Fake Hires, Real Threats: When Background Checks Aren't Enough
Show transcript [en]
I'll introduce Mabel who's going to speak on fake hires, real threats when background checks aren't enough. Uh reminder, we are not doing verbal Q&As. So, if you have questions uh for Mabel, please put them on besides.sf.org/q&A. With that, thank you, Mabel. Thank you. All right, so I think we have all heard the phrase fake it till you make it. I know we've all heard that, especially when it comes to our careers. But what happens when someone fakes it, makes it, and then infiltrates your organization. So, I'm here today to talk through a few things with you. um a history on fraudulent candidates, what signs to watch out for, what we ran into at Clockwise with fake candidates, how
to stay mindful of hiring biases, a few mitigation tactics, and what the future of hiring will look like. So, before we get started, um all of the applicants in this presentation have been deemed as fake, completely made up. Um, if you do see your information on here, um, let's chat afterwards because we might need to check your your credit score. Um, but lucky for you, um, I am a real person and I am not a fake candidate. So, my name is Mabel. Um, it feels like I have lived many lives at this point. At one point, I was a nurse aid. Um, but I started my what I call my click-clack career out in accounting and
I found my way into GRC. I've had the pleasure of sitting in a variety of functions um, beyond the traditional security team. I've sat in internal audit. I've sat in engineering and I've also sat within the legal team. When I first put this talk together, um, last year's No Before case was one of the few public examples out there. But since then, more stories, more headlines have come out and it's become very clear how big of a problem this is. So, how did we get here? to take a step back. Um, I want to say this also has been happening prior to May of 2022, but the US Department of State, Department of Treasury, and the FBI came
out with a joint advisory about fake North Korean IT workers that were coming into organizations and they were targeting cryptocurrency companies. Um but as they have evolved pretty much any company is up uh for game here and um since then they have uh have joint uh follow-up advisories and as you know in July of 2024 the uh noore case was publicly shared. I won't go and discuss this in depth because they have already released the incident summary on this. But some key points that I want to hit is that this person was able to pass multiple interview rounds. They will they were able to pass a background check using someone a US citizen's um stolen
identity and finally they were also able to pass reference checks. So how does this actually work? There are many variations of what occurs here, but the first step is to establish a fake identity. So they may use a completely fabricated uh name and information. They may use um US citizens stolen information and in some cases they may actually work with a real legitimate developer or person to have them stand in and do the hard parts of being on interview doing the actual technical rounds and then um switch them out later on in the process. And there's also multiple personas. This is an entire network of fake people. they're basically giving each other references, setting up these front companies as
well. So then um the next thing is to apply for a job and get hired. I think we all know how AI has made this extremely easy to create a bot to automatically apply for jobs as soon as they are posted. Um and also there have been many ways to just ease through an interview, have a guide or a coach to help you through these interviews. And then step three, they get hired. But what are they actually doing? They are downloading sometimes remote uh tools. Um they'reVPNing into your environment to make it seem like they are based in the US. Um they are stealing company information if that's not obvious already. Um they do try to work the
