Who are the people in your neighborhood? Tracking 'Shady' CIDR blocks
Show transcript [en]
500 organizations he prides himself on being a generalist with exp python javascript networking databases as well as security specific tools like broseek application firewalls network firewalls packet analyzers and siem solutions so with no fur with further ado uh i present uh john smith awesome all right let me get this screen shared for you guys [Music] okay so hopefully you can see my screen yep good so uh again my name is john smith i'm not sure what my parents were thinking um today we're gonna talk about who are the people in your neighborhood i don't know if sesame street is even still on but uh but we're gonna talk about how to track the internet's shady cider blocks
i have a blog it's called digital vigilance someone had parked digital vigilance so i just have dignig.com it's easier to type anyway i've got two articles today but i will uh start posting more and eventually have a podcast if you want to find me in github linkedin um look for packet jockey that's a joke my brother used to call me when i took the job at extrahop networks um so uh anyway we're out ndr or wire data analytics solution so he calls me a packet jockey a little bit more about me so the the um for me in particular this um this um talk is going to be around devops right we're going to use python
we're going to use jupyter notebooks and a module called pandas now for me in in my career i've been in the industry about 23 years this is a meme or a very bad version of a meme of 13th warrior it's probably my favorite antonio banduras movie where he's there's a scene where he says i'm not a warrior and one of the vikings looks at him and says soon you will be right when i came over to the uh started working in the devops space and if you don't have a lot of money you have to leverage open source tools well you know maybe you're not a programmer well soon you will be right um i hadn't written a line of code
until probably 2012 so you know a lot of times when i would look at programming it would basically look like egyptian hieroglyphics don't be afraid if that's the case uh with respect to this presentation everything that you see today will be on my github site this is going to be a project that i'm going to track uh here but if you go to github packet jockey cider tracking you can actually use these long term i want you to be able to just do a git clone and be able to just run through the jupiter notebooks if you're learning to code right hashtag learn to code isn't just a way to get banned on twitter um it is actually something
that's good for your career it's nice to see uh with the uh kind of this return of the it generalist right for a long time we'd all become really specialized but now your next-gen products have rest apis right and json has made life a lot easier to code against so now you know we're starting to see people add the ability to just write a little bit of scripting or a little bit of code whether that's python javascript powershell something to make your life a little bit easier so again this today we're going to use python in fact here are all the tools we're going to use today we're going to use uh jupyter notebooks and for of the different modules
pandas json requests netapp csv um i know we compete with corelight but bro is an open source solution i'm not sure my company goes about that but but for the examples today we're going to use brocon.log but we'll talk a little bit about the different sources and iframe and then we are going to use uh our product that's called reveal x i'm just going to have a couple of things that i'm going to talk about there but we'll talk about showdan uh a couple of different uh ipinfo dot app i just want to cite some of the different sources that that help contribute to this namely i love that aws digitalocean and google publish their cider blocks which i think
is important firehole is great if you don't have a lot of money hole makes a really nice uh way to leverage open source uh threat intelligence so what led to this this is the only thing about our product i'm gonna show that everything else will be open source but this is a dashboard i built now this one is in our attack lab but it's basically i call it a whack tracker or a slash tracker i probably need to think of a different name but we refer to cider blocks as slash 16 slash 20 wax 16 wac24 and basically it is a here's a here's egress where we see a number of outbound servers that we're talking
to this particular cider block how many unique clients and then how many unique flows do we have and i'll get into why this is important but when you start to see a bunch of persistence right now that doesn't necessarily have to mean it's a threat a lot of third-party applications a lot of your vendors will establish persistence they don't always tell you they're doing that but they'll do that right so that they can either send metrics check licensing that type of stuff right but persistence on non-rfc 1918 addresses should be investigated if it's not a b2b partner if it's not an approved session then we need to peel that thread and tug on that thread and just see what
