Can Cyber Mercenaries and Human Rights Coexist?
Show original YouTube description
Show transcript [en]
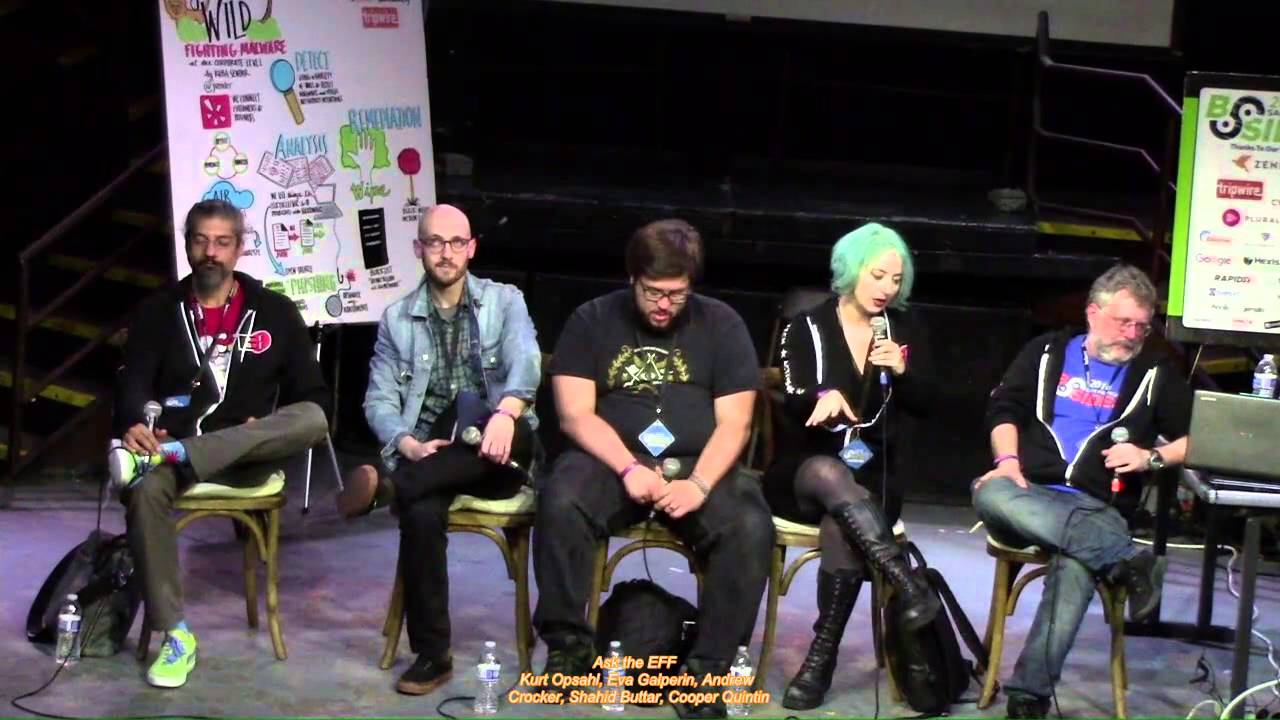
I'm Dana Torerson, vice president of product marketing with Armor Code. Uh, but today I get to be the MC for Theater 13 here and meet so many wonderful folks and as they can communicate this tribal knowledge to everybody else. That's why we're here. That's why I appreciate that. Uh, right now we've got can cyber mercenaries and human rights coexist. Uh, and Cooper Cooper Quinton if you'd like to take it away for the team. And by the way, you can I don't know if you can see it or not. There's some QR codes and that'll get you out to Slido and maybe you're used to this pattern now if you can just go to the QR code or if
you're oldfashioned because who here should actually click on anything like that? It's bsidesf.orgqna org/qna. Q N as in Nancy, A as in Apple, and that'll get you to be able to bring up the uh the the portal, log in, and then ask any question throughout this whole session, and they'll be able to cut those questions up uh throughout in real time if you'd like uh or save them for the end. With that, let's give a warm welcome to the team here. And if you wouldn't mind, uh Cooper, take it away. Thank you. Thank you. Hi everybody. Thank you so much for coming to our panel which is can cyber mercenaries and human rights coexist. The answer is no. Thank you for coming
to our panel. No, we'll go a little more in depth than that. Uh so uh as Dana said, my name is Cooper Quinton. I'm a ste senior staff technologist at the Electronic Frontier Foundation where I've been for the last 10 years working on um starting out on privacy badger and now working on uh targeted threats against vulnerable populations. So anything from state sponsored malware to street level surveillance like cell site simulators uh license plate readers celebrate devices that clone our phones all of those sorts of fun things. And I'm also a fellow at the citizen lab, the Monk School of Global Affairs at the University of Toronto, where I work on also state sponsored malware, uh,
targeting vulnerable populations such as activists and journalists all around the world. I'm here today with two of my colleagues, Bill Marchek and Eva Galprin, and I will let them introduce themselves. Oh, thanks for the lovely introduction, Cooper. Um, like Cooper, I also work with the citizen lab. Um, I'm a senior researcher uh at the citizen lab at the University of Toronto's Monk School of Global Affairs, which I guess we're legally obligated to say the full name. Um, so we can get funding or something. Um, but yeah, so I work on uh similar stuff to Cooper. So looking at um I I sort of define it in terms of what we call cyber mercenaries or mercenary
spyware companies. So these are companies some of which you might have heard of like NSO Group, Paragon, uh Citrx, which sell spyware often exclusively to governments. Um and of course they advertise it as a stealth and untraceable. So in addition to using it to fight crime and terrorism, governments say, "Oo, it's stealth and untraceable. We can go after political opponents, journalists, dissident." Um and we've seen that time and time again around the world. Um so I work a little bit on uh from a technical perspective trying to understand and and document the cases trying to do things like you know uh mobile device log analysis to identify whether devices are compromised internet scanning and internet
measurement to measure and identify and map out u infrastructures associated with with spyware like servers that are used for the infections and to receive data. Um, and also, um, getting more of an interest in the sort of quote unquote, uh, mobile forensics devices like Celebrate and Grey Key and things like that. Hi, I'm Eva Galprin. I'm the director of cyber security at the Electronic Frontier Foundation and I am legally required to tell you that I do not work at the Citizen Lab. Um I have worked with for the last thousand years uh with Cooper and I've been working at the Electronic Front uh Frontier Foundation uh since 2007. Uh please excuse me while I crumble into dust. Uh and I have been
spending most of that time working on privacy and security uh for vulnerable populations. So that includes activists, journalists, dissident, survivors of domestic abuse. uh for the last I would say 15 years or so uh Cooper and I have worked on uh tracking uh you know sort of uh government actors that are um that are going after journalists and dissident uh especially uh EFF's clients which we talked about earlier today in our tracking the world's dumbest cyber mercenaries talk uh which should give you some idea of how smart we thought these These guys were uh and we have been working on this problem for a very long time which on one hand is great because it means that we have a lot of
uh knowledge of the history of the problem and on the other hand is bad because this is this problem has been going on for a very long time and we have not single-handedly solved it. So, this leads into our into the first thing I wanted to talk to you all about, which is um and you did you did a bit of a definition of what cyber mercenaries are. Um, but I I think it'd be good to expand on that and talk about some of the type of work that they do. Uh, are they are they all the same or are there different ranges of cyber mercenaries and what what is sort of the nexus of
