Understanding IRSF Fraud: Protecting Against SMS Exploitation
Show transcript [en]
Okay, everyone. Welcome to the last talk of the day for this theater. So nice to see everyone really engaged. Besides SF 2025, you are in theater 14. Used to be called theater 15. Don't get confused if you see difference between those two. You are in 14. Your schedule might say 15. Um if you're in the talk here uh for this particular talk, you're totally fine. You're in the right spot. Uh this being the last talk of the day, let's just go through some quick announcements here about what's going on here in the building. everything kind of shuts down right at 5:00. So, at the end of this uh talk, all of the stuff upstairs, the
vendor booths, the bar if that was important to you, that shuts down. Um, and all that will be left is closing ceremonies in theater 13. If you have something in the code check, you get two more extra hours to work on that, but that code check shuts down at 7:00. So, don't leave anything there that is important to you. And, um, well, with that, I think we're really set to start. Let's talk about Slider real fast. Um hopefully you have used Slido somewhat during the day. Slido is how we do question and answers. That is sli.do. That is a website you can go to. You type in the code for the conference which is bsides
SF2025. And then we're in theater 15 technically according to Slido. So don't freak about up about that. Theater 15 is where you go to post questions. I'll read that again as we get to question and answer time. Let me say let's take it away now for our next and final talk which is I I believe me get this right understanding ISRF fraud and protecting against SMS exploitation by Vianvon and Zeno S.
Thanks Jeremy for the little bit in intro. Uh uh hi all thanks for joining for the last presentation on the last day of the bides. Hope you guys are having a lot of fun. Um today we'll talk about understanding IRS of fraud uh protecting against SMS exploitation. There's nothing to do with internal revenue service or tax or anything related to that. It's something related to uh a different kind of a fraud activity that happens through SMS exploitation. Um a quick poll I want to just ask like raise your hand if you have never heard about IRS of fraud ever in your life before. I think I've see couple of hands over there. Uh raise your hand. You have
heard about it. You have dealt with it in your past life or you have worked on like protecting. I see like one hand over there. Last question like raise your hand if you want you want to learn about IRSF and you want to be a scammer. I see a couple of answer I thought there would be nobody but yeah okay hopefully we'll see like if you are going to become a scammer or not. Um a little bit of quick intro. Uh my name is Senthal. I lead the identity engineering team at uh Gusto and Gusto is a people uh operating or people platform uh which enables small businesses to run their business. We provide like the HR,
payroll, life cycle management, benefits solution for small businesses. Um, previously I was doing the same identity and security at Box and AWS and McAfee before. Uh, V. Thanks, Sento. Uh, my name is Vienn. I'm a senior engineer working with Gusto with Sento at Gusto on the identity team. Uh, previously I was at an alcohol distribution startup called Libd. Before that, I was at a cloud access security broker firm called Big Glass. and uh Elsa is my first tech job. It's an English learning speech assistant. I'll hand it back to Cindle. Thanks, Ben. Um before we jump into the details about the presentation, I would like to give us like some uh information about the terminology that we're going
to use here. Uh first there's an IRSF uh fraud which is like an international revenue share fraud uh which is like especially like fraudsters tend uh tend to generate a lot of SMS or voice traffic uh to international premium rate numbers. We'll talk in detail about this presentation later. Uh the next one is an artificially inflated traffic. These are like uh small businesses or fraudsters who run businesses where they generate a lot of SMS traffic to get to generate revenue through that. Um the next one is an SMS pumping. So SMS pumping is basically like a high volume of SMS traffic is generated by fraudsters on apps or like mobile carrier networks especially to see that