unravels maybe it's nothing but a lot of um a lot of solutions that exist in thread intelligence spent at least you know 30 to 60 days not on any threatened intelligence while they ran amok and then ended up getting blacklisted so we're going to talk a little bit about that today so if you notice here pivoting from a powerpoint slide into a into work is really difficult so i just kind of put the slides into the jupiter notebook so i'm going to pivot directly into the jupiter notebook here so again this is a little bit of a technical session but that said if you can just if you can get clone this or if you can grab those uh those um
jupiter notebooks if you're capable of hitting shift enter then you can use this tool now i learned a code by grabbing somebody else's product and then just editing it for myself i think that's how a lot of us i'm i'm older i'm a gen xer i'm over 50. there weren't a lot of programming classes so a lot of us in this generation are self-taught programmers so here i'm just going to walk through some of these here where first thing i want to check i just want to cover why we should be looking at particular cider blocks now our threat research team created a list of the sunburst threats now what i'm going to do is i'm going to
read this threats.json file and i'm going to create a data frame and i'm going to get a list of the malicious iocs on a per 24 basis right and what i'm getting at here is that a lot of these iocs a lot of these malicious hosts are gravitating towards a few select cider blocks right and if you notice here i've got an octet variable if i want to make this a slash 16 i simply take off the last two octets and again here it starts to take shape you see that a lot of these malicious ip addresses are gravitating towards a slash 16 so one of the things i use to determine whether or not there's a
campaign against me is if i see you know persistence against a particular cider block so moving on through this let's take a look at some of the cobalt strike servers that were observed in showdown john altos has uh alt house has an algorithm called jarm where they're able to cut out some of these uh shodan or i'm sorry some of these cobalt strike servers and if you look here in january there were 4 685 cobalt strike team servers in shogun in february they were 1639 and then obviously in march they were 114 so now let's just take a look at and see what some of these look like right so here we've got a data frame so let's
see what they look like in terms of slash 16s so this is the initial one in january that we're looking at so if i go ahead and hit this this should eventually populate on here right and this is a live demo so uh bear with me so here we can see this 119.5 112.194 again these cobalt strike servers are collating around these top cider blocks right they're sort of living in a particular set of cider blocks now if i want to look at it by port well first off let's look at it look at the february numbers and again you can see how they're going down there we had several hundred now we're down to 79
and then if i look in march i just ran one recently right and i look and i see that same 119.5 is down to six so um so a couple of interesting things there right first off that's great um but let's look at the ports that they were running on too so if we come here i want to look at the port
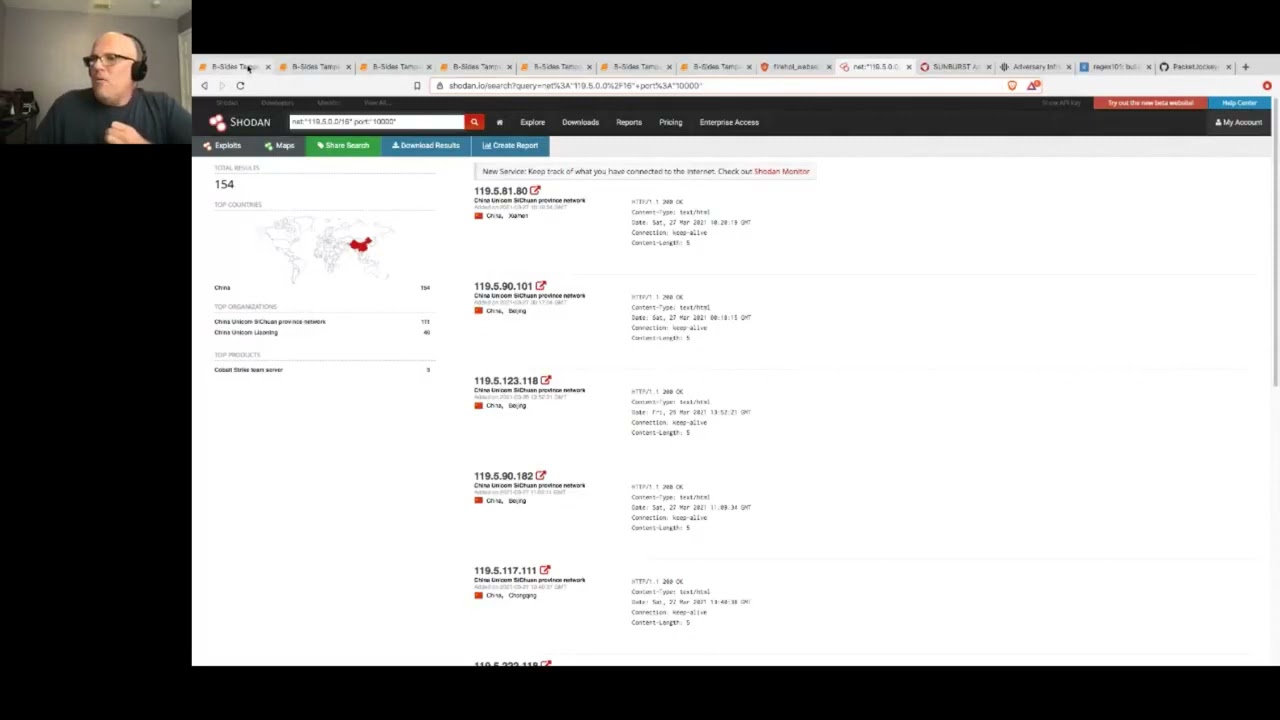
and again all i'm doing is uncommenting different parts of my of my notebook here and that's giving me back some more information about the individual here we've got the isp here on port 1000 119.5 only has six cobalt strike servers so what does that mean well let's let's take a look at showdown real quick right right now there's only 86 servers okay but let's look at something else we saw that the port was ten thousand
right and the uh network was one one nine dot five dot zero slash so again it at the start of march we only had six cobalt strike servers running on port 10 000. now let's just look at then there shouldn't be a lot running on port 10 000 right well when i do a quick search and give this a second here oh let's see what i did wrong yet um let's see here
give me a sec all right and then let's look at port 10 000. and i'll bring this home here in a second so we still have 154 systems on that cider block running something on port 10 000. now when i look here and i see that we have only had six cobalt strike servers running on port 10 000. a lot of us who have had to lock horns with cobalt strike they have something called the malleable c2 right and by malleable meaning they're able to change it now have they suddenly become shamed and decided to walk the righteous path and they are no longer hosting something malicious like cobalt strike on port ten thousand or have they just figured out a way to
evade that signature and now they're just running cobalt strike on nginx or something else right and so this is what i'm getting at is that just because you know because something matches a certain set of threat intelligence or because we don't see cobalt strike running on this cider block it doesn't mean that these people have changed their ways right now we've gone if you notice we've got 154 systems running on port 10 000 i'm more inclined to believe given the industry we are in um we are sort of paid to be pessimists right uh we are what my uh one of my colleagues calls professional haters if you look here initially in january uh we had 199 cobalt strike servers running