night shift um since they are based maybe not in the United States. Um but to make it seem like they are working uh in the US in the daytime. Uh step four, um most importantly, uh they're getting their bag. They are making money off of this. They are funneling their paychecks back into North Korea to fund their government's weapons program. So to sum it up, these folks are exfiltrating company data and your organization is paying them to do it. So during my time at Clockwise, we caught a fake a few fake candidates um before it got that far where we actually hired them, but it was very clear that something weird was happening. Um I also want to preface
this by saying that at the time we were like a 50 person company seriously startup and I think there is a common misconception that this is only impacting a fortune 500 companies you know these really large organizations where you can really get lost um in the numbers. No this is happening even with two person companies. So this is not something that is just happening with larger organizations or more mature organizations. So, let me walk you through what happened and how we responded. So, in 2023, I had reached out to our head of talent to ask casually if we were seeing anything like this. And at the time, we weren't. It was one of those things that
I kind of filed in the back of my head. I was just like, we're not dealing with this. No biggie. Well, several months later, I get a slack from an engineering manager and they had finished conducting an interview and he said, "Hey, this seems really off and I know I'm not the only one um from the engineering team that has been experiencing this. This last call was really weird. It sounded like they were there were multiple people in the background chatting. um the latency was really bad on the video and they started asking really weird questions about our company specifically where people lived and not in the aspect of like where are you a remote first
organization but they really wanted to know where did people live. Um so we actually looked at this further and um what we did first was with this particular incident uh we pulled the logs from Zoom to see where this person had called in from and you would think with IP addresses and the way they can be spoofed that you we thought this would be a US-based address but no this um particular call was coming in from a Russian-based IP address And when we expanded our analysis, so we grabbed the engineering managers and said, "Hey, can you provide us a list of folks that you interviewed that you thought were fake?" We actually found more instances of this where people were
calling in from or doing their Zoom interviews through uh with Pakistan IP addresses and addresses in Spain. And after that, we actually implemented Zoom geob blocking to prevent things like that. Um we also found that the majority of our fake candidates came in through uh thirdparty sourcing integrations. So we use greenhouse um for application tracking and we found out that the majority of these were coming in from one specific integration. Happy to chat afterwards about which one it was, but um we ended up removing that integration um from Greenhouse. And then of course we had education with our hiring managers and with our interview panelists um and our hiring team on what they should do and to also empower them
to end a call if they did not feel comfortable. So I want you to meet Hannah. Uh this is a bad example of a really bad resume and loweffort resume. But um a couple things to call out here is that uh the GitHub URL that she provided um it just leads to a 404 error. Um it does not exist um like Hannah does not exist. But also when we dug a little bit deeper into the first company that she worked at um we went to the website and at first on the website it looked like a normal company. It had testimonials. It had web pages. I mean, it looked beautiful. Um, but then when you kind of scrolled down a little bit
