Jak zdobyć flagę?
Show transcript [en]
Hi, I see that there are a lot of people in the room. Greetings to all the people who are watching us on stream, including our friend Radka Żuber. Unfortunately, he couldn't be here, but he's probably watching. Today we will tell you what CTFs are, what they are about, what categories of tasks they are and how to start. We would like people to start playing with us, Well, it turned out that we tried it and it was a great thing. That's it. A bit about us. My name is Mateusz Szymaniec, I work at CERT. Of course, I am also a co-founder of P4. I do some tasks and these texts will be explained later. I am Jarek, I work with Mateusz at CERT
and I am also a co-founder of P4. I'm also doing some tasks, completely different from Mateusz's, but it's good because we're completing them and we're somehow living. Yeah, a bit in our team. Generally, our team came from the fact that there's a portal for programmers, where we're admins and moderators. And there was a chat and a friend who used to work in SEC told us that maybe you'd be doing security and there are such CTFs. So we were voting for CTFs, it turned out to be quite cool. The name P4 is created from 4programmers, but the opposite, we even have a similar logo. This is our website. You can see it, but we'll explain what it is. It turns out
that we started in 2013 and our team has developed a bit, we've also gained some knowledge and it turned out that we're doing pretty well, because we're currently in the fourth place in the world. I'd also like it to be better. So, a small agenda and let's get started. There are different categories of tasks on the CTFs, actually they are different types of the CTFs, but I'll talk about them later. But on the first category of the CTFs there are tasks that belong to one of those categories. These tasks can be combined, they can belong to many categories. But in any case, more or less such issues are on the CTFs. We'll explain each of them in a
moment. What is CTF? Does anyone play CTF? Hands up. Great. I hope that in a year, if we are here, there will be more of these hands. Everyone will raise their hands. Yes. And the CTF itself is a description that doesn't say much. Anyway, it's more or less a competition for computer security enthusiasts. And that's it. There are tasks. There are tasks. There are points. And people are awarded. It's great. There are two main types of CTFs: Geopardy and Attack Defense. Geopardy is a product of an American contest called Wabang. There are categories and each task is rated for a certain number of points. As you can see, there is a screenshot of one of the CTFs. where each task is a rectangle, you click on it and get
a task description. And here you can see that there are some categories, each task is rated from 100 to 400 points. Traditionally, the task is rated from 100 to 500 points. There are also Hindu Jopards, so it turns out that Hindus are a big country and organize a lot of CTFs, but their quality leaves a lot of room for improvement. When you choose which CTFs you want to play and which not, the Hindu ones are a mess. This is a very interesting type of CTF, it is more difficult to organize than Geopardy, but as the name suggests, it is about not only fighting with tasks that the organizers prepare for us, but we both attack
and defend, i.e. there is a created infrastructure, each team gets a task, The first category is Revenge Engineering. It's the lowest level, maybe beyond owning, type of task. We get a binary and we have to figure out what it does. Here's the general semat of these tasks. So, a program reads some data, does some magic and checks if the data was good. We have to open this click in a debugger or disassembler and figure out how it does the check. For example, it compares with a password or counts some hash, md5. And we need to use our knowledge as a reverser to take out the algorithm. Here is an example of a very simple task I wrote. It took 5 minutes. There
is a program that we are using and we enter the password to it. The program checks if the password was correct or incorrect. We load it to ID, because it is our favorite tool, and we look. I don't know if anyone knows assembler, but even if you don't, it's easy to guess. There's a printf, a scanf, strcmp, and you can see that the password is compared to the written one. And on a real CTF, it was a flag. Besides the fact that there are no simple tasks on a real CTF, You just need to do something like that. In practice, the easiest way is to load it into hexraces, which can replace something like this into a code
that is almost always correct. Even if you're not an expert in reversing, but you've seen something like that before, you can solve most of these simple tasks without any problem. Or you bought it in Zatoce. We don't recommend it, there are bug doors. Yes, no, no, you can't do something like that. But IDAP is free, so you can do without it. So what? We enter this flag and we did it, we got 100 points, let's say. Besides, the real CTF tasks are harder, but the principle is always the same. We enter something into the program, the program checks if it's good and we get points. Here is such a... An example of an interesting task that was on Confidence this year and was
made by our colleague from work, Mac, who presented it here on Friday. But I don't think he's here. He's probably drinking at the bottom. Anyway, he created his own architecture and we only had a binary file that needed to be loaded from some hex editor and to find out which encodes do what, etc. And basically, starting from nothing, with the editor itself, we could figure out what the assembly machine looks like, what the program does, then we could make the algorithm, and that's how we got the flag and we got 500 points. It was one of the most important tasks on CTF. Yes, here you can see that the code, the password that was needed