on port 10 000 and when i look at showdown here i'm more inclined to believe that they've just moved their uh or they've just changed their c2 so that can no longer be fingerprinted so again bringing this home getting back when you see a connection to a cider block and you see persistence to it you know just because it's not on a piece of of of um threat intelligence persistence of any kind to a remote location whether it's external uh whether it's domestic or whether it's in china russia one of the big you know um bad actors that we lock ones with a lot that doesn't necessarily mean that it isn't a problem and it should
always be investigated so pivoting over here the next slide it's cloud it's cool no it's not and now you must die now i've had some rather palpable frustrations this year with uh some of the folks we talked to saying oh no that's aws it's not a big deal we don't have to worry about it but this is uh recorded with future report i just want to call attention to a couple of things here um first off one of the things they said is our detections had an average of 61 day lead time before an ip address was found on open sources now this i don't mean to endorse any particular uh um threat intelligence platform but what
we're getting at here is that if you're using open source essentially this system is going to have 61 days to run a mock before someone actually catches it and again bringing this back to the earlier narrative of of why um if you see persistence to a particular part of the internet or a particular cider block just because it's not considered just because it's not blacklisted today anything that's blacklisted today got to enjoy some period of time where it wasn't on a blacklist and one of the other ones that i want to point out because another frustration is people ignoring domestic persistence right um if you look at the one of the other big things that they
talk about the hosting providers that had the most command and control services servers in their infrastructure were all us-based amazon digital ocean and chapa chupa right so again you know if you wanted to see who was the biggest threat or who had the most malicious uh hosted networks that foam finger is is decorated with those beautiful stars and stripes we are still waving the foam finger we are still number one when it comes to hosting malicious sites on on these cloud platforms and so we just want to walk through a couple of instances of how these cloud platforms are dangerous so again i'm coming back to my um coming back to my my pandas instance and i'm going to look
at a couple of things here you'll see a list of systems here right what i'm going to do is carve these out into cider blocks now the first one i want to show you is this web server uh this web server fire hold this right these are updated every minute so i'm just going to cut them out into slash 24-bit networks and what we're going to see is there are a number of now this one includes a number of different networks um so i didn't need to chop off the first octet yet i'm not doing that i'm just bringing the raw data up sorry so here you'll see a number of different cider blocks if you do business with one
of these hosting providers and your ip address your elastic ip is in one of these ranges then you run the risk of having your site blacklisted now i've been in the industry a long time and i can tell you what more than once i have gotten frustrated with a particular set of bad actors and just blocked an entire slash 16. now that's a bit rash but it is certainly not uncommon for someone to get frustrated and just block an entire slash 24. that happens all the time uh in my 20 years of experience where people just get frustrated and they know someone is in this cider block and they're engaged in no good so that's one area where you can have a
lot of frustration so if i want to look at now i want to do a few comparisons and i'll cover how we got these lists in a bit but if you look here i've got a set of aws cider blocks and i just want to see how many aws cider blocks are in this list of known bad web servers right so there's my aws data so i'm just going to do a quick pd merge and again this is all in github if you wanted to play with this you can definitely do it but i want to take a look at the matches here so when i click here you'll see that a large number how many
uh 38 of these aws networks or hosts are listed as known bad web servers on fireball if i want to get a account of them i can also use this and get account looks like there's one in each cider block but the point here is that just because it's aws it doesn't mean that it's safe right there's a lot of bad actors in aws and like i said one of my very big frustrations is with uh with people ignoring cloud data likewise if i want to compare to if you notice here i've got do data so this is the digital ocean cider blocks and here's a list of the google llc cider blocks so if i want to compare those if i want