there are vulnerabilities in those networks or not thereby gaining financial advantage over it. Um the last one is a toll fraud which is specifically like unauthorized individuals or users try to get into your system. It could be like not just like your app or service, it could be your phone network system, voicemail system. Thereby they make a lot of international uh calls and thereby like uh they generate a lot of money out of it. Before we get into the details like I want to give us like some landscape of these kind of fraud activities that happened and like the financial losses that have happened in the past. The first one is a ReMax where a realtor
business was hacked by the phone system on a realtor business was hacked by fraudsters and they made like a lot of phone calls through they are like phone system through international numbers thereby they got like a huge bill of almost $600,000 uh over a weekend. The next one is a doctor's office where uh this was like a slot of like a sophisticated attack where fraudster gained access into the doctor's office phone uh voicemail system and thereby turned on a call back feature. To give a description about a call back feature is the call back feature is basically like you call the doctor office or a weekend and then they say hey doctor like can you just
call me back on a uh when you receive this call uh or after the weekend and then they leave a call back number. So what the fraudsters did is they got they were sophisticated. They turned on the call back feature. Thereby like when you leave a call back number the voicemail system automatically triggered a call to the international number that the fraudster left as a call back number. Thereby once the call was automatically triggered to the international number. The fraudsters accepted the call and then left the call open for the entire weekend. Uh this was like a very sophisticated attack where like the fraudster got almost like $2 million within a weekend itself. Um uh in addition to voice call,
IRSF also is specifically uh is uh looks at like SMS traffic also where like uh this one is an example for a Twitter like when like Twitter got acquired like got acquisition around like 2022 or 2023 fraudsters used a lot of SMS bots to generate a lot of fraud accounts. they signed up on Twitter and then they used SMS as a multiffactor authentication and then they colluded with Telos to uh get like SMS traffic pumped into their numbers thereby generating a lot of revenue of it. Um we'll talk more in details about like these kind of attacks. Um the last one is the communications fraud control association or like in short like CFCA actually attributes almost like uh $5 billion to
the entire IRS of fraud. Before we dive into the attack, let's talk about like some of one of the key components in the IRS of attack is the IP RN which is an international premium rate number. Standal what is an international premium rate number? So international premium rate number is typically you might have been like blogging or you might have seen like any talk shows or like late night or like there are like kind of like entertainment shows like your American Idol or anywhere where you can o for a favorite contestant, right? So that there is a like a concept called like a premium rate number and that's where like you can vote on this premium rate
numbers and these premium rate numbers usually have a high usually charge a high termination fees and um and what and we'll talk more details about like how uh IPRNs are being used and this is a legitimate business model where the revenue is shared between the carriers in that like network uh while they you're using the IPRN numbers Uh one of the other like uh downside of this particular business model is it's highly unregulated meaning that like there are a lot of providers who generate IPRNs as a service and individuals can use it for legitimate purposes but trans nexus reports almost like 121 providers but unfortunately we can see that 40% of them are like undisclosed unregulated meaning like we
don't even know where they operate from, who they are, how they operate. There is no regulations on them. So you can clearly see that fraudsters can take this as an advantage to use like to generate a lot of revenue out of it. We'll talk details about it like in the next slides. Um so this like if you see like it clearly starts out as a legitimate business model but it can be heavily abused by the fraudsters. Looking at the graph you can see that like from 2019 to 2020 we can see that IPRN grew exponentially over 8 million numbers have been generated in a short span of one year where fraudsters use this IPRN as a key component for the IRS of fraud.
Um let's see how the fraudsters use these numbers.