more, uh, some things started looking a little bit off. Uh, like their email address, where they were located, and then when we looked them up on LinkedIn, uh, they only had two employees working there, and they were not based in the US. Now, I would like you to meet Sophia. Uh this resume is a little bit better in terms of uh we'd sort of consider ré quality, but we noticed that there were minor discrepancies on the resume. And I think a lot of the times recruiters or hiring managers may brush this off um because there are legitimate reasons of why someone might have a discrepancy on their resume. But one thing to point out is that the
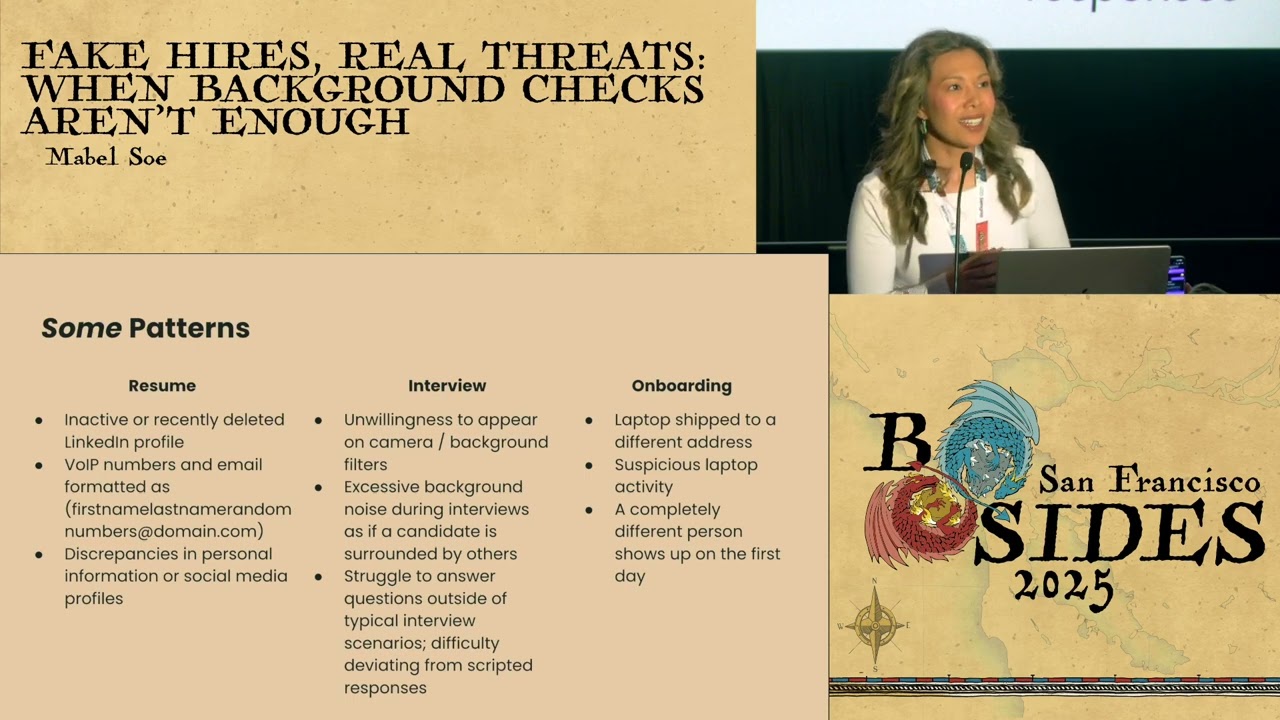
email address that was listed on the resume was not the same email address that was sent for their interview. So that is also they were very similar but they were not the same and I think this goes back to that hiring uh recruiters they are very much pressured to fill roles and they may not catch these when um scheduling interviews on behalf of interviewers. Um, one interesting thing about Sophia is that we had already implemented geob blocking at that point and uh, of course, she did not join the call and immediately sent this follow-up email to our hiring manager, which was only proof that this person was fake. Okay, so what are some patterns that
we're generally seeing? Um, many of these fake profiles will have an active LinkedIn profile, but then in parts of the hiring process or maybe when they're caught, they'll either hide the profile or it's just completely removed. You can't find them again. Um, another thing as well is that sometimes they will um the profile will be pretty new. So, you'll see that they joined LinkedIn maybe in the past 5 days or the past month. And they will also look pretty generic. Um, they're also most likely using a voiceover IP number. Um, I will talk about this later, why that's not always an indicator of a fake candidate. I'm sure many of us in here have a separate
phone number, uh, outside of our usual. So, um, with a lot of these résumés, uh, you will see a pattern emerge. So you'll see they'll come in batches and that you'll see some of these same universities listed. You'll see some of the same locations listed. You may see see similar work histories. They may um pick a company and you'll get a bunch of them that have worked at the same small company. Uh and you're kind of questioning how is this even possible? Um during the interview of course they will try not to appear on camera. there may be uh very big lag. There will be background filters. Um there's usually excessive background noise as well. Um so it's there they may
be in a laptop form where there's other people involved and they will struggle to answer questions outside of the typical interview process. Um they struggle with casual conversations. Um or of course again with AI they may pause and then give some generic scripted answer. Um hopefully you won't get to the onboarding part but uh we're seeing that laptops are being shipped to a different address than where they say they're geolloc. Um they will also try to change the address or say oh it's an emergency. Oh I'm moving. Um please send it to this address instead. Uh and then of course suspicious laptop activity um remote admin tools uh being downloaded and uh in some cases a completely different
person shows up on the first day. Uh, this is kind of interesting in the sense of I think since we're all people and humans, you don't really want to call out somebody that you interviewed and then say, "I don't think this is the right person that actually showed up on the first day." Um, but this is a few and far between.
