Responsible Disclosure W Banku
Show transcript [en]
Hi, my name is Christian Szybisz, I work at Royal Bank of Scotland, now called National Westminster. I am responsible for several services, including Responsible Disclosure, pen tests and several others. Today I came to tell you how we implemented Responsible Disclosure in a large bank, which turned out to be not as simple as we thought. Maybe you will also tell me how to improve it. If you have any questions, the procedure is probably at the end. I suspect that we will take up to 30 minutes, so you will have half an hour of free time. I made this presentation on B-Sides, but it's on OWASP template. It's in English. I hope everyone understands. Great, that's what I was talking about. Agenda. But in fact, the caveat is the
most important. All the views presented here are my personal, not my employer's, nor other employees'. However, when I will speak, I will say that we did something, not me. Because it was me, it was Lead Pentester, it was a few other people who contributed to creating this process and going through the whole road of maturity. What we will talk about, how we created it, what rules we implemented, what we found. I don't think I have Drivers for Improvement on the slide, but I can answer if someone has it in the questions. Because it is still implemented, so not everyone can see it. Okay, does anyone know what is Responsible Disclosure or Bug Bounty? Does anyone know? Hands up. Ok, there is no such
person. Does anyone know what is responsible disclosure? Ok, it's like back bounty but without bounty. Easy? Easy. The point is that Most companies reach the bounty stage, when they pay for the item. It goes through various stages of development, and this is the intermediate stage. We decided to create a program, probably two years ago. and that it will help us find what our pen tests and other services have not found. We have a lot of pen tests, so probably the researchers will not find anything wrong with it. Why did this service seem important to us? Are you familiar with defense in depth? With such a concept, with such defensive layers? No. Okay. The point is that By combining many types of assets,
none of which is super, everyone has their own flaws, you can achieve a better level of security than if you didn't use them. Now we have vulnerability scanning. Who knows what the flaws are? Everyone knows, but no one will tell. Well, someone knows what the disadvantage is. The disadvantage is that it has a lot of false positives, right? If there is no engineer there, if it is a pure unverified scan. And the advantage? What is the advantage of free scans? Some market? Automation, that is, we want to test 50,000 servers a week, we do it on Friday afternoon. And how long would it take, for example, a pen test team? It would be necessary to
have 1000 athletes who will eat 1000 cutlets, and they would not do it on a Friday. But, on the other hand, pentesters have the advantage that they have a much narrower scope in a week. One system, one application will check much more accurately and find the gaps that the machine will not find. Fredhunting and redteaming are also directed a little differently. They also have certain advantages, but in fact they only complement I added Security Assessment for the sake of simplicity, because I was closer to it before. So, we wanted to introduce Responsible Disclosure, so what can we do first? We need to see how others do it and copy it. This is probably the easiest