all this? Like what is the origin of this industry? Where does it go back to? So um I mean the origin of the industry is essentially that uh people were a mistake and uh computers also not a good idea. Uh governments uh furthermore very bad. Um this is my summary. Drop mic done. Um so the the problem is that uh governments want data which is located on computers. Sometimes they are not able to get at that data simply by asking for it nicely. They are often not even able to a to get that data by uh you know filing a court order or going through any sort of u valid judicial process. Sometimes they just want to
grab the goddamn data off of the machine. And whether or not they are allowed to do this and how much oversight there is really varies from government to government and from state to state and indeed from jurisdiction to jurisdiction. Um but the problem remains the same. The government wants data. It is living on devices. Those devices can be uh mobile devices which uh also have the the sweet sweet uh location data of uh everybody that you know cuz you keep a tracking device in your pocket at all times uh with it also has all of your passwords and photos and communications on it. So governments are thrilled to get their hands on this. Um but also a
bunch of devices you know inside of uh other governments or uh at newspapers or belonging to uh journalists or dissident. So how do you get your hands on this sweet data? Uh one of the ways in which this is done uh traditionally is that you go to uh you go to the people whose device this is and you show up with a court order. say handmade the device so that I might analyze your data. Uh sometimes you're like no I don't want to give them the opportunity to say no uh or hide information from me. I would like to uh surreptitiously pull data off of this device. Um sometimes you go to a third party. For
example, we are mostly not running our own mail servers, a horrible and dark art that uh almost no one practices anymore. And so not many years ago. Yes, I I myself gave up running my own mail server. Uh probably about 15 years ago. Uh but there was definitely a point in my life where I just sort of looked out into the distance and went I know send mail.cf. Um those days are gone. Uh so now if somebody would like to get their hands on their mail, they do not show up uh at uh at your office uh with a warrant or a subpoena. They send it to Google. And Google then turns around and ideally sends it to you, but only if uh
they it does not come with a gag order preventing them from uh from doing so. And so that's one other way in which you can get data. But again, if you are say an authoritarian country and you don't want to tip off the person that you are spying on and you would like to get data from their devices, you don't want to go through platforms that are owned by, you know, uh, companies in other states that might uh, tip your target off. And what you really want to do is you want to surreptitiously install an implant on their device. Uh cyber mercenaries exist specifically to solve this problem. Um a lot of countries that originally had the
ability to do this uh did not go to cyber mercenaries. What they did was they had uh extremely uh a very well-developed intelligence apparatus. And as part of that intelligence apparatus, they had a bunch of very highly paid engineers who didn't get out much uh who would write all of these implants uh and also keep them under very very tight wraps. Um, in more recent years, I would say like the last 15 years or so, what we really saw was the rise of a bunch of companies that said, "How about if instead of developing uh a very expensive uh to maintain and and create uh infrastructure of uh highly expensive engineers that may or may not know what
they're doing? Uh what if you just buy it from us? You can have turnkey tyranny. It would be great. Uh and in fact, we won't even charge you that much money for it. Uh we will charge you maybe like a million dollars, maybe $2 million, like you know, authoritarian pocket change. Uh and that is much cheaper than trying to sort of uh roll all of this on your own if you are an authoritarian government. And one of the reasons for this is because the number of engineers that are sophisticated enough to write this malware on a level where it is unlikely to be detected is very low. Uh and the more demand there is for those engineers, the more
expensive they become. Uh for example, there was a cyber mercenary company uh in UAE uh called Dark Matter that uh spent its time again trying to roll its own, you know, that this was the the UAE's attempt to throw money at the problem. They said, "Fine, we're we'll build our own NSA." And uh what they did was they ran around offering malware researchers something like $400,000 $450,000 a year to go move to uh I think it's Abu Dhabi. Uh and a lot of them simply said no. They said we're not going to do this. Um some of them said yes. Some of them were former uh employees of the NSA. Uh some of them uh
