Rod Soto - Civilianization of War: Paramilitarization of Cyberspace
Show transcript [en]
this whole new thing about um this Market about selling exploits so uh good afternoon my name is Ron Zoro and I am with um I am part of the board of hacker space Co hack Miami I worked at the um Security emergency response team at uh now aami Technologies used to work for proxic uh we were acquired by aami technology not too long ago and I worked there as a senior security researcher what you're about to see is uh kind of a compilations of things that I seen uh in the field and while performing my work uh obviously have obus skated a lot and I won't get into details but the bottom line is um during
my tenure and uh as a security professional I have um researched a lot of uh what you would call what what would be uh the implications of active defense or cyber weapons of cyber War uh not too long ago people will laugh at Cyber War people would say that there were no such things as cyber weapons uh people say that active defense was ridiculous um that there was no need to respond or or pretty much saying that that an active or a prehemptive of um attitud was uh reposters uh I was actually uh an advocate of of appr prented uh approach but uh like the President says my view has Evol uh after doing some research I have
found that it's not that easy uh and there are some serious implications uh when you are in the front lines and if you are an infos professional and you're a civilian you are in the front lines and now we're about to talk about that so uh my talk is about the Civil civilianization of War and the paramit param militarization of cyber space and what the implications are for the infos professionals I also came up with a proposal for collaboration we're going to talk about that at the end uh but I'm going to present you with some uh facts and then of course you you have your own opinion if you know me or you had seen me before on defcom uh I
participated in defom St talks last year and the year before and the panels were about cyber weapons and second amendment and infoset research at that point we really have an aggressive posture of what to do how to respond in the case of an incident but again like I said before my my view has evolved and I'm going to show you why it's not that easy it's complicated and uh we are starting in at limbo right now so let's start first of all let's define War as the classic concept right an act of violence intended to compel our opponent to fulfill our will let's close with and that's the classic definition of word the classic definition of War
also isolates where it's a civilian person and a military person a person that's not in the Arm Forces or police law enforcement is civilian military is obviously the Arm
Forces so what has happened we live in a country that is militarily speaking it's the is the is the power Supremo and I didn't create that term that's David Kil kin if you know who David kilin is he's the master of the counter Insurgency um manuals and he was one of the advisers of uh Petrus in Iraq so basically America is the power Supremo there is no other country in the world militarily speaking that can face us or or or be one to one through us this was seen a long time ago and actually uh it has modified the way the conflicts and some of the uh events in the world have unfold so again I did not create the the
the whole power Supremo thing and uh uh don't get too excited we're going to revisit it at the end um who basically usually thinks that the bla the concept of unrestricted warfare that's uh 19 around 1999 I suggest everybody to read this paper these are two colonal from the pla that came up with this idea of uh uh pretty much everything goes and and that everything goes they focus on the Cyber aspect of warfare uh we also have a decline of Interstate Wars the reason is simple they can't match us militarily they really can't so what you see is a um uh a number of regional conflicts a number of Insurgency a number of uh
confrontation what you call non-combatants which at times they're called terrorists all right so we we have a bunch of regional conflicts we have a bunch of uh situations where even though States May oppose us they will not face us one to one simply because they can right so that's where the concept of the pla unrestricted Warfare comes from they pretty much said we will never be able to catch up with this guy we we we are 10 20 years away in technology well we might as well use techniques and take advantage of for example the Cyber domain to hurt dis guys or defeat them in battle so uh we have other CS that approach that I don't know if you if you
guys have read Thomas feet where he talks about Leviathan and sis admin and here's where comes the uh involvement of civilians in the uh the Theater award this comes because of the adoption of Information Technology the adoption information technology in military has brought a lot of civilians into it as we can see there is a there's a growing um U direction as of now of like I said a decline in Interstate Wars and there's also um a growing role of civilians in um things that might be related to a Theater award and we'll see that in a minute okay so uh as I was saying before uh this is actually a quote from uh colel lean and I'm sorry I can't