um red flag or hiring bias. So, like I said, um it's easier to almost like spot anomalies in a log. So, if you look at logs all day, it may be easier to to spot an anomaly there um than it is, you know, compared to human conversation. Um people are complex. They're nuance. Um people are shy, awkward. um we all have our reasons uh you know for maybe we've moved multiple times every year um and maybe that looks a little bit off. I know we're in really tough times um where there's a lot of layoffs occurring as well. Um so we want to make sure that we're not leaving or discounting real talented people. Um
I didn't include this earlier in my patterns, but um if you look at any of the advisories from Mandant or um the government on this, they do mention that uh there are signals of folks that have Americanized names and then you get on a call with them and they have a very strong accent that is not where you would typically see them from. Uh, I also want to state that race or accent is not an indicator of a threat and we should really be careful of that. Um, and also um, our Civil Rights Act does not permit hiring discrimination based on nationality or race. Now, before we can mitigate, we need to understand the hiring process. Do you
know what your organization's hiring process looks like? Um, do you know what checks are in place? Where in the process are we uh identifying or verifying someone's identity? Is it just through the I-9 verification process? I think we have seen that this doesn't really work. Um, I recommend that if you haven't already to start working with your talent teams. Recruiting, like I said, is often under pressure to fill roles very fast. Um, you'll need to understand the trade-offs and the constraints. Uh, it is also a very big waste of time, energy, and budget. I know if you're a leader in here or if you're an interviewer or hiring manager, what a struggle it is to get the budget
to open up for a role in the first place. And then now you're spending all this time going through the hiring process weeding out these candidates. Um, and of course, like I said, candidates are not just a security risk. Um, they do drain our teams. Um, and you need to understand the trade-offs. What's going to be worth it for your organization? Are we going to add more steps in the process? Are we going to get some fancy software tool that can uh reidentify or make sure that these people are who they say they are? I mean, in this economy, I'm not sure. I'm not sure. Um, and you can also expect that um these threats will continue to
evolve. Um, the p different patterns are emerging. Um, so you want to stay flexible. All right. So mitigation tactics um from pre-screening and application submission surprisingly uh I have been seeing at least in my observations more long form questions to weed out generic applications even though uh with AI um it's pretty easy to kind of generate a paragraph but um from what I understand is that this is also a way to for folks to actually be really specific and uh personalize their answers. Um, additionally, uh, some tactics are checking their LinkedIn profile. Like I said, um, if you have a developer, um, heavy role, you might want to check their GitHub contribution activity. Um, and this would be a good
time to actually go to an engineering team and ask, hey, what would you normally want to see? What kind of questions would you want to ask this person if we were to screen them on what what they've done in their work? Um, some recruiters are getting uh tools for phone carrier lookups to screen for either stolen um phone numbers, spam phone numbers or voice over um IP numbers. And there's also I we've been seeing a lot of knockout questions or even some smaller organizations are using um hidden instruction questions. So during the interview process, um we should move away from phone screens um and just jump straight to to hiring or to not hiring them. Uh not
that uh we should definitely uh just start with video and um asking location specific questions. Um asking casual questions. Can they uh tell you what their favorite coffee shop is? Um, I did put on here record interviews. Controversial, I know, but um, this would require consent from your candidates and you would most likely need to work with your legal team and also understand the privacy implications as well. Um, but I think most importantly, you want to empower your interviewers to end the call if something's wrong. Um, I want to be clear, you don't need to confront these people. You don't need to troll them. um you want to arm them with soft scripts that they can use if they feel like
something's off um and not waste any more time uh to trying trying to fill this role. So, you can say something like, "Hey, I'm going to pause here. I need to follow up with my recruiting team." Or, "Oh, I have an emergency." Um our recruiting team will reach back out to you and you can end the call. Uh mitigation tactics for onboarding. again hopefully you will not get to this point but um laptops so um I think we're seeing more and more companies as well doing onboarding in person now so they'll need to go get their laptop in person in the office um some organizations I've seen as well they are shipping their laptops to um a
local UPS uh the nearest UPS shop or delivery service and they're doing identity and identity verification there. Uh, again, some of these can still be uh bypassed. Well, probably not the inerson part, but um picking things up at a at a local shop. Um, and also reconciling the information. So, this might be a good time to work with your finance teams and your HR teams that are handling all of these payroll um information from from your employees. Um, and then of course, uh, enhanced monitoring if you can swing it. I know resources can be constrained, but if you do have enhanced monitoring for new joiners, um, what you would need a baseline of what you would expect a new