then kind of freaked out when uh Dark Matter then turned around and used those skills to go spy on American citizens because it turns out that if there is one sort of hard line that uh the NSA uh that former NSA employees sometimes have, it is, hey, we don't spy on American citizens. Um, and so in order to get around this problem, uh, a bunch of companies have sprung up saying, uh, listen, we are going to employ a relatively small number of these guys, and we're just going to sell to a bunch of different states, thus preventing them from having to uh, essentially build their own NSA from scratch. Uh, and that is what a cyber mercenary is at
the government level. Um below that you also have a bunch of cut rate cheap cyber mercenaries and those are cyber mercenaries who will not only sell to the government uh but will also sell to companies and to individuals and whether or not what they're doing is legal is you know uh question no a lot of what they're doing is not legal and frequently they will deny everything if you catch them. Uh but that's these are also cyber mercenaries. They're just working on uh on a different scale and they have uh a very different sort of clientele. So that's what we've got. Anything to add there? I don't have anything to add on Eva's very precise
definition of of a cyber mercenary. I went out of it. No, I but but um I mean I could talk about some other companies in the space if you think that's appropriate for now or we could reserve it to a later question. That'd be great. What's Yeah. So, what is what is some of the kremlinology of this space? Who are the who are the main players right now and who are some of the big actors that uh that we're following? Well, it's interesting to track the evolution of the industry over time. As Eva said, about 15 years ago, things, you know, look like they started getting started. Um we saw companies uh one of the first
big companies in this space that made spyware and sold it to governments was FinFisher uh based in yeah uh EFF has citizen lab both have a have a history on you know doing reports and in the case of EFF uh legal cases regarding um you know the company Pinfisher. Um, so this was a company that came out of this, I guess, the main dude, uh, Martin Munch, uh, was a former, you know, you know, Linux developer or something. I don't know, like he was a former, you know, I guess what they refer to as, um, I don't know what the term is these days. He was a defensive security researcher and then went went on the
offensive side, um, and said, "Hey, we can make money selling, you know, hacking tools to governments." Uh, so their product was spyware called Fins Spy. They had versions for PC, Mac, and mobile devices. Um, and they sort of sold this to to governments all around the world. There were big scandals in Bahrain Ethiopia um, probably other countries too that I'm forgetting. You know, they sold to a bunch of really dodgy dodgy governments. Uh, yeah. And so, FinnFisher was terrible. And there were also some follow-ups from them also uh, in the same region. But like, and you know, we we we know all about uh, NSO group now is probably the most famous one uh, uh, that's come out of
the modern era. And we have Paragon Solutions, uh, which has been which has eaten a lot of NSO groups lunch and I think a lot of their former employees as well, uh, if I'm not mistaken. Um, and but what what are the sort of broad trends that we're seeing in cyber mercenaries and how they act and what their customer bases are over the last 10 or 15 years? Are they becoming more sophisticated? Are they becoming more widely utilized? Um, or is the opposite happening? Well, it's an interesting question. I mean, from the perspective of the research that I do looking at, you know, the these sort of cyber mercenaries that sell exclusively to governments. Um,
they're necessarily becoming more sophisticated because it's a, you know, sort of arms race between defenders and and attackers, right? So, you have more and more um defenses or mitigations that developers of apps or phones or computers or whatever are adding in. Like you probably hear like oh there's a new security feature or you know some new bug was was patched and you know not not you know often it's not only just a specific patch issued for a bug but you know generally u defenders try and figure out okay what is is is this a new class of bug can we come up with a mitigation that will you know like a sandbox or something an app sandbox or a
sandboxing of a particular component that will render future such attacks even if they're not this exact attack much harder to conduct. Um, so they're necessarily becoming more sophisticated to get around all those mitigations. Um, there's also been, you know, a lot of work that EFF has done, that Citizen Lab and others in the space like Amnesty International have done tracking these groups. And of course, how do you track someone who claims to be invisible? Well, obviously they're not perfectly invisible and, you know, they leave traces behind, right? Uh, you you all could potentially imagine like how you might uh design a perfect crime, but there's really no such thing as a perfect crime, right? There's there's
traces left behind. someone forgets to, you know, firewall a server properly and it it, you know, broadcasts some interesting information. Um, or, you know, maybe someone starts up, you know, these companies all have to give demonstrations, right? So, you start up like, you know, nsod demo.com or something for to give your demos for of your of your spyware if you're NSO group. Um, so there there's ways that you can you can track this stuff. Um but because of all this work um now threat actors you these cyber mercenary groups have a a lot of things that they know not to do. Okay, we don't do this because this is how we got caught in this report and we don't do this because
