BSidesNYC 0x03 interview with Anita D'Amico
Show transcript [en]
hi Anita it's great meeting you thank you so much for taking the time out to chat with me for our audience could you please give a brief introduction about what you do sure my name is Anita Deo and I work at synopsis uh where I am the vice president of cross portfolio Solutions and strategy synopsis is a big cyber uh company it is semiconductor chip designs and they also have a business unit where I work in software integrity and my job is to help our customers solve really big problems with solutions that combine our services and our products and for example one of those areas would be software supply chain risk management great and um what
is your formal background I have a very different background than most other people in this industry I actually have have a PhD in experimental psychology nice and uh there are very few people in this field who have that kind of background but I've felt that it has really helped me uh grow in this field great I I always love hearing stories from people who come from different backgrounds uh because that brings a lot of different perspectives into the problems that we're solving so thank you so much for sharing that one of the first things that I want to ask you today is there are a lot of security conferences why be NYC and what have you been most excited
about today well I I love bsid conferences and I like them because they're Grassroots okay you you get to meet people who are just starting out on a field you get to meet people who are in the middle of it people uh who are closer to the end of their career and so you have all different kinds of perspectives so I really like that I particularly was looking forward to the bside NYC because it's New York City and while I live in the metro area one of the wonderful things about New York City aside from the fact that it's close to my home is that there's just a diversity of people and there are so many people who are
involved in different aspects of security so I was looking forward to that as well and uh I was so pleased to be invited to to speak here and then when I looked at the program I said oh there's a bunch of things that I want to attend myself uhuh yes and what are those things that what do you think you'll be getting the most value out of today so I I I like to go to things that may I may not be an expert in or even may not be something that's directly relevant but I want to see it so one of the things I found that was really interesting was the FBI outreach program
okay I really enjoyed that presentation it was an introduction to the FBI and uh how they do Outreach to Citizens and I'm going to tell people about the program uh I also saw some interesting things on um cyber threat intelligence and I'm looking forward to the presentations on esom which is near and dear to my heart and also to metrics um I am very interested in how people measure the success of security or failure and how they represent that to their management because I really believe that security is essential but that you have to convince other people in the management chain to of that fact and so unless you actually meet them where they are and represent risk to
them in a way that they can understand it uh you're not going to be able to really move your security program forward so I'm looking forward to that metrics presentation great thank you so much for that and I think you hit some of my Um passion project areas as well so for example I love talking about metrics because to your point it is difficult to measure the value and articulate it so that everybody sees security as something that's essential for businesses to thrive and metrics is one way to achieve that so I completely get that I think it's not just the metrics it's also how you present it yes so my background is in Psychology and
the way I first got involved in cyber security was through visualization how do you represent a lot of network activity visually in a way that people will understand that there is is a potential malicious pattern there and it people are very Visual and so I'm interested both in the measurement and then how that measurement is expressed to people in a visual in a visual form or narrative form so that they will immediately grasp it yes absolutely because in the end it's really about communicating across a wide range of functions and bringing everybody together to move forward so I completely agree that you know communicating that Pres ing that in a way that's digestible is critical digestible is a good word
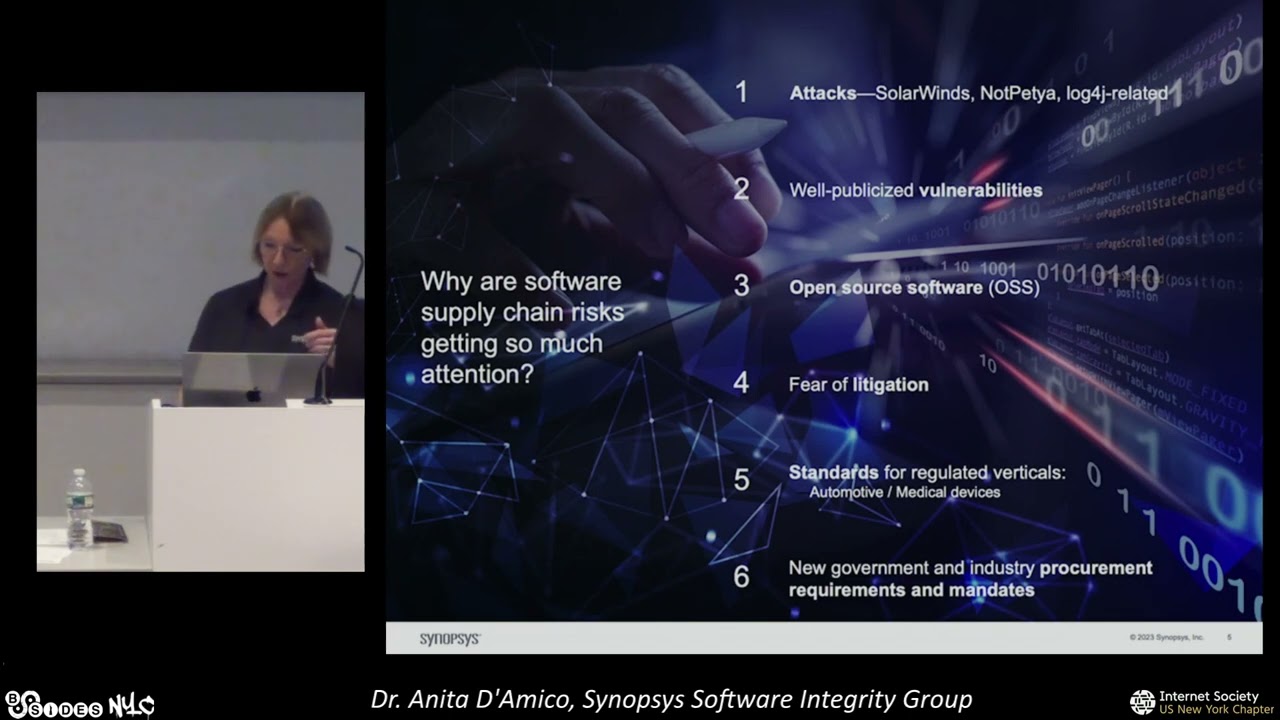
yeah so thank you for that you are speaking yourself and you have a very exciting talk coming up as well and I particularly wanted to understand what You' be talking there and for most folks people think supply chain security is like part of application security part of it is true but I don't think that represents the complete picture what are the commonalities and where do they differ can you share your expert opinion sure so software supply chain and and the securing of the software supply chain is something that starts all the way on the left during the design phase the architecture the threat modeling and goes through the software development phase which is where application
