Egregor Awakens: Taking a Tour of a Threat Action New Digs
Show transcript [en]
do apologize my computer wasn't being user friendly so welcome everybody
uh
group is the technical uh or is the threat intelligence arm of the company so today what we're going to start with is a little bit of background under gregor so talk a little bit about who they are what they've done some of their victims and then we're going to move into a technical deep dive on the ransomware itself then we're going to talk a little bit about overlaps with other threat actors and ways to track mcgregor is what we will finish up with so to give you a bit of an idea of who gregor is they began operating in september of 2020 and the ransomware itself is considered a variant of the sekhmet ransomware family
so around the same time maze which is another ransomware family that i'm sure you're all familiar with stopped encrypting new victims so in september 2020 as well so really what we observed was you know maze wound down and grigger started winding up so it's suspected that many of the affiliates of the maze ransomware variant have moved over to mcgregor um so once maze went down they moved to mcgregor and like many big game ransomware threat groups they do the name and shame of their victims and their extortion site is called a gregor news so you can see on the right an example of one of these extortive companies on the gregor news site um so where they threaten to release the
data if the company does not pay so in mid-february actually members of the gregor ransomware as a service were arrested in the ukraine and at the time so since about middle of february so 2 12 21 ish we started to see that their infrastructure so their c2s their leak site um have been down since then i'm just checking in the comments can people hear me great fantastic
um
[Music]
appetite and desire to conduct ransomware attacks so if they are successful and they actually succeed in getting a ransom from a company the ransomware developer who created the code gets some cut of this ransom so some ransomware affiliates are affiliate programs are anybody can join if they pay in and then others are more selective so they have to be invite only you have to be chosen to participate so because gregor uses a ransomware as a service model as we'll discuss shortly the ttps will vary between the attacks so this could be anything from those initial access techniques so how does the threat actor introduce kind of malicious code to the organization's systems and we'll talk about those um to also
sort of the things that they use for the pre-encryption techniques such as lateral movements so once they're inside the network they want to sort of figure out where else they want to move within it um ultimately they're really trying to create the maximum impact from their attack so trying to figure out you know what different parts of the network are there what shares what other um pieces should they be on in order to encrypt as much as possible when they drop the ransomware they'll perform reconnaissance so um what kinds of information do they want to collect about the system itself um because ultimately they may want to drop other tools so what kinds of things are on the
network if they also might want to target then maybe the ransomware wouldn't necessarily target itself and then doing credential stealing so in either to enable access to other parts of the system or if they want to you know save some credentials for future access just in case they're not changed they might do this as well so as i alluded to this could also be tools used in really any stage of this ransomware attack so like i said after performing some initial reconnaissance the threat actor might want to drop additional tools that might have additional capabilities so you might see something like banking bots or other kinds of credential acquisition malware so things like meemiecats um other pieces of other tools that
might help them further accomplish their goals but this will really depend on the affiliate their goals and then the organizational system that they're in so some affiliates may be or have been involved with other ransomware groups so the idea is you know if an affiliate is only working with one ransomware as a service group versus two you may start to see some of the ttps start blending together and we'll talk about this more so as people participate in different programs and move between programs you start to see some kind of blurring of the ttps that are associated with a particular group in general so mcgregor was especially prolific while it was active so by the end of
2020 they have claimed 206 victims according to the extortion site um and these were definitely large well-known organizations that i'm sure we're all familiar with um if you look at the names of targeted groups um and this how this fits into the ransomware attack landscape as a whole so looking at this chart so through november 2020 here's about the approximate breakdown of a lot of the big ransomware groups and how many attacks they accomplished through november and you can see that maze that ransomware group we mentioned originally um was responsible for almost 20 26 of the attacks so they were active for the better part of this time period so at least through the better part of
