Your Intrusion Detection Still Sucks (And What to Do About It)
Show transcript [en]
So, um, if you want to use Slido, scan that now, please. If you want to give feedback about how my talk rolled you to sleep, uh, please feel free to, uh, scan the one on the right and give me feedback as well. I'd love to have it. Can everybody hear me? Okay. All right. Cool. I can't see anything. So, all right. That's cool. Cool. So, thank you, Jason, for stealing my spiel. Appreciate that. Yeah. Sorry. Now, we have Jason today talking about your intrusion still sucks. and maybe he'll also tell us what to do about it. Yeah, hopefully hopefully there'll be some of that. Uh, as Jason mentioned, all question Q&A will be vis www besides
sf.org/q&a uh there will be no word and that uh there will be no uh verbal question answers so we'll just be doing. So with that Jason appreciate it. Hello everyone. I am shocked to see this many people here given that it's happy hour soonish. So maybe maybe uh 50% of you will leave in 15 minutes. We'll see. So um for those of you who don't have the pleasure of knowing me, like I ran a lot and I talk a lot of trash and I think that's why William's here just for dank memes and and talking trash. But you know, know your audience. So here we are. So um in 2023 I gave a talk titled
Lapsis is winning and I put forward a thesis. They were all getting our butts kicked by a bunch of neo-Nazi teenagers and I was like, "Please tell me I'm wrong." Nobody was able to do that, sadly. Um, they're less winning these days, mostly because they're getting rolled up, but uh, they're still very effective when they choose to be. Uh, in 2018, I gave a talk in the IMAX theater where I did not successfully troll anybody uh, with the screen size on Mac OS supply chain compromise. And uh we introduced some techniques and some telemetry using Santa open BSM audit framework and a bunch of other stuff to like beat Patrick Wle to a blog post.
That was the actual goal for the talk was like if you do this you will beat Patrick Wle to a blog post about OD Mac OS malware. Please do that and it was in the context of CC cleaner. in uh 2017 uh gave a talk called effective intrusion detection at the b or excuse me at the DNA lounge and uh some of the things that are incorporated in this talk are like evolutions of all the those talks plus also one from a former colleague uh this guy who goes by four his name is John Flynn uh he gave a talk in 2012 at black hat titled intrusion detection along with killchain now you have to put
a trademark by that because it's trademarked by locked Martin and the the synopsis was like why your detection system sucks and what to do about it. Very similar like Genesis, but this is an evolution of all those things over time. Cool. So, who am I? Who cares? I'm Jason Craig. That's my handle. At least the one I want you to know about. I'm kind of that everywhere. If you want to ping me on like Blue Sky or LinkedIn or Gmail, you can use that. Send me malware. Please. Um, I I am currently uh I've been at this company called Remittly uh for about two and a half years. I'm director for detection response. One colleague.
Thank you for showing up. We're a Seattle based company. So there's only like six of us in the bay. Anyways, so I lead our detection response or uh Remittly is a consumer to consumer international uh financial transfer platform. So chances are if you're an immigrant to the US, you like 100% know of us and like 50% use us. If you're like native born in the US and you don't like send money abroad, you probably haven't. So anyways, we're hiring. uh holler at me after if you want to talk about that. Um except for this guy. Um so uh my background is in a lot of things in the last 20ish years, a little more than 20 years. Uh I've done a lot
