Identity Theft: Stealing Your Secrets in 0 Trust Attacks #shorts
Show transcript [en]
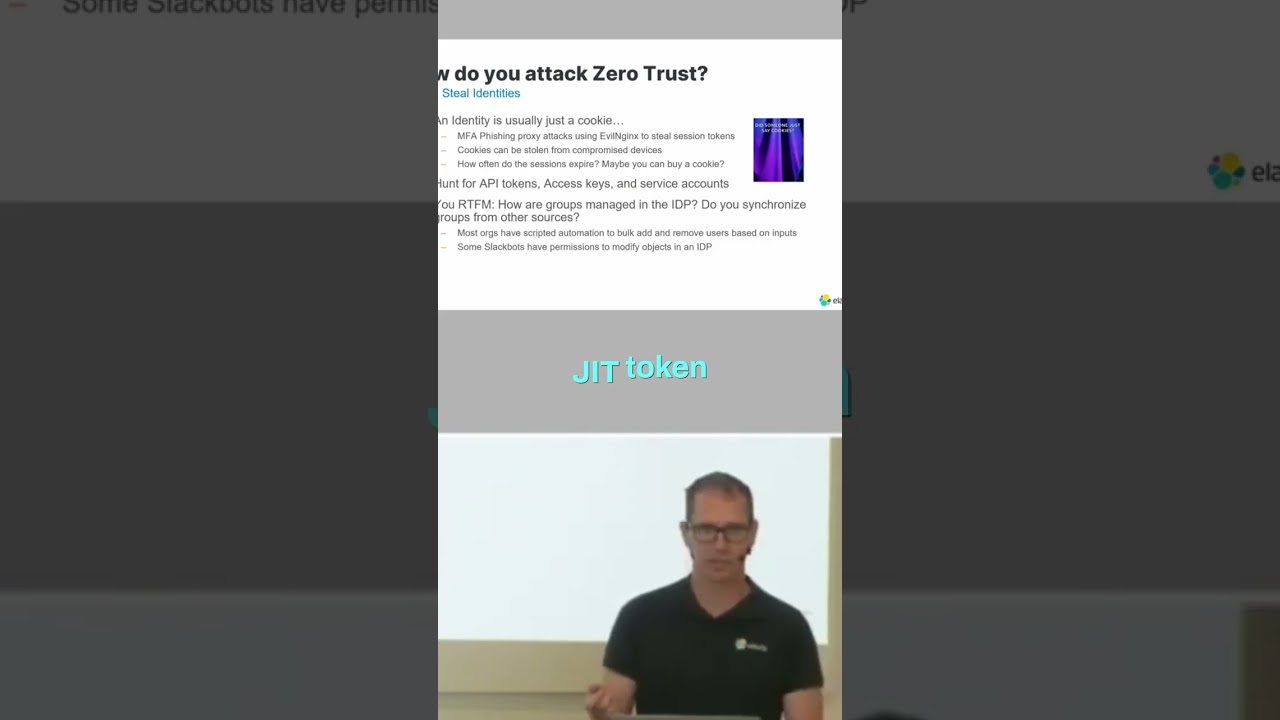
You steal an identity. It's identity theft is the core of zero trust attacks. And most of the time an identity is just a cookie. It's a session token stored in your browser or stored in your Slack application or GitHub desktop application or whatever you're using. It's It's going to be a session cookie or a jet token or JWT or some form of string of text, really. And these strings of text are generally not stored in a secure manner. And so you're going to try to attack it by fishing attacks. Uh you hunt for API tokens, access tokens, accounts. And you RTFM. You read the freaking manual when you get access in and you find out how
everything works, how everything's talking to each other. And as That's the overall view of how you attack zero trust. Going through this through the different phases of the kill chain, how do you attack initial access?





