with them and you kind of lead them through, let's say, the top level um hierarchy that you find
in um something like fair factor analysis of information risk. It is great because you can say, okay, here's the factor. How how probable do you think this is going to be? And guess what? If somebody provides the answer, they're more likely to believe it than if you try to tell them what the answer is. So there's a lot of hidden expertise in risk management that you know your management has. It's just not in the same words that you use. But if you talk to them and say, "Okay, three out of 10 of our systems, you know, are behind on their patching." They'll go, "Oh, yeah. Okay." Now it's seven out of 10. they'll start to feel a
little nervous and if you go okay 10 out of 10 of our servers are behind they will say okay I guess it's time to do something about it so they will kind of get a feel for what the risk is if you help them and if you frame it in a way that's meaningful to them now let's talk about capability um there are some you know if if you go to an organization and they say yeah we don't run our own network so No, we can't put any firewalls in and we can't tell them to do what to do with the firewalls. Uh, you know, you're kind of hosed. But there were a lot of things
that are non core to the business that are well understood by this point that are well scoped that you can migrate off into something else like email. Um, there are only so many use cases in email. It's really well understood. uh nobody really almost nobody objects anymore to having email hosted by a service provider and run with a well-known application. Uh payroll has been outsourced for decades because everybody does payroll more or less the same way. So if we can identify other things that can consolidate well onto those sorts of of standardized providers, it may not be the way that that organization's used to doing something, but they can kind of fit into it if you trim the edges off, you know,
can we move these some of these things so they don't have to worry about anymore. Um other other capabilities, can we understand what their constraints are and help work around them? not just say we're going to regulate harder until you comply. That's not going to work. We have to understand what the real obstacles are and not just free tools and training. Either most people either suggest throwing money at the problem, which again does not necessarily solve everything, or say, "Oh, we're going to give you tools for free. We're going to give you training for free." As I explained, that's not expertise. That doesn't help. just throwing stuff at them and going, "Well, we have a whole
list of free tools for you to use. Good luck." That's not going to work either for all of the reasons that I that I talked about. And you can't just do scanning and solding. I'm sorry if you're there people here who do red teaming, who do testing, but that, you know, that's one of the I know you work hard, but that's one of the easier things to do is to go, "Oh, you missed the spot. That is very annoying to me as a born and red blue teamer. Uh because it's, you know, it's not helpful. Even if you say, "Oh, I found this and there's a patch for that. See you. I'm on to my
next one." Yeah. Not not not helpful. Um I don't know if you read the essay by Leslie Carheart, Tax for Pancakes. They did an excellent essay about what's wrong with hiring in the industry right now. And a lot of it is that people are getting trained out of whatever pipelines just to do pen testing and software. And there is a whole bunch more um to security than just poking holes in things and and pointing out flaws and pointing out this sort of thing. Being able to build something in a very imperfect environment is so much harder and so so worthwhile. Um, you know, so there are some academics who are actually trying to solve real world problems, but there are
other ones that have a really beautiful, wonderful theoretical problem and a theoretical solution. And yeah, yeah, that's very nice. And then they throw it out there and go, well, somebody will pick it up and try with it. First of all, should they be making money off of it? And secondly, you know, who's who's going to spend the time to actually implement it in the real world and not just throwing it over the transom. How many people here did not know what the word transom meant until they saw a picture? I had a terrible time searching for an image of this on Google. Nobody knows what a transom is anymore. Uh it's this little window thing o that would
help with air circulation over a door. And the expression to throw something over the transom would refer to something like a manuscript where you couldn't get in to see an a publisher or an editor, but you and the door was locked. So you just kind of throw throw your manuscript on paper over the transom and hope that they would read it and and decide to publish it. So don't just say, "Okay, I've got this whole list of things you should do. Here you go. Bye." Because that's what I see most of the solutions out there for. Even, you know, even says it, bless their hearts, um, you know, they cannot they can't actually go to every organization
and lay hands on keyboards and do it for them. But if you were doing a list, you're going to show that to somebody and they're going to go, "Yeah, this is a great idea. I agree." But, you know, I've got something on fire right now. Uh, so none of these things are really truly helpful. So, I would ask you to learn the difference between helping and being healthy. Hey, I'm helping. I'm I'm finding all these problems for you to fix. No, that's not helping. That's being healthy. Um so you know think about what you are suggesting and remember there is no just in security. If you're using the word just you do not understand the
problem. Um um yeah, please you know because as a CESO I would go to black hat and whatever and go oh great these are all talks about more problems I need to worry about this is not a good time for me I'm not enjoying this and and you know I can learn some things but they'll just make me more depressed. So whatever you are finding try to take the next steps and figure out talk to somebody who actually has tried to solve this and try to work with them on a way to actually do it. There are so many complications to things. Uh, for example, I had an outsource team uh do a an assessment of a 10-year-old customer
in single sign on portal and uh they they did it and then they did the fixes and they they turned it around in about six weeks. It took me a year to roll out those fixes and that's a whole other talk between standing up a new development server for the code because we didn't have one anymore because it was 10 years old and nobody was working on it all the way to doing traceability matrices for change control to explain every line in the 500page PDF report and explain why we had to make a code change for each one. um a a developer who was working on this part-time who decided to do something that broke the build for like two months
until we finally took it away from him and fixed it. Other dependencies that we discovered uh for example the the we were going to encrypt the passwords and the credential string. Great idea, right? Everybody should do that. But those credential strings and the passwords were being passed to all the applications. Why? I don't know. the applications didn't check the passwords. I don't know why, but it broke a lot of stuff when we encrypted those credential strings. So, had more work to do. So, please learn the difference. Um, there are organizations that are helping now and this gives me a lot of hope. uh the cyber civil defense initiative. Uh you should go to Grace's talk at 1 PM. She's actually with them