hire on their first couple weeks on the job, what activity would you expect from
them? So, we're clearly seeing some big shifts in hiring. Um, I know I have felt it as well. I think everyone in here has gone through, you know, several rounds of interviews, take-home exercises. We've evolved. We've taken personality tests, all sorts of hoops that we've had to jump through just to get hired. And now we're competing against these fake workers. Um, I think a lot of organizations are also moving to referrals. they are trying to figure out a way to establish trusted ways of finding candidates. Where do we source them from? Um but also who are we leaving behind um in that process? Not everyone has the joy of making it out to something like Bides or any other
conference. Um so I think where we go from here is still unfolding and still evolving but um I think one thing is is very clear that our hiring processes have got have to keep up. they have to evolve so we can stay ahead of this and make sure that um your organization is protected, you are hiring the right fit and um ultimately keeping your organization safe. So I will pause here. Uh thank you for your time today. I will open it up to any questions. [Applause] Thank you, Mabel. And uh our next talk will be in uh 25 minutes. So, thank you folks. And sorry, we have questions. Oh, perfect. Yay. Sorry. Okay. My bad. No,
you're fine. All right. So, uh let me start with the first one. And thank you, Sarah. What was the integration you removed with positive results? Oh, the integration we removed. Um I don't know. Did I get sued for this? I don't think so. Uh we removed um Wellfound, which is uh formerly known as Angel's List. Um that actually brought down a lot of the um fake hiring candidates. If you work for Wellfound, please don't come for me. Is it likely that any of these fake candidates would be able to pass a fingerprinting, background check, and dug drug screen? My company requires that for all hires. Wow, that sounds fantastic. Um, I don't think for uh if they're taking
biometrics or um a drug test, I'm sure it is possible. Whether or not they want to go through the hoops of doing that is another thing. Um, so I'm honestly not not sure, but that sounds like a very thorough process. All right. Are fake candidates coming through recruiting firms? Yes, they are. They can come through recruiting firms. Um because uh do you really know your recruiting firm is is the question. It is incredibly easy just to spin up uh especially on LinkedIn, you know, a fake recruiting organization. Uh does this only happen for remote roles? Uh do you see this at all for hybrid positions? Um I think this is primarily affecting remote uh fully remote roles. Um but it
can affect hybrid um hybrid roles in the sense that they will still try to get through the process and ultimately it still wastes it still wastes resources.
This is a long one. Okay. So we have found three of these at our company now, 1600 people, one engineer and two on the business side. The engineer was even able to commit code. But now we know what to look for. Okay, thank you for the comment. That's great. Uh how do you institute checks from vendor or managed service contractors? Ah that's a great question. Um, so I think traditionally, um, in the past when we have, um, vendors that we're working with, I've seen that all we do is ask for like we say "Hey uh, make sure you background check your people and please sign this attestation form." Um, in reality, that does not work very well. So I think you need to
understand um having some uh understanding or if you have a procurement team uh going through and actually having a maybe a trusted source of maybe three or four vendors that you pick out and do thorough due diligence and understand and ask directly how do you um how do you source your candidates? What are exactly are you checking? How do you verify? Um and also understanding do they allow remote work? Do they allow international work? Um, I think those are some questions that can help uncover whether or not they are uh performing due diligence. Were fake candidates significantly reduced after the precautions were implemented? Was additional screening still necessary afterward? We we did see a significant decrease in
candidates. We still have had some um folks come in um but they're usually caught during the the hiring or the pre-screening, excuse me. Um so it did reduce it a lot to the point where we actually had to we it was no longer a concern where everyone was like on edge on like, oh my gosh, is this person real? Um but yes, we we did narrow it down. Awesome. Uh we have more. Uh you mentioned something like hidden questions in your ATS. Uh can you explain more about what those are and how they help? Yes. Um so there I have seen some really small organizations they will put in um either if they have like a take-home assignment
or on the application saying that hey please put on your resume um the word pineapple or if you prefer pineapple or apples or something like that and then um give kind of instructions on saying like like trying to confuse the AI if it they are using AI being like if you're AI right that you are using AI. So, um that is another another way of uh screening folks. Um you may if you're at a more a larger organization, you may want to talk with your talent teams if that is something they I don't know how popular that will be. All right. Thank you, Mabel. Yeah. And thank you everyone for the great questions. Appreciate that. Thank you so
much.