that's how we got caught in that report. And um it's becoming you know they're becoming potentially more sophisticated in operational security because getting caught ultimately while it might not be the you know sort of end of of their business there are you know negative consequences down the line if you keep getting caught over and over and over. uh as we see with companies like NSO Group, you know, things uh the tide does does change a little bit. You know, they get restrictions uh from their regulator, the Israeli Ministry of Defense, um and they can't sell to as many places and Yeah. Yeah. Oh, one other very interesting trend that we saw was that uh a lot of the early companies
that we were tracking uh were located in Europe. They were located in uh in the UK, in uh Germany, and in Italy. Um after that initial first wave of companies, the finers and the hacking teams, uh we saw a migration to Israel. Uh we saw a lot of Israeli companies uh including uh most famously NSO group. And one of the reasons why we saw uh so much of this kind of technology coming out of Israel is because uh Israel has mandatory military service and a uh fairly advanced uh offensive hacking program. So if you are going into the IDF and uh you would like to uh sit in an airond conditioned room uh then suddenly learning how to write uh
offensive malware seems like a fine plan. And then once you have written all of this offensive malware, you then turn around and you go to uh Israel's equivalent of the RSA. You show up at security week and you say, "I have taken the uh extremely advanced knowledge of offensive hacking that I have learned in unit 8200 of the IDF and I have used it to build this new security product." And then VCs from Silicon Valley uh and and Europe show up and throw money at you and you start your company. Uh, Israel actually does not have a particularly strong economy. It is not a place with a lot of opportunities to get a job. But if you are looking to work in
offensive security, you can start a company and you can do fairly well. And so that's really the way in which the incentives are aligned. Um but what we have seen is that over the last few years as companies like NSO Group have repeatedly gotten caught selling uh offensive malware to authoritarian uh countries or to sort of questionable gray area countries that then use their uh surveillance malware to spy on dissident journalists activists. basically just like enemies of the government. Um other uh basically the investors have pulled out. Uh the the investors are like, "Hey, we we were not on board for human rights violations. You told us that you were just going to use this in
order to find terrorists." Um, but again, if these people had bothered to take international relations or political science instead of just learning how to uh write surveillance malware, uh maybe they might have noticed that uh for country that countries tend to frame their enemies as terrorists. And so counterterrorism will in uh in authoritarian countries usually be described uh as this is a way of going after your your political enemies. Uh for example um when we talk about uh surveillance malware and we talk about sort of threat reports uh the the mother of all ABT reports is uh the Mandant report on ABT1 uh from a number of years ago very very long time ago. Uh what Mandant was
reporting on was they were reporting on a uh threat actor in China that was uh you know an advanced persistent threat that was repeatedly going after the New York Times. And the reason they were going after the New York Times is they they were trying to unmask uh the source of a number of stories about uh sort of internal uh Chinese political corruption. And the reason why they were trying to identify the the source of these stories uh was probably not to reward them and tell them what a good job that they were doing. This is definitely an act of going after their uh their political enemies with the purpose of punishing them. Um so this is
the kind of thing that uh that this gets used for. And the most recent uh kind of move that we have seen among these companies. The hot new trend in all the clubs uh right now is actually to leave Israel because even the Israeli government has gone dude dude you you you have to you have to chill out a little bit. uh we we need to at least pretend to put some kind of restrictions on you uh and and make a a gesture towards human rights. Uh and so a lot of these companies have moved back uh to Europe. They have moved to Cyprus or they have moved to Spain. Uh I think those are primarily the two places where
we have seen uh where we have seen companies form. And the idea is that uh often this is still Israeli talent uh but it's Israeli talent that is moving somewhere else where they think that they will be bothered less. And I think I mean so this brings up an interesting point. If we're let's assume for the moment that governments are not going to want to give up the ability to spy on people. Seems like a pretty safe assumption. And so therefore, if governments are always going to try to hack people, would we be in a better off position in terms of international law and human rights uh or are we in a better off position when