pronounce that uh from VI Warfare in 1999 this is a Doctrine from the pla that says you know that pretty much they will take advantage of any domain um including cyber to uh exercise either mitigations or uh exert power on an opponent that they see they cannot match on a strict uh formal um conflict so so with that in mind as they as our opposing Powers see that violence and War can can be appli to the internet technological violence obviously involves the internet so you will use the internet as a mean to get advantage of over adversary countries you you will uh steal intellectual property you will exper trate data Espionage you will take uh um IAL
Services you will deny the great destroy the ability on adversary to provide essential Services via aggressive digital attacks we'll see that in a minute and you will insert Power by amplifying the effects of hostile actions uh by you can either uh black marrow or store or you can also infect millions of host with malw or spy word and I will talk about that at the end as well so consider this um the security and effective operation of the US critical infrastructure including energy Banking and finance Transportation communication and defense industrial base rely on cyber space industrial control systems and information technology that may be vulnerable to disruption of exploitation cyber threat to the US National Security go well beyond
military targets and affects all aspects of society and this is an absolute truth we we're about to see the 16 um items that the department of Home Homeland Security considers critical infrastructure uh so effectively National Security is redefined by cyber space so here it is so as you can see this is what the Department of Homeland Security considers critical infrastructure all of you working at one point or another so you have the chemical sector you have communications you have dce you have emergency services financial it transportation services commercial facilities defense industrial base energy food and agriculture nuclear um water wasted water now do you see anything related to dood there are there people from dood at your
cover no right do you think you will get attacked by an opposing power okay well there you go you're on the front lines and that's the point of this talk yeah go
ahead yeah I believe they are on uh yes yeah so this is this is yeah I took this from actually from the HS um so this is if you are any way related to this sectors you are in the front lines right this is whole critical infrastructure so here's a quote that they actually used uh the uh um unrestricted worker every citizen is a soldier and uh um they seem to have a better grasp on how to on how to approach cyber when is when it comes to approaching attacking us they don't look at it um as a way of uh how can I say this they they don't think it's unfair to hug us they don't think it's um unlawful to
get Advantage uh through uh either exper trading large numbers of intellectual property or stealing our Creations or hacking our industrial base and They're copying their stuff and then beating us in the market right besides this like for example give you an example so some of the things that the Chinese are doing is they basically go to countries they find out what the bid is the bid is financed by the government and it's financed in a way that we will never be able to match their price and that's so they are gaining Advantage by getting all these deals mostly on critical infrastructure and that's happening right now okay besides that we also have the param militarization of cyers space
we have there's an increase of proliferation of hackers for hire activist and what I will call digital insurgents some of these digital insurgents um may look like they're activist but they are not activists and I'm asking you when you if you're a person that looks at uh open source intelligence I want you to look with detail of certain things that happen to certain countries and certain uh actors that will pretend they belong to activism they will tell you they're Anonymous they will tell you they are from whatever they are not they are there are uh there are a number a growing groups that are uh effectively attacking other other countries including us uh and there is a
there's a t a trend mostly in uh um North Africa and you will be hearing a lot about these groups in the future but basically what we are about to see is the transferring of what you will call gorillas in the late 60s or 80s into cyberspace this already happening in some other places it may not have gone public yet but it will at one point so um a little bit of what I use to understand this is I base my um I based my research in the Cyber threat taxonomy you have the uh deer one and deer 2 which is exploits that are preexisting and known to vulnerabilities this is like going to exploit DV right
you go to exploit DV there's a there's an app there is an exploit and basically you execute it if you know and most likely you get a shell or the exploit will go successfully then you have the deer3 or deer4 which is people maybe like some of you that are pent testers that are vulnerability assessment people who you know will p a little bit more than just the public known vulnerability and then you tend to find stuff and then finally you have the deer SPID 7 which is creates vulnerability that using full spectrum and usually this is what we call the the zero days the aps these are people that goes beyond or what is public and what