Oh
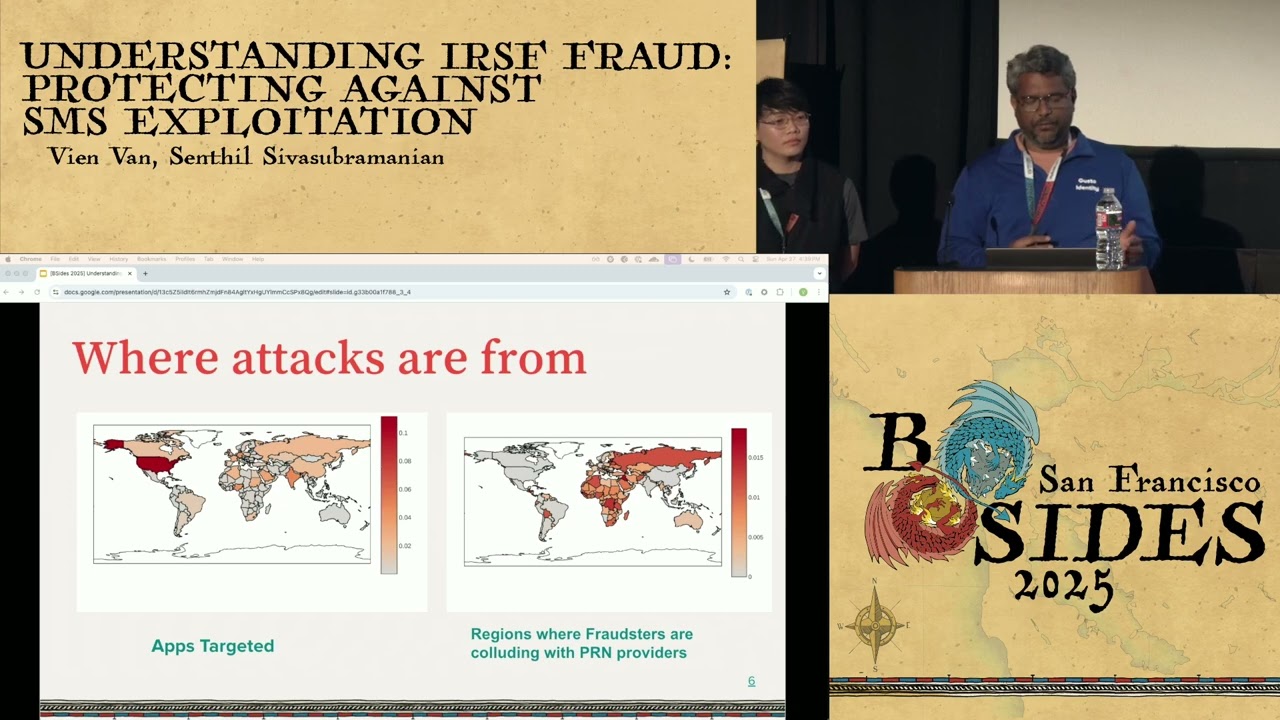
um in this case like SAP SAP research did a study in 2021 where on the left you can see there were a lot of apps who are being targeted and these apps are usually uh targeted in like countries like US Canada and like all of the locations and on the right if you can see like where are all the SMS or voice traffic is going to from your apps and you can primarily see like it's all like happening in Russia and like a lot of other geos outside of US meaning the fraudsters have as I talked about like there is an undisclosed or like an unregulated market these fraudsters collude with this PRN providers to take
your money let's look closer uh closer look at how the typical attack happens right so fraudsters collude with a PRN provider who who gives you PRN numbers as a service and what they do is they generate a they log into your uh typical like a SAS application or it could be a consumer application. They log into that system and then like let's say you have like a system where you can trigger voice or SMS calls. So the fraudsters they get into your system and then they generate a lot of SMS or voice traffic. What you typically do is you pay uh like some x amount of dollars to your uh UCS which is your unified communications as
a service which is typically your talisign twillio service where you probably play $1 for every SMS that could be sent like it's probably for your OTP code or it could be for voice traffic you probably send like $1 for that then like that telline will eventually give it give like at least like $30 cents to the operator one then the then they give give it to the international carrier because these are all usually international uh premium rate numbers and then from that like the 70 cents the international carrier will take almost like 20 cents and give it 50 cents to the operator too where they actually collute with the fraudsters thereby gaining 50 cents for every $1
that you pay. 50 cents goes to the actual fraudsters and thereby like there there is a large amount of volume of uh money that is being uh shared between the fraudsters where like uh through the SMS or the voice traffic. Next I'll hand off to Ven to go into the deeper details about like detection and mitigation. Thanks Sento. So that's why they're called international revenue share fraud. These fraudsters are colluding to each other and sharing the money with um that they take from your business. Let's take a closer look at how the attacker is able to leverage your system to execute this attack. In the first screen, we see the normal signup flow where user could enter the email
address. They're likely to get prompted to confirm that the account uh via an email. After email confirmation, they're prompted to set up multiple uh multifactor authentication. Usually, the top two are authenticator or SMS. If they choose SMS, your application could allow a user to set up SMS with an international phone number. Um, once they input the phone number, a one-time password is sent to the the phone and uh uh usually on the screen, a user can request to uh get the code resent via text message or voice m or voice. And the attacker can automate this pretty easily with a browser script. And if um these u endpoints are not uh left unchecked, it could be a uh uh surface
of attack for for these u fraudsters. Uh but uh I mentioned earlier that an email has to be confirmed. Surely they're not creating thousands of email accounts, logging into each email inbox in order to uh uh orchestrate this attack. Um well, who here has uh entered their email address in order to receive a 15% off discount on a um website? Nice. Uh I have as well. And who has added an extra plus sign at the end to reuse this uh system to get an extra code? Nice. Um well, if you haven't done it, you can totally do this to get infinite um uh glitch. But yeah, uh I'd like to introduce you to an old