those governments are doing that in-house? Uh you know, in other words, are are self, you know, or publicly funded hacking organizations better for human rights than these sort of private cyber mercenaries or do we just get to the same place in the end? Um well, you know, I think we probably get to a very similar place, right? Because I guess if if you think that that publicly funded hacking organizations are strictly better than cyber mercenaries, then you're sort of saying that well, there is some sort of correlation between the technical sophistication of a particular location and its sophistication in respecting human rights, let's say. Um, and that might not necessarily always be the case. Um, however, I will say though
that without cyber mercenaries, you don't really have the same sort of scaling because not every government can do this, but every government can write a check. Well, probably most governments can write a check, but not every government can develop this themselves. So, if you take away the industry component, then you dramatically reduce the sort of club of of countries that are doing this. I mean, I think it's interesting, too, because with the cyber mercenary uh uh industry, you get like it's an industry, right? And so, like you were saying, they have to go to trade shows, right? their employees are on LinkedIn. Um, and there's all sorts of really cool open source intelligence we can get just from that, just from the
fact that these guys job hop and these guys have to have salesmen and be public in a way that uh, for example, the NSA does not, right? Um, but so, so you know, maybe from that perspective for people who like us who are doing threat hunting, it's actually better that they are working in industry and and have more of a incentive to do it for profit than to do it correctly. and be untraceable. That's an interesting point. Yeah. I mean, you know, while the the the part that I want to respond to is I think, you know, while we see these companies definitely advertising like, oh, our spyware is stealth and untraceable, there's no possibility for,
you know, a researcher to trace back, you know, a victim to the specific organization that is that is uh you know, spying on them, right? Um, and of course that's not true. There's no way for anyone to measure whether that's true or not. Uh, the companies can just claim it. And you know if you're a government that's buying the spiral you're like oh no very impressive you know that like how do you evaluate that as part of the procurement process you can't um so if you can't really evaluate it if you can't put metrics on it then there's no way to sort of differentiate it if you're the if you're the customer like you can't say well oh this is this
uh the spyware is you know 10% more more untraceable than the other one right having a private spyware industry also creates plausible deniability for the states um if you have a threat actor that is well understood like AP1 or Lazarus or Fancy Bear uh then you know when you are looking at you know Fancy Bear's uh you know uh indicators of compromise that that's probably Fancy Bear you know you're probably you know you've got a bad case of Russians um you know the the Koreans say sorry the North Koreans were here um and if you find uh Paragon Solutions uh malware on your phone, you still don't know what state is uh all of this data is being
exfiltrated to. Uh and to some extent, this is an advantage uh for states because they have bought plausible deniability. And you can see this in uh the recent case in which a bunch of uh Italian uh targets were were compromised, including an Italian uh activist who was working on rescuing migrants from the Mediterranean. Uh in in I suppose I should probably not talk about this case because uh Bill knows more about it than I do. So uh here don't don't let me talk about your work. Bill, do you want to talk about this? Well, sure. And and this also gets to I think a broader point to your point earlier Cooper about whether customers are evolving. And I think you know one
of the interesting trends that we've seen more recently um and this is perhaps maybe just because researchers are getting better um is we've seen you know the the spyware scandals are no longer confined to like you know the Bahraines and the Ethiopas of the world um countries which are not necessarily you know role models for human rights. Um, but you know, we're seeing more and more quote unquote western democracies, right? We saw cases uh in in Hungary uh with the Pegasus project. We saw cases in Spain uh where uh the the Catalonian um separatists uh were being spied on. Uh we saw cases in Poland um where uh the government you know so they had a
change in government and the new government is investigating and they figured out yes the old government did spy on like a ton of people in government journalists lawyers etc. Um, and now most recently, as Eva mentioned, we have the cases in Italy, another quote unquote western democracy. Um, and I think it's really interesting, you know, the the the sort of it's it's easy, right, to imagine like, oh, this is a sort of a problem of, you know, oh, authoritarian governments, you know, the sort of the good governments and the bad governments. You sold the good governments, you're good. You sold to the bad governments, you have a problem. It's it's a little bit more complicated.