september but then if you look at a griger which as we discussed started off only in september they're responsible for about 13 so in the span of at this point about two months mcgregor really hit the ground running with encrypting as many victims as they could and then in that short time period of about three months they had already successfully encrypted 206 victims so i want to underscore that these are only the ones that were successful and that you know they published and we know about um it's very likely that there were many other attacks that actually didn't work out so this only represents a portion of these attacks so in order to understand how a mcgregor
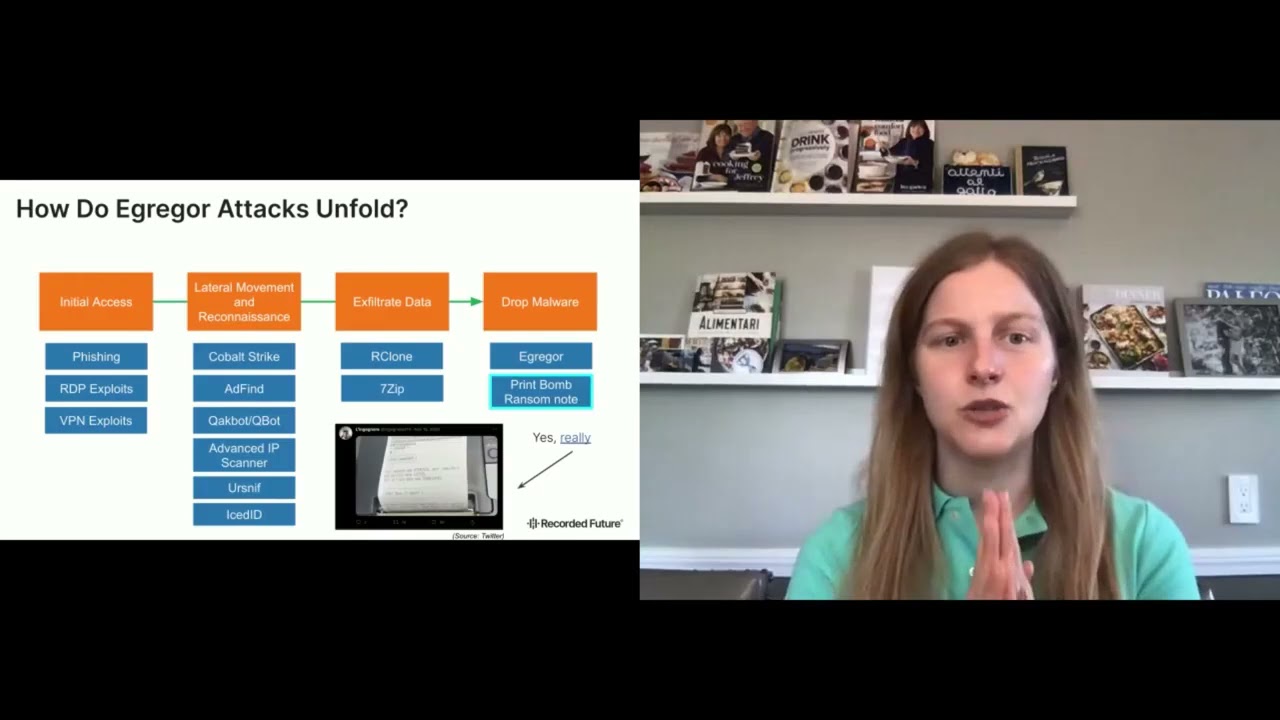
ransomware attack unfolds i've divided the attack into kind of four main stages so the initial access so again how does the threat actor introduce the malware or first stage of the malware of malicious tools to the organization's network and then moving into lateral movement and reconnaissance so now that they're on the system what are they doing to enable themselves to move around through it to collect different information and data about the group so the time that's spent here is known as dwell time so this can range anywhere from a couple of hours between the initial access and the dropping of the ransomware up to days or weeks so it really does vary based on the threat actor who's
doing the attack um their specific needs desires and really what they're trying to accomplish so i wasn't able to find any data about the average kind of a gregor ransomware dwell time but i would argue that that's maybe not super useful because it's probably very affiliate dependent and maybe some affiliates kind of have their own pattern of behavior or ways of attacking systems so next we're moving on to the exfiltration of the data so as you can imagine you can't really extort a company unless you have something to sort them with so at this stage is where the threat actor takes some or a bunch of the uh organization's data and then takes it off the system and
then that is what they would threaten to release on that extortion site so this is arguably the stage where um it's very hard for organizations to kind of mitigate against the threat of extortion itself um you may see things like fishing or anti-fishing other kind of like detections for lateral movement or reconnaissance but really this data exfiltration i would argue is one of the scariest things for a corporation and this is kind of that final stage before you get to the dropping of the ransomware so this is the stage that we're all probably pretty familiar with in association with ransomware so this is where the ransomware lands on the individual system and encrypts everything so what this looks like from the
aggregate perspective so let's start with initial access so nothing here really stands out as very aggregate specific so fishing i'm sure you're all familiar with fishing is used by pretty much any threat actor because it's works it's simple changing the lures around really to try and get a victim to click on something and download that initial stage of malware then we have rdp exploits and vpn exploits so these are fairly commonly used among different kinds of big game hunting ransomware threat actors really again nothing very gregor specific here moving on to lateral movement and reconnaissance so i'm sure many of you are very familiar with at least some of the products on this list so
cobalt strike is a open commodity tool openly available commodity tool that is used by threat actors who are apts or threat actors who are you know criminal threat actors um it's a pen testing type tool that's available for purchase on the internet really not distinctive of any particular threat actor in general but very commonly used then you have some of your more kind of common banking trojan bot uh and bots so quake bot or sniffing ice id again not very gregor specific and popular among several types of threat actors as a precursor to kind of the final stages of their malware that they drop and then add find an advanced ip scanner so again nothing really highly
gregor specific here then is that exfiltration of data so i'm sure you're all familiar with 7zip at least and probably our clone for their benign use cases this is the point where the threat actor will zip up the data and exfiltrate it so this is particularly interesting because these are both fairly benign very easily available tools arguably accomplishing one of the most complex threats for corporations to detect against and how do you start really looking at is the presence of 7-zip on my system good or bad finally we get to the dropping of the actual malware itself so here is kind of the first extremely a gregor specific stage that we have which as you kind of notice is at the