security uh mostly resides so through all the software development the proprietary code using open source bringing third party components in putting things through the development pipeline all that is application security and then you get release you release the software correct so we're still in the supply chain the supply chain continues after that when you release the software now part of software supply chain risk management is to include a software bill of materials that software bill of materials gets handed off to a number of people and they are involved in the supply chain there's the it operators well they have to deploy the software so the deployment environment is part of the supply chain there are the people who patch it and up
update the software that is part of the supply chain there are the people who are looking at risks to the supply chain such as the legal people who are looking to see if there are license violations that is part of the supply chain and then there is the people that you deliver it to and the people who deliver it that receive it from you are actually part of the supply chain as well so application security traditional application security is I would say the first third half of the software supply chain risk management process but there's a lot more beyond that yes I think you articulated that really well so it's like a small subcomponent the
application security but then supply chain security has so much more to it can you talk a bit more about how people who are consuming the software themselves are part of the supply chain I think that's a very interesting point that I had not thought of before right well actually the big interest in software supply chain Security is coming from the people who consume the software and one of those is the United States government okay um the United States government is one of the biggest software consumers in the world and certainly one of the big purchasing um uh areas for software and they were taken back by solar winds which affected a lot of networks including government
networks um by other uh certain types of attacks like code CU and and not pet you they they saw all that and they said you know what we are buying power and we're able to we need to be able to look at our software that we're receiving and know that it was developed in a a secure way got it so what the government is doing and now regulated Industries like Automotive medical devices they're doing the same thing what they're doing is they're saying to the software suppliers it's not enough that you just develop this software in a secure manner you need to attest to it you need to prove to us that that is the case because the
the receiver the the the uh proc sure of the software is actually inheriting the risk that's true which is why we have an entire field right of third party risk management as well right and and I think to your point these new um requirements they're sort of elevating the Assurance levels that are needed and I think that's a good thing for the industry it is I I think it really is it it is just ensuring that the good practices that we know you're supposed to follow you're actually following great great great thank you so much for that a lot of our viewers uh come from different backgrounds and you briefly mentioned that you have um a doctoral degree in um
psychology in experimental psychology how are you using it now like how is it still relevant you spoke about communicating what other aspects of what you learned are you applying right now in your day-to-day role well my background in exper experimental psychology has prepared me in many ways for what I do uh one important part as I described is to understand how people perceive information and when they perceive information in a certain way they'll they'll either absorb it or they won't and so I'm very interested in representing risk in the case of software supply chain how do you measure risk and then how do you communicate that to people so that that's one area of psychology um the one of the other
areas that I have used over and over again from my experimental psychology background is that in experimental psychology there's a very systematic U methodology for how to study human behavior people are by Nature variable people will do something different just to be different they don't conform to rules like in biology or chemistry or physics physical world and and so psychologists have to have methodologies to study VAR variability and be comfortable with variability and you're not going to get the same answer every time when you're when you're dealing with human beings and and so that has really equipped me for being able in security to understand that there aren't always Harden fact rues hard and F rules and that the
attackers are going to be variable and so and so we really have to be agile as well so those are just a couple of the areas that's very nice that's very well put I think it's so relevant because to your point the adversaries don't confirm also they're also human beings and they provide a lot of uncertainty and being able to meet or like rise up to that challenge itself is some kind of training that perhaps uh a lot of people are not accustomed to and you having that background really helps you there so I think that's amazing and with that I'd like to really thank you for your time it was great chatting with you I am so excited for your talk it'll
be amazing so thank you so much once again thank you for inviting me yeah