Um, right. It it it sort of depends on the mechanisms or means by which a particular government is or an agency is exercising their power. Are they you know respecting you know the rule of law? Are they having good oversight or are they you know trying to implement more authoritarian practices right um where they're trying to you know circumvent or skirt oversight measures to go after go after opponents. Um so this is a very you know the the Italy situation is actually quite interesting. there were kind of two at least two uh clusters of of cases um that that have gone public, right? There's this the sea rescue uh cases. Um and there's also a
case of a uh journalist um who uh Franchesco Canelado, I believe, uh who went public as as uh saying they had received this this notification from from Meta that they were targeted with with Paragon spyware. Um, and if you look at the the reporting uh surrounding these cases in Italy, it's actually quite interesting. There's a sort of, you know, reporting reporting about the the the sea rescue cases. Oh, well, you know, that the government sort of tacitly admitted, oh, well, this this might have been um uh, you know, legally authorized preventative security measures to, you know, make sure that nobody was abetting illegal immigration. Um and they've been relatively silent on the the case of the
the journalist. Of course, Italian law um you know specifically proscribes spying on um accredited journalists. So I feel like we've made a pretty good case now that uh cyber mercenaries are not good for human rights. Um but to the can they coexist part can they coexist part of our question. Is there do you think some framework legal or otherwise by which we could make cyber mercenaries and you know respect human rights to a greater degree? Uh or is this industry just inherently going to be a tool uh of of governments to violate human rights and curtail freedom of expression? Yes. Also no. Um this this is going to be the worst answer. Um so on one hand I
am extremely cynical. I fully believe that if a uh if a government is out to spy on its enemies, if it's out to uh circumvent human rights, they will they will find a way of doing it. they will find a cyber mercenary company that is willing to sell to them uh at least uh for you know as as long as it takes for them to get caught and then possibly after that and then maybe there will be another cyber mercenary company possibly run by the same people uh that will simply sell for the sell to them again. Um so bad actors are bad. Uh and the people who run these companies have a lot of uh of incentives to to sort of
frame their work again as uh as anti-terrorism as catching bad guys um while making it clear that they are not the people who decide what a bad guy is. Uh and one of the big problems with this framing is that if you sell to one government, uh even if the government that you are selling to has a good human rights record, even if you know if good states exist, which is honestly kind of questionable these days, um those states don't stay the same. States are not uh you know sort of inanimate objects in which you know their human rights record is written in stone. Uh governments change as we saw in Poland uh and in the United States
and indeed in Italy. Uh the human rights records change over time. Attitudes towards uh you know how acceptable it is to use spyw wear in order to spy on your political opponents uh change over time. They can even change depending on what part of the government has their hands on the spyware as we have seen in places like Mexico. Um so on one hand it is better to have rules about uh the cyber mercenaries and who they can sell to and the circumstances under which it is acceptable for them to sell. I think that these rules are very important but they are not the be all and end all of uh of solutions. We should not be
surprised when then uh the companies go on and break these rules or when uh governments go on and break these rules or when companies break these rules repeatedly in spite of bragging about how they have better human rights records than everybody else because they have such good oversight. I'm looking at you Paragon Solutions um and for that matter hacking team and for that matter NSO group. Um, so this is the sort of thing that happens frequently, but that doesn't mean that trying to put limits and regulations on these companies is a waste of time. Um, because these regulations create friction and they create a circumstance in which the investors get spooked. And in the end, it turns out that the thing
the only thing that stops cyber security mercenaries is uh going after their wallets. uh if you starve them of VC money, if you make it sketchy to, you know, become one of their customers, if you make it sketchy to become one of their investors, if you make it, for example, a violation of uh the state of Oregon's charter for the investment of pension companies to invest in a company with the human rights record of say NSO Group, a thing which happened a couple of years ago, um then you affect the bottom line of that company and I think that that is uh is a good thing and so to the point of government's changing uh I I want to ask one final
