HEALTHCARE INSECURITY: WHAT ARE WE GOING TO DO ABOUT IT?
Show transcript [en]
[Music] all right I am allowed so before get started I just want to say that this is the fourth besides Vancouver what four years ago now thirty people pretty fly people in one room kudos Alex and the team and I'm proud to say that I have been at all four of them and this is the third time speaking so you can see the title of my talk been looking at it for 10 minutes disclaimer anything I say today is my own personal opinion does not reflect current future or former clients or employers I think I mentioned my current employer once you which so we talked a bit about health care challenges opportunities talk about what we do about it and then summarize
have a pretty basic agenda the first of all who is Bob fruit so it spent nineteen years at Microsoft did a bunch of different things the last two and a half years was the security and privacy program manager for the core of the Bing search engine wrote several of several SDL requirements and published some updates through crypto STL before microsoft worked at a bunch of different companies and a lot of different products and about here and a half ago i got intrigued by the medical records space and the challenge of putting patient and clinical data in the cloud so now that GE healthcare protecting medical data one record at a time challenges and opportunities well health
care has some unique challenges first of all there's the privacy of patient information patients expect their providers to keep their information private providers i believe are required to take providers by providers means doctors nurses medical personnel are required to take the Hippocratic oath which comes out of the ancient greeks of the world medical association created the declination of geneva in the wake of World War two this is the most recent edition which I think dates from 2006 or 2008 you can find these quotes directly in Wikipedia full disclosure Wikipedia is one of my most useful information sources there are also medical privacy laws people have mentioned HIPAA Canada has Cappetta or not sure exactly how it's commonly
pronounced in Canada but bottom line is most federal jurisdictions on the planet either have or will have privacy laws that tell providers and people who handle patient data what they can and can't do with the information and then there are regulatory challenges there's a significant number of regulatory government regulations and they generally change on an annual basis data privacy again regulatory applies to that and government agencies are increasingly able to levy large fine so this was an example from October against st. Joseph's Medical Center the US Department of Health and Human Services levied a fine of two point one four million u.s. dollars for a breach of thirty one thousand eight hundred records now they breach was active for a
year which probably is a deck directly correlates to the size of the fine but if you do the math at sixty seven dollars per record that would buy a lot of beer and of course then you talk about medical devices which have to be reviewed and approved before they can be used you know certainly if I'm going to have an x-ray machine taking pictures of my teeth through my head I'd kind of like to have somebody who knows something about x-ray machines looking it over and saying yes that's approved for clinical use Canada has helped Canada you USS FDA desciple can be very time-consuming the good news is that regulatory agencies are waking up and
understanding that a lot of these medical devices more and more of them have software in them and they now actually in December issued post-market guidance final post market guidance that basically said gee if you have a component that he's updating you can update it without going to another clinical review that's huge that basically means if we have another heart bleed that affects medical devices we can go update them so they're secure should say we can update them now so they're secure and then there's an overriding factor patient safety if we're talking medical devices medical records what-have-you if it handles anything with patients you kind of want to keep them safe so consider some not scenarios I work
with medical records software let's say you are a provider or doctor or nurse and you need to see mom's records now for some reason or listen ABAB has allergies you kind of like to know that he's allergic to certain antibiotics before you prescribe them for him or worship until before you give him a shot with those antibiotics you know if you're in a hospital the hospital hospital bed I think now has 15 different devices connected to it the folks who are monitoring those devices really expect the data to be timely and accurate okay but this is a security conference you're talking about privacy and patient safety stuff which is kind of interesting but we're talking about
security so let's look at some security trends affecting healthcare I feel like I'm echoing what other people have said we all know the hacking attempts are increasing the number of reported breaches is increasing I would also claim that the unknown number of unreported breaches is increasing you know if you don't have to report a breach you don't report it but it still happened more and more records being exposed medical fraud is lucrative fraud in general is lucrative for criminals but medical fraud is especially lucrative because not only if you have payment instruments and payment and money but you also have things like prescription drugs and prescriptions that are controlled substances and if you can do fraudulent prescriptions you
both can get reimbursed for them even if you didn't actually spend the money and then you've actually got the drugs themselves um insider attacks are also concerning the IBM study was published in December estimated the 60% of network attacks were insider attacks and I don't know whether it was insiders who were malicious or the rut was insiders who were unwittingly carrying out an attack on behalf of some external attacker I the study didn't differentiate but still it's a significant percentage and the last one was very sobering when I found it cyber security ventures 2016 report cybercrime costs exceeding six trillion dollars annually in four years I guess on the bright side for all of us in this