way. If someone has done it wisely, you don't have to get too tired. We took a list of the top 50 banks in terms of asset management. There were no Polish banks there, mainly American, Chinese and a few British. We checked 50 and I had a strange feeling that none of them had a Disclosure or a Back Bounty. It's strange, because it seemed to me that when Google writes, when Facebook writes about it, when Allegro writes about it, everyone has backbounties. It's so obvious that our worldview is narrowed down to this narrow world. Meanwhile, we discovered that only 5 out of 50 of the 50 largest institutions of the type of bank have programs of the type of backbounty or responsible disclosure, from
which suspicion Three were Dutch and had very similar descriptions. So we have the impression that the regulator is ahead of the others, i.e. a Polish equivalent, a Dutch equivalent of KNF. He tells them that they must have it, so they all put it in. We also checked banks that were not in the top 50 and also had it. Dutch banks. Two American banks had such poor pages. Um... And now, some caveats about this. We don't know about private backbounts, so programs where a bank hires hackers, and doesn't tell anyone about it to maintain its reputation as a safe bank. We don't know about it and I reserve something that maybe Google Translate has misinterpreted the Chinese banks' side, which is also possible, and
they can have backbounts, but we don't know about it. And there were a few of them in the top 50. Now, the approach. When we thought about what we would do with it. To be honest, building such a process in a large financial institution is like building any other process. It carries with it only a greater layer of risk, which needs to be properly handled. We had to talk to business owners, who will be in this program, with communications, i.e. with people responsible for communication with the public, because in such a large financial institution there is such a communication department. The same goes for legal department, because they also wanted to make sure that what we
have come up with is in accordance with the agreements we have at the moment and that the jurisdiction we will announce it in will be legal and will not cause any trouble. What else did we wonder about? Bullet number three: should we start with the process right away or maybe try to start doing it somehow? and then write down the process. Depending on how the institution has grown and the senior management requirements, you can do these different approaches. The first approach had the advantage that when we came up with it, we came up with a few things that didn't work out as well. So, before we formalized it, before we gave it all the descriptions and the framework that are needed in a large institution, we improved many aspects
and we still do it to this day. What else did we think about? Did we have a dedicated team to handle it or a virtual one? In our case, we thought that no one would write to us. However, the amount of actions needed to run such a process normally, to receive an application, to check if it is not malware sent to us by this channel, to check that it is indeed a finding, to check if it is, for example, Are there any other findings besides this one? We need to think if this finding can be replicated with our knowledge, because we have much more knowledge about our infrastructure, whether its instances are different and also to be found somewhere else. All this requires at least one person