to look at digital ocean you'll see that you have even more i think in digital ocean how many do we have there to put some good number and these are updated every minute so they change day by day but there you've got 480 digital ocean um ip addresses that are on that known bad actor list one of the terms i've used for digitalocean is digital slumlord if you've ever uh um my first job out of college i was with the health department and we had a lot of troubles with slumlords in the phoenix area and slumlord is basically someone that doesn't care what you're doing as long as you're paying the rent now that's not fair to characterize aws
digitalocean or google in that fashion but there is a little bit of frustration i understand they don't have a crystal ball but but a lot of bad activity goes on and the assumption of of of reputable ip addresses because they belong to those clouds cloud providers is not necessarily something that's true so again uh here you see with digitalocean you have a large number now google uh has kind of calmed down in the last couple of years but if we look here we do see a couple of google um a couple of google id addresses that that lived in there that that are part of that so again getting back to it's not cool if it's
cloud right a number of these um a number of these bad actors currently exist in in aws google digitalocean um so basically we can run this comparison of known bad actors against these cloud providers and i'm just using this section to kind of prove a point of hey just because it exists in these network in in in these particular cloud providers it doesn't mean that they're a reputable site likewise if you wanted to just you know use a different one let's say we wanted to look at level one again here there i see these and if i want to go ahead and build out my block here here we have the different blocks right i've converted them to slash
24s and now if i want to do a quick comparison let's see how many of them are in digitalocean right let's look at that one right here do data is my digital ocean data so now i'm going to do a quick comparison there you see a number of those are again in digital ocean living in digital oceans ip addresses so hopefully i haven't beaten this to death but it's not cool if it's cloud if you see something that looks suspicious then um then it needs to be investigated again back to my health department days people talk a lot about you know dates on the back of cans and our our philosophy on that was always
if the food is spoiled you have to throw it out regardless of the date on the can if if you see suspicious behavior you need to investigate it regardless of whether it's from a reputable site or not so the next one so let's do our own cider block watch right so we're going to do some comparisons we're going to use the tool uh against some log files to see if we can root out any bad any malicious or any suspect data in here so we're going to do this uh first a few a few things tracking cider block persistence what are the sources we can use well apache or web server logs are very good especially if you want to
look at ingress if you have someone trying to upload web shelves on your system something like that a build up and tear down um if you've used i don't know what the i i use i was an asa guy back in the day i don't know what the um the um logs look like but those firewall logs can also be very valuable as cam proxy logs and then there's also a rest api sources right again with the with the uh move from away from xml over to json it really has made programming and consolidating and federating this data much easier especially when you use a solution like pandas so um you know any rest api source can
can be leveraged uh as a data source to do some comparisons with and then obviously bro zeke logs which is what we're going to use today i'm going to use con.log but these logs again looking at that connectivity can also be very valuable as well so let's walk through and look at some of these now here's an example of digital oceans so digitalocean publishes their cider blocks you should be tracking their cider blocks uh i know that they're about to go public i think they're look i'm sure they have some reputable people working there but the truth is i'm not the only and i'm certainly not the first security professional to get frustrated with digitalocean
right so i'm gonna go ahead and come in here and i'm gonna build out um i'm gonna build or create a data frame out of this digital ocean csv that they published um so if i want to look at that if i want to see what that looks like right i can just come here and type cider and i should publish so there's a list of all the digital ocean data frames now if you look here some of them are slash 18 22 so for me what i'm going to do is use a net adder python module to convert all of those into slash 24s right so we will convert all of these um all of those
super nets into 24-bit cider blocks and then that will give us a list of all of the digital ocean fighter blocks and this is going to take a second but i'm basically converting thousands of networks into slash 24s so there we have the first three octets and what i'm doing here the goal isn't to necessarily create a sev1 incident so much of it as it is to give your threat intelligence and your instant responders a thread in your threat hunters a thread to tug on just to see what unravels so i have all of my digital ocean cider blocks as a slash 24 and then i take con log from bro and i convert that into a slash