room this does mean that cyber security is not going to go away and we will all have jobs in four years and then there's Big Data everybody's big buzzword of 2017 Oh the first quote came out of the healthcare IT Digest I subscribe to it's one of the top priorities because data sharing has some real benefits if you're in healthcare you can share for the common good the researchers love it if they can share data the study that was that 5000 patients can be expanded to 50,000 just by analyzing data that's huge um you can also spot trends see there's a flu outbreak in Calgary it'd be kind of nice to know about it as soon as we
can detect it so we can actually respond to it sharing is part of doing the part of doing business HIPAA defines what's called third party business associates these are basically not Medicare medical providers but these are folks who have some business need to see some part of your medical data typically the folks are actually paying the bill like insurance companies and government agencies and so forth and they really know who the patient is and what the diagnosis code was I would claim they don't need to see all the transcript of the conversation I had behind closed doors with my doctor um there are a whole bunch of analytics dashboards that are coming online provide different
views of Big Data one important point there's a process called DNS FD identification it's really important if you do this that you do it in such a way that patients can't be read in a fight um and there are people who claim that if you know five things about somebody you can figure out who it is um if you want to have a debate about that we'll do that afterwards I don't disagree with that characterization bottom line is Big Data large databases ap is all need to be protected and managed that's a challenge for healthcare it's a challenge for everybody not just healthcare and some additional challenges IT is not a doctor or nurses core competency they
take care of patients we want them to do that that should be their number one number two number three priority hope I should ask before I say this next this has hex bolts how many people here work and healthcare IT I see a few hands I'm probably preaching to the choir when I say that money for IT is tight and you have to support lots of history you know clinical devices in the last 10 to 20 years if you're spending 250,000 dollars u.s. or Canadian on an x-ray machine you kind of like to get your money's worth out of it on the software the software elm you'll have a mix of vendor provided applications and applications built
in-house especially if you're a bigger provider like a chain of hospitals and Technology is often outdated we're here to conversation yesterday of presentation on ATMs that talk about Windows XP and then there is inertia folks in the healthcare industry generally are very fearful of things that might break other things G don't put that update on it might break our clinical network would prevent us from providing patient care now that's a real concern there's a very much you know cliched it ain't broke don't fix it and that's something that's very true so common refrain so there's conductivity concerns as well there this is not common to health care but there is it trying to connect everything to the clinic or hospital
network and they collective connect the network to the Web API access is increasing acting on the regulatory space regulatory agencies are starting to look at that and saying you need to provide it and then at first they say all you have to do so securely but of course they don't tell you what how to do that political technology is often given designated networks the question I would ask all of you working healthcare IT is are those networks secure or private you don't have to answer that question here the answer is no we probably want to answer that question here because there are a whole bunch of us who would know what to do with that
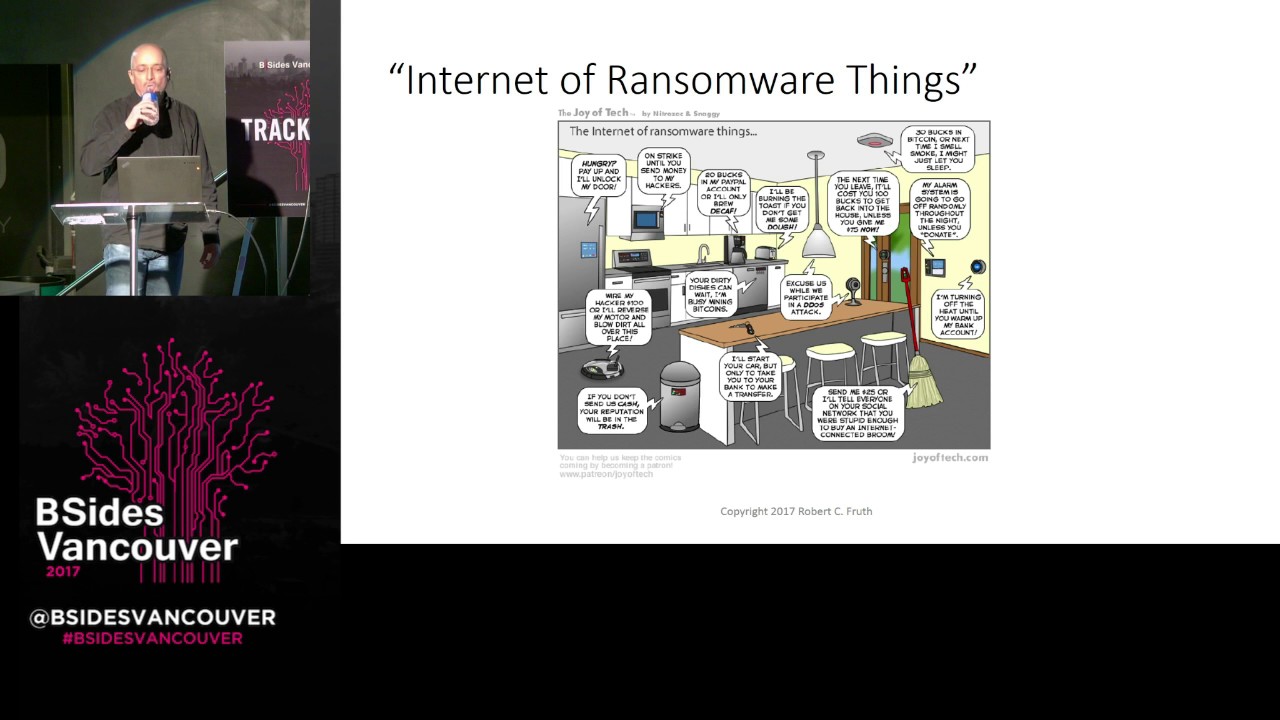
answer and then of course into the Internet of Things let's connect every medical device to the network what could possibly go wrong oral the story never assumed that something won't be connected to the Internet you get a comic like this let's let you digest for a moment this is your kitchen but I like it because I could say this is my kitchen or my bank's main offices or the credit card company processing or my doctor's office or the hospital or what have you and my personal favorite out of these is if you look at the dishwasher right in the middle it says your dirty dishes can wait I'm busy mining bitcoins why a dishwasher needs to have any bitcoins is
beyond me this is from joy of tech I stumbled on everywhere I stumbled on this but I saw this and I said oh this has to go in a presentation sometime I may use it multiple times because it's above the comic so just talks about internet of ransomware things so why should ransomware attack healthcare and the USA FBI actually says it's not healthcare they're attacking they're attacking everybody what's happened in 2016 is there were a bunch of high profile attacks that hit home and hospitals went offline in several cases for multiple days turning away patients not being able to fulfill their mission which is to take in patients and take care of them and of course there's the obvious
revenue losses as well there's some other factors at play I'm going to talk about medical data and financial data intellectual property if you're doing a medical study and you've got results that are really groundbreaking you kind of like to be able to inflict eight when they're actually become publicly known your reputation we've all heard of Hollywood Presbyterian down in Hollywood California their IT staff right now I'm sure probably does not enjoy a good reputation in that area I don't really have an opinion about the reputation I think it's unfortunate they got hit um Healthcare has like some other IT sectors one of the things about moving into the healthcare sector about 18 months ago is I feel like health cares
about where finances was five to ten years ago and it's having to catch up fast because if they don't they get wood ransomware um some healthcare organizations just pay the ransom because they want to build to take care of their patients who are see if you pay a ransom there's no guarantee you'll have your data back in the kids a Hollywood Presbyterian they paid the ransom the data came back they were down I think two days so port of entry for ransom we're not breaking any NDA's I can say that one of the typical points is phishing surprise surprise surprise somebody yesterday said he hoped phishing simply just make a phishing go away and I almost raised