point where it's almost too late to prevent this ransomware attack because we have now introduced the ransomware to the system another particularly interesting thing that a gregor did was in at least one of the cases they actually print bombed their ransom note to a bunch of the printers at the organization so you can see in this picture an image of the rants note being printed out on the company's receipt printer so i thought that that was fairly interesting um for them to have done so moving into the gregor ransomware payload itself there's really three layers to this malware payload so the first the stage one packer which i saw obfuscating on obvious gated versions a stage two packer and then finally the
actual gregor payload itself so in order to successfully execute this payload you need to provide at run time the correct cryptographic key if you do not provide the correct key you don't it does not execute successfully um and the payload itself will accept several different kind of command line arguments to determine its functionality and behavior which we'll talk about shortly so starting with the stage one packer as i mentioned i saw two different versions an obfuscated one and an unobfuscated one so in the image on the right you can see an example of the unobfuscated um first stage packer mostly just because it was much easier to sort of see what's going on than in
the obfuscated one um and because they were their functionality was semantically identical um it suggests that this is something that was a probably a compile-time obfuscation utility um and not two separate pieces of code that were written you know at coding time it's not like they were obfuscating their code so it's probably something that a compile time or any sort of post-processing created the obfuscation so let's talk a little bit about how this works so this first stage packer contains some baked in cryptographic key material to perform the cha-cha cipher decryption and what's notable about this is that if you have all the key material required to do the decryption you are totally fine and you can decrypt
that next stage so really this first stage packer functions too like many packers obfuscate that next stage so you can see in the key expanding keynotes add the provision of both the crypto key and the initialization vector next um we i saw a very similar so all of these first stage packers were very similar and had only very slight differences so some of them were in the command line parameter that's passed so you can see here dash dash no operation i would see that vary between the samples doesn't really have much effect on the overall functionality of this first stage packer um in the basic c4 to code an xor function uh the xor value varied uh predominantly
it was three or four that i would see in these first stage packers and then finally the cryptokey and initialization vector so again not really impactful because you have all the required key material so you can be off to the races with your next stage of the packer so some other interesting things about these packers is that some of them had baked in pdb paths that were fairly similar to each other so often this will be some sort of compile time or development artifact so prefaced with m slash ewdk and m sc p was the majority of what i saw in the samples that i had so in this table you can see the distribution of the count
of these pdb paths um this could suggest that there are multiple individuals compiling the code and some were more active than others in doing so but this could also just be the set of samples that you know i happen to have um however it's definitely worth noting that pdb is very easy to modify per build um these patterns are still interesting but it's notable that in case you're not super familiar with kind of ransomware pdb's in general um sometimes spread actors like maize will use them to make snarky comments against researchers or kind of put other unrelated information in them so that it's something that threat actors will change so again i thought this was interesting
to talk about but obviously not some sort of smoking gun so moving into the stage two packers so that next stage here's where things get really interesting so how this works is that first it there's function that will read the command line looking for an argument after dash p so this is where that password that i talked about that's required to decrypt the final payload will be passed this password is then used in a rabbit cryptocipher decryption function so in case you're not familiar with rabbit ciphers you're not alone so this is not something that i've seen really in any other ransomware that i've looked at um so it's very uncommon generally i see things like rc4
des triple des aes a lot of those more common cryptographic algorithms so this stuck out to me is kind of strange after the decryption takes place there's a function that will look to see if there's a valid mz header so did we successfully decrypt that next payload as a valid pe file and if we did we run so here is really where if you do not pass the correct argument to the ransomware the correct password decryption will fail and then you will not have a valid pe file and you will not run so game over if you do not have the correct password at this point and the right no ransomware attack takes place and you bug out