of roles in security. Uh I focus mostly on intrusion detection, instant response, threat intelligence, offensive security, and like I'm a big proponent for Thront life. And if you don't like the way that sounds, I don't have anything to say for you. That's just the way it is. So some fun facts about me. Uh firstly, there's a new AP in town. Uh it's English- speakaking. It's a lot of people that look like me, but some that don't. Uh it's called Goth Typhoon. I'm an unnamed member of this new AP. One day you'll find out about it or not. We'll see. So, uh speaking of ghosts, my actual favorite AP besides Goth Typhoon is one called Wild Neutron. Does anybody
know that name? Sad face. Know your lore. Know your lore. Uh, so speaking of ghosts, um, my favorite CVE, I was asked in a job interview what my favorite CVE was by a very serious person. I thought it was hilarious and I responded to him immediately. CV 2011 0322 and he was like, "That was fast." And I was like, "Yeah, cuz I worked that. It sucked." And if you know about this one, you know about it. That's all I'll say. That's my favorite CV ever. Um, so some shout outs to people. Uh, besides SF, first of all, thank you volunteers. Thank you sponsors. Thank you speakers. Thank you attendees. Uh let's not forget Besides SF is a for us by us nonprofit
community information security conference. Uh so let's take a poll. Um who was here last year? I can't see anything. So like holler. Cool. Cool. Who is here at the DNA lounge for any year? Okay. Who is here at besides one besides me? Cool. Yeah. Yeah. At the at that little co-working space. So yeah, uh I encourage you to volunteer when you have the opportunity to because I met a lot of really wonderful people that year volunteering at Besides one. So anyways, um uh I just encourage you to to like volunteer when you can. It's super helpful and you get to know a lot of great people. Um so also shout out to the Thor Collective. If you don't know
about Thor Collective and you're in the DNR space, you really should. uh Lauren Sydney and a bunch of other hooligans like they published some really fantastic uh research and some thought leadership in like the serious sense and you should check it out. Also um I won't talk about it a lot in this talk but Haley Mills gave this great talk called magnets for needles and hastacks and it's what you think it is. It's about building risk-based learning as a technique and a concept and it's super impactive impactful and super effective and I encourage you to check out her talk. Um, if you have not heard of it and you want to find magnets for needles
and haststacks and also like Thornconfam, they're uh they're the best. If you don't know them, ask around and my colleagues who just again I feel bad for every day, especially Adrian. Um, so so what problem are we here to talk about? Uh, do you struggle with false positives? Yes, you do. Do you struggle with false negatives? Yes, but you don't know about it. Yeah, exactly. Exactly. How do you know? I know unknowns. Um, so false negatives are challenging and false negatives are like an afteraction KPI you can try to figure out. But if you're not thinking about false negatives and you work in the detection space, you really should think about it harder. Um, similarly, do
you long for meaningful effective alerts? I do. I think about this every day. Uh it really is tiresome, but I can't stop. So, uh I'm emphasizing effective for a reason. Like, you need to figure out what effective means for your organization. And if you're just thinking about like, oh, I just have alerts, like that's not the way to do things. Uh do you have too much spare time as a DNR team? Like, so much spare time, right? So few alerts, nothing going on. And I guarantee you your alerting pipeline broke if you have no alerts. So which you're probably not monitoring either. So how do we detect and respond to threats? Seriously, that's the problem.