my hand and stated that I don't believe that's possible to get a lot of smart people for a long time trying to do something about phishing and we can see how successful we've collectively been but we got to keep trying so here's it here's a typical attack user gets an interesting email from somebody who sounds legit email has an attachment that you have to urgently open to review these ssl spreadsheet oh you need to enable macros and a story chaos follows so moral the story don't open your email summary what I found is that health care has all the common and uncommon challenges and security plus data privacy plus patient safety which you could say it's a large
number of challenges it's too many throw your hands up and leave and we've got patients to take care of so I view these opportunities so I call this the now what slide okay you described a pretty bleak situation what do we do about it and I wish I could tell you there's a silver bullet because if there was we'd all be chewing on it right now there isn't so I believe you take a pragmatic approach understand what you're protecting patient safety the privacy of data vision privacy itself I want my doctor's notes on a conversation I had with him out on the internet for you guys to read you know medical data financial intellectual property reputation is huge
it only takes one incidence I mean think about targets IT staff they've been under the gun for the last two or three years now for reasons we all know we still talk about target and it's been three years ultimately one of the things you're protecting is the denial of service against the providers if the doctors and nurses can't take care of patients because of a cybersecurity issue that's a denial of service attack you provide protecting that capability so pragmatic approach to assess your threat landscape look at what you're trying to protect what the risks are list them all it may be a long long list it's not a trivial exercise to do then you go through like
with any other threat analysis to evaluate based on potential damage the ease of attack the script kitty can carry it out that's kind of important to know if it requires a fully authenticated administrative users for displayers deep in the data center pod is easy to carry out that attack you prioritize you apply mitigations and you monitor like crazy you want to know whether you can detect whether there's been an issue ultimately one of the things in security is you only know that you've done you think you've done enough because you're monitoring and you don't see anything and you have to assume the best you have to leverage the easy conversations the people in this room
working health care understand patient safety overrides everything else and his story full stop when I first got exposed in health care software about eight eight or nine years ago one of the conversations was to break the glass the buildings on fire scenario which is think of a hospital emergency room break the glass yeah I don't have incinerated Fallujah I don't have the right privileges to see that but the patient is needing some help privacy conversations should be short if they aren't you have an educational opportunity and if you work in health care you may be doing that educating alongside one of your attorneys because they care very much about data privacy laws my personal anecdote is working at
Microsoft for years privacy got more important more and more important over the years then I went to work on Bing and the privacy conversations got relatively shorter because you don't want to miss user search results kind of bad if somebody else's search results show up there kind of embarrassing they show up in your search pane your search history and I moved healthcare the privacy conversation is two words tip it to petty issue data privacy law done people don't argue it they go yeah you're right none it's a short conversation and there is a silver lining to ransomware health care security to healthcare IT now has people's attention the conversation is different because there's that threat you'd hope that
health care providers are sitting here going either they've been hit by ransomware second group probably hasn't hasn't been hit their intimates going why haven't we been hit the third group is just has their head in the sand because they're not thinking things through which leads me to the next slide learn from others experiences use their incident as a teaching tool why hasn't this happen to us and within reason and well-planned considering doing a response drill now obviously when somebody at the of the food chain to be approving this so that if people panicking to stop the food shake and say no this is a drill thank you very much we'll take the learnings from this and we'll go on
because ultimately if you're doing a drill you want people crashing vacations and weekends just because it's a drill you want to see whether however an immediate reaction is the ideal cases they come out here's the plan they start executing it and you pull the plug when they get to a point where they're going to talk to the PR folks about an incident you want to leverage industry best practices I'm a slightly admittedly biased about Microsoft STL since I lived and breathed it now for 11 years longer than that 15 or 16 wrote some pieces of it my point about that is Microsoft put that together because they learn the hard way it's not that they learn
everything right or that it is completely applicable to your situation but it's a piece of information it's an information source I love a wasp I work with a lot of teams doing application development the OWASP cheat sheets are wonderful absolutely wonderful and there are any number of how-to information sources I mean ransomware net defense now has its own for dummies book you admittedly this is actually Cisco licensing the image and the name and putting their own ransomware protection stuff in this so it's a bit of sales tool but the point is if ransomware defense has it has a for dummies thing there's another information source and this is not meant to be a plug for or