24 or i grab the first three octets and what i'm doing there is i'm comparing the first three octets of conduct log with the first three octets of digital ocean and i'm getting as you can see below sorry i'm getting if you look here you'll see uh 103 104 105 106. there's several thousand persistent connections to a digital ocean cider block this is the kind of thing that you need to this is the kind of thread that we want to tug and again we're leveraging pandas a free product we're leveraging our bro con log another free product and we're able to do some nice intelligence 4 000 connections to any external cider block especially digital
ocean or let's say it's spectrum or comcast or bright house right those are probably not b2b partners now it's possible someone's hosting something on digitalocean but i want to find out i want to peel that back and i want to see why is what processes running this persistence who is it talking to because again as we talked about earlier a significant number in fact if we go back to this recorded future um study here right monitoring only suspicious hosting providers can leave blind spots as 33 of c2s observed by recorded future were hosted in the united states many by reputable providers right so again coming back to this if you notice persistence with any cider block that's external
you need to peel that thread tug on that thread and let's see what unravels because a lot of shady business goes on in a lot of reputable places likewise i want to pivot over to aws so here again kind of the same thing i won't rehash it but i've got a list of aws siders and i can come here i create this csv file and i make a data frame out of it and if you look here there's my data frame and it's very large but this is there are 208 000 slash 24s in the ec2 in the amazon ec2 space which is their hosting space and the great thing about pandas is that i can pd
merge these i can pd merge almost a million records with my uh with my bro con log and this gives me a list of all of the connections that are going to aws well one system going to a division in fact i think a lot of your there's i see a ton of traffic going out to aws what i'm looking for specifically is do i have persistence and there in this case this is a sample con.log but if you have a single ip making like 600 000 persistent connections right that's where you'll want to you know sort of tug that back hey what is this is this a b2b partner again as i said earlier too often we
tend to ignore when folks when when there's a persistent connection and it's not a blacklisted site so again any persistence going to a non-rfc uh rfc 1918 address should be investigated
so i'm gonna make this a little faster but i'm gonna just go through uh google llc real quick so again same thing with google uh google publishes here's a couple of links and again these are in the get uh the git repo a couple of links to the google ip ranges there's a lot of persistence there's a lot of bad actors running in google llc so again i walk through i create a data frame out of those google ip addresses i convert them to 24-bit cider blocks and again and then again as we did earlier i take my con log and i'm looking for uh i'm looking for persistence with any google llc ip address so if i click here you'll see
i have a large number of a significant number of of uh connections so if i want to do a quick group by i can see that okay and if you uh speaking of sesame street like one of these kids is uh is not like the others there you see a spike in persistence here with this ip on this particular cider block so again we want to be able to track persistence with these cloud providers because they they've really become kind of a medicine just because they're reputable doesn't mean that someone isn't doing something wrong now in the case of google digitalocean in aws as i said earlier i agree they don't have a crystal ball
but that said that said we we do want to make sure that we monitor them because bad actors do purchase space from them and they do engage in malicious activity one other thing i'd like to point out here this is the uh additional research from sunburst right and again here we are back with the the uh these cider blocks this is an aws cider block right here i don't that one might be i don't it's interesting when you've been in this industry this long certain first octets raise your hackles if i see uh if i see 185 or five right i start to immediately think oh this is malicious right so you learn certain cider blocks that are
or certain octets that that raise your hackles here again we're seeing that there are a number of cider blocks that participated and we saw that earlier when we pivoted over to the to the um to the um emerging threats i'm sorry the threat research our threat research team when we looked at some of the um here we looked at some of the uh sunburst data and again here you see they're sort of especially near the top a lot of bad actors are are looming around that top area then when we come here let's see when we come here you'll see also fire eye sighting again these are these are in dns responses but again this is where the bad actors live