so if you do pass the correct payload or correct password you get the aggregator payload itself so overall at a high level it was pretty typical ransomware it did pretty difficult ransomware type things so first it did language checks for commonwealth of independent states countries so it looked to see if the computer's language was that of one of those countries and if it found it it would bug out um deleting the shadow copies using wmi is also fairly common um so this just makes it harder for um the organization to recover from the attack so this is fairly common they do it as well um stopping processes and services that could aid in recovery and backup
so again trying to make it harder to recover from the ransomware attack and stop anything that might you know stop the ransomware attack from happening um and then finally it is ransomware so it encrypts the files on the system so it avoids specific file extensions and folders predominantly related to the functioning of the actual computer so you can imagine how encrypting things like executables and dlls would make your computer stop running um because that's kind of what it built on and what it does so in that case if somebody did pay the ransom it would be very hard to decrypt their system if their computer wasn't working so by avoiding those files it makes it
more plausible that if they pay the ransom it will decrypt successfully and here on the right is an example of a mcgregor ransom note um pretty difficult ransom node stuff and gives the victim information about how to pay the ransom so a little bit more about the aggregator payload so i mentioned it was very related to the secmet ransomware family and it really borrows heavily from that code so in the processes that are terminated in particular like we talked about that make recovery harder the extensions and file names to avoid to avoid encrypting so again related to the functioning of the computer um the ransom note names so they're both name recover files.txt the way it renames encrypted files so
after it encrypts the file it changes the file extension to um something to let the victim know something is wrong um the method of string encryption like i said i enjoy talking about strange encryption so both of these ransomware families used this same string encryption algorithm to obfuscate these strings so it's a fairly simplistic xor based cipher which is common for other ransomware families to use varying xor ciphers themselves but this particular one i hadn't seen before except in sekhmet and gregor so you can get an idea from the pseudocode here in the image on the bottom of what it does but yep same between the both and the method of code obfuscation that we use used
so the aggregator payload itself did employ code obfuscation primarily to make the control flow very confusing so the path that the code takes as it executes so jumping around a bunch and you can see some of some examples of what this looked like um in the two images on top um some of the jump zero and jump not zero to the same address different things like that not wildly uncommon when people do employ um control flow-off eusation but this is the technique so remember this for later as we talk about what some other ransomware families do and then finally they had a very similar first stage packers remember the one that we talked about that uses
the cha-cha encryption with the baked and key material those are very similar between both families
so there were a few key differences that i observed between the gregor code and the segment code so aggregate does have code for an http post request a network request um but it doesn't appear to be triggered at any point so this code was functional in the second ransomware family but not mcgregor suggesting that you know if the threat actors just kind of left it in there or was this digital in some way so there but no longer used additionally the segment code had two stages only and there was no password required to successfully execute the payload so we talked about that initial first stage packer and then it would have the segment payload but that middle kind of rapid decryption
where it checks the pat or takes the password and tries to decrypt the final payload was not there so no password required successfully execute segment on any double click and then aggregate does add a couple different command line parameters so we talked about the command line parameters that changed the functionality of the ultimate payload to some degree so dash samba which meant that link files will not have the delete on close attribute and kill rdp which is self-explanatory kills off um programs that would perform rdp programs and services that would do rdp and then finally in the dropped file name so gregor dropped uh something called dtb.dat while segment dropped sysconfig.db so i've heard a lot of people talk about
how similar gregor and mays were and then i just want to highlight a couple of the differences that i noticed um in looking at both of these pieces of ransomware so first they use substantially different obfuscation techniques than each other so on the right on the top image you can see macy's is import hashing techniques so in case you're not familiar with that um import hashing makes it harder for a reverse engineer or an analyst to be able to tell what functionality is being imported into the binary and what's called when so it's a little bit harder to see like well what what this thing might be doing aggregate doesn't use any sort of import