How do we detect and respond to threats quickly and effectively? So this is the crux of DNR. Your job as a DNR practitioner, as a team, as a program is to find, detect, and contain threats as quickly as possible so that your thing, your incident, your investigation doesn't become a b- word. like your job is to avoid the b- word at all costs. That's breach in case you didn't catch up there. Um, so how can we scale without like a lot more meatags? Meatags are expensive and they're hard to come by. Takes a long time to hire walkoffite engineers. Let's say you go from like a 100,000 compute nodes to a million compute nodes. Like you should not be
10xing your team. You should figure out how to scale. You figure out how to apply engineering principles and better analytics. Cool. So uh anyways, back to my premise. Your intrusion detection still sucks. I mean like like not yours because yours is yours is fire but like hours not so great right so let's talk about some data so luckily for me uh DBI dropped this week so N trends has anybody read it awesome distinct minority not sexy not like super interesting hot reading but like super needful right so I sourced this data from this week's uh two reports uh munched together so for a b- word for breach. The estimated median dwell time for an attacker in the
environment was 10 to 15 days 1 0 to5. So that's better than prior years as a KPI, but like you're still kind of failing at your job of detecting and eradicating threats effectively. So internal detection dwell time. This is when the internal something, whether that's an engineer noticing like a GPU spiking too high or whether your AWS bill goes up crazy or like your stuff just stops working or your DNR team actually catches up finally. 6 to 7 days. Not a good metric. External detection 12 time. This is somebody outside telling you you're wrecked. 20 days. This varies by region and org size. So it's approximately 20 days. Uh, and according to DBIR, which sources
this differently than MTRS, um, 50% of breaches are reported by external entities to the breach entity. So that's that's pretty sad, right? So, uh, here's how I think about intrusion detection. Um, intrusion detection is approximately like almost 20% like known good stuff, right? You're like, "Oh, that popped. I know that's fine. Ignore that." Well, you got to automate that and implement it in code. Uh, 0.1% is like known and evil, right? like you got to go do IR, you got to go figure out lateral movement, attacker objectives, like how to do eradication, coordinated eviction, etc., etc. And 80% is like I don't know, like it's interesting. It's kind of sus, but like I don't it's not obviously
evil, it's not obviously good. So what do we do? So like 80% of our job as detection people is the work phase. Like figuring out how to apply work to that 80% corpus. Now for those of you I know there's a lot of hot talk about AI. Like I'm kind of an early adopter actually, but like if you're afraid for your job, just go look at this slide on the right. I ran that query Thursday. And if you don't see it, I'm not going to point it out to you because you'll see it eventually. Math also color I don't know how much I heated the earth to run this query, but it was sad. And I did a similar one with the other
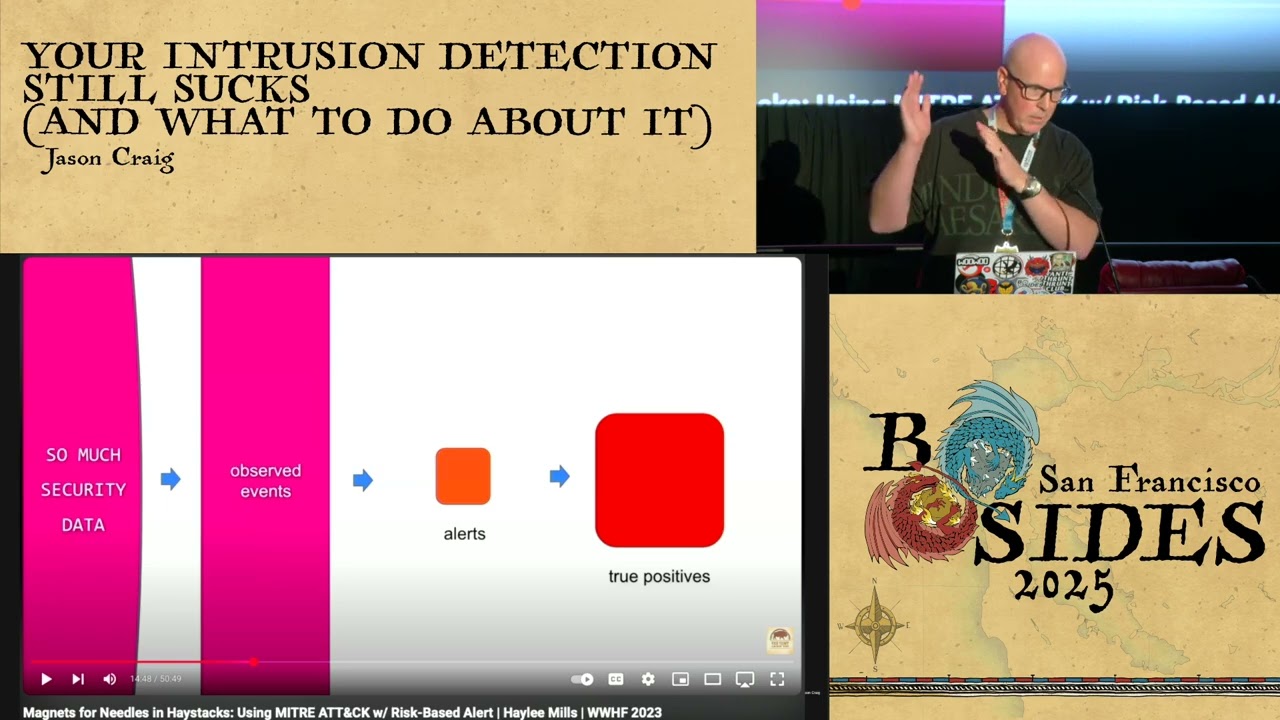
AI platform that we have on the as an enterprise licensed AI platform. It didn't do any better. So don't worry about your job yet. Maybe 6 months. We'll see. So back to Haley Mills. Uh Haley's talk is great. This is a screen grab from YouTube obviously of like how she synthesizes like her way to find uh needles and hacks using magnets, right? So you got data, data becomes observed events, those events become alerts, and then those become hopefully true positives, and that's sort of her thesis for how to apply a magnet to getting uh the mag getting needles out of haststacks. So we'll talk about that a little bit more. So I have some basic
assumptions here. Number one, you have tools. This is not like introductory level like you need to have a SIM. Here's how you get your EDR logged into a SIM. Like you need to have those already. Uh you need to know them as well. you you have to have uh capabilities to do analytics on this data. Um whether it's logs, normalized data in a sim, whether that's you know an S3 bucket or like a dumpster, you put your data somewhere, whatever that may be, you have to act on it using analytics. You also need automation. Uh you need some capability or capacity to do automation. You also have a detectionist code lifestyle. And if you don't, uh it's a great lifestyle. I
