Remote Code Execution: Investigating Appliance Exploits #shorts
About this talk
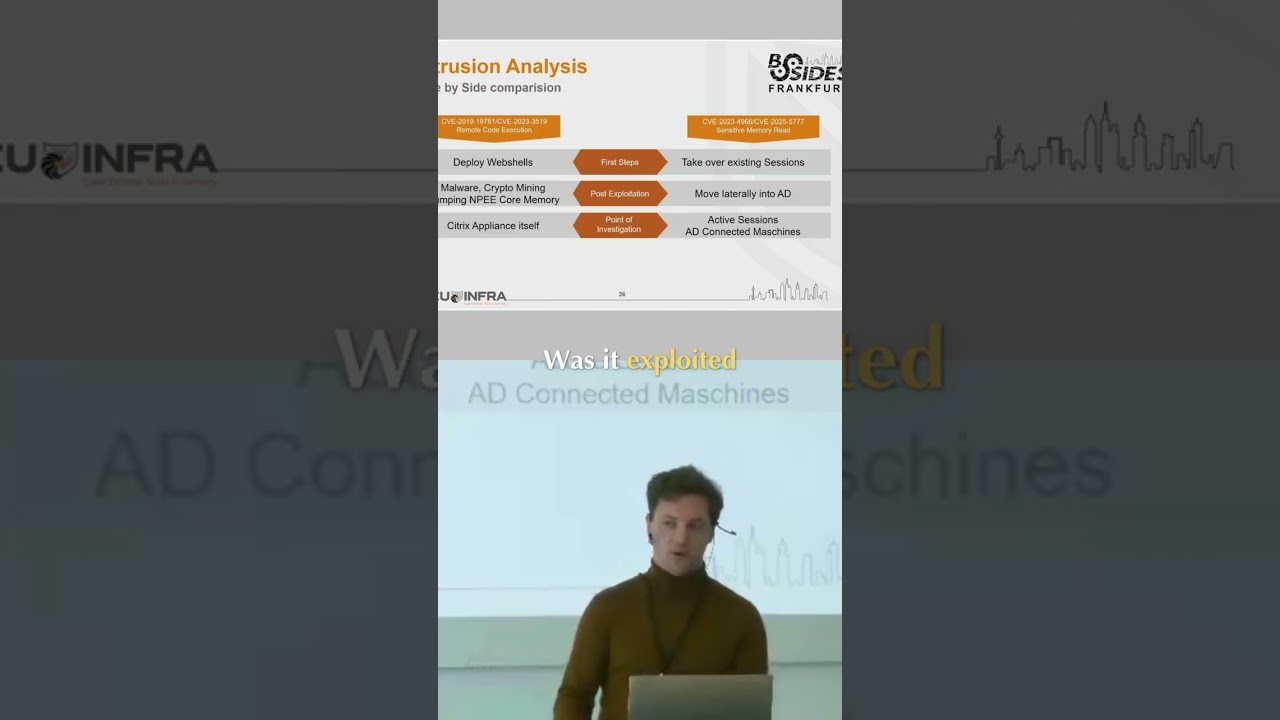
When remote code execution occurs, the focus shifts to the appliance. We must verify if it was attacked, exploited, or if the attacker has already moved on. Analyzing appliances is complex, requiring specialized techniques. #RemoteCodeExecution #Cybersecurity #ApplianceSecurity #Vulnerability
Show transcript [en]
If we look at the remote code execution, we obviously try to investigate on the appliance itself because we want to verify was it a tag, was it exploited, is the attacker still on appliance itself or has already dumped the memory and has gone further. So we have to focus on appliance and as we already saw analyzing appliance is not that easy. It's not that common. We need to pick up some tricks from our sleeves.