to run is the pin, which is 5129, and it turned out that the algorithm that was implemented with the help of this VM was the RC4 encryption. Yes, you can't see it anymore, but there are other things, for example tasks that pretend to be KGN or ransomware, and you have to break ransomware, of course pretended ransomware. Often there are some difficulties, such as anti-debugging, anti-disasm, or weird architecture. In Poland, there were popular crack me and such tasks. If someone has ever done something like that, then this category is the most similar to the classic ones. Yes, it's basically crack me. OK, but there are also other categories, for example... Yes, for example, "own". On the
one hand, the category is similar, because we also get some binary, "slide", we get a binary, sometimes Linux, sometimes Windows, and of course we also have to learn, like with R, how it works, but apart from that, how it works, we have to notice some errors that are in it. And the point is that, OK, we get some binary, But there is no flag in it. Sometimes it is cut out or it is somewhere on the server. The binary itself is also run on the game organizers' server. This binary is communicating with us using standard input and output. But on the server, input and output are redirected to TCP and we can connect to TCP. Everyone can access such server and play with the binary already
running on the server. What does this game mean? We have to bring to the situation where we can make our own code in the process of this binary. The scheme is that you have to find these errors, and with these errors you have to take the opportunity to do certain things. The most basic one is Write-Read Primitives, which is the ability to write and read the memory of the process. And with these primitives we have to be able to make some code. Then we write the program that does it, because we do it manually, and run it on the server. Mistakes that are in such applications, it can be for example some, it can even be a reading to a buffer and it can be some common
buffer stack overflow, but it can be something more complicated, for example, it can be some kind of a shortcut, which we can create elements, edit, delete, there are different types, and for example, it can be use after free, so we delete some element, then we create another type and we can properly, in memory, We wanted to make the structure so that we could edit not what the authors of the task wanted. Of course, when we manage to do something like that, the exploitation itself is not always so trivial, because there are, over time, and the authors of the compilers and operating systems created some security that are supposed to make it difficult or impossible to exploit. And depending on the difficulty of the task, almost every task
has one of these security, for example, and of course you have to omit it somehow. They are always made in such a way that it is still there, because then you can't solve the task. And these are, for example, techniques of omitting these previously mentioned security, for example, we can bypass DEPA by creating ROPs, Return Oriented Programming. This is an example, a real example that was once there. It was based on the fact that the program was collecting some buffer from us, giving us the address of this buffer, and then nothing, then it was written out and this program had to be exploited. And you can see here right away that we have a scanf on a buffer that has 128 bytes, and we can give more,
of course, so there is a stack buffer overflow, But we have an obstacle in this program. And of course the goal is that if we have a buffer of alpha, then who knows how to use it. What should be done to be able to perform your own function, for example. Exactly. Exactly. Writing the return address of this function. The problem here is that it should work. This highlight doesn't work. Anyway, here you can see how these local variables are arranged on a stack. And we can see here that this buffer has 80, in fact, it has 80, in fact, it has 80, in fact, it has 80, in fact, it has 80, in fact, it has 80, in fact, it has 80,
in fact, it has 80, in fact, it has 80, in fact, it has 80, in fact, it has 80, in fact, it has 80, in fact, it has 80, in fact, it has 80, in fact, it has 80, in fact, it has 80, in fact, it has 80, in fact, it has 80, in fact, it has 80, in fact, it has 80, in fact, it has 80, in fact, it has 80, in fact, it has 80, in fact, it has 80, in fact, it has 80, in fact, it has 80, in fact, it has 80, in fact, it has 80, in fact, it has 80, in fact, it has 80, in fact, it has 80,
in fact, it has 80, in fact, it has 80, in fact, it has 80, in fact, it has 80, in fact, it has 80, in fact, it has 80, in fact, it has 80, in fact, it has 80, in fact, it has 80, in fact, it has 80, in fact, it has 80, in fact, it has 80, in fact, it has 80, in fact, it has 80, in fact, it has 80, in fact, it has 80, in fact, it has 80, in fact, it has 80, in fact, it has 80, in fact, it has 80, in fact, it has 80, in fact, it has 80, in fact, it has 80, in fact, it has 80,
in fact, it has 80, in fact, it has 80, in fact, it has 80, in fact, it has 80, in fact, it has to avoid the risk of overwriting. And we implement compilers. And here we see that the author did it himself. For the sake of simplicity, these are variable numbers. In X86 listing it looks much more complicated. Here we have hexraces and we know what to do. So when overwriting this buffer, when we click down, we have to enter this channel and then the return address. And here we see the exploit. which does all of this. Here is the IP address given by the organizers, where this service worked. We download the address of
this buffer, which will be our shellcode. This long string of bytes is the shellcode that calls us sh. We also add our stackguard. Here it is exactly the same number that was there before, only that we byte. And then we can make any recommendations. Now let's talk about the tools that are needed or at least help in this type of tasks. There is Aida Pro, which is our favourite tool, especially because we have it at work and we have a license for it. It's a bit hard to buy it yourself because it costs so much. It's also a more advanced tool, The biggest one exists and they were able to develop it for the longest time.
