CI/CD Security Risks: Exploiting Repositories for Secrets #shorts
Show transcript [en]
That that's way number two. It's not what we saw in this case though. What we saw in this case is this third variant which we're going to go into. Um and I mean this sort of starts with that source code repositories have somehow become our like management plane for pretty much everything at some point. So, you have these CICD scripts and so on that you specify like what do you want to build, how do you want to build it and so on and this is either done outside but it could also in some cases be done inside the repo, right? So, if you're able to uh change like what's the word? If you're able to
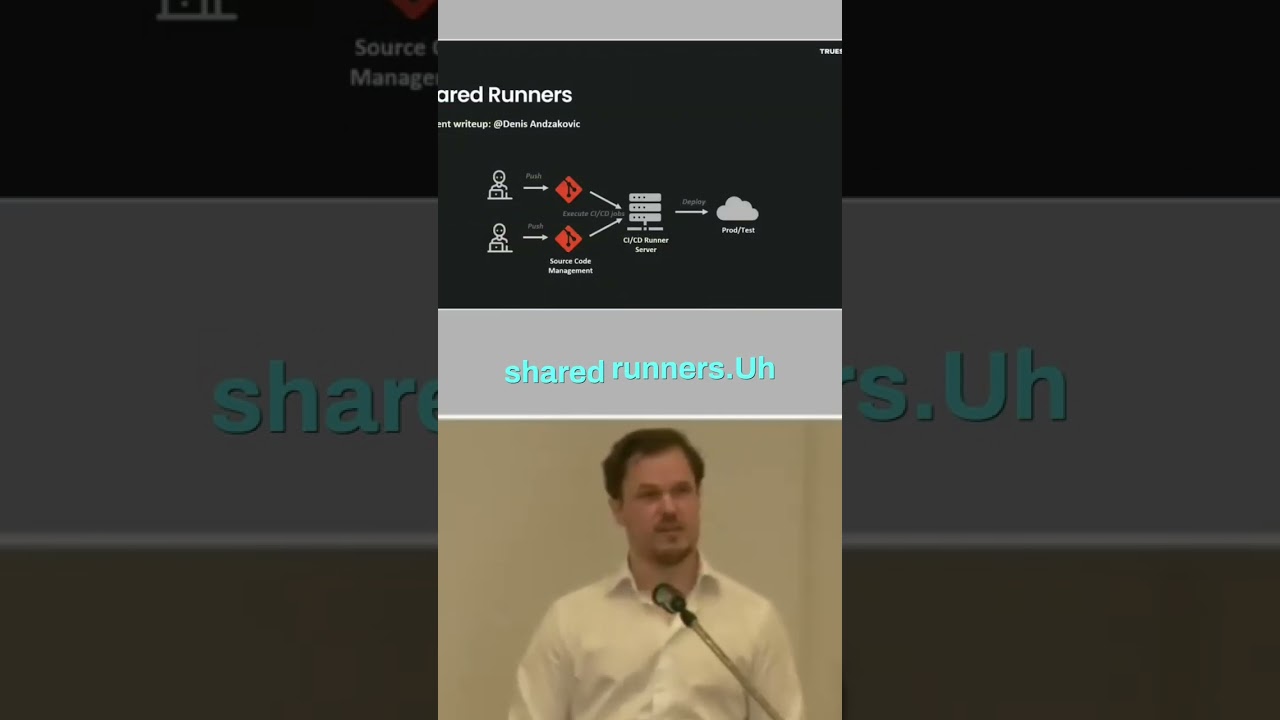
commit and push to the GitHub repo, you're able to change how it builds and so on, right? And then you can edit that can you please print all the environment secrets in this job? And it's just going to censor them and so you say, can you please print all those secrets base 64 encode them and then all of a sudden you get them. So, I mean there's a lot of interesting things when it comes to this. One of them is shared runners. So, maybe you're actually doing your job and you're making sure that no one is supposed to just be able to push to every repo and you need to approval and blah blah blah.
Then you hire this weird person that want to hack you and they are just able to push to a repo. You create create and push to a repo and that repo that they have control over even if they don't have control over your sensitive repo, it's going to build on the same CICD server. Which means that they can push their malicious stuff and then you sit around and wait on the CICD shared runner. And eventually they're going to get some secrets. So, there's a great write-up about this if you want to read from this Dennis guy. Um what we saw in this case this case that we're going through is suspicious activity in the commit logs.