friend, email tumbling. Uh email tumbling is a technique where you add extra periods or plus signs in the beginning of your email address and all of those uh email addresses they will create unique accounts on the system that you're signing up as but they all go to the same mailbox. Um this all technique is also leveraged by QA in order to test multiple accounts in the system where they don't want to you know sign up for multiple accounts in different mailboxes. Uh it's a harmless um and uh often overlooked uh technique, but it can be leveraged to uh um generate uh thousands and thousands of body counts and orchestrate an RSF attack. Uh we looked at the anatomy of
attack, what the potential lawsuits for your company, and where these attacks are coming from. Uh let's take a look at how we can spot these attacks before they scale. Um first it might be seem obvious but um uh we could monitor for traffic spikes. Uh specifically the endpoints that um the user can trigger an SMS sent for example a registration endpoint where user is enrolling onto your system or an SMS enrollment where they're setting up to FA for the first time an SMS verify when they need to log in with SMS. Uh an SMS resend where they're requesting to resend the code. Uh voice verify can also be taken advantage of uh where um you're requesting the code to be sent to
you via a call or a voice resend. Um establish a baseline for what a normal traffic for your business looks like and alert loudly on these anomalies. Um you can also look at um alerting on when new country codes are being uh used to uh um receive text message. Uh in this slide you can see if your business is usually doing uh uh receiving uh SMS verify in one country but you suddenly see a spike in another country uh work with your SMS provider and see if they have a uh monitor via email or Slack that they can alert you when these traffic going to a new country is happening. Um if they do not
implement this yourself by monitoring for new country codes being used and being saved in your database as uh for SMS. Uh you can also leverage cloud configure uh traffic monitoring tools like data dog. Data dog allows us to group access logs and analyze them by user agents, IP addresses or countries. Um on user agents, if a majority of traffic uh normally coming to your application is coming from a Mac or Windows and you suddenly see a spike in Linux, uh that could indicate a scripted and bot attacks. IP address ranges that um you haven't seen accessing your site or uh countries where these traffic are coming from. Make sure you familiarize yourself with your observability tools
and find meaningful signals to alert on so that these alerts don't get ignored by your devs. Um you can also alerts uh when there are an influx of new users signing up. Uh this is a good uh time to check in with other teams like grow for marketing. Do we have an active growth for marketing campaign that could explain the in the sudden influx of uh of new users? Or these new users have uh suspicious email domains or uh patterns in their attributes like first name, last name that look kind of suspicious. Set up the alert for when these anomalies happen at different thresholds and uh when these uh attacks are happening, these fraudulent traffic most
likely hurt other channels like the sales channels as well. So it's it's a good opportunity to work with the other teams on your company. By now, I hope you see a pattern with the way we detect this kind of attack. Anomaly detection is the name of the game here. And although your applications could be a little different attacks often try to abuse a very familiar onboarding user experience with the same UX, it's often very easy to detect when anomaly occurs. Um, now let's take a look at how we can mitigate these attacks. Um, I'll talk into details about these three strategies, but to stop attacks before they start, um, these are some strategies you can take.