It has a lot of different versions of architecture. It has Hex Races, which make everything easier. AIDA doesn't work on everything. There's also GDB, which works on everything. You can run a code. There is also a GDB server, so you can run a remote debugger on a computer that is somewhere on our server, and then run an IDE and connect to the GDB server from our IDE. So we are able to debug everything with the power of these two tools. But since it is a good business, a lot of new deassemblers and debuggers are being created. There is Binary Ninja, which is very It was recently promoted by various people, even on CTFs. Apparently it's cool, I don't know, I've never used it. It's
quite cheap, I mean, a normal person can buy this program as much as possible. I remember it was $100. Another relatively new tool is Radar 2. It's an interesting tool in that it's fully console-like, so old-school, everyone likes consoles, it has nice colors. It says that it's a Vim among debuggers, because you need to know a thousand keyboard shortcuts to do something with it. But some people like it. There's x64dbg, which I didn't use either, but it's also supposedly good. I don't know what to say. Have you used it before? No. Yes. If someone wants to, it's also cheap and you can try it. I'm a kid of AIDS. And there's the OwnTools library, which is a great Python library, which allows you to do a lot of things
when it comes to exploits. You can connect to the server and instead of sending things with a raw socket, we have a library that takes care of all of these repetitive things. Exactly. - Which is basically a code for exploits for all architectures. - Yes. Actually, you don't need to know Python to play with CTFs, but it's such a good language for this use that it's just easier. I originally, as an online programmer, wrote my first exploits in C#, and it works, but it's not just manual. Sooner or later, everyone will come to the conclusion that it's nice to write it in Python, or in Ruby. There are also many other debuggers that work but are better in our
opinion. If OliDBG is still old school and immunity, then WinDBG, Softice, CDB, NTSD are tools that don't fit to CTFs because they have different applications. What can I say? Next category is webs. Some of the sites have fewer web pages, some have more. The most hardcore web organizers say that web is a bad category. We should only look at ASM. But there are web pages and we just get an address to an app that is usually written in those languages. PHP is of course a great tool. I'm not a great speaker for such tasks, because there are plenty of ideas for breaking PHP. There is also Perl, where you can break something even more. Yes, there
is even more in Perl. It's hard to read Perl. And an example of a task. Luki typu ołasz ten top ten no cokolwiek nie wiem pewnie większość z was miała styczność z jakimiś błędami związanymi z bezpieczeństwem aplikacji internetowych No i to jest taka przykładowa przykładowe zadanie dostaliśmy adres do aplikacji PHP która do której można było uploadować ikonki można było się tworzyć i edytować i tyle i to była cała aplikacja No ale założyliśmy od razu że nawigacja klikało się po linkach był parametr get op operation i And it turned out that it works in such a way that there is an INCLUD where the GET is not filtered and it is added to this PHP. You can't use null byte poisoning here to add anything, because it turned
out that the PHP version was too new. But there is PHP, something like filters, wrappers, and they do it in conjunction with INCLUD or other functions that collect resources. They can do strange things and for example one of them is something like a rapper which is called a filter and we can do some operations on such connected resources. And this is, for example, encoding 64, we give the resource and then the PHP dot will be added, so this resource will be the actual file. And if the base is included, it will be displayed, so we can download all the source codes of all files, at least PHP files, which are in the application. And that
was the first step to actually find out what's going on there. And we know now that it will be difficult to do something with this upload, because first of all, the file will always have a PNG extension, you can upload only real graphics, because they were imported with a full GD. All metadata was stripped, but we can edit this image with an online editor, so we can change their pixels. But we still have only different images. But PHP also has a ZIP read filter. We can create a PNG that is simultaneously a ZIP, and in this ZIP there is a PHP file. And it will still be the same file. And the code that is, these hexes, is this
ZIP. And these must be pixels of our image, And then, using another ZIP filter, we can include our PHP shell. I think that PNG was just throwing it on all these servers and now it has like doors. Exactly. It's not a coincidence, in my opinion. And such a ready-made PNG is something down there. Nobody sees it, but it's... PNG 32x32 pixels with PHP shell. Jarek, please explain how it works. Why PNG and ZIP at the same time? You didn't tell me that I should explain it. OK. It works like this: ZIP is a very strange format and... There is no header at all, contrary to what many people think. Maciek said yesterday in his presentation that normal formats have a