hashing and um it just kind of calls functions and they make sense um while mcgregor does use string encryption maze does not appear to so these are kind of like two key differences in at least the obfuscation techniques and anti-reverse engineering strategies applied by these two pieces of ransomware in addition the packers and first stages are very different from each other so we talked about the one that i observed and used for the gregor but there was a wide variety of these packers and first stages used with maze this is probably an artifact of the affiliate program so affiliates may be bringing their own first stage packers and just receive that actual ransomware um so it could be things that they write
themselves or they purchase or they acquire in some way um you'll see things that are less common you'll see things that are definitely commodity or kind of like openly available type tools but it really did vary with maze whereas at gregor's first stage was more consistent in addition we talked a little bit about the gregor code obfuscation so maze used very different code obfuscation techniques so you can see in the image on the two images on the right on the bottom um those are just examples of what the obfuscated maze source code looked like versus what we were talking a little bit about with mcgregor so other researchers have done these great in-depth kind of write-ups of what these
obfuscation techniques are and how you take them apart um they're definitely worth checking out if you're interested however there was a pretty similar looking kind of country check we talked about that cis country language check so on the bottom left you can see gregor and maze this is not really a smoking gun in my opinion it is not definitive proof that they are exactly the same code but it is really important for to mention for our discussion as we talk about similarities and differences at a technical level so yes lindsay that is just code what else so i agree the diamond model definitely still does hold here so we can't just consider the relationships from just the
technical level and we'll talk about why so you really do have to consider infrastructure actors and the victims in really fully understanding similarities and differences between threat actors so the reason why we can't just look at the technical things is that ransomware affiliates are moving to new variants they're moving between families operations are spinning up and down cartels are forming commodity tools like we discussed get used um so it starts to be that the hallmarks like the obvious hallmarks of a specific threat actor or variant starts to become blurred so let's look at a couple examples so in chain alice's analysis in chain analysis analysis of the blockchain um stuff that was associated with ransomware they saw that there was
something that suggested affiliate overlap and other possible connections between a couple of big ransomware families notably maze mcgregor sun crypt and doppelganger okay so then cobalt strike which was that tool we talked about previously has been used in 70 of big game hunting incidents in 2020 so if you remember we looked at that graph of um ransomware attacks in 2020 there were so many different families on that so if you start to think that approximately 70 of those attacks we're using cobalt strike you start to see that there is probably some overlap between who's using it and then rdp is the most common attack vector employed to install ransomware and vpn vulnerabilities are not far
behind and if you remember those are two of the things that the gregor ransomware family used and so a lot of other big game hunting ransomware families are using them too and then finally as we've talked about everyone uses fishing they will use different lures different strategies kind of different initial stage documents but just mere use of fishing itself is not enough to say it is a specific type of malware or ransomware so really a lot from the technical level that we're looking at here is just suggestive of the idea of people who do big game hunting at that broad technical level not a specific threat actor in general so for defenders there is some good news
here because many of these same gtps are used between ransomware actors so that allows you to focus some of your detections and mitigations on these common issues and tools so if we see a lot of different kinds of groups using things like cobalt strike or certain kinds of rdp or vpn vulnerabilities focusing our detection and mitigation efforts on those helps us get a little bit more bang for our buck there and then it helps us be aware of vulnerable products and tools at that high level that if many threat groups are targeting them maybe we should prioritize these for patching so for example in fbi's advisory on the mcgregor ransomware they suggested patching several rdp vulnerabilities in