You can rate limits on the anomalies that you have identified earlier. You can restrict who can use your SMS to FA and you can prevent these fraud users from entering your your system. Let's take a closer look at the first one. Um rate limits. Uh you've identified those endpoints that a user can use to trigger SMS um like uh IP region, user phone numbers, devices, TLS signatures. At the firewall level, you can analyze the unique identifiers like suspicious IP range, new countries traffic is coming from, user agents that indicate a bot traffic. You can also analyze TLS signature like a J3 hash. Uh but be careful with J3 hash to not block good traffic and good users. An a good method
in order to determine if J3 hash is indicating good traffic or not is analyzing the traffic at least two weeks in advance to see if you've seen that before. And if you haven't seen that, it's most likely a malicious traffic. Uh and then at this application level you can also uh monitor for if the same number is being used across different accounts. If the same number is being used for SMS uh more than 10 times a minute or you know 50 times a day. Um do you have a device fingerprinting mechanism? Uh there could be a good opportunity to see if the same device is accessing multiple accounts. And uh you can limit the blast radius by setting
strict ray limit rules on these attributes. Here you see a screenshot of an example uh rate limit configuration on a firewall where you can set um uh if the host name equals your website and the user agent contains a uh uh not going to contain RSF but it could contain something like Linux that you've identified as a bot traffic. Uh you can set the URI path as those that are um can tr trigger SMS and uh you can also block outright block countries if you've never seen before or allow list of countries you you want to let uh traffic through and um we can also restrict users who can use SMS to FA. I think
Wendy Natherther in her keynote mentioned a company turn off SMS overnight although this is not practical. Uh Twitter actually stopped the bleeding by uh only allowing paid members to set up SMSs or two-factor authentication. Uh I realize this isn't always practical because uh you want to improve um you want to um excuse me um you want to uh increase adoption for 2FA. Um so consider limiting the countries that you're allowing a user to set up SMS to FFA from. Um, when you do uh restrict the country codes, make sure you apply defense and depth where you take away the country code on the front end, restrict the country code from being used on the back end, and work with your
SMS provider to establish a denial list of all the countries that you're allowing to let in so that uh the attackers can't uh drive the bill up at the source. And uh you can also prevent fraudulent email domains from entering your system. Interal Consulting found that there are multiple general top level domains like top.xyz that are attracting scammers because they have rock bottom prices and no meaningful registration requirements. These domains are often used for fishing attacks but surprise these domains are also used as financial fraud as well. Um when you see these domains establish a deny list, stop these email domains from entering your system and you can also sprinkle some AI on it. Um, you can use AI to
detect. Uh, and this is an example. Um, AI could be wrong, but you could use AI to detect whether the attributes on the signup form could be fraudulent, like they're following some gibberish names, for example. Uh, you could set alerts and when these alerts are happening at scale, something's probably going on. And you can also use AI to help detect whether an email is following a email tumbling technique or fraud patterns. Um, after you set up the monitors and the remediation techniques, put together a playbook. The key to stopping an attack as they are happening is a well-written playbook. uh put down what to do when you see the alerts, what to look at, what the what what the incident
is, um how to detect these, the queries you usually run to detect anomalies, dashboards where you're outlining the SMS endpoints, how to mitigate these, your existing limit rate limit rules, your SMS endpoints, and the revalent code paths that your devs put in. And uh try to have controls where you do not need a code deploy because deployments could take a long time. uh have controls where you can uh adjust allow list or deny list on the on on the fly and make sure you link this playbook and all of the monitors that you've set up. Um let's do a quick recap. So today we've learned about what IRS is, international revenue share fraud. We've learned about related terms like
artificial inflated traffic, SMS pumping, how they make money by colluding with operators and IPRN providers. Um we learned how the attack takes shape. they find a way to onboard into your system and take advantage of SMS endpoints. Um, we see how we can detect the attack by uh uh various angles of anomaly detection usually through traffic spikes, user spikes or new country codes being used. We learn how to mitigate an attack by auditing your rate limit rules, add to it, make it stricter and have a clear playbook and attach it to all of your alerts and monitors. Um and you can find the resources we did the research here and uh I hope uh everyone has learned about what RSF is.