header that is at the beginning. ZIP is a less normal format. Yes, ZIP starts basically from the end. According to the standard scanner, it reads the last 512,024 bytes of the file first and looks for the last header, i.e. Central Directory Header. And from this header it starts looking for the document tree only backwards. It sounds pointless, because it's like the heads are at the end, but it makes sense, because ZIP can be streamed, so you can generate ZIP dynamically, so new files come in and you generate them all the time, and you don't have to wait for the entire input to start generating something. But it allows us to make cool tricks, like making
a shell in ZIP, because the file starts with a php code, php is happy, it does it, and the file ends with ZIP, and ZIP is happy too, because it can open it and it thinks everything is OK. And at the very beginning there is a png code. Yes. And then we have this matryoshka. And it turns out that it worked and we could perform any PHP function. Of course, we create a system and it turns out that the flag was in the root. These are the opinions on the CTFs. The tool we can use is of course a regular website. We can use the inspector to see what's going on. If we click on it and see what's going on, we can start
a burp or a fiddler. A very cool tool in burp is a repeater. We can modify the questions and keep on bushing. It's not used on automatic TTFs. In theory, it is possible, but in practice almost every CDF forbids it. Therefore, tasks that can be solved with automatic dependencies are rather weak tasks. You just do it in such a way that you can't do it. And of course, Python for writing exploits. If someone can see the subtitle, maybe someone can tell what it is called. Poe long to bytes crypto EN? Yes. Oh, a lot of people know. The task in crypto is pretty simple. In the previous one you have to think what to do and where to break. Here
we always get some encrypted data and we have to decrypt it. How we do it is our business. Usually we don't get a hexadecimal block and say "have fun", but we get something more. For example we get more encrypted data, so we can earn some kind of cryptanalysis or we get a code that encrypted this data and then we see that someone used a 4-byte key and we can corrupt it or we get a service where we can put more data and it returns encrypted data with the same key and in this way we can mathematically, magically break this key and what can be broken on such tasks? How many ROT13s can be broken or
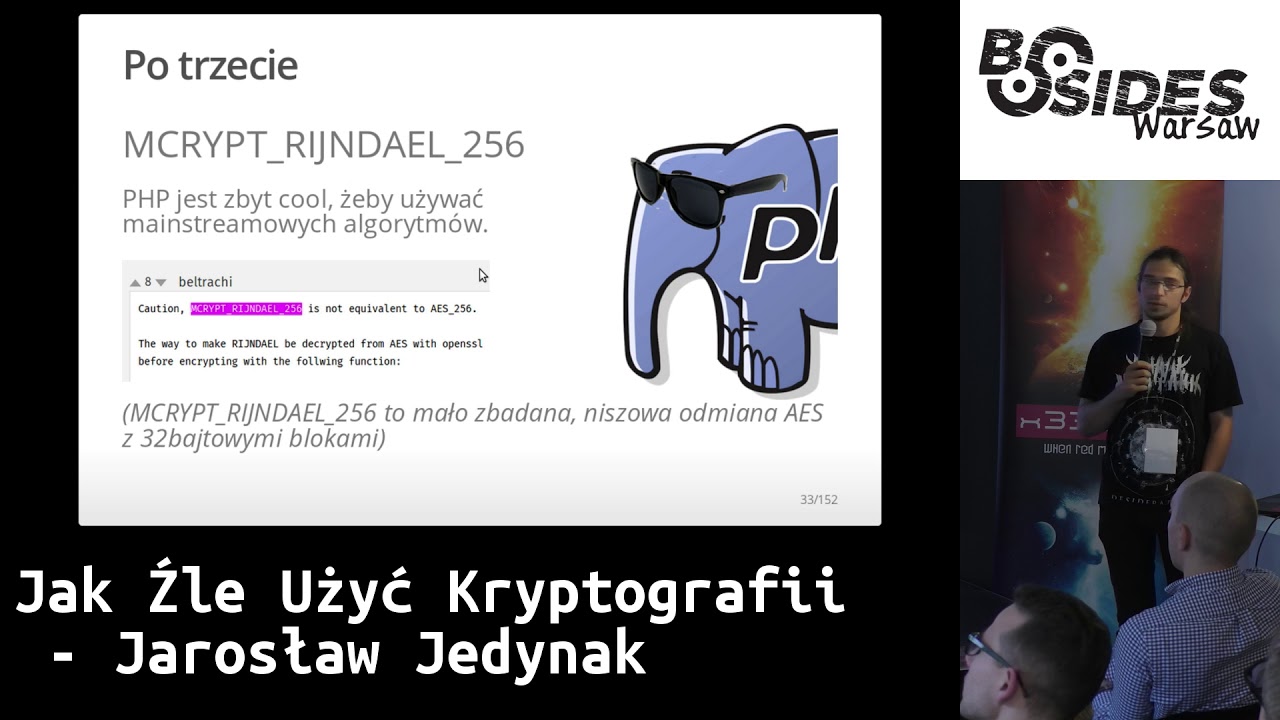
B64s decrypted? In practical encryption algorithms, because these are the most interesting in my opinion, there are a lot of, maybe not errors, but if you use them wrong, you can break them. You have to be very careful when you use things like RSA/AS. It seems that if I use RSA 4000 bits, no one will break them. And in practice, you can generate a key wrong, you can make a lot of mistakes. And here are some examples. You can use RSA wrong, use AS wrong, you can use libraries, which does everything for us, but We give it some parameter and it will do something that it wouldn't do what we would like it to do. You
can implement some algorithm by itself and completely ruin the whole idea. Here is an example of several selected RSA attacks. I won't discuss them because it would take us three times as much time. But these are all examples of attacks when someone used RSA but did something wrong. For example, he generated the key wrong, used the same modules a few times, Or you can do a fault attack, where in a private key someone is transmitting cosmic radiation, flipping bits, and thanks to that you can get back. These are really crazy things. Timing attacks, so many things. What do we need for crypto? This is a category that basically requires nothing, no tools, no need to
pay anything. You don't need to pay anything for others, but here's one thing we need for a paper card and Python. And that's Google. To find papers with such attacks, we found that someone actually wrote something and we need to implement it. Generally, it's not bad that we get a task and we're wondering how to solve it. And 90% of the time we spend in Google searching for something, some description of something, some liability. And in crypto it's even more visible, because it's not even 90%, but 98%. - Besides, you have to write what you've found. - Sometimes it's not easy. - Sometimes it takes time to make it. - Mathsians write papers with a lot of weird characters, and then they don't publish the code
they used. And... have fun. But you can, you can. It's not pleasant, but sometimes someone will put such code on GitHub. Okay, what now? This is one of the categories we don't like and we won't talk much about it. We apologize to our team mates who may be watching and feeling a bit offended. In any case, typical investigative informatics, we get a pick-up or a disc image and we have to look for the needle in the haystack. Yes, but this is a theory because investigative informatics usually know what to do, and sometimes creators do such strange things that they think they hide data somewhere Search for needles in haystack. Yes, I get 300 MB of pick-up and search for it. Of course there are programs that make
it easier. For example, Wireshark. The first thing we do after picking up pick-up is to run Wireshark and make file export object, so we know who is collecting HDD. Sometimes it helps, sometimes not. Sometimes you have more luck, sometimes less luck. We don't like steganography in this category either. Steganography is hiding something in something. For example, hiding some text in graphic files, video files, audio files. Generally, we don't like tasks in which you have to guess, you have to try to guess what the author might have meant. In steganography, it often looks like this. There is a program called StackSolve, you can load graphic files to it and it allows you to do some operations that