question then we'll move to the audience questions in our final 10 minutes here um why do you think historically we've seen so little targeting of individuals residing in the United States and also how do you think that this that this whole landscape will change under the Trump administration given that they've demonstrated a willingness to work with companies that have shady human rights records. They've demonstrated uh that they are perfectly willing to hollow out the cyber security talent within the United States government. Uh what do you what do you see as the future of this? Do you think that the US starts working with these organizations more? Do you think more people in the US are
targeted? Um or what happens? It's an interesting question. I mean, I can kind of see I think I have one opinion of where things are going, but I can kind of see two different arguments, right? Um, so one argument says, well, um, maybe we won't see, um, a big influx of, let's say, foreign cyber mercenaries, but maybe there'll be sort of a domestic industry, right? This whole the whole United States response to spyware under the Biden administration and these cyber mercenary companies was essentially, well, look, um, we can differentiate good companies from bad companies. If you're a bad company, we prohibit you prohibit you from doing business with the United States or US agencies. If you're a good
company, maybe we we do business with you. Um, and you know, the sort of adding certain companies and individuals to various sanctions lists uh who were who were quote unquote bad companies. Um, and of course, the cyber industry, the cyber offensive industry accused the Biden administration by basically saying, well, look, you're only really doing this so you can shore up the domestic US cyber industry. you just want to hurt other companies side cyber biders so you can be the big dog in town, right? Um so you could sort of see the quote unquote, you know, buy American approach, right? Where we say, okay, yeah, we're going to keep keep those regulations on those, you know, or
call them tariffs on, you know, the foreign foreign spyware companies and buy American, right? So maybe there'll be sort of more of a domestic industry that springs up. Um but I suppose it's also equally possible and perhaps more likely that you know the sort of deregulatory approach is the you know the the bigger uh impact and you know fewer regulations on buying spyware so more people just go for it more agencies per freight and it's a safer investment environment to to Evas White. Yep. Um I I am actually on team free-for-all. I I think that that is more likely where we are headed. And one of the reasons for that is that the Trump administration
has shown a a real determination to hollow out the you know all that hard one cyber security talent that the US government hired. Uh it used to be that if you wanted somebody who was reporting on uh you know sort of US uh offensive capabilities, your your best bet was to read a Kasperski report because there was nobody in the US who was going to be writing uh writing these things. Uh but also because it was it was very hard to find. Uh equation group reports are uh incredibly complicated and baroque. you read that stuff and you're like, man, someone spent a lot of time building these implants. Um, a lot of those people don't have jobs now. Uh, and I
think that the Trump administration has shown a strong tendency to embrace simple turnkey solutions from uh certain actors within Silicon Valley. And I think that this will be a big investment opportunity for uh you know local Silicon Valley companies to spin up uh their equivalent of uh of these kinds of uh cyber mercenary companies and use them to replace uh the things that we used to rely on the FBI and the CIA and the NSA to do. Um how good are they going to be? Who knows? Uh are they going to be used for human rights violations? I'm going to go with Yeah. pretty likely. Uh will they get caught? Um I don't know. But uh I know that I
will be looking for this stuff and I expect that uh Citizen Lab and EFF and Amnesty Tech will definitely be writing reports over the next few years. Well, thank you. Thank you both so much. We have about five minutes left and I want to turn now to some of the audience questions that we have. Um, so the first question comes from DuckDuck and DuckDuck asks, "As governments move toward implementing the Palm Mall process declaration, how will we see security researchers and benign/desirable business models impacted? Should how should this best be avoided or mitigated and what alternatives might you prefer?" I'm going to be honest, I'm not familiar with the Pal declaration. So, uh, maybe you can explain that a little bit and
then answer the Yeah. Um, yeah. So the the Pal Mall process is one of these quote unquote multistakeholder processes designed to you know achieve some sort of international agreement on what rules should be applied to the offensive cyber industry. Um, so you know, it it's sort of like international like many types of international law, right? The direction that this goes in is not necessarily, you know, the silver bullet, right, that's going to stop uh all sorts of bad stuff from happening, but sort of like what what can we all agree on? We got a lot of different people in the room, a lot of different perspectives. What is the thing that we're going to produce at