and she will be talking about the work that they're doing. This is being funded by Craig Newark of Craigslist. Um and like like me, Craig is a boomer and he grew up in an air in an era where there was such a thing as civic duty and civil defense. Um and so he is funding a lot of initiatives to help protect the whole of society. Uh they're doing great stuff. Uh Common Good Cyber is an organization, a foundation that is uh trying to help get funding for nonprofits who are helping to secure the internet like Shadow Server, trying to get funding for those organizations to keep those things going. And by the way, isn't it really
sad that these organizations have to go around cat in hand trying to get private money when it's really for the good of everybody? Um, I just recently joined the global forum on cyber security expertise. I'm on a committee to build capacity for cyber security in the Americas. Uh, so we're going to be uh working on that. And then there's a great organization run by my friend Andrew Brandt uh Threat Research uh called No Havoc where that they have a hotline where they're actually just talking to people who are calling in and saying, you know, something's happened and I don't know what this is and uh just talking to people, talking them through how to recover uh when something
security related has happened on their laptop at home or something like that. Something for consumers to do. Uh, I'm also on the board of sideline security, which is a nonprofit that helps other nonprofits assess their security. And they have a great process here. They often do it in cohorts where certain types of nonprofits with the same sorts of missions can sit together and go through this process together where they are asked a whole bunch of questions translated into plain English from from this standards and then talking about what it means to them, what it means to their mission and how they can do something about it. Now, you would think that a lot of these nonprofits are just
incapable of doing anything, but they are so used to doing all sorts of things just with toothpicks and duct tape that often if you bring a security problem to them and say this is what you need to do to fix it, they will turn it around like that because they are very used to having to do that sort of thing if they understand how it endangers their mission. And let's face it, nonprofits are the other critical infrastructure. if they go down, people don't get fed or housed or rescued from human trafficking or, you know, rescued in the case of a natural disaster. Name name your stuff here, but this is critical infrastructure here. Um, and then there are
organizations that are doing mutual support and they're also using lynch pins. They're amplifying the effect of what they're doing with the resources that they have. Oh, look, it's a red queen. Where did that come from? Um, Tara and Red Queen are helping small organizations through the or using and amplifying the organizations that they rely on most, which are a lot of MSPs. So, they are they're doing that. Um, Nick Sinto, who founded Hilltop Technologies, is building much cheaper security tools and He's m and and offering services to organizations under the security poverty line, especially higher education. And he's he's making it cheaper by using students at various colleges to help write the code to provide the services. College students
can still stay up all night. They can do a night shift on the sock. I can't anymore. You can't pay somebody in a lot of cases to do the night shift anymore. But you know, the college students are crowning anyway, so they can do that. Um he he's also helping by the way one one of the higher ed institutions that that he's leveraging in this way is said university in Ukraine where they have stood up a cyber security and entrepreneurship program to try to build up skills for after the war whenever that ends um using those those students as well and the thing is the students then get hands-on experience and it helps to that get you to to spread this
sort of expertise and get cheaper services and software out there. Uh the UC Berkeley cyber security clinic, there have been cyber security clinics stood up all over the place where again the idea is to let cyber security students help with projects with small organizations. um help them to do something simple like implement MFA and again it gives the students exposure to how this is supposed to work in the real world where the traps are. Um it it is a great it is a great effort. I personally don't know if it's going to scale to where we need it to be but I I'd love to see this going on. So you can join a lot of these
efforts to help. The other thing you can do is help us understand the scope of the problem so we can fix it. I'm pretty sure that we don't understand everything in this problem yet. I suspect that it is every bit as complicated as healthcare reform was here in the US. um or or climate change dealing with the politics, the cultural attitudes, the differences, all the different constraints in the environments, the willingness or unwillingness to fund this sort of work and then understanding all the factors. You know how insecurity where you run into something weird and you go, "Why did somebody think this was a good idea?" And you start pulling on the thread and you find that at the end
of it is a decision that somebody made that sounded like a good idea at the time and in fact it probably was, but times have changed and that is no longer a good solution and you have to figure out how to rejigger that. Um, but helping to understand the problem, sitting with somebody and going, "Okay, help me understand why you can't do this, help me understand the constraints that you're working under, the the timeline and that sort of thing. And then sharing that knowledge, think, well, the reason they're not doing it is because of this. Um, that is one of the most valuable things that you can do as a security professional, regardless of what your role is, regardless of what
you're building or not building or breaking or, you know, whatever it is that you're doing. understanding what's beneath it and what's behind it is one of the most valuable things that you can do and then help us try to figure out what the right incentives are. Uh I have spent time on Capitol Hill talking to policy makers and going well you could you could do a regulation that says that you know everybody has to do that but they can't. They just can't. Uh you know you're going to be beating them until morale improves but you're not going to be improving security. So if we can trace a lot of the sources of these issues and
get as far upstream as we can and address those there that's hacking society that's social engineering you know I mean getting a thousand people to click on a link is not that that's lame sauce but get getting a thousand people to stop clicking on a link is a lot harder and even more getting fixing it so that it doesn't matter whether you click on the link or not. Now that is boss level. So let's let's work on that together. And I want to wish you all a wonderful uh rest of the day. Lots of learning and sharing. And if you want to argue with me, that's great. I will be outside and and I'll I'll have like
Terra behind me. She's terrifying. So [Applause]