against Cisco I'm not familiar with the product this actually came in another digest email I got and I'm like oh yes I have to pull this in you send it to my inbox I can use the image want to talk a little bit about risks versus controls legislation and regulatory tends to focus on controls you must have a control for this you must have a control for that which is good to a point but control should mitigate risks so I like to turn the risk versus controls conversation on its head and basically say here's the list of risks here are the controls that mitigate those risks now at the end of the day if you take either approach you
should get to the bottom of the page and largely be in agreement with the set of controls you're going to put in place but I would argue that if you've done a risk-based analysis you'll have more confidence that the controls are actually the right set you
you want to use tools and best practices effectively so I'll give a plug to Alex in the b-sides Vancouver team I was shocked about 18 months ago I go out and search my name on the internet and two things in YouTube popped up and here is my talks from looking previous b-sides Vancouver or I could view myself talking and so I pulled up the first one on threat modeling from few years ago and viewed it got about two minutes and I said enough I don't need to watch myself I probably should might be educational I might learn something the reason I mentioned that talk is I talked about throughout modeling two years ago it's love fly threat modeling
to health care if you're not familiar with the stride acronym you can view my talk there's also there's a link to it in the slides there's also I'll mention a book in a little while too through modeling and she came out of client-server architecture discussions and and review of though of making those architectures secure I do claim that rep Milan can use you just about everything that Joe got myself as I happy careful I fly because I tended threat model TSA um anyway spoofing which is an attack against authentication G you want to know who's viewing the patient data okay tampering an attack against integrity you want that needing to be accurate repudiation you want to know who viewed
it or modify the patient record that is a HIPAA requirement by the way that you have will have repudiation threats fully mitigated they don't classified as that they talk about audit logs but it's the same thing information disclosure that's kind of obvious denial of service that's made preserving the capability of the healthcare device or the healthcare provider to do what their what they do best final elevation of privilege in traditional threat modeling you tend to say if you have elevation privilege you have everything and if you get root on the system you own the system it's kind of the same way in health care if you get root on the device here on the device or give your route on the patient
database you on the database and it's now whisked away somewhere else or encrypted right so if you work on healthcare products I have some thoughts and guidance for you but first remember that any product and you use in a healthcare environment I could go down to Redmond and give this talk to the Microsoft Office team every doctor's office on the planet probably uses office or an equivalent of some form if they're doing anything with computing you want to assume the worst case scenario if you're building a product you're debating whether or not to put that extra security feature in figure the worst case scenario will happen then you'll build the feature in I mentioned threat
modeling if you're not threatening your products go watch my talk or follow two solid design principles and I don't I'm not listing every single design principle on the list huge list here these are some that came to mind that really affect health care the principle of least privilege is important if you're looking at the data in a typical doctor's office or clinic or hospital you've got patient data you've got financial data you've got a whole pile of different data depending on who's viewing the data they should be able to see different slices of it so Bob the patient is scheduled appointment the front desk needs to see my calendar or needs to be aware of calendar aspects
the provider probably sees that only in terms of who they're seeing that day the back office doesn't need to see that in terms of the medical data the back office needs to see gee here's Bob this is his government ID because we track everything on that and here are some diagnosis diagnosis code so when we bill insurance or build government agency we get reimbursed appropriately the back office is not seen you see the notes on mine visit with the provider and the front office staff doesn't need to see any that financial data and I would actually are the provider doesn't need to see the financial data either our administrative safeguards it goes without saying Matt talked about cloud
and how Microsoft has a policy of how they view customer data in Azure it's kind of the same thing with health care data yeah you may have that situation where the IT staff needs to see everything not all the time there's no reason for - and they can do the same thing and health care products we need to design your admin roles don't hard-code passwords poor initialization vectors or salts we can go though I can give a talk on crypto to talk just about initialization initialization vectors and salts and the evils of hard-coding them but this is not a crypto talk and finally required credentials we changed on first use that's kind of common sense you'd be
surprised how many products don't do it and all data securely you want to protect the products assets and the customers access assets don't click data don't need this came up yesterday in one of the talks if you don't need it don't collect it you don't have to protect it it's common sense there are privacy laws that dictate what you can and can't collect and of course you have to you know every website of the planet these days has a privacy policy that basically says this is what we collect this is how we use it and this is how we get rid of it when we're done with finally logging I mentioned this already you don't want to log patient health
information or personally identifiable information without protection it means encrypted in transit and encrypted at rest and if it group it into transit not using SSL v2 or v3 or even TLS one of these days I mentioned earlier that this regulatory requirement for at least for hip and I suspect Canada has the same thing you have to be able to provide a thousand product you need to provide tamper proof audit logs so that somebody can go through and see oh doctor so-and-so saw Bob's health record on Tuesday the 23rd of February and the doctor couldn't change it or could the attacker unless obviously they got administrative control on everything during development and test use the latest development tools if you're using