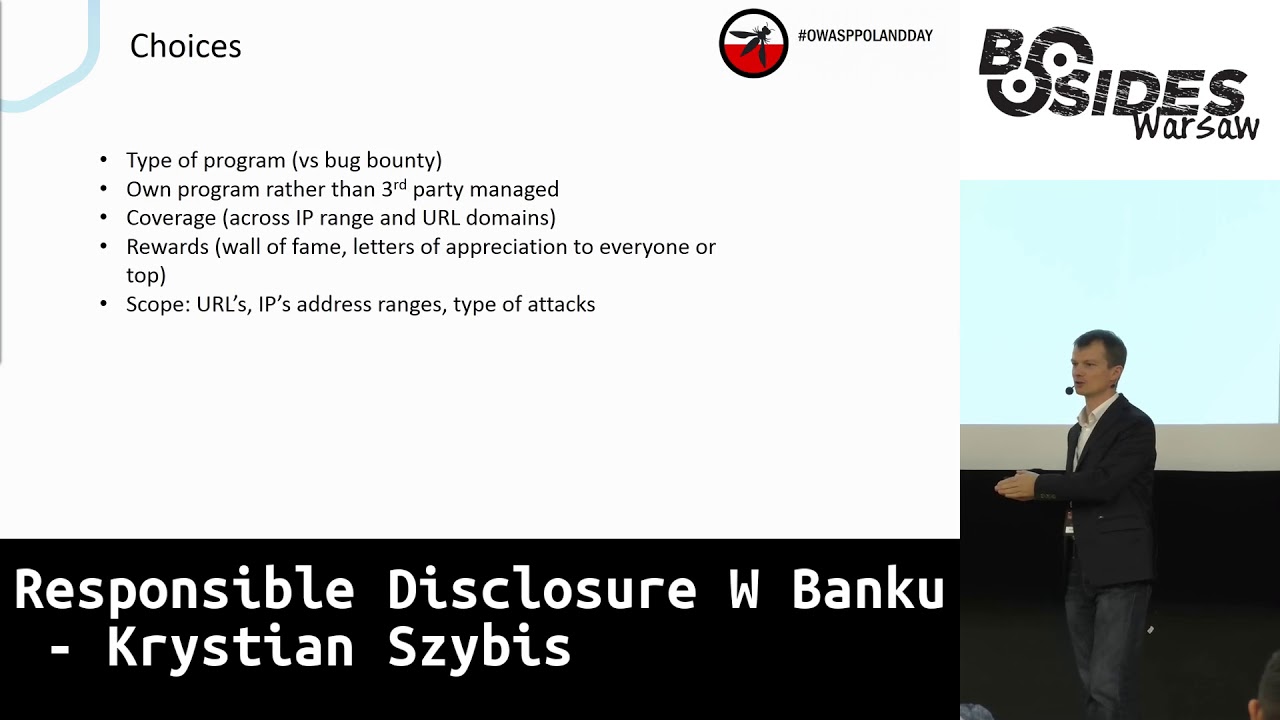
in our case. One dedicated person who spends most of the week doing something, checking something, chasing someone to do something with it. and so on. The rest is standard for the process. I won't bore you. Choices. Responsible disclosure or back bounty. I already revealed a bit why we decided to go with responsible disclosure. We think it's a journey. Journey is the English word. I don't know if it's the best form of it in Polish. It starts with a model when We could be offended if someone sends us a message. Such big corporations are sometimes known for sending law enforcement in reverse communication. And we wanted to go to the stage when we already talk, we allow it, but we don't pay
yet. Why don't we pay? Because we are afraid that there may be a lot of mistakes. On OWASP Day we talked about backbound Ruby or Ruby on Rails example which had to be taken after one day because it turned out that on buffer overflow From privilege escalation, 200 bugs were reported on the first day, and there were probably 500 or 1000 euros. And they ran out of money faster than they managed to turn it off. And the whole approach is about this. Do you remember the Defense in Depth? Most of the errors will be caught there. This process will catch some errors now, but The fact that we don't pay anything has negative consequences. The attention span
of a pentester will be shorter. Because, as we discovered, and I will tell you about it later, pentesters are motivated by what they receive. They are intelligent people, so it's not strange. We were also thinking about hiring a third party, who would be in charge of the whole process, and we would sign a contract every year and transfer the money. This is also an option. There are many companies on the market, especially worldwide, where there were service managers of these services from the most popular companies you have heard of. They can do it really well, they have really great ideas, they have very good tools and the only disadvantage that At the end of the day, you will have the fact that they don't know
the companies from the inside, they don't know who to go to, to which doors to knock. In a large bank institution, which can have hundreds of thousands of servers, maybe not hundreds, maybe from 100, such knowledge is very important in order to really do something with this tax, than to bury it. Now, coverage, which which we will cover under the web, which we will hurl. We have chosen those that we have already tested quite well. I wonder why, no? Maybe... What will we give you as a replacement? We came up with a letter of appreciation at this stage, which is a nice thank you that you can put in a golden frame or on your
website with a biography next to 50 others, which I also saw. And that's it from the choices. What have we found? I thought it would be a peak of findings at the beginning, but I was wrong. We have a stable flow of findings every month, not every day. Sometimes we get something interesting. There are no months when there is nothing. There are peaks. And peaks appear before holidays and before holidays. When all hackers find the most likely mistakes. I don't know what the logic is, but that's how it is. Holidays, yes, maybe that's what it's about. Now, the second point. We discovered an interesting thing. Who would have thought? Just look at the data. Pentesters are motivated by what they get.