can sometimes help to solve such a task. Sometimes the tasks are so stupid that it is enough to load such files and immediately see the flag. There is also a steganography of formats where in fact These tasks are not the worst, because we get a file and we have to get to know it well enough that only after learning the specification and seeing what each byte in this file is responsible for, we get an idea of what to do. And for example, GenVal likes to do such tasks and they are really cool. Here, for example, you can see the type of task in which the program is running, TPS_Audacity, and you can see the flag immediately. We need to guess how to use a spectrogram to look
at it. If we use something else to analyze it, we won't find anything. Beautiful, right? A few tools, of course, Python. And there's also the category of so-called "misc", which are tasks that don't fit anything else. It's a half-category, because everything is added to it: soap, toilet, etc. And what can be in such a "misc"? For example, recons, which are We find out that the CETF organizer was in Georgia 3 years ago and bought a figurine. What kind of figurine was it? If we find this figurine, we'll get a flag. And it turns out that 2 weeks ago, in your GitHub, in a community, there was some information, some link, and you walk on a string. We don't like these
tasks very much, so we won't talk about them any more. There's also trivia, so here's an example. Quiz. We don't like them either, but they are simple. Usually it's just 5 minutes of googling. An interesting type of task is hardware. Very often, hardware tasks are based on getting Authors implement a task on a certain system and make a photo of it. You have to trace several photos, for example, where some cables are disconnected. There were a few such tasks and a colleague later sent us a photo that he had to write everything down on a piece of paper. Are there any tasks that use some strange esoteric programming languages? For example, we once had a very strange text and we found out
that it was a programming language. Our teammate from the team decided that we should reverse the language and started writing our own interpreter and guessing what the operators would do. Later it turned out that it was an existing language and we found the interpreter of this language on GitHub and we would have a flag. There are also tasks that cannot be classified at all and tasks that couldn't be thought of in a sober way or without eating mushrooms. That's the task I'm planning to describe now. It was on HitCon recently. The task was simple: you have to write a regex that will match various things. It started with regex matching the text that contains select. So it was a bit of a wav. The answer was
simple. It's probably a bit too low for people to see it from the back. But it was okay. Unfortunately, there was also a second level. We had to match regex with something like this. I found out that such a thing is impossible in language and automation lectures, but it turns out that Rabim and Regex are not really expressive and global, but they have a lot more possibilities. So I googled, I found something, it worked. And now I had to write Regex that will be massing the letters that are the length of the first number. I don't know if I'll ever need to write such a Regex in my work, which searches for letters that are the length of the first number, but I don't know, I like such regexes
in Taiwan. But it wasn't the end. Later, you had to match the letters with palindromes. And then the letters with three letters that repeat the same length. And then only the years of the year. For example, if you wanted to validate that users who have been here in the previous year can't register, such regex would be useful. And so we finally reached the regex that matched the size of 42 and at this point we were almost out of the game. You should have regex, it takes almost a year to get there. We would have copied it, I've seen it. It's a lot longer. Yes, it has a few hundred kilobytes. And it's still in Perl,
and we would have to write it to Rabia. But the first task was to get the number of the links. Yes, exactly. So when we had the rules, we would sit and remove every single sign. We removed unnecessary attachments, we made up... No, we don't want such tasks. I didn't fight for such tasks. So, to sum up... Regexs are not very cool, but in CETEFs it's cool that you can learn things that you would never normally try. I don't know, for example, I don't suspect that you can do such a miracle with regexs. I don't know if they wanted to know, but if someone asks me about it at a qualifier talk, I'll know. There is also the PPC category, which we don't know if we like
it, but we are better at it than other teams, because we have a bit of a programming bug, so it will work. We go ahead. This is a summary of Professional Programming Competition and generally these are tasks from the IT Olympics. For example, you have to multiply the numbers of the math problems so that it is fast. But it's a bit boring. I did something like this at university and I would like to do something else at CTF. Sometimes it's different. For example, we write solvers to games or bots that are supposed to win with other bots. Or we have to solve CAPTCHA. -Captcha solution is a type of task that many CTFs have such
sentences. There are a thousand captchas to solve and you have to solve them. And there were so many of them that we wrote "fairamorg" to which we only modified the part responsible for the recognition of the characters. -Even when we were doing CTFs, we made such sentences because it was fashionable then. Unfortunately, it turned out that at least two people did this task so that they sat and wrote these thousand captchas manually. It wasn't supposed to be like that. There were three stages of our task. There were 300 CAPTCHAs to enter, 500 and 1000. And in fact, at least two people entered these 1000 CAPTCHAs manually. Yes. Or sometimes you have to do some game