digital shooting for example in your building C or C++ code you /gs canary the stack based canary for that basically has made upper overflows a thing of the past and yet I still get the computer emergency response team digests and I see buffer overflows in every weekly digest I'm like really a pro overflows are so 2007 you want to aim for clean code static analysis is a good thing it is a pain especially if you ignore it for a while and you've got 50 or 100 or 500 or 1000 warnings to go through but clean code is going to be run better it will probably have fewer bugs and it will probably have fewer reliability
issues next bullet it's pretty obvious but I'm going to beat that drum a bit anyway use the latest version of third-party components and open-source software development engineers love to plagiarize each other's work which is a fine thing open-source is a great thing dropping a piece of open source in and then forgetting about it for five years is not so you want to stay current heartbleed kind of was an eye-opener for many people because it kind of order them of the factory wow there's versions of OpenSSL in all kinds of places and they all realize they had to go catch it because of that one consumer vulnerability if you're testing a healthcare product or any product for
that matter think like an attacker the attackers don't attack features they attack vulnerabilities and features they attack systems if I'm an attacker I don't think I'm going to own that product no they think I'm going to own that database that's deployed on that data center and oh by the way oh the admin workstation over there and I'm going encrypt the mess crypt a lot great a mess
if your organization finds you don't have the right expertise bring in some outside help security testing can be expensive and iteration testers are very specialized subset of test engineers they're very good at what they do many of them um they're not cheap necessarily you get what you pay for the bad news is the defenders dilemma attackers need to find one vulnerability and you need to find all of them now whether you fix all of it or not is a different conversation and see my recording from b-sides three years ago about prioritizing bugs but if you know about the issue then you can make a decision about it you you need to be transparent set expectations for your customers clarify
what you expect them to provide from a security perspective how they can manage their networks don't just say oh their network is secure because chances are it isn't and of course you can't control for that when you're building and developing and testing and releasing your product but you can tell the customer what you think they ought to do and you can give them some best practices and then document everything hopefully in documentation it's pretty accessible and that they can drill in order to pretty quickly don't necessarily document your hard-coded passwords and develop an incident response plan especially view third-party components understand what you'll do if the next are clean hits and you have open SSL in your product or in
your service line of this is that well-informed customers for that matter well-informed product teams and companies will make better decisions the overriding goal X security strength and I've seen cases where security was decidedly not a string for certain products and they turn that around both the public perception and the reality so if you work in healthcare IT first of all consider that healthcare IT is not just providers and payers it's anybody who handles medical data if I live in Seattle if my medical did is somehow getting sent to some agency of the US government I sure as heck hope they are protecting it given the WikiLeaks article revelations from last week I'm not sure I trust them as much
but that's a separate conversation you want to leverage the privacy and regulatory landscape if you're working in healthcare ITA yes those are think boxes you have to check but because you have to check them they're also the whole organization has to help you check them let them help you make them part of the solution ransomware threat has health fairs attention I'm certain that most hospitals in the United States and Canada probably looked at what happened at various ransomware attacks and said oh and then the next question was are we next I do feel it's very important to type in health care to tie security to privacy and patients say if you can't separate the three you can tease out nuances that
are in there specific to each of those for instance I work at GE healthcare we've seen the shop the factory for where they build the big MRI machines and you see an eight or ten foot high magnet sitting there over in Canada three meter high magnets sitting there it's like okay if that falls the patient it's probably a bad thing I'm making a joke but bottom line is tie it all together my purchase if you work in an IT infrastructure throughout all your environment your network topology in threat model TSA you can certainly throw huddle-up topology preaching to the choir backup often backups are your friends if restore works have you tested restore recently you
want to have disaster recovery contingency plans in place you want to know what you'll do in a crisis before the crisis hits and again I mentioned it unannounced private practice drills again do that within reason don't do it without having somebody high up the food chain improve it understand at what point you pulled the plug because it's a drill or because you found what you find to define as a result of a trilogy we did a drill we found this in this that's great stop the drill because in the case of a real event you're not going to pull the plug you're going to go through the entire plan and execute it let's say said
Hollywood Presbyterian got hit with ransomware there Pierre our department whomever whatever sort of public relations department they had was very busy that week you don't want to spin those people up unless you need to and then if you need to you want them there um this next protecting your perimeters firewalls layered defenses should be pretty self-explanatory I needed to put it in here so you know I was thinking about it you know if you have a single level network that's probably not a good thing deploying software require vendors to be transparent and honest ask them to set your expectation set your own expectations what you know Matt mentioned the security responsibilities in the shared security responsibilities