If we give a letter of authentication, guess what is the average number of findings that researchers report to us. One! Very good! That's what it is. They get what they want, so they go on. So this is one of the problems we will address now: how to extend the span and what to give more. We could say that bug bounty is the answer, but before we get to bug bounty, what can we do more? The fact that we have placed our mailbox as the only one on the company's external page means that we receive other things and regardless of whether these are things for us, we still have to serve it properly in the eyes of our senior management. It happened that other pentest teams communicated
to us, we got something that was sent to another bank and we had to send it back because this zero day bug is cool but it doesn't work in our domain. The last point is quite ironic, because if you didn't want to talk to the communication department or the legal department, then by creating such a program, you will definitely have a lot to do with them and you will get to know them and make friends and you will exchange a lot of jokes and you will see that they are cool people. It will be useful, ironically, because not all pentesters are nice and not all of them are mature from A to Z and there are different cases when sometimes you have
to formulate a statement so that it leaves no doubts. Now, what's next? I've already betrayed it a bit. How many deductions? More than 100 years, as so far. The middle of the normal distribution is between low and medium. So we have mostly low and medium, a little bit high and a little bit of critical and informative. We have really cool criticals from this program. We got such that we were collecting the cheeks and of course I can't say that we were laughing and saying "lol" because in a professional bank such things are not allowed to do. We dealt with these matters very quickly. Despite the fact that we use an email inbox, not a web page,
most people who send us something, send us everything we need. We were surprised. We thought they would send us a bunch of information, we would have to ask them 2-3 times and talk to them. No. Almost always, 99% of cases, these are findings that are as good as needed, with a screenshot, with a POC. We don't have any questions and we reproduce them in 5 minutes. The most important thing is at the end. No production service has suffered during the delivery of this process, i.e. for two years, nor a minute of downtime on our e-banking services. Remember that the principles of this Responsible Disclosure were formulated in such a way that the attacker must take it into account, i.e. he cannot save data. We know that
it is a bit complicated for him, maybe even a leg, but the most important thing for us is to provide the client with a service. We have one of the most popular mobile services in the UK and it has to work. The most important thing is that there was no impact, so our senior management sees it like this: we have an additional process, we had to have only one additional person, and in fact we have a lot of value from it. Every company would like to have such a process. Maybe it's for the service provider, but I can tell you about it in the couloirs. What do we really do every day? What in the couloirs? Finding the asset owner. If the
company has gone through many acquisitions, restructurization, it can be very much infrastructure, a lot of applications and finding this owner will be difficult. And when you find it, it may turn out that he does not want to hear that he has to mitigate the budget, which already has, i.e. without an additional cent, pound or penny. I do not want to hear about it sometimes. However, There is a good psychological aspect here. When the owner sees that someone from the outside knows about his small, the word "sin" may be wrong, about this small liability, he will gladly mitigate it. It even happened to us that things that we found earlier and the owners refused to mitigate them corporate reasons, which were not allowed to be overrated. Here, when they
saw that someone saw it from the outside, they did it in an hour. So, is it worth it? Yes, everyone would be happy. Now, we have a few duplicates, maybe 10%. Mitigation time is probably the biggest problem. I saw in the OWAZP presentation that the average production time is 168 days for the loss of critical liability from the production. I can't say anything about ours. Ours is much better, but it's not as perfect as we'd like it to be. And it's a constant fight and... well, it's quite an absorbing process. Now, with the good ones, with the findings that are out of scope. And what to do with the finding? We'll get a nice critical one, but it's out of scope. What to do?