2019 from 2019 to 2020 so while these vulnerabilities were associated with specific aggregator attacks now there's no reason that they won't necessarily be used by other threat actors um especially if they continue to work and other threat actors say oh these are very successful let me try that too however there's also some bad news um they're using these ctps because they're still succeeding at using them so phishing is going to be an eternal problem um the alerts are more creative now and they change very often and um it's something that they as they get very targeted and then people are very enticed by them people still keep clicking on stuff um so that's not going away
and patching does take resources so resource constraints um make it hard to patch everything that needs to be patched and you know patching may fall by the wayside as other more urgent issues arise for teams and you have to make difficult decisions about what to prioritize and then separating the good versus bad use of tools is not easy so like we talked a little bit about that 7-zip being used for egressing organizations data starting to understand um you know whether it's malicious use of 7-zip or benign use is something that is very complicated especially with the size of many organizations these days and the diversity of tools that folks have on their systems however the
worst news of all is that while these are the ttps we know and understand now these groups will evolve their ttps if these stop working or they need to um there is big money in big game hunting it is a business and while people are making money they will still want to do it and in order to do so they will try and find different ways of succeeding at it so we also talked a little bit about the affiliates and as i mentioned affiliates move between programs so maybe they pick up skills in one or find certain success techniques and then move to a new one and then now they're sitting there and these and using a lot of these
techniques in association with a new group so while we may have a very good understanding of like what a gregor's the ttp is associated with gregor now from the initial access perspective let's say look like today maybe tomorrow they will be different so really keeping kind of abreast of what are these changing ttps what should we be monitoring for over time is really important as things change and evolve and people pick up new skills and new vulnerabilities are announced so if you're interested in tracking mcgregor there's kind of a couple approaches you can take so first looking at it from the more general level so monitoring for unexpected commodity and openly available tools so things like cobalt strike and quake bot
that occurred used um this isn't a gregor specific but these tools are commonly used with other ransomware deployments so if you're just interested in ransomware in general that might be something to look for in general um unexpected presence of quake by cobalt strike on an organization system is often precursor to many different kinds of unsavory behavior not just ransomware so if you're looking to mitigate for and defend against things that are more general bad behavior that might be something worth doing and recorded feature has actually created sigma rules and urls for some of these to make monitoring and defending easier if you want to specifically track a gregor itself there were a couple of unique technical aspects that i
highlighted so first that second stage with the rabbit crypto is extremely consistent between the samples even at the byte level so being able to detect that might help you you know find ransomware samples that are associated with the greyer the strain encryption technique that was used in the final payload so both in a gregorian segment was also very unique and then finally that first stage description process so the basic c4 and xor the chacha cipher mzpe check and sleep of fail was a fairly unique pattern that was very consistent among the gregor samples so what's next everybody wants to know what's next um so now that the affiliates are arrested they're associated with gregor a gregor itself is very likely dead um
so it's pretty likely that these operators will move to a new operation so they're not done and it's possible that we'll start seeing some of the ttps that they've used so not only those other tools that they're using those commodity tools but potentially some of the lessons learned and the more i guess effective aspects of the code might carry to a new operation itself but it's key to remember that ransomware as a threat is not going to go away anytime soon and while big game hunting remains big business it will continue um if people are going to keep making money they will keep pursuing it as long as organizations are paying and the idea of that name and shame
extortion if it remains effective in getting organizations to pay it will likely remain popular similarly the formation of cartels in which groups share things like leak sites and other infrastructure will probably remain fairly popular as well as long as there is a financial benefit to doing so so thank you everybody for attending uh my name is lindsay k does anybody have any questions i'll look in the question chat okay thank you so much everybody have a nice rest of your day