and more and more observing and being able to track these external cider blocks is very very very uh important so moving into let's see here so the last um pin does one that i want to show here real quick um we're looking at i'm looking at this uh abuseat.org this is the i believe the cia's fact of the most infected networks on the internet so here you look you'll see this particular one i believe that's india they saw 45271 this is uh has 15 percent of the hosts are infected so i want to go ahead and create a data frame out of that convert those into 24-bit blocks and do some comparisons there so here we see uh 45271 so i'm going to
go ahead and shift enter and where this is going to go it's going to go out to this website here right and this is a really useful website so this gives me a list of all the cider blocks that are in this known bad um this known bad asn long term what i would like this project to do is map everything to an asm right and and not so much not i want to get out of converting these to 24-bit blocks and comparing the first three octets i was using an api for that um and then i inadvertently sent 40 000 requests and and and now i'm in the process of trying to beg my api key
back i'm going to try it with max mind to do some mashing up here internally and hopefully that'll get a little bit better um but for today we're comparing the first three octets so here i've got this list on this asn of several cider blocks i'm going to go ahead as we said earlier i'm going to convert these to 24-bit blocks and if you look that makes a lot of them but here now i've got the first three octets of every single address in that known bad and if you look right they have 2534 24 ip addresses and that's a lot of room to do a lot of bad stuff and they can move a bad actor can move around
as well um so now i'm going to go ahead and i'm going to compare i've done some crafty uh find and replace right so i sort of rigged the results but now i can come here and see oops in this case i guess i don't there we go all right so here i've looked at my con log i created a data frame and now i'm doing something called pd merge and that's giving me a list of all of the persistence and again if i want to group by so i can get a high level look at i this here and i see 42 connections to 112.110.120 and again this is 42 connections to a known bad asm now if you are a
developer or a programmer when you look at this programming this to happen automatically or periodically or every few hours right is not that difficult it's not that big of a reach and you can check several dozen known blacklists against your logs to be able to see you know hey do i have any persistence that i need to peel the onion back on um and that's kind of the goal of what i want to show here i didn't want to give teach a pandas class here the only expectation i would have is that you'd be able to click shift enter while you use this but that said hopefully a latent function here is that you can learn a little bit more
about pandas and learn how you can leverage it a lot of your big cyber security startups a lot of your big you know really sexy machine learning companies they're using pandas and you might think that that's out of your reach or you know when when i worked in security uh when i was a government employee there wasn't always money and so you used open source for things like this and and my point is things like bro things like pandas right these are free and you can use the same weapons that fortune or that that future 50 cyber security companies use these are all readily available um from a career standpoint uh anything you could learn
that any anything you do to add a programming language to your skill set will absolutely forward your career it will make you a very key person if you've been in the sock and you're getting a little burnt out you know adding a little bit of devops skills that can be really valuable if this looks like egyptian hieroglyphics right i all i can tell you is that it did to me when i first started learning to program to and just kind of look at it and eventually you learn to edit other people's code and and uh from there you know you can you can build some new skills so um i realize this may have been a little
bit of a a complicated uh presentation but again the only thing you would have to do to use this is clone those clone these um libraries run jupiter notebooks and then hit shift enter and then hopefully through the process of this you can you can you can maybe develop a few more python related skills but there's a lot of open source thread intelligence and if you've got logs and you've got a list of bad guys there are tools free tools like that will help you sort of mash that up and do some really interesting threat hunting and as you saw earlier we took nearly a million records did a pd merge and merge those and
matched up those bad actors within and this is on a mac with 16 gigs of ram you don't need a super huge system it's very fast and it can yield some really nice results so in closing before we open it up to questions first off thank you i know that this is different normally i do slides but i kind of wanted to do a practicum or something where we actually use the jupiter notebook um but a few things that i have as a call to action first off as an industry i would like to see us sort of demand that cloud providers do a little more in terms of accountability as i said earlier i know they don't have