the end? Um, and the thing that they're going to produce at the end, I think, is sort of looking more like a voluntary code that that folks are going to sign on to. Um, and you know, the code will, you know, say like, oh, you should do this, you shouldn't do this. Um, I'm not really I haven't read I think the full the last uh uh iteration of of what the code is. Um, but I think in the long run, um, it's important, as Eva said, to have these processes. Am I optimistic that the Paul Maul process will, you know, totally solve the issue? No. Um, but I think it's good. You need both the
sort of action of these you know multi- big multistakeholder groups and also individualized action like we saw with the Biden administration with the you know designation of of uh you know irresponsible actors and things like this. Okay. Uh so the next question um I think this is an interesting question. This comes from anonymous who's asked a lot of questions today. Uh, what are your thoughts on orgs that are considered cypher mercenaries simply for the fact that their endgame is to defend marginalized international communities? Oh, it jumped in the for example the anonymous hackers or who claim to who claim to be peaceful protesters. Is that a gray area or is there I I think you know to rephrase the
question is there room for offensive cyber security uh which comes at the uh mission of defending people who are at risk and do they count as cyber mercenaries or do we think of them as somehow different? Cyber mercenaries get paid. That's how mercenaries work. Uh I I think that that is really essential to the definition. That is why the word mercenary is in there because these are companies because somebody writes a check uh in order to target the people that they want to target. And in that sense, these these groups simply don't meet the the definition. Uh that doesn't mean that everything they do is always great. Uh but it does mean that they're a very different kind of animal. Yeah.
to to emphasize that point I think um you know back in the sort of early days of of cyber security right we saw a lot of very sophisticated techniques employed by people working for free in their spare time you know people who wrote the early internet worms right that were able to infect millions or I don't know however many computers were on the internet at that time uh in their spare time right they didn't you know they they could you that was tractable to do in your spare time nowadays given the increasing complexity of everything you need not just one you genius doing this or whatever, you need a team of people and they need to spend more than
just their spare time. So, you need money basically. You need someone to be writing a check for the sophisticated stuff to happen. Uh, and with our with our last couple of minutes here, uh, Anonymous also asks, uh, if we can call out some of the local Silicon Valley companies that are engaged in human rights violations currently. Palunteer. Palunteer. Palunteer. Uh, what's what's Lucky Palmer's company? Uh, are Palmer Lucky? Oh, I I've blocked it out. Andrew, thank you. Yeah, Andrew. I think Andre and Horowits funds many companies that violate human rights. And then there's And then there's the entire uh uh defense industry as well. Yeah. Not a not a fan. We we can skip it. Um, do we have anybody else we want
to call out while we're here? No. No. Yeah. I think uh primarily while we do have a lot of companies uh in the US, but seriously repeated shout out to Palunteer uh that are excited about uh selling products to the US government that enable them to do uh greater and more powerful and invasive surveillance of uh the administration's uh many and varied enemies. Um, I think that one of the things that we really need to watch out for is that uh these companies that keep getting caught uh selling spyware to governments that spy on their enemies um are largely funded by VCs that are located in the US. And I think that those are the people that we need to
keep uh a particular eye on because if we can starve these companies of venture capital, then uh it will be much harder for them to exist. Great. So I think I have like 30 seconds left in which I will quickly answer one final question which is what do you advise individuals etc. uh journalists, private companies or local governments to do uh when they discover that they've been targeted by uh uh mercenary companies like this and been targeted by malware. What I advise them to do is contact EFF or Citizen Lab or Access Now or Amnesty International or one of the many nonprofit organizations that are doing this. And so the final part of the question was especially when those are
in located in countries that the US or US investigations or law enforcement won't work with and the answer is to reach out to us. Thank you all so much for coming to this panel. Thank you Eva Galprin and Bill Marchek for answering these questions and I hope to see you all at the party later and have a lovely evening. Thank you. Well done. Thank you folks for coming. Uh we got a happy hour starting at 5:30 sponsored by Whiz up on the fourth floor. Please go have a lovely time. It literally says that. So I have to say that