encourage you to try it out. It's been very rewarding for those who have enjoyed it. Uh and if you don't have a detectionist code life, uh this talk is not for you. So sorry. Um you also in addition to doing detectionist code, uh you need to have a structured protocol for interacting with everything. You need a protocol for interacting with your data that's in your dumpster and doing analytics. You need a protocol to say like here's how we interact with these other exogenous things like Slack, Jira, uh Pager Duty, like a big red emergency power off button, whatever that may be. Um, so you have a structured protocol for doing those things and it's standardized and like
normative for a team. They know how to use it. Uh, you also need a defensible posture. It's not related to DNR, but it kind of is. Uh, your defensible posture should be a couple of things like if you're not living the 502 web end life, like good luck. You're going to have a bad time. You need that as your default and it has to be enforced. And uh, if you don't have that, you should really get that. It's probably one of the most valuable things you can do as a security organization. Um anyways uh note I didn't say pass key pass keys I have I have feels about enterprise pass keys don't don't do that
uh zero trusty thing for device health attestation this can be zu Arman's here he built it talked about it uh at Pinterest it's a certificate based uh IDP whatever you got for zero trust you got to have a thing needserts needs to make decisions it's got to work uh so base analytic techniques I had no idea why I'm running out of time so quickly but that's all right based analytic techniques um you need to build context, you need to decorate your data, you need to enrich your data, you need to do that in a way that's standardized and normalized across all the things you care to do analytics on top of. In addition to that, uh you need to be able
to crossorrelate data sources. So like if your SSO logs are there, like they need to be next to your EDR logs and whatever else kind of logs you have. Um and if you don't have those near each other, you need to be able to act across them. So you need you need a way to do cross correlation for those things and I think I described like the XDR vertical uh but you don't need XDR anything to actually do this as an analytic technique. You just need a way to performantly query things. So in addition to that you need a concept of computer profiles machine identities. These can be laptops they can be EC2 they can be Kates nodes they can be
containers they can be whatever you want. You need a concept of a computer profile and identity. In addition to that you need to have a concept of a user profile and identity. I am me. I do things in a way that's regular. I talked about this like almost 10 years ago now. Um it's a really really useful technique. Um and if you have a way to measure computers to themselves over time and to their cohorts over time um and similarly for users, it's a really powerful technique and you'll find things um that you can't find otherwise. So for example, like I have a home IP, it doesn't really change a whole lot. I have a mobile device that changes like
once every couple years probably. I have a user agent that's probably pretty sticky, especially if you work in an org that enforces Chrome or some other browser as standard. Like you are your UA and that will only change as you upgrade your browser over time typically. Um, and then like I said briefly a moment ago, you need the ability to do cohort analysis for all of these things. And then obviously you need to be able to pivot on that data. Cool. So I'm going to present this diagram to you and let you digest it for a second.