What do you think? Send the lawyers? Any opinion? Does anyone have one? Thank you and bye. We are mitigating it as it would be any other finding. But we are not telling the person that we will not send him a letter of appreciation, because he could read what we asked him to. And if we are ready to expand this scope to other domains, we will do it. But it is limited to half of the company now, because it is our zone where we feel quite comfortable. Social media... Social media... God, what a bad translation. Social media? Socialistic? No, it's something completely different. Anyway... This is also something we encounter. We write in our conditions that we don't like it very much. If someone does, it also reveals
some critical vulnerability in our social media. And most of us stick to it. But not everyone. And then we have to run, mitigate. There is only more stress. And in fact a little unnecessary, because we will get it anyway. It just takes a while. I've already mentioned the last things. What were the lessons for us? First of all, benchmarking the policy we created for the process and improving it every now and then. It's natural when you have a process. Always find better ways to complete some steps, some controls, because in such a large organization it will turn out that You can do things more effectively, but you have to find ways and cases for which these methods work. We noticed, for example,
that if I can say such a non-popular thing, that maybe it's different from the type of roles, but that a person who has a good, flexible way of communicating is needed to operate it. So not very technical, focused on truth and falsehood, but one that can talk to business and convince them even when they don't want to cooperate. So a bit of managerial skills. Pentester is also suitable for this, it also depends on corporate culture of the company. For a large bank, it is better to work with smaller companies. I know it's not popular, I can see your eyes, but it is. We noticed that sometimes there are findings when we go out of the process and just sit on
one and sit until we mitigate it. It was so with the critical ones, because it was really such things that maybe we didn't laugh for a while, of course, but later we found the right people and regardless of what they said, we forced them to fix it within an hour. And it worked, but it also required those people who were sitting there with the time dedicated to it, which if you have a shared service model, which are very difficult. Maybe I'm saying obvious things, maybe not. Owners often ask if they will get additional money for mitigation if we take them into account. And we tell them then no. Not a penny more. What do you think? Are they happy? Yes, they
are dying when they see it. So there is a large part of owners who are willing, there is a large part of owners who are resistant. And as with every heavier policy in the company, there are methods for introducing such changes and it is introduced. The last point is apparently one of the most important for me. If we find any vulnerability, we ask ourselves a lot of questions why. Remember when I said about defense in depth? We check when was the last Wulnscan, when was the last Pentest, who did Pentest, what checklist he had, what was Pentester, what was his personal bias, where were his favorite areas, and which he likes to miss. As you can see, if you even had "From a very good pentester,
our perception is that everyone has their own areas that they like, or that they like less and that they will check less. Maybe my former employees may disagree with this, but I see that one clicks, one nods that it is so. What does it mean? It means that even if you hire a very good pentester, one of them is not enough and there must be another one to check it. So we ask ourselves the following question: if there was an asset, if there was a mistake and the pentester overlooked it, did we change the pentester? And this was one of the conclusions, that today, when we do a pentest in the second year of an
asset, the pentester is always different because we ask for it. We want someone with a different approach to this and maybe find something from the previous one. And if it turns out that they did not find it, then we look at their checklist, at the company's methods and wonder why. Maybe only Responsible Disclosure will find it, and Pentester will not. I do not know the answer to this question, I just throw it. What's next? What is the net result? Less liability? You will get to know more Pentesters outside of the company, you will also get to know Legal and Communications in the company, you will get to know your Senior Management and many other important people, so maybe someone likes such exposure. You will create
a nice process, you will have a lot of thematic reviews, where you will look at the error through the whole infrastructure or the application, because it will turn out to be strange. The first time I see it, I will test it, and then I look at the infrastructure and see that it is the same. And then you have to start running quickly to do something about it. The end result. This service does not replace any of the services that I mentioned in the Defensive Depth in any way. Here, the pentesters do not cover the entire methodology. They only give us individual shots. It is a supplementary service that allows us to mix the number of findings without impact on the production and at a lower cost. But in