Thank you so much for coming to our first talk of the conference. Huge thank you to Sam Frenchie Stewart who helped us do the dry run and Brienne Bolan who's here with us today who nudged us to you know submit our first CFP and for helping us with the the presentation and uh yep we are hiring so you know hit that link. Well, thank you, Vienn and Cynthia. All right. Well, question and answer time. We do have one question in the queue, but just a reminder, we already have about seven minutes left, and we're going to put a pretty hard deadline in here, so get your questions in uh for this last talk of the day in this
theater. Again, slide. I believe that QR code is correct, but if not, I'll just kind of tell you what it is in case you don't like scanning codes with your phone, you paranoid security people. That is slide. Do so sli. Is the domain. The code you want to enter in there is besides SF2025 and you go to theater 15. I know we're in 14, but 15 is where it's categorized and we had to stick with that. So, let us go look at this first question here, which looked uh looked good to me. So if fraudsters are actively colluding with the network providers to carry out this kind of attack, is it legal and are they being prosecuted?
Um so I think like uh that's why I think like it's an undisclosed and unregulated market. It's been really hard to find out on track the fraudsters. Um we actually had tried like working with the some of the UCS providers like Teles to figure out like if they can be tracked down. Usually they operate outside of US but if they are in the US you can usually track them out and then find out and prosecute them. But generally these are not inside US. They are always outside. So it's very difficult to find out and prosecute them. Can you perhaps solve it by um whitelisting premium prefixes or deny listing? and you detect premium prefixes uh prior to texting them.
Repeat the question. Yeah. Is there a way by looking at the number programmatically to determine if it's a premium service or not? It's highly difficult to uh figure out like by looking at the numbers you kind of not figure out like it's not going to be easier for us. It could be like any random number that's being there. Yeah. Um can you put the resources slide back on again while we ask the next question and we'll just let that sit there. So, I'm going to ask this question though. How did you figure out this attack was happening to you be beyond what you told us? Did someone know about IRSF on your team or did you have to piece this
together from scratch? Uh, we had to we nobody knew about it like we learned on the fly when this attack was happening in our system on the fly. Yeah, nobody knew about it. Like we came to know like looking at like the same way looking at the normal traffic, the fraudulent traffic, the user spine signup spiking. Those are the ways that we figured out like something like this is happening. Yeah. Does anyone here need the QR code of the Slido uh screen again though? Um just specific as I asked for the resource screen to be on because that seems to be popular. Okay, we seem to be good there. Well, we've run out of slider questions for now. Let some
trickle in. Maybe you're perhaps embarrassed to type something into a device anonymously. I know that doesn't make sense, but if you're here in the theater and it makes more sense to vocalize your question, I'll give you the chance to do that. uh try to make it short so we can make this as a question and repeat it. So if you have anything just raise your hand and I'll try to attend to it and as a reminder you know we're all participants here some are in the role of speaker right now but uh this is a community of peers so we your question is probably completely relevant and uh something that someone else wants to know too.
Okay. Well, we got some uh what tools do you use for detection engineering? You want to talk about it? Uh detection engineering. Um I think we use mainly data do for detection and uh unfortunately detection engineering is another team on our uh our uh or so. So I'm not really sure what tools are being used, but I think they're talking to a lot of vendors out there um on the B size floor as well. Yeah.
Well, it seems like that we probably got a pretty good end there. Thank you again, Vienn and Cynthia. Um, we find ourselves at the end of the conference at least as far as this room goes. Uh, you can probably find Cynthia and Vienn in um in the room outside or in the closing ceremony which is coming up right nowish 5:00 I believe. Is that correct, Anthony? Uh, in theater 13. That's the only thing that's going to be remaining open at this point. So, um this becomes a regular movie theater uh very shortly. Uh and if you want to donate anything you leave here to the next people who come in and to watch a movie, that's how
you do it. You leave it in this theater. So, don't leave anything here that you particularly want. We won't be able to retrieve it because the conference is closing down. And I just want to thank you all for being here for this last and wonderful presentation.