is uh or already know and what this is happening um and I'll go back to it in a minute uh I wanted to give some examples to some of the Cyber War examples of uh of of conflict in cyers space so you have stonia you have stocket you have shamun and then you have isoko problem bro uh isoko problem bro has to do with the financial institutions in the United States uh this is a campaign that almost extended for 2 years and that invol financial institutions in the United States and it was actually focused on a a country in the Middle East um there are also numerous incidents that I would not name but had to do with the vertical
I can tell you one thing this stuff is public there's many things in other vertical and sectors that are is not public yet where they have already tried to apply the same um the same logic the same uh procedure to affect us as well other vertical such as uh Communications such as uh power and many of us I would probably say that any of those critical infrastructure sectors have been proved and evaluated for the possible Vector of attack against us by opposing Powers so um this is the definition of an existential Cyber attack so let's go back for a minute you have 16 sectors you have a dependency on cyers space and then we have the concept right along
with what the actors can do in the taxonomy uh of threats and then we come with this definition an existential Cyber attack this is actually I took this from the Department of of of Defense science board report and basically what it says is that uh an existential cyber attack is Defiance an attack that is capable of causing sufficient wides scale damage for the government potentially to lose control the country including loss of damage to significant portions of military and critical infrastructure which we talk about power generation Communications Fuel and transportation emergency service Financial Services Etc so obviously our government is aware that this can happen and it has shown you not only has showing you the categories of
actors of what they do but also the sectors that can be targeted so basically this conflict brings infos civilians to the front lines the current state of affairs has no Frameworks that guy is infoset professional basically the closest that you have is CFA AA which is the Computer Fraud app which BAS basically they can get you in jail for anything okay you write a python script that download PDFs you go to jail I went to a conference in San Francisco where a bondet was taken down in public this happened on my view and the company that did it awesome for them actually I thought that was great that they actually took down that bondet but
again in hack Miami we've been told by the Feds that if we hack live we will be prosecuted and where does that come from from the CFA right so the the actual the current state of affairs the current the status quo on the law that we have Computer Fraud and crime is is inadequate for this because it puts infos seex uh civilian Professionals in a very uncomfortable place where you can be prosecuted it almost sounds like it goes to if they like you or not right you go and scan the entire internet but your name is so and so they won't do anything but if you're John do you might be prosecuted I don't know if
you guys are understanding this because this has happen right there are examples quite examples of this so then we have two things that are very important the title 10 of the United States code which is DoD military operations you have Army Navy Air Force and then you have the title 50 on the United States code which is the intelligence connection you have NSA Dia CIA which are sort of Civilian agencies and they are the civilian networks fall under DHS now this is what happened for most of us here we fall under the red if you are a corporation or a residential you're on your own there is nothing that says you can respond you can block or what what is
the procedure what should you do if there is an incident that you need to act upon right so basically if for any reason we had to respond if for any reason we were attacked with a certain Vector like a B net or adids attack the key drugs have actually to be executed by military personal you cannot respond it's unlawful and I'm going to get even deeper into this all right remember I used to tell you that that W for responding right so so in this context the war is no longer just military business and that's what I'm trying to to say here you know this is something that we all talk a little bit at the end but basically we can't ignore
this it's a reality if you work in any of this 16 sectors you are in the front lines there's nothing you can do you either face it or you don't do with it and it's part of a bigger thing that eventually affect us all there are no rules of engagement there are no clear channels of communications no clear procedures or disclosures of such incidents reaction is and prosecution is based on value so usually if you if you ever I don't know if you ever if you have relationships with the with or talk with the federal agencies mostly they will tell you hey how much are the damages cuz if not we can't prosecute but my question is what
if the mare is part of a bigger campaign that is coming that is about to come or that is happening already so because there are no numbers you can't prosecute it you can't look at it that is very dangerous not only that's dangerous it's leaving you exposed not only as a corporation but as a citizen so because we don't have a framework to act we are Expos we're in limbo cuz it's not like you can go and take the uh the bond it's not like you can go and researching they will tell you uhuh you can do that we will prosecute you if you do that so then we go what we call this the