a crystal ball but i do think that it's important that cloud providers my frustration with digitalocean especially that they would be maybe a little bit more responsible about the type of activity that that goes on there don't give people a laundry list of things they have to do to file a complaint i would like to see cloud providers actively you know actively going out and looking for people who are misbehaving i think that's fair i think that there should be sort of a nice lease agreement when you agree to host your stuff at a cloud provider that at least within your cider block you can expect everyone to behave in a certain way because like i said
more than once i've gotten angry and blocked an entire cider block because i just got fed up with them i would like to see them offer fortified hosting blocks and what i mean by that is your elastic ip is x and in this cider block we guarantee you that there will be no bs going on i think that's fair right that's why if i want to rent an apartment in a building and i want to have the expectation that everyone there is going to behave a certain way because we all got to live together well it's the cloud and we've all got to live together right so um so i'd like to see and i would be
willing to pay as a consumer more to know that i'm in a fortified hosting law know who your neighbors are we went earlier to that um fire hole example right where again here with these um web server blocks know who your neighbors are because if there's a bunch of bad actors i had a blog on godaddy that kept getting blacklisted well i finally got fed up and just took it down and i don't have that look i understand godaddy has a hard job they have a lot of stuff that they're working on but i ended up just having to i moved it over to uh medium but but the original blog i ended up taking down wiredata.net because
um i literally kept getting blacklisted and i i would have to go through this long you know um process with google to get it taken off so that's that's also challenging so know who your neighbors are track persistence again it's not cool just because it's cloud and recorded future is very reputable um falcon x says the same thing from crowdstrike there are a lot of malicious actors on what what you would assume to be reputable hosting providers also please again remember the foam finger is colored in stars and stripes um do not ignore domestic persistence uh that's something again i've been looking at packets now for probably 15 years and working with people and showing them
some of the stuff that that we derive from the network please don't ignore persistence regardless of where it is obviously if you don't do business in belarus or a cis block country you want to tug that thread but but keep in mind the us is still number one when it comes to uh malicious hosting providers and then know what your sources are right um know what uh know where you have some intelligence and hopefully we've seen here today it's not that difficult if you've got you know a gigabyte of apache logs then then you know it might take a few minutes to run that but it might be worth it to do some comparisons with
known bad actors and any api exposed intel you know in your sim you'll leverage those data sources and and find ways that you can compare those uh with some of the open source and then i guess last night inside it here but guys pandas is great data science is great i know it's sort of become a drinking game now especially machine learning has totally become the uh the infosec drinking game but that said you can leverage a lot of these tools that that really sexy cyber security startups use and you don't have to pay a lot of money and if you want to get started you can clone my my get repo and uh if you can hit shift enter and
type in the location of a couple of log files right then then you'll be fine um lastly what i will say um if you want to reach out to me reach out to me anytime i will not try to sell you reveal x i will not do a sales call if you want to walk through this with some of your data i will happily do that with you i'm happy to mentor anyone um who's looking to get off the sock and get into more of the architecture role um you know i'm happy to do that as well so anyway with that i want to hand back the floor to chauncey um and again thank you for
being patient this was a different presentation this is my fourth besides this is the first first time where i've actually done something in front of folks hopefully i didn't lose anybody but again thanks so much guys thank you everyone for joining the session with john smith um hopefully all of uh your questions those that had questions and q and a had those questions answered uh just know that uh john will be around uh and you can always uh just chat him directly and i'm sure he'll be more than happy to answer those questions right john absolutely yep awesome awesome all right folks it's uh 12 45 we've got uh 15 minutes here before our one o'clock
presentation and uh our one o'clock presentation will be uh julie carr and she's uh up next for uh track one uh see you soon