it's the same into the software if you're deploying it in your network and then prepare for patching because ideally you won't have to do a lot of it but you want to be prepared and you want to ever require your vendors to give you timely updates want to mention patient kiosks one of my peers actually suggest that I talk about this for a minute or so kiosks are where the patient logs in is able to view their data their appointment records or medical records whatever and then they can log back out you want to encourage them to log out because of course if they don't log out somebody else can view their medical records and to that
matter if it's a browser-based thing they've logged out the cache will get cleared if the web underlying website web app is written properly they don't log out that won't happen so you need to use timeouts ah the person who suggested I talk about this also talked about shared responsibility with the patient in this case I assume the worst the patient won't logout they have some communicable disease it's really embarrassing and somebody else is going to walk up to the kiosk right away you want to think about that through as you're designing your kiosk and boy your web application your web code better or log a patient out and clear everything if you develop software in-house and I'm
sure I know that the larger hospital systems do treat it like a product yeah the people who your customers are the people paying your salary doesn't matter treat it like a product to regular releases prepare for updates monitor the software be careful to use third-party components it's the same thing follow the same kind of release timeline and planning finally train your users he'll really educate your users Hollywood trust me Tyrion was and some of the other ransomware attacks were phishing attacks that succeeded consider using fishing grills G send around a interesting-looking mail with an attachment that people open and click and then send them to an internal site that it educates them you just open
something that was not real you can take a very positive tone with that gently scold them and say this is here is here's why we care and this is what you can do look for next time I have seen this used at both my current and previous employer and I can tell you that it does work the incident the trend of people not clicking in the attachment has gone up rule-based access and usage three important Windows has group policy through policy once they learned out the kinks about 15 years ago is a fantastic thing because it gives you you can define user groups and you can tell them till those user groups what they can and can't do you
can give them privileges the whole authorization you're authorized to see this data but not that data I'm always warned people about being worried about other people asking for privileges or information they don't need so in the clinical case let's think about it if you're looking at a large Hospital why would the head of the cardiology department need to see anything having to do with podiatry and I would claim not at all it would be up to the podiatry department to share data on patients feet with the heart department and I can't imagine why except for maybe circulatory issues why they would need to share data except for more than passing interest and if all else fails turn stuff off
yeah this audience I'm preaching the choir for sure disable office macros I suspect there's some people in the office team who would just soon get rid of office macros I haven't asked any my friends who work on office but I'll assume that so in conclusion health care has a lot of challenges they're listed some of them there I strongly suggest use this as an opportunity for excellence get weighed down by the oh my god we've got everything and then buildings on fire positive attitude to it it would be be pragmatic figure out what assets are protecting take a risk-based approach be transparent and then educate and form and rinse and repeat because well edge will inform users patients customers IT
administrators hospital administrators etcetera will make better decisions and a final word one of the things about healthcare technology they really haven't thought about until I got into it is if there is something that has its unique versus other technologies and that it improves quality of life and saves lives that hadn't really occurred to me when I got to GE healthcare and people said oh by the way and I'm like oh that's cool let's see some resources Microsoft SDL oh wasps org there's the link to my b-sides talk which of course I'm not expecting any of you to scribble that down if you search for Bob truth on YouTube you'll see me it's the first head drop my link book is the book on
threat modeling but my good friend Adam Shaq who spoke at the very first b-sides Vancouver conference on threat modeling go figure um full disclosure he wrote that when he we were both at Microsoft my comment when I read it was that there were about 10 or 12 of us at Microsoft who could have written that book the right one of us did and then just to prove that I wasn't blowing smoke I did actually go out I can't say I read all the medical privacy laws but I glanced through them and said okay this is they all basically say the same thing and I'll leave the reading of those logs to the privacy attorneys because they're paid more money than I
am I think I've got time for a couple questions yes why don't you wait for the mic to show up and sorry he didn't see you or somebody else on you though there we go thank you about very interesting presentation you touched on industry standards are just wondering if there's anything happening in terms of the field of medical devices specific to medical devices industry standards um in the United States the closest thing has been the FDA guidance it's been tied up with our medical products or considered medical devices and some of them are like an x-ray machine is a medical device but you'd be surprised as some software products that do things like manipulate images are