fog of war the fog of War which is is is is a is a term that is I'm trying to to make an analogy of what's going on and uh we can read it it's a term that seeks to capture the uncertainty regarding one's own capability adversary capability and adversary intent doing an engagement operation or campaign that's basically what we are into we don't know what to do we don't know who to call the damages are based on on um Financial value so if there is no real Financial value they won't prosecute they won't escalate but what if that is just a piece of the puzzle right and I'm talking about commercial sectors I'm talking about the
DHS 16 sectors I just told you not we're not even talking about homes your grandma with Windows X me right so that's something that you got to consider and then um something that I want to talk about is that uh you see there there's countries like the um UK that they have this por filters uh we talk about the porn filter in the end and what what that means for us as Americans uh also part of this F of War uh and it's also part of the infoset community there is this at times perception that the government is looking the other way so you got all these companies that they go public and say oh yeah I got a Ser day for Word and
Excel and they're worth between $2 to $500,000 and you know based on the current low that we have depending on how that those Expos I use they are prosecutable so there are no clear limits or how we using things either we are responding either we're going to do certain things or either we don't but based on what we have right now really there's nothing else to do by uh own opinion is based on the CFA if I respond if I scan like for example in in China and map is considered a hostile act so I can be prosecuted for that so basically I am not protected as a civilian so I am forced to either call
the authorities or do nothing because basically with the current framework that we have you can't do anything all right so this a good question you have a bunch of vendors this vendors sell Z day exploit some of these vendors are known for doing um government work so are this vendors kvr or black water do that what's happening is sort of what what's happening with this where we had this civilian contractors where they do uh certain work that the government would not do but then they have plausible deniability so our infoset contractors the equivalent of a black water or the [Music] KBR and in case you wonder cuz I don't know all of you but you probably wonder
are you a mercenary right cuz basically if you are doing operations that include aggressive include offensive uh breaking penetrating you might be consider a mercenary why because you're not part of the military and you're not part of law enforcement you see where I'm going with this okay so in case you wonder here here are the six factors that will classify you as a mercenary you have a special recruitment you have a direct participation in hostilities desire for private gain as a PIV primary motivation neither a National Party of the conflict not a resident of the territory controlled by a body not a member of the other forces or Body In conflict and not sent by another state or
official Duty as a member of his La en forces so for example I took this from the talent manual the talent manual was produced by NATO and they did this because basically they concluded that international law is applicable to cyers space and I commend them for doing that because is a it's a it's a it's an it's a positive step to we're studying uh either Rules of Engagement or a framework that will permit how to act in case of conflict so in this case for example you have a company located in state a that is engaged by state B to conduct CED operation on its behalf and it's our conflict with the state C so
one as the six criteria are fully met is employees who conduct the cber operations are mercenaries and does unprivileged belligerant and unprivileged belligerent is a combatant an unlawful combatant that is usually a term to define terrorists you can be protected by Geneva Convention because you're not a military and you're not a civilian and this can happen if you decide to go bunkers and start attacking once you see an attack on your network so that's a huge huge huge risk and liability and uh this is actually real this is happening right now because there are no Frameworks that will allow civilians to collaborate either with LA enforcements or military and have the right protections so basically
[Music] um a person that qualifies as mercenary does not enjoy coma status so responding again our infoset companies equivalent of Defense contractors the answer is no right there is no legal framework that support s collaboration one of the things expressly prohibited to contractors like I said we talk about infosite companies developing zero days or doing operations prohibited Contra functions include actions that directly result in disrupted or destructed combat capabilities including offensive cyber operation electronic attack missile defense and air defense I took that from the law of armed conflict even though contractors are entitled to self-defense but that's not self-defense is oh yeah we s this we're going to we're going to respond it's not that