logic, like a pseudocode or a nonogram. Nonograms are such strange things where you enter colors, squares in black. We could put a picture in it, because it's appropriate. And then the QR codes came out of it. It also had to be done there, a few dozen or a few hundred. Tools are Python and C. If someone does too many tasks, someone changes their mind, like in this picture. So we rotate during these tasks. But they are not so bad, because other hacker teams are usually even worse than us. So we move forward. You have? Exactly. There are good and bad tasks. CTFs, which have more bad tasks, are bad CTFs. Indian, Hindu. And someone came up with
a way to do it, I think we even know who, probably a Russian, a Ukrainian, and created a portal called CTFTime.org and it has both CTF rankings and team rankings. And of course it's related, because if a team with a good CTF takes a high spot, they get more points. The first screenshot with the teams will be posted soon. It's worth mentioning that there are many CTFs in a year. We're now in a situation where sometimes there are 3-4 CTFs in one weekend and we have to choose which one we want to play because we don't have the resources to play everything. But there is the most important CTF all year long, it's called Defcon. Defcon is a type of CTF attack-defense. Everyone has
to go to Las Vegas and play. The CTF formula changes a bit, because this year, for the first time, before Defcon, there were fights between the programs that were supposed to automatically search for the vulnerability. You had to write a robot that plays in CTF. And it turned out that you can do something with it. And the reward in this in this challenge, making a bot like that was a lot of money, because it was a million dollars. And then the bot that won, played with the players on the devcon. And it turned out, very interestingly, that this bot didn't do it's job as well, because it was probably the last place. I think it was the last. The
last. But on the other hand, it didn't do it's job as well, as some people from Dragon Sector suspected, that he didn't do any tasks. For some time, he was 3rd or 4th place from the end. So he did something there, he was better than some really good hacker teams, that were sorting. So maybe someday, not now, they will do something. Yes, and the most important Polish CTF is held during Confidence in Kraków and Dragon Sector is the one that does CTF. Has anyone played Confidence before? Great. There are different types of teams, of course depending on who plays in them. We are a team of typically internet friends, but there are also teams of university students, and for example in Poland VAT has its
own team, or it had? It had. Interestingly, more and more CTF teams appear, which come from companies. And it's not just about the fact that the employees of a given company know each other and as friends they make a team, but simply the head of the company assumes that it would be nice to play in CTF. And we even have one such company in Warsaw. Two, three, two. Three at least. This is a screenshot from CTF Time, the best Polish teams at the moment. And of course, at the forefront of this event is Dragon Sector. Maciek had a presentation from this band yesterday. What else do we want to say? Maybe there is someone from the band in the audience? There is, but... I mean, not from our
band. Do you want to call people? No, no, no. No exaggeration. There are a lot of bands here, and they are actually corporate bands. We can't say which bands are from which companies, because they don't boast, but more than half? Maybe not more than half. I know about 5. Anyway, there were very few of these teams 2-3 years ago, because only 2-3 teams were active. Every year there are more of these teams, I hope there will be more, because it's really great fun. We also made our own CTF, which took place at the end of 2015. It was a different CTF, not a team one, but an individual one. We wanted to invite people who had never played
it before. It turned out that a few people, or even a dozen, who took part in the CTF, founded their own team. And we took the best guy with us. Greetings, Adam. Unfortunately, I lost the source files of the CTF, so it's gone now, and I had to steal a screenshot for the game. I hope I'll find it. And this is how offline CTF looks like. Of course, most of CTFs are online, you can play, enter your address, viewers, and that's it. But there are also offline CTFs, where a large group of people gathers, unfolds their laptops and plays. And this is, for example, Insomniahacks this year in Geneva, Switzerland, where we also had the pleasure to be. We were probably in fifth
place. Dragon Sector took first place. Yes. They're even... They're sitting here. They're sitting here. Yes. Now we would like to give some tips on how someone who has never played TTF can start We have a few questions, we will prepare them and we will answer them ourselves. We will start with the simple ones: is it legal? If someone asks how to start with security, then it seems that CTFs are one of the best options, because we don't hack people who don't want us to hack them, but vice versa. People prepare tasks that are not legal. and we're breaking it somehow. So, what's more, is it legal? It's a strange attitude, that a lot of people, when they think about CTFs, say