classified as medical devices so it's really been tied at with type with that and the standard has been more on patient safety historically but the revelation a couple years ago that the FDA was actually listening to people talking about instant response and then doing something about it the back story on that is that there was a it was a year ago there was a gathering in Washington DC and it they brought in a bunch of people both from healthcare IT and and other folks from security who weren't in healthcare and had a bunch of committee meetings and so forth and that that guidance came out of that yes right in front yeah I mean like so
many industries there are issues with funding and budget issues as we all face but here you've got this growing case being made as to the value of what technology can deliver particularly in this space so I'm wondering not only do you have to deliver in an industry that previously might not have seen technology as offering value but you also have to decouple so that you can segregate and control that much more so for a privacy perspective so that in first additional cost yeah these additional peers yeah so I mean it's back to that same old story where you have to be able to convey this value to the decision-makers see this is why we need to do it this way yes so how
is that battle going against at a macro level um it is improving because the decision-makers are looking at the ransomware attacks and asking the questions um I'm sure am i I'm not aware of it in a micro level I know that um that I'm sick but I'm seeing that definitely that is that people are more open to having both the decisions that need to be made and maybe more importantly to listening to the rationale that you're presenting and you can use that the threat of ransomware on the ongoing success of your security landscape is way of saying hey we are trying to this is what we're trying to protect and this is what we think we
need to do and obviously if you can you give them choices see if the budgets this big giving a choice that's like this they're going to look at it go we don't have to budget for it they'll say well can you give me this that meets the budget now you may look at it and say well we're not going to be as protected as we would be because we we won't because we can't throw the money at it but at least you've given them those options okay so medical devices are quite often very insecure how do you think healthcare providers should try and kind of limit the risk faced by the healthcare device security and then a
little bit further how do you think responsibilities should be shared for vulnerabilities and medical devices between the vendors and the healthcare providers okay you've asked two questions I'll talk to the second one first on which we can talk about it privately but I'm not going to comment about it because of where I'm employed of in terms of the shared um the first question is I think it's really a matter of taking a hard look at the individual device and saying okay what if it isn't collecting where is it on my network what is it doing and what is it I need to do to protect that data um and again it gets back to working with the vendor
and question saying hey tell me what your product what your product what is happening to product it and how its protected it rests etc etc um I think it's got to be a cooperative conversation certainly and starting to see that more and more of the larger clinics are starting to wake up to that going gee we want to buy your next generation x-ray machine and we here's the set of things we'd like to know about as we're making a purchasing decision which is a reasonable thing there the customer they have the money to spend they should be able to say these are our requirements but I think what we're seeing is that cybersecurity is showing up on that list or
requirements more often and that hopefully that behavior will drive the vendor response which which is oh we need to do something about this or better yet we are doing something about this or even better yet we have done something about this and we're continuing to do even more to comment on your comment about making sure things are secure at first use it's often very important to make sure that they're secured before first use like the server won't even become accessible until you change the password otherwise you open up a window true that's a purpose or a point so the comment was a paraphrase server before first use don't even let it start so I'm sure this
conversation has been had a thousand times but this data is so siloed particularly in this industry and for good reasons but has there been a growing conversation around the need to standardize this data to a certain degree where it can go beyond the private institutions and be provincially from Canadian perspective or federally structured in a way that not only with every significant cost savings but there would be significant shared development in it around security etc there are movements of foot the one I'm directly aware of is fhir or fire which is an industry standard that it's more and more vendors in the software space are starting to look at as a way of using that as a format for exchanging data and
you know your education your questions I was muted thinking the US Centers for Disease Control down in Atlanta gee wouldn't be nice and I'm sure they have this now but would be nice if it was even more interoperability so the u.s. Center and the Canadian counterpart which I'm not sure where it is I'm sure there is one and the UK counterpart in the Japan Japanese counterpart and the Chinese counterpart are all sharing patient data so gee we have a worldwide flu epidemic for example we can you know medical providers can get ahead of it and the example I would give on a flu epidemic is 1918 when all the World War 1 soldiers came home and I can't
remember how many people worldwide died it was an outrageously large number and was have as large as the number of casualties in World War one as I remember first of all note I lost a great-grandmother I think in the flu epidemic so more questions well thank you all for hanging out to the bitter end and hearing me out
that is true thank you hello test tests thank you very much Bob all right we're going to do surprises now before we let you go the people that are walking we're just gonna miss out that's okay the people that are up there isn't a zani and we're going to do a bit of a trivia so if you do want to get involved in winning come on down so admittedly you're not live can we get yellow up live on one now this guy okay so we wanted to encourage or enable our sponsors to be able to collect data and help give in to their marketing team that will come back and sponsors next year the big numbers game
