Gmail as a C2: Stealthy Cloud Security Threat Exposed #shorts
Show transcript [en]
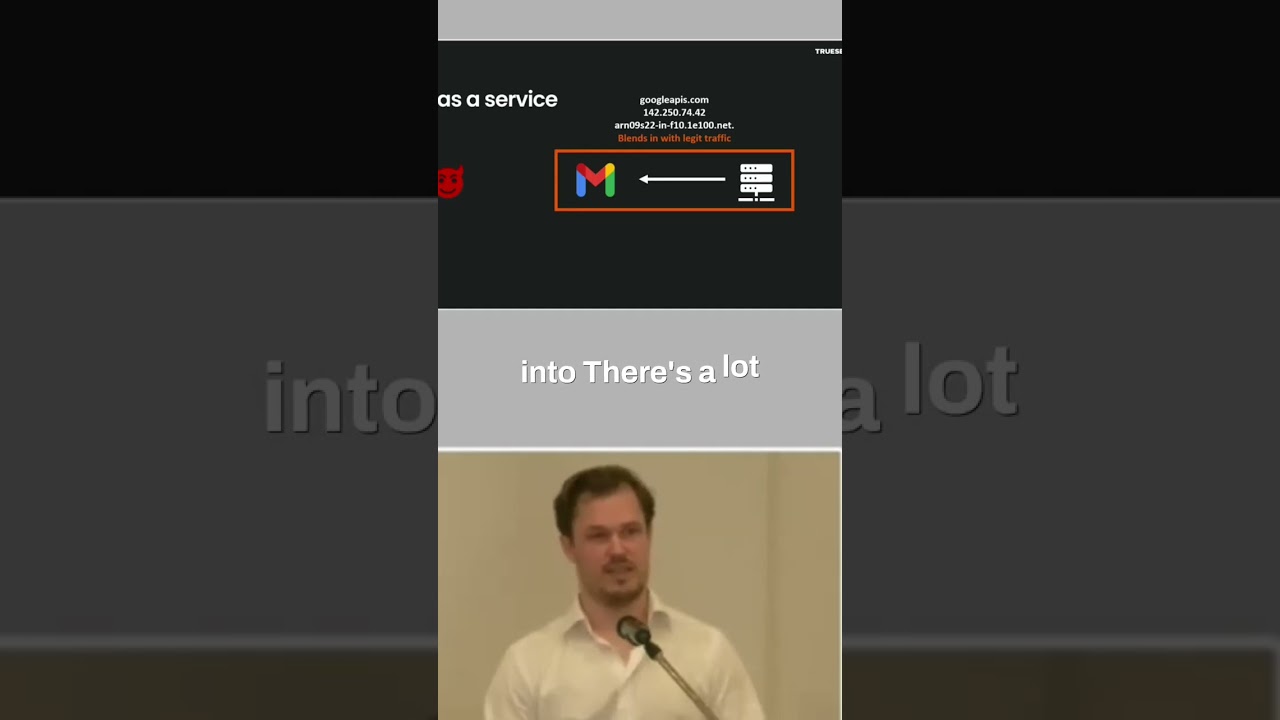
We have the secrets dump on a Jenkins server. How did I get to the Jenkins server then? And when we look at the Jenkins server, we see that there is a rat installed on the Jenkins server. So, we see that it goes through Gmail. This is nothing new, but I think it's cool just because we're talking about cloud security. Threat actors can also use cloud, and they can get a C2 as a service, as I used to call it. We talk about Gmail here, but the same principle is going to apply to we see I mean there's open source C2 channels for like Slack and Dropbox and pretty much any service that have the features needed to do this.
But basically, what they're doing is that they are querying from the rat. We have the rat where the server with the rat is, and then the evil is the threat actors C2. So, it's questions like, "Do you have any new draft for me?" And it says, "No." And it keeps polling like that. Checks for a new draft. And when the threat actor wants to communicate with the rat, it creates a new draft. And I mean, this is a bit simplified, but you still understand the concept. So, it creates a new draft with like exec you name A, which is the command they want to run. And then the rat gets that command. It executes the
command, and then it adds an attachment to that draft, which is the output of the command. And then it checks for attachments obviously on the other side of things, and it gets the draft. When it reads it, it deletes it, and so on. So, then you have like a channel where you tunnel everything through Gmail. And if you're just looking at network traffic, it's going to be kind of hard to see this, right? Especially if you're this company that we're talking about, who's actually using Google Cloud, which we'll get into. There's a lot of services that are talking to Google Cloud all over the place, right? And I think that's when we see this being used by a sophisticated
actor, they look what services are the this company using. If they're using Slack, and they have Slack integrations for pretty much everything, then why not use Slack as a C2? It's going to be really, really hard to find that in the midst of all that traffic. So, it's really hard to see it network-wise. On the other side, we're obviously completely blind. So, we cannot see anything because it's just a threat actor accessing Gmail on their end, right? So, is this the perfect C2 that is like the C2 to rule them all? Well, it's got one big of a problem, right? To be able to do this, you need to persistently store the credentials to the Gmail account on the compromised
server. So, before we turn ourselves into cowboys and log in to that Gmail account, because of course we can, at least do the things that that API secret is able to do, we actually found that by collaborating with these vendors, like Slack and like Google and so on, if you just talk to them and say that someone is abusing your infrastructure as a C2, and you give them evidence, they're actually really helpful in my experience.