the future it will change, because we will probably look at the choices related to it again. What do we ask pentesters for? If any of you would like to take a look at our website, read RBS, in Google you will find under the search query RBS Responsible Disclosure, what are the conditions, which URLs, which sub-nets, first of all. We also ask everyone to provide the appropriate information to reproduce, as of now they have no problem with it. We ask for patience, mitigating, do you remember these 168 days? Mitigation takes less time, but it's not one day. Maybe for some critical mistakes it is, but generally it is not. We don't always have enough time to throw everything, especially if it is not
a critical mistake and to start only after that. For example, what is more important - reorganizing the reteaming for next year or dedicating yourself to this one burden? These are such difficult questions of managers. Now, only report to us if it happens to you. And remember that if we do something in some way, we usually do it for a specific reason and not because we are bad or irrational or the dog ate our favorite book yesterday and we are envious of everyone in the whole world. We do it because we have some good reasons, because we have a long practice and we have seen a lot and it turns out to be the most repeatable,
reasonably good way. I've connected our autoscope, if anyone would like to have a look, but let's move on to questions. Does anyone have any questions? We'll ask for a microphone. Hello, you said that you improved the critical in an hour, so where is the time for testing? Well, Pentester was nearby. It was a simple critical, I can't say, but you could recommend reproducing it to both a student of pharmacy and a manager. How did he know that he didn't get something else? This petester? In my case, it was a clean cut. We just removed it from production. That's it. Someone went to the socket and pulled it out. That's it. The fastest way. In the second case, someone turned off the ethernet on
the port. I have a question. How many days do you talk about the mitigation? In the industry, generally 168 days. What about the longest? I don't know. I can't say anything about my bank. I can't say anything about mine. I would like you to hear about mine. On October 1, in my case, I announced 365 days. And it still exists. If you look at the errors in the architecture of NT Kernel, they can be there for 12 years. having the best choice to fix it. There are some mistakes, because they are heavy and result from architecture, so you can't fix it with a quick hack. Ok, and tell me, does it often happen that in the next year, month, month and a half we will
change it, let it stay? I think that it happens that other approaches, for which the pentecostals have little empathy, that is, the bank has the way of managing risk, and the taxes fall under it, according to the methods that are used to manage financial risk. And the bank can, for example, accept the risk. Most people do not take it into account, but the owner can say: "Oh, I have a risk approved by all saints according to the procedure" and he says that he does not have to mitigate it. So, such situations also happen, but if it is on our perimeter, we usually say: "Ok, ok, ok, now give me the date when you remove it
from production, because it does not satisfy us." So we rather pull it this way. It happens that these dates are changing, for example, recently I had a report of some liability, I look at the catalogs, it's a duplicate, but the previous one is noted as closed, weird. I see. Oh, the risk was raised. And it was mitigated last year. But when I click on this portal, I still see it. And it turns out that something like this happens quite often. When something comes back. For example, I happened to write to the owner the day before yesterday that here we have such a mistake on the portal. He says: "How come? But I have decommissioned it
and I have not paid for it for two years." I look quite alive looking at this page and I sent a screenshot. Such things happen too. It happens that things come back from the dead. Because someone has returned the backup somewhere and forgot that something should not be on the prod. Okay, but I would say that these are not critical things. No, if they were, we would be there. I would announce to you a situation where you have access to half of your infrastructure through one stupid www and it hangs for several days. I understand that this is the moment when you run and pull the cable, or you fix something, right? No, this is
the moment when we call and the guy runs away, he doesn't know where to go. The guy or girl doesn't know which room to go to, the other one tells him which floor to go to. It may sound funny, but in our case it was like that. When we called and decided that we won't talk about this problem in the risk category, but in the when category, the person went to the appropriate room to disconnect it and the next day you have to disconnect it from the infrastructure and throw it away because something is left. So it doesn't happen that it was 360 and it was critical. No, no, there is no such case. I have such a question. Okay, then we'll ask that
random anonymous gentleman. Sorry. The question is, if the reportant does not warn these politicians, let's say he sets a deadline for a month and publishes it, do you send a team of lawyers at this point? I wouldn't want to speak for the company here, but Legal and Communications would be the answer to that, especially for things that are outside of scope. Can you tell us about cases where you actually send lawyers there? No, I can't, because I don't even know about them. I know that it happened to us a few times when the discussions were very unpleasant. We always tried to mitigate the liability, and not to send the lawyers, and to talk to the person so that she knows Doing such things and using such