So going back to going back to Haley's uh Haley's flow from data into true positives. Uh you can see I'm obviously like ninja level at flow diagrams. It's a big skill I have. Please endorse me on LinkedIn for it. Um so events go into your analytic platform whatever that may be. And then from your analytic platform something happens on your data on your logs and you have an output from that. That output can be an alert, it can be an action, it can be a whole number of things, but you act on your data. You perform queries against it usually assuming it's all normalized, assuming it's, you know, sim compliant or whatever data model you choose to apply
to your data in your data dumpster that you're acting on. You you then get an alert out of that where you get an action. It can be one, it can be both, it can be either. So, uh, one one step is like, okay, I've done the analytic, there's nothing to worry about. So I just hit that as like we're good or it's a false positive. It's a known false positive and I know that because I have a key value store that says here's a known false positives drop if it's these things and then you just end. You're done. Um if it's not one of those known things, maybe go enrich your data, build context, decorate it, do crossorrelation
for your different data sources based on atomic output and then feed it back into your analytics platform. Do that pivoting I described and you can like rinse and repeat the cycle until you're done. uh where it's like we're good drop it we're fine known known case where we can ignore it or you need to take an action and that action could be like you got to go do IR now and that could be a number of things that can be like uh I want to pull forensic artifacts back from a host uh using automation I want to go uh take a running EC2 instance and park it in a graveyard that has no network access and
start running memory analysis tools and disc forensics tools on its uh disc volumes stuff like that. And at the end of that, when you're done doing your IR things, you say, "We're done." Um, or after further analysis, we know this is a good state. We're going to update our queries and our analytics to say we should tune this out in the future given these certain parameters. All right, so like that's all well and good. I don't think that's really useful. Uh, but there's a diagram and you're probably all confused now. So uh I'm going to walk you through a few examples that will hopefully enlighten uh some ways to build context and decoration on this
data and to do pivoting crosscorrelation. So everybody knows like there's a bunch of thread actors out there that uh do funny things uh as it relates to corporate ATO. Uh some are nations aids, some are again teenagers. But let's say you get a suspicious SSO login. Cool. So the login uh the the log event says hey uh here's a new login on a new device from a new location and a new IP for this user for JSON and it's from a sus IP um so like what do we do with that? So, so firstly, um, what makes it sus? You have to go look at some external data store. Unless your log tells you natively this is sus by being like a
toxit node or something else. Unless it's actually stamped in your data and you trust that data from whoever gives you those logs, you need to go enrich that. So, what is this IP? Um, why do I care about it? Is it interesting? Well, it turns out the new IP is a MoladvPN exit node. Now, I don't know about y'all, but like I know some people who are using Molvad in the last year and I don't want them touching my stuff. Uh, it turns out the IP is located in Germany and the meatag like I live in San Francisco. So, what's going on there? Well, it turns out was the O 502 or web au authenticated? Now, I asked this
question. It's sort of rhetorical if we come back to this is enforced globally. Um, why do I care about this? I care about it because it's non-fishable authentication. like we don't have passwords. Uh we only have hardware tokens or or hardware back biometrics with like a secure enclave um or some trusted execution environment or TPM. So if it's 502 that means uh that it's probably not an attacker. It's probably me because it's a hardware authenticator I have and is already registered with the service I'm authenticating to. So let's do some crossorrelation. The EDR agent on my device is coming from that same Mulvad IP. So now I know it's Jason C with a Ubi key on his corporate healthy managed
laptop and the EDR agent is on the same IP address. Not so interesting anymore. Not so sus anymore. And let's go further. Right. So the EDR logs show uh that the network connection to the SSO around the time I get this alert is from Chrome. It's from Chrome on my my Mac and it's derivative of the login TTY which tells you that uh it's not malware on my laptop running as me in some other mode remotely. That's super helpful and useful to know. So, um, the EDR logs also show that I downloaded and installed MulvadVPN and it was running at the time I did this. And I downloaded Mulvad like a week ago or whatever. So, uh, like a a show of,
uh, a show of voices. Who wants to get paid at 3 in the morning for this? Anybody? No. Seriously, like this could be existential or it could be fine. Like, does anybody want to say yes? I don't like I don't want to get paid for this ever. And if you just take like your SSO logs, this is you're going to get paged at three in the morning for this every single time. So, um, my position on this, again, it's, you know, adaptable to your corporate environment. Like, you should have a risk posture that makes sense for your organization. Um, there's no one rule fits all, but my recommendation would be that nobody should get woken up. The employee that
did this should probably get a Slackbot uh, ping to them. should maybe get a jury ticket assigned saying, "Hey, Meat Bag, did you really know you're violating the corporate policy by running this non-approved VPN service on your corporate laptop and CC their manager?" Like, that's all I'm going to do and I'm not going to get woken up and we'll track like remediation to that ticket over time, but like that's that's on them and like don't mess around. Um, and the idea is like the DNR team is not there to police unauthorized software. We're there to, you know, detect and contain and evict attackers. Cool. So hopefully that made that one use case that one use case hopefully made this a