for them as well as they have some cool technologies that you should be learning about potentially buying so but we wanted to really respect your privacy most conferences do not do that they sell your information we don't however for us to do that we have the QR code on these badges that we're just a number I'm sure most people will figure that out that it's not your all your personal information we're not going to do that especially with most of the attendees here that are going to be on your QR codes and email you or worse while that was a great idea on paper turned out it became very complicated trying to figure out who got stand up there and so we
apologize that we can't do a raffle so we're going to do a trivia instead and our two prizes are another networks continuous and second prize is going to be a spare lock but before we do that I do want to ask that if you are thirsty after this event and are good at folding chairs we've got beer so you pick around if you'd like to pull a couple chairs in terms of beers with us afterwards all right Joe Joe Chet is our game show host for the evening for the next five minutes so take it away all right well so last night for those of you that weren't joining us at the VIP dinner we did a little bit of
hacker jeopardy at the VIP dinner and I was a little surprised at the lack of ability to do arithmetic I had 31 questions as you would on a Jeopardy board he had six categories with five answers per category and of those 30 29 were answered correctly but one of them the ports of call category which is port mathematics was answered incorrectly so I thought we'd have a little remedial arithmetic on port trivia for the prizes since some of you seemed up but you can pull your calculators out if you were here last night because apparently you couldn't get to the correct answer and we'll start off with the grant program start with the grand prize right answer with a
grand I'm ready for this we've got port mathematics here for the grand prize we have sauce - message submission protocol - 50 now no yelling out you have to really put a hand up if you have the answer if you get it talks - message submission - 50 and you can give me either the number or the name of the protocol that is the answer oh oh too hard and when he wants a grand prize oh no I'm sorry we all can we need some jeopardy music here we need all do you relate you know I was doing it too hard oh oh I still have to go to number two all right we did have a queue I'm
your parent wanted to do the math for your port map failure it's okay to be wrong we might even be kind to you this time we have 20 times FTP data plus who is everybody so tired they're just trying to make us fail but it seemed like a good idea on the cue card good 20 times FTP data plus who is cheating is allowed oh we have we have a guess 500 no no or 4:3 that is we have a winner get up here so FTP data is 20 times 20 is 400 plus who is which is 43 that's not even a deprecated protocol I didn't even know we didn't even go for Archie and Veronica here like I stayed in them
we didn't go too far off the chart
congratulations tray happy hacking alright this this one comes with clues so maybe maybe we'll have more luck with is it lockpick 3rd is going to be the lockpick starter can't target arrows from sparrows and thanks to sparrows that give us a nice deal to make sure we could equip our lockpick village and that was very kind of yes they did probably regret continuing to pick locks and want to buy tools we recommend sparrows there's your community service message uh the the price for this one HTTP -1 ah I saw that hand over there 79 but what is it a protocol oh I see people looking at their phones who has LTE Plus yeah here if you're on the
Wi-Fi you're screwed ok wait no we sponsor that oh I saw that hand gentleman there what a finger that is Kerber any friendly it's protocol get up here well he gets at least appear because you got 79 I even even have a drawing of the answer hahaha not to be rude but
congratulations Glenn double winter you guys should it be nearly as tired as we are we had to write these alright it's over alright so I wanted to make a big thing so board members get up here leave them thank you so again this morning we I did mention these are the board members users are the core organizers of b-sides but by no means is this the limit of who does in help speeds I'd Vancouver be real so first photo op this team is living off of no sleep we were struggling to make those trivia questions will tell you that much we know computers so yes you know be size is a labor of love it is awesome
and thank you very much for being a part of our community and supporting us and making us who we are but like I said we are just five of many many people so let's bring Jacob here George George is not here he had to go for medical appointment but since he was wearing that high as it is killed that's still burnt in most of our product if we were to open up the back door we might still see him alright so Jay King is a community member that has helped us with more than one thing he actually did Rav in 2015 he's also been the man for track 2 and actually more importantly he was
the architect and whip cracker for building designing building these badges and for all the ones yeah yeah so I almost talked to my batch microphone Jake what is in the badges so again Jake did designed these he found the manufacturing in China we learned the ins and outs and pains of dealing with manufacturing in China and we also did a lot of hand manufacture anything that lit up on these badges is actually hand done by Jake myself a slew of volunteers that are hopefully still out in the audience so again give a big thanks to Jake for making these back and again George who could be here with the architect for all our ad so some very
high-tech solutions here duct tape together a little bit with a little cable dangling everyone every every once a while but yeah we couldn't do this without our community and our volunteers and it just you know it's very humbling to have these people help us make this event as professional as it can be on a shoestring a shoestring that has cuts in his own breaking budget so let's have one last round of applause make it feel good wake up thank you and I would do a mic drop is not my microphone so have a great day are you [Applause]