methods is very unruly and you can play with the spark plugs, but sooner or later something bad will happen. And we always managed to do it. What pentesters don't realize, and I can say this quite critically and honestly, is that it is very inversely productive. Do you know why there are 5 of them and not 50? Because of responsible disclosure? That's why. I assume that every bank is afraid of it. That there will be a big problem that will be hard to control and will cause more harm. And that's why there are probably no such programs. If you have a classic way of managing for many years, You can't beat yourself with the argument that you'll
find new taxes if the other person sees the risk. And if someone writes info to TVP or puts it on the outpost, I see it as a risk, so I don't want this process. So I think that these hackers, if they sometimes laugh at themselves, they don't realize that such a process can be closed as a result of it. And then there will be only a lot of lawyers. Some big companies, which we won't mention, even withdrew their presentation from Black Hat and Defcon an hour before. And they took someone in their pants at the airport. So, well, that's what it's about. Contrary to appearances, you have to appreciate good will and try to have it. And it works in all directions. You know what, I have
a feeling that you would discourage me from sending applications to banks. No, I don't discourage you. No, because it's like... OK, let's say this: if someone collects... I don't know, let's take the simplest example. Of course, let's say that it doesn't exist, but... SQL. If I, as a proof, collect a piece of the database and send it to you, Is it okay? I'm telling you an example of a situation that I could find for you. If it's in scope, so it was in url or IP range, you didn't save any data to the database, If it is in accordance with our conditions, we have no problem with it, no matter how critical it is. We
only have a problem when people do not obey these rules and think that they know better. I will simply formulate one simple rule: if I find something, I will not dig deeper, I will collect what is on top and send it to you without ridiculing, ridiculing. I am just a nice, good person, then you are nice and nice to me. Yes, and I think it works in such a way that if other banks, because now there is a lot of talk in banks about these programs, if other banks will not see such negative things as ridicule, then maybe they will also decide on it and, contrary to appearances, everyone will be won. I won because
pentesters are also dealing with other portals, pentesters won because there will be more opportunities for letters of appreciation and so on. And the banks will win because they will have fewer liabilities, which can be used later in some strange attacks and circumstances. They could be used potentially. Good morning. Anonym. I have a question. Why responsible disclosure and not bug bounty? Generally, lists are nice, but it's not a new achievement. These are not the times when recommendations are so crucial. We don't build CVs based on recommendations. Like when we were talking about one researcher and one finding, Did you consider that if there was a bug bounty, there would be more of these findings? What did you think about the bug bounty?
I don't know exactly, because it was before me, but I can tell you how we look at it in general. If you joined WulnScan on some databases about 15 years ago, it was a success. And then even doing WulnScan, even the whole Infr, was off-limits. No. Today... Later, each bank grows to the point that these volume scans work, then that pen tests, the first few will maybe show something, but then we will define such rules that we will learn not to spoil this e-banking, which is so important and yet it delivers. And I think that the answer to your question is the same as We start with small steps, we look at how it works, what are the
advantages and disadvantages, and then we move on to the next stage. I don't want to talk about when my employer will have backbounds, whether it will be tomorrow or in 10 years. I think that the natural path from my personal knowledge is either to back bounty or private back bounty. One of two. It is also important what researchers should know. Private back bounty is basically obtained by being a good researcher from the past. If we ever wondered, we would have a table of years, the sum of CVSS or who had the most criticals, respond to them, invite them to the program, show what we have in return if we realized it. So I think it's a development path. You have
to start from this point before you get to red teaming. and will allow for much more, but this is the way to go. And I think that most financial institutions are in some stage, because with the number of conversations, we think that most of them want to take the first or second step. I just wonder how to do it well, so that you know what didn't happen. I talked recently with my friend about pentests of large enterprises. He told me that he found a mistake. He found a few mistakes, one of them was out of scope. It was about finding this mistake, my friend won't get anything. Do you think that in the case of introducing a bug bounty program, there
should be some annual budget for Out of Scope errors will be considered individually and the award will be awarded until all Out of Scope errors are resolved. Okay, I can answer that. ...by weight, right? And the most critical ones will be rewarded. Because it wouldn't discourage pentesters. I think that... It's a bit like the slide I mentioned, that sometimes we do something, the researchers don't know why we do it, and we do it for a good reason. Maybe some things we think haven't crossed the line until we want to take them. And because of that, supporting such behaviors as