easy right so some of the things that also contribute to this um fog war or confusion is when I call The Curious Case of going from classify to classify and I'm sure this has happened to some people here basically you're your work and you find something and and you happen to be uh worried about it you happen to report it and then it went from a simple incident to a classified incident all right this happens basically because hold on this happens basically because there is no collaboration for law enforcement they don't tell you where they're looking at and I will I will talk about this in a minute they want the whole bu but they don't want to let you know what
they're doing so uh this is actually I talked to several colleagues and this has happen The Curious Case of classify to classify how is it that you're doing your normal work and then your report ends up in theend why because there's something that they have realized is bigger it's part of a bigger piece of events but again if you don't know what you're doing if you don't have clear procedures or um guides how would you know right and if everything is based on dollar value you may have found a piece of malare but there is no loss there is no it's usually around $5 to $10,000 so nobody will report it plus there are obviously some uh reporting or
disclosing incident is kind of commerson and some companies in in the uh commercial industry um they simply don't want to disclos it because it's embarrassing among other things so uh there's a lack of communication between national security agencies and infosite professionals so we're not putting the dots together the line between civilians and Military is blurred in some cases the biggest civilian responsibility in protecting critical essential infrastructure services so let's say things the get to that point you think that if they bring a a a homeboy with with guys in in in uniform and they said sit there go ahead and defend us you think that's going to work no all right who knows your network better than you
who knows your assistance better than you maybe instead of separating instead of isolating maybe we can collaborate and make it more effective all right let me um
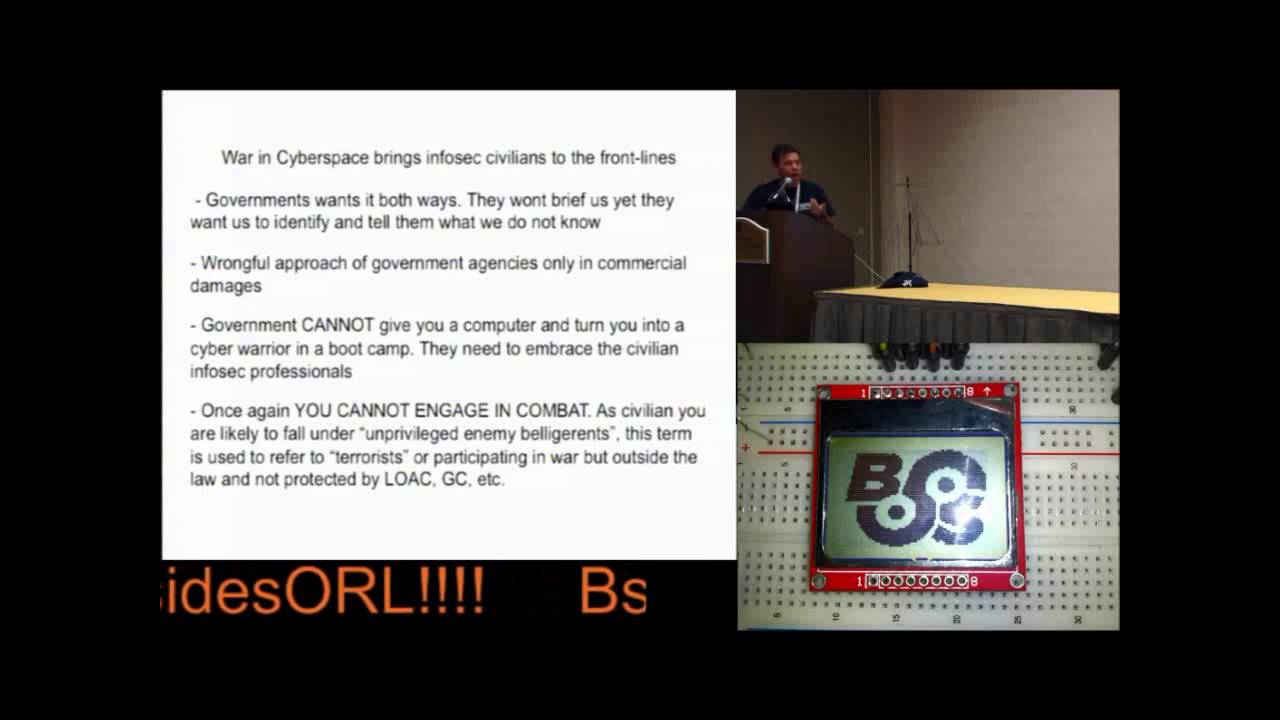
and like I was saying the government wants it both way they both they want brief us yet they want us to identify and tell them what we don't know the wrong it's a wrongful approach with government agencies Focus only in commercial damages the government cannot give you a computer and turn you into a cyber warrior in a bull Camp it's not that easy I know they try it's not going to happen they need to embrace the embrace the civilian infoset professionals and again as a civilian infoset professional you cannot engage in comat as a civilian you are likely to fall on their own privileged enemy biger and this term is used to refer to terrorist or participating in work but
outside the law and not protected by either Geneva Convention or law of our com so you're basically unlawful you can go to want gu but uh it's obviously not not a right place to be so let's talk about this the PO of Bremo as we explained it at first is now being tested so you see there are a series of incidents and there are reports that indicate that by 2015 at least one of the major Powers will be able to either rival or defeat us regionally all right that's a report that's out there and I guess based on the latest board there is some of it you might at this point have an idea where
things are going but that is something that was actually analyzed already but by around 2015 a major regional power will be able to match or defeat the United States of America regionally speaking um and this will translate into the cyber space right so that's why I put this you know that we had all this history of exfiltration of intellectual property we have all this history of we have these Chinese Fighters that look um quite similar to ours including the Russian one so those those are just examples of what may happen and then we have all this instance where our civilian infrastructure is being proved uh by this opposing Powers so basically I give you a little
hints of what happened on 2013 on 2013 we had near critical levels of of downtime of us financial institutions almost around 10249 hours of downtime yeah this stuff has really not gone public you can find it if you Google it but this is how B again uh obviously there's widespread IP theft that's intellectual property uh there's BR footprinting our essential National infrastructure uh like I was saying Regional power was able to reach military level enough to defy the us around 2015 and this this will reflect Insider space opposing Powers seem to have a clearer strategy a framework for military civilian collaboration they also seem to have a good grasp of using cyber to counter military might in
Balance there are no cyber treaties the Geneva Convention do not apply to cyber war and even if forc it would not it will be nominally so right now that we if you read certain others like Rachel Clark Rachel Clark for example wants to have a cyber treaty where we say oh yeah we we we're going to limit the realm of cyber conflict to this uh limits uh there's no such thing as that uh it will never happen and if it happen is nominal because our opposing Powers know that we depend highly on the technology so that would be stupid for them to sign to sign a treaty like that that's not going to happen uh so maybe we could bring peace
right you maybe we can have peace on the internet and then the an example what happens when you sign a treaty and you are misled by thinking that by signing treaties there will be peace there is no such thing as peace they know and they're very well aware of capabilities and what they can do to us they are already getting louder and more aggressive and this will happen even more so um what to do as an infos professional well obviously don't panic become aware of your responsibilities and implications in your organization not only locally but nationally and internationally persist and persist in secure the awareness training at your organizations family and communities government must Embrace
infoset civilian Community nurtur it and protected not prosecuted our Warriors are the hacker spaces Prosecuting somebody that wrote a script in Pearl or Biden is stupid thank you stupid we are the ones who going to help we are the ones they need they can't give you like I said before you can't give somebody an AR15 or something equivalent the computer and said okay now you are a cyber Warrior there you go you got a boot camp that's not going to happen they're going to they're going to have to rely on us but in order to rely on us there has to be a relationship where where there is mutual collaboration and there are protections for
civilians only through communication collaboration and cooperation will be able to avoid this Doge not put together government will must cloudify the Cyber domain chain of commands and Rules of Engagement I will get into more detail in a little bit and please do not be a naal chamber um being a vigilante is not good only organized Community efforts will bring the attention of related government branches participate in the community and help military government understand cyber domain it might be prudent and this is an idea that I suggest to reopen something like the office of Civilian defense which was closed in 1945 obviously it doesn't have to be the same organism but it has it can be something
that is related to cyber where there is a a collaboration between civilians law enforc law enforcement and Military and I'm going to show it in a minute here so as you can see there we got a gradient right we got a gradient where we we will all get together government law enforcement infotex cilian appr and Military obviously there are areas where we match we got to be able to find a point where we can collaborate and get away from all this limbo confusing situation so with that in mind here are some of the points that the framework that that I'm proposing first you got to get disclosure procedures Rules of Engagement all right if you are attacked by this this and
this this is how you respond all right communication means how are we going to communicate with either law enforcement or the military cross training with military and law enforcement we can help them we can tell them a lot of what we know um we are the main driver of research incidents must not be approached from the monetary perspective and that's what I was saying we we got to away from that $5,000 $110,000 you know if if there is no value of it then we won't prosecute it or we won't investigate it infox bility professionals must be trained in low bar conflict in Geneva conventions if we're going to engage we need to be aware what
is it that we're facing what are our limits and what is it that protect us chain of command when dealing with National Security incidents what who to call what to do and were to receive approval or denial or whatever actions we're going to do and obviously you had to have what is called in military escalation control and matching procedures this does not exist right now basically if you get attack so people will go back and hack back and delete the content or destroy whatever machine they're attack fromont um usually there are procedures where you know you you escalate appropriately and this needs to be established for the Cyber domain and um for civilians because it's us who's seeing all this
it's not them um and obviously you have to have legal protections for infos seex civilians that are engaged and you had to like I said before you had to create an organization that oversees this framework with that in mind do you have any questions
what's your what's your view on infr guard oh that's a that's a good question I'm I am a member of infrar uh I think infrar has some good things but um it ended up being simply uh open source intelligence like it was it was really not uh a true collaboration platform where you will find things that you can read in the newspaper uh there needs to be a closer relationship and probably uh part of that closer relationship will um will probably up the level of betting so they can probably rely or give you uh uh certain things that they can right now because of limitations on disclosure and uh clearance so that's also part of this so you have to
establish points of communication there are some right now there's there's things like up thrust uh maybe some people here are members of where they tend to share collaboration they tend to collaborate pretty good and a lot of info actually gets uh uh distributed pretty quick it's actually pretty uh pretty good you have you get a lot of actionable items but it would be great if that um which is civilian uh impos had also some collaboration from law enforcement and Military and I want to try to propose here is to to um dissolve those silos that we have in between because I think we're missing we're missing the dots and uh we are being reactive more than proactive and if you