that they started in CTFs, but they have to learn more. And it's pointless, because CTFs are there to learn. But it's worth playing. There are so many different categories, so many different types of tasks, that even if you can't do anything, or you can only do one of those things, everyone will find something for themselves, and there are so many possibilities of learning, and we'll repeat it many times, because
Exactly. You don't need to know anything. Sometimes when I ask someone to start playing in CTF, they tell me that they don't know yet, they need to learn something first and then they will play in CTF. No, no, it's the other way around. Jarek and I are originally programmers who qualified through CTF. Almost everything we know about security we learned during three years of playing in CTF. We started with the game with the service craft and so on, but we learned a lot during the CTF because these are things that are specially created so that we can learn. Exactly. The game itself costs nothing, of course, compared to the computer and the Internet. If we make a lot of effort in CTFs to go somewhere and
play offline, then of course there are costs of some tickets or nightclubs. Sometimes there are offline qualifiers and offline finals. If we do well in qualifiers, the organizer can fund us a ticket or a hotel. But it's usually hard, because you have to be really good. Everyone starts then, because everyone wants free tickets, free holidays. Sometimes it even works out. And it turns out that from a certain time CTFs even have some awards, and even more and more, and these awards are getting bigger and bigger. For example, T-shirts. I have a T-shirt from CTF. We won a new CTF online from Brazil this year and we got T-shirts. But you can get money, but you can't earn it yet. If we
want to go somewhere, the costs are still higher. But it turns out that more and more sponsors, more and more companies are entering this world, so the rewards will be bigger. Practical tasks are not very practical, but skills that we use in such tasks are certainly useful in real work. You can start playing it yourself. Of course, CTF is mainly a team game and it is very nice to find a few people with whom we would like to do it together. This is a bit more difficult question. I think we are in the best place where each of you could find someone you would like to work with. It's hard to find motivation to do tasks. If there is another
person who motivates you to play further, it really helps. I recommend it. It doesn't even have to be someone who plays, you just assume that you want to learn something, so you do it. There are many categories, not everyone has to know everything in the sense that CTF starts, there are tasks, categories, so everyone takes a task that he likes the most and does it. And then, when we are in a team and we play seriously, that this person specializes in this category and I in that category. And it was even on the first slide, and on the second one, which categories Jarek and I like to do the most. You can start with any CTF. We go to CTF time, there is a calendar and we check that
in a week, or even on Monday and Wednesday, there will be an online CTF. But there is also something like PicoCTF, it's a CTF made by PPP, the best team in the world. It's a CTF for beginners, there are even special CTFs for high school students. And what is very cool about this PicoCTF is that it still works. Both the 2014 and 2015 editions are still online. So all you have to do is go to the website, create an account and start doing the tasks. And recently, Gynwal on its streams has just developed tasks from this PicoCTF. So if someone doesn't even want to just start doing tasks, they can go to YouTube, start Gynwal's
stream and then Gynwal will explain how to do these tasks, what the whole thinking process is like when doing tasks. I highly recommend it. Some teams, when they finish a task, or when they finish a CTF, they put in text descriptions of how they did it. This is called write-ups. We are one of those teams that tries to, or at least it used to be better, now it's a bit worse, to send all the descriptions of tasks we do publicly to GitHub. So you can get the link and read it. You can even do it simultaneously, that by downloading, for example, source files of some task, try to do it, if something does not work, then you can read what's next. And so it
turns out that we were programmers, we started doing CTFs and we learned something, and it would be nice if it turned out that someone else could pay us for it. And it actually worked and now we both work in CERT Poland. And in fact, the skills needed for CTFs are useful in the work of a security engineer or a security searcher. So we recommend it. Some people think a little worse about it. And this is a very interesting man who summarized it a little differently. I mean, I don't think he offended me at all. I like what I'm doing. That's true, I got a Multisport card, a NIDA license and a warm ear in CERT. And actually, doing analysis of bots and malware is not that bad. Taking botnets,
who would want to do that? Yes, even recently I went to Denver, because I have a job, they sent me to describe how they do analysis of some stupid bot. Cool. In a moment we're going to Japan for CTF, who would want to do that? As a delegation? Yes. And does anyone have any questions? Give me your microphone. Is CTF a Wargame with a time limit? Yes, you can sum it up like that, but in Wargame there are usually some levels one by one, and in CTF you have a list of tasks and you don't have to solve them in any order. But it's a very good association. Just like HackMe, CrackMe, etc. have something to do with the CTF area.