little more clear. Um so let's talk about like another use case where you have a new admin added. Uh so like Jane uh Jane added JSON as a super admin to a service. Now first of all you'll note like this is a Dash admin account and like if you don't have Dash admin accounts in your life, you're also missing out. You should definitely try those. They're really a really good way to bifrocate your risk because you can apply differential controls and you shouldn't be reading your email at the same account that you're also administering like your SSO or your cloud control plane. Um, so let's also talk about HR data, right? So my automation platform has to be able to shell out to
say, hey HR platform, tell me something about these these people. Who are they? Where do they work? What do they do? What is their uh presently registered home address, for example? Um or you can do that on a cron. Uh you can have a key value store use as an input lookup against whatever query you're running. Um but you your your automation platform needs to be able to connect your HR store and then like hey maybe go look at jury tickets. Is there a jury ticket because surely there's a change management ticket for creating a new super admin in your organization. Thank you. And you can pivot off of that. Super useful data. And let's say take it
even a step further. Jane uh Jane doesn't live the gooey life. uh she's not about driving a mouse in her job. So she uses infrastructure as code. So Jane uh uses Terraform to manage our SSO and she also does that using GitHub because we use GitHub as part of our CI/CD workflows. So I can go contextualize this event to say hey is there uh is there a YAML file I can go look at? Is it in GitHub? Was it applied through infrastructure as code or was it applied through click ops? And then obviously um we can pivot on some other metadata for the event like the IP addresses for Jane and for Jason mostly just for Jane
because she's the one taking the action in this case. Look at EDR logs for Jane system. Uh and look at the SSO login and like sort of scrutinize that a little bit. So does anybody like want to get woken up for this one? Deafening silence. Cool. So nobody wants to get woken up for this either. I think I might have convinced you. We'll see. Um, so let's talk about a third example. Um, yeah, let's talk about a third example. You have some suspicious AWS findings. Uh, so you get a guard duty alert. The guard duty alerts like, "Hey, Dart service successfully logged into this RDS database. Uh, CEX astronomy blah blah blah in an unusual
way." Okay. Well, as you probably all know, like guard duty is not super useful unless you take the data and go do something with it. But I'm like, "All right, that's not helpful. So, let's go let's go look at this further." Um so you can look at the user you can look at the session token uh do some ARN mapping like uh in this case you can see if you do a little pivoting that JSON c-admin assume the dart assume the role dart service and JSON C admin is actually like the human that did this thing. So like again, who is he? Like what would you say it is they do here? Um and and again like based on who I am,
uh this is suspicious according to guard duty because I'm a manager and I go to meetings. I don't normally log into RDS instances, right? So uh but it's an RDS instance. It's assigned to my team. I can see it's in the right repo. Maybe the code I'm working on is in that repo. Also sus. Um, but anyways, like there's context here that's relevant to this being a false positive. So again, you can look at the IP address in in the AWS cloud trail data. It's the headquarters office IP. Uh maybe I'm sitting with my office colleagues uh once a quarter because I work from home. Uh troubleshooting an issue that we're trying to deploy like a new thing for
our engine, our our automation engine. Um and that's actually what happened in this case. And if you uh go even further on EDR data, you'll see it's like AWS CLI. Uh the parent proc is terminal because I like default and I don't customize things and it's also derivative of my login TTY. So you also may be able to find some GitHub activity related to this or even a Jira ticket uh if like the team is doing some stuff. Um so again like who wants to get woken up? Cool. Um so if we apply this uh to my favorite thread actor in the last few years lapsis um let's ignore for the sake of like ease that you know we don't
have web authentic but like let's say you're uh lapsis stands up uh a new instance uh to attack us and our threat intel team observes that there are some lookalike domains that are registered and they discover some URLs that are probably going to be used to fish us but it hasn't started yet. So their tip has a hook to us on DNR and their tip shovels out these indicators to us so that we can autodeploy blocks. Super effective. Like why would you want to get wrecked when you could like proactively block it? So and then also uh we're we're big proponents for canaries. Uh we have them everywhere. And uh you can put a canary on your SSO
login page for most SSOs. It's it's pretty pretty fantastic. you're not going to catch like you know a teams but you're going to catch this kind of stuff where people lazy web just clone your HTML so those get triggered too really useful um and again coming back to like device health if you have a manage healthy device and your agents are all running uh you stand a fighting chance that it's going to be really really hard for attackers to get malware on that endpoint steal your session cookies and then go import them somewhere else to replay so like what about sophisticated malware Sure. Sure. Like a team. A team, right? Like some of us have faced those
in our career. Back in my favorite AP. Um, so this would still catch them. Like let's assume the attacker has really good malware like this guy wrote one time that neutered out u EDR events from like a protobuff or something. And so your EDR was running in a managed healthy state, but they were just selectively pruning out themselves from their activity. So you couldn't see their activity. So let's say that happened. Crossorrelation and cohort analysis and decoration of these types of events would still catch that. Thank you. Cool. So now let's do response. Um so like the first use case back in 2011 2012 uh when Ford talked about this at black hat was about the
responder getting a very good payload of data in the responder package. So if you get paged, if you get an alert, like you want to have a rich amount of information as a responder and a detection engineering team has the burden of providing them good actionable information. Like the number one thing you should be thinking about when you're preparing a payload for an alert is like am I teeing up the responder to easily understand what's going on as best I can describe it and take a response action or make a decision not log into a tool. So that's really helpful. Uh you can network contain hosts like super easily. Uh you can rotate and disable accounts.
