Exploiting Citrix Vulnerabilities: Web Shells & Deep Dives #shorts
Show transcript [en]
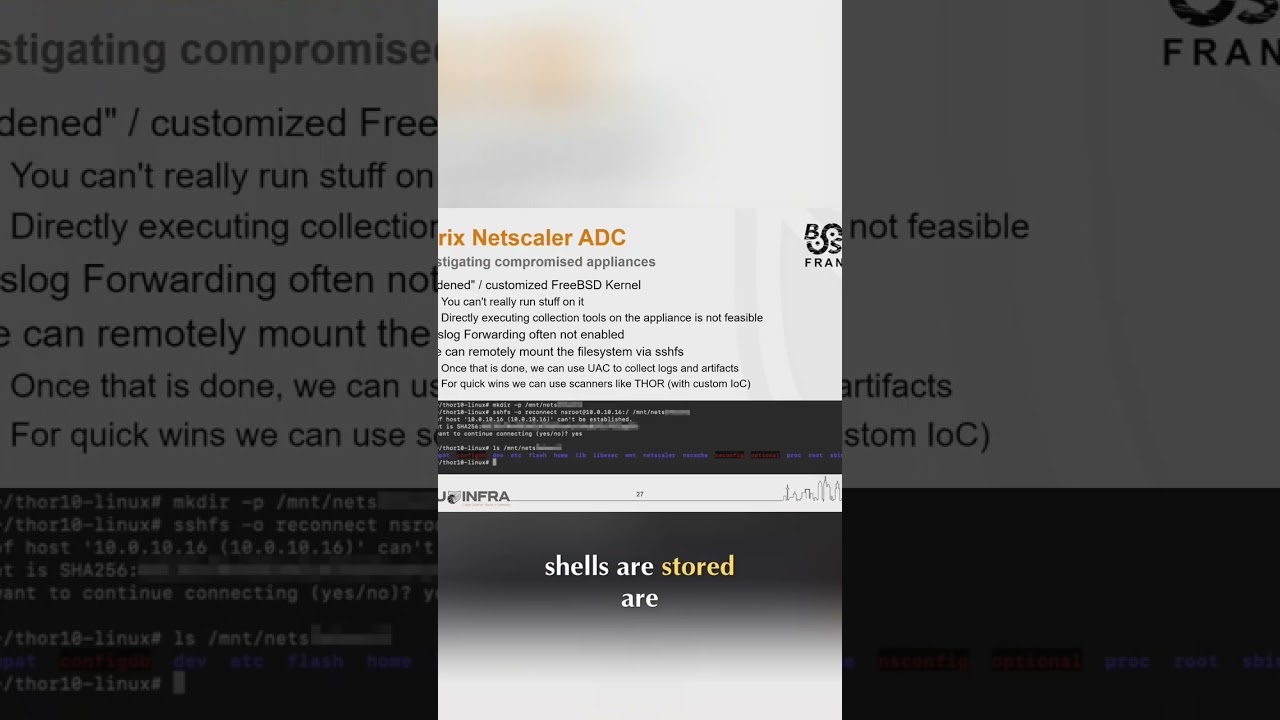
Now, as we can't really run stuff on it, we need to use another machine, then use SHFS and basically remotely mount this appliance to another analysis machine. And then we can do something like using four or four live for some quick wins because we're looking for web shells. And basically the directories where those webshells are stored are mostly the same. So we know it and we can [snorts] just look there. Or else if we want to do a deep dive, we can do a UAC image. So Unix artifact collector and look at the logs and artifacts to get a bit more insights when where happened what and what can you do and basically if you do not patch in time what do you
get you get web shell number one web shell number two web shell number three web shell number four and as I said at the beginning we had four C vulnerabilities This