It's hard to say. I would recommend CTF, which is on the edge. CTFtime.org has a list of upcoming CTFs, so you can always register for CTF, log in and when there are only "re"s, you can leave. But honestly, there will always be some 1, 2, 3 webs. Sometimes there are more of them, sometimes less than in reverse engineering. There are also webs for CTOs. Yes, sometimes it's not like most of the tasks are for programmers. No, it's the other way around. When we were in the CDF team, it turned out that programmers are a minority. All the people in top teams work as security engineers, as security guards, and so on. And even in our team, the number of programmers was
higher compared to security engineers. Now, when we moved on, it's different. But it's definitely not an obstacle to be a programmer. It helps a lot, but It gave us a bit of an advantage at the beginning, because we were programmers, and the tasks that people who didn't program were not so good at. We had a slight advantage. But then it turned out that we needed a lot of security knowledge for the tasks. We were very far behind, so we were mainly learning security, and we were somehow able to program. But it's best to be able to program. Anyone else? Are there any CTFs or hackmifs where you have to get up from the computer and go somewhere and do something?
Sometimes you can jump into the toilet. I was thinking about that a little bit. I'm wondering. There are offline CTFs where the exit is not part of the task. But where do you want to go? Aha, that's it. Okay, maybe not. But on some offline CTFs there are offline tasks. You have to physically approach something, for example, some device and do something with it. And in fact... Yes, and on Confidential... Yes, last year we had a printer, and last year we had a vodka machine. We had to shake it. And when we did, we poured vodka. For free. Or for example on DEFCON, we had this kind of sentences. But going out of the house... Who would want to go out of
the house? Anyone else? How many CTFs per year? Hmm... There are more CTFs than we would need to do to get them. So... Maybe it's like this. With our current skill level, to be so high in the ranking, we have to do CTFs almost every week. But of course... When are they? I don't think that playing CTFs is... I don't know... The key to good fun is to be high in the ranking. Maybe some of you are thinking about it, but you can do CTF without spending any time on it every weekend. We also have 8 of us, so if 2 people want to go on a weekend and they start, and 6 are on
caribou and drinking, then we start, but it's not our full strength. So we start as a whole, it's rare. Maybe once a month? Twice? I have a specialization, I have a specialization for the team. Do we have specialization in team? Yes, we have very strong specialization. When I was only with Mateusz, it was weaker, because we had to do what it is. But now everyone takes the tasks as they want, as they like. You can say that each has more or less three categories in which he feels good and how are the tasks from these categories. He takes them. Such tasks for 100 probably everyone would do but such difficult tasks you have to specialize
in it. Yes, and this team-building also consists of the fact that at the very beginning each person takes one sentence and does it, but then if there are difficult sentences we start to sit together on these tasks and even the whole team can sit on one task. We actually sit on a chat of 10 people and sit on one task, even though it's not a specialization of all people. Anyone else? In fact, if someone really wanted to, we would probably accept it, but we wouldn't look for it. Recently we've had two people, but not a year ago. We don't want to be a mass of people, we want to take everyone as they come. Maybe we would be a few places higher
in the ranking. Well, not a few, but a few places higher in the ranking. But the whole fun is that everyone can show up and do a few tasks. In my opinion, if someone wants to play and start, it's better to start your own team and then you can learn together with people who start like them. At the beginning it's nice when there are a lot of tasks that I can do and I'm on my level, and not that everyone will do simple tasks and then I don't know, I sit like this and do nothing on this CTF. We definitely don't regret that we set up our own team instead of joining some other one.
That was our last warning. Five minutes, but... Five more minutes. But there are no more questions. If anyone has a question for less than five minutes, we'll take it. Yes, or maybe our contacts... Or we won't run away from here. We're even on Twitter, so we won't run away, so we can come and talk. Okay, thank you.