You can revoke sessions. You can uh revoke MFA if you really want to get crazy. Uh you can auto forensicate computers. You can do like auto actions on cloud accounts if you're like using infrastructure as service. You do all kinds of really interesting things there. You can also autopop populate IOPS or indicators of attack. Um so super super great there. Again, I talked about the use case where elapsis stands up new infrastructure and they get autoblocked. You can also auto ticket uh can auto slackbot, you can page your duty, you can email, do whatever you want. Um so again, how do we do this right? So you need a sim length thing for analytics. You need an automation
tooling and platform. Uh the sim thing can be whatever you want. I don't I don't have a favorite. You don't need a commercial thing, but it may be your choice. Uh automation tooling or platform. There are commercial vendors or you can DIY. Like back in 2017 at Dropbox, uh we just built our own. It was Python and MySQL. You just need a brain. Um you need these external and internal sources of enrichment, decoration, and context. Uh I don't know, like you can't really do that all yourself unless you're like maybe Google, I don't know, like or Facebook, like you just don't have your own data to feed yourself about external stuff. So you need some other external oracle
that can be like census, domain tools, URL scan, spur, whatever. I'm not uh I'm not recommending those to you. I'm just mentioning them. I'm I'm not uh not an endorsement, but they do exist and they're great. Um you need again detectionist code and a CI/CD pipeline life. You need a structured protocol and obviously you need a brain. So why does this work? Context decoration enrichment and crossorrelation takes isolated atomic events and turn those into actionable insights where you can actually do something. You can take an action or you can say this is a known false positive and move on with your life. So, uh that's all I got. Um thanks y'all. Appreciate it. I'm happy happy to
have any questions. All right. My time. Thank you, Jason. Uh I guess we have time for just one question. Who will be the one? I want to go with does your introsion suck too but you can answer that time you want. I mean I feel like I know me who maybe answer that ask that question. However uh regarding 502 and pass keys one what are your thoughts on pass keys and uh how do you work with your IDP to get to know that a particular o was 502 based? Sure. Uh so firstly like enterprise c pass keys uh are very stealable very very stealable they're super easy I'm a huge advocate for pass keys for consumers they're easy
and they work I'm not a proponent for pass keys for the enterprise uh most of them can be stolen from like let's say you have them in your Google account in your corporate Google Google workspace let's say none of you would ever do this but like maybe you backed up your personal iCloud because you allow that on your work laptop That never happens, right? I've never worked in an incident where somebody had to log into their personal iCloud for us. Um, so pass keys are bad and that's why they have a different threat model. You don't have to trust me. You can just say, "Let me apply a threat model to pass keys for the enterprise and let me apply a model
to UBI keys in 502 and web authen for the enterprise." And the second question is how do you know what's what? Well, your SSO has config options to enforce authentication policies based on authenticator types. All the major SSOs have this. Uh they all exist. They're all pretty robust and powerful and they all log. So I have a I have like a daily report. It's not an alert because I'm not stupid. I have a daily report that says like bad MFA things daily and like over time that's asmmptoic to zero which is how it should be. Now recall uh if you use some SSOs you can't ph or web a everything. So like Tableau for Mac for
instance like just says screw you guys I'm not doing that. Microsoft Office for Mac if you want to license it through and Microsoft 365 you can't do it. I don't know why they don't fix it because you you obviously know what those companies are doing for their own authentication because it doesn't work. All right. Thank you Jason. Yeah. Get out your own folks.