actually you go back to my life when you had the 16 sectors there's no military there how would they know one of the other things in in uh I talk about the PO filter one of the things that uh I found curious when I was reading um rear clar's book is that he says that unfortunately to protect the internet you're going to have to lose Liberty and losing Liberties meaning means putting DPI technology at the main points of AIS aka the porn filter that's what the porn filter is it's deep packet inspection where they're going to tell you oh we're seeing Seuss here we got to block you oh you got to install the antivirus does that sound similar as we
got to t you because you may have a bom you see where I'm going with this if we do not if we're not proactive if we if we're not able to approach either law enforcement or military this is going to come there's going to be an event that is so bad that we're going to get something the equivalent of DSA on the internet and that will kill it as soon as you put DPI on the main uh points of access of the internet you kill the internet there's no privacy anymore they will be seeing everything you understand what I going with this okay so in the Cas of infragard it is definitely a positive step but we got to go further than that
and we got to eliminate the whole either $5,000 to we prosecute or we don't care that's my uh that's actually my opinion about it yes sir I find it curious that you use the word is there you know there will be no more privacy I've got to be honest with someone who works in the field and I've seen some of your work why would you expect any privacy for the past at least 10 years is this in reference to the disclosures about the NSA no no no just in your comment about privacy and the expectation in the future of privacy well I would think at least 10 years ago I lost my privacy when I started using
the internet well that's actually I I you got a point uh but the fact that it seems inevitable that privacy would die does not mean that I cannot hope for it right even though what I'm saying is emotional not rational uh there's still some some things that you can do to protect your privacy and I am an advocate of privacy I I understand that the Privacy is the Last Frontier of the individual you are your privacy that's you that's your stuff so there are certain things where I can understand uh that things need to be either disclosed or reveal but part of the success and the the Liberty AR Power of the internet is the ability of people being
themselves and to be the yourself you have to have some sort of privacy so once you put this DPI technology or porn filters it's not porn filter they just trying to watch what's going on I mean if any of you ever seen net witness or whatever that's basically what they're going to do they're going to put it they're going to watch it oh yes sir just but that that technology being by policy so you're putting that you put that DPI technology responsive policy makers calling for that and also had some questions about like when see civilians on the front line at what point are you able to respond being that if the government says okay now that
cyber is domain Warfare and you're being attacked the Second Amendment right is to use a weapon in response at what point if there's a threat you consider an acceptable level of force excised against you to respond that's an amazing question and I can answer it uh two years ago I did a presentation about Second Amendment uh Castle Law at defco right it was very controversial uh some people think we were crazy uh you know I'm from Florida so we don't have that problem about having guns I remember someone from the UK said you guys are crazy we don't have we just still have guns in uh in the UK so that takes the problem away right
obviously that for us is unconceivable right but if you look at the possible implications who are you hacking back who are you hacking back and what happens if you hack back and you provoke an international incident you understand what I'm going with this I'm not saying that that's going to happen usually then we use either proxies or then we use rbn or or uh a bulletproof or whatever they would try to offis skate but what happens when you respond and if there is no escalation control and you go hack that hospital or a bank and people lose money or people die you see you see where we're going with this there has to be procedures that tells you what to do in
that case and right now we have anything you have to call them and then is I guess it's their criteria if they go for it or not and usually for what I seen they tell you are they losses Val losses is this over $5,000 no okay we won't prosecute but you don't know that there are other things such as the executive order not one ago the president got to shut down the internet that isn't in my opinion the way I see that isn't the case let's say uh we have a botnet that infects uh Windows machines there are millions of them we cannot attribute who the attacker is because the attack comes from inside the country the the Pres
then can go ahead and shut down the internet you follow what I'm saying now if you are in your home if you are in in your uh organization and you are able to see signs that this may happen why not bring it up and talk to them and see hey we're seeing this are you aware of this is there anything that we can do about it so that's precisely the point of my talk so yeah that's that that that would my answer my answer is yeah yes see you do have the right to do it but the repercussions and the liability you will fall into it's not too great to try it it's probably easier to just block it
or Let It Go any other
questions all right well then I'll thank you very much [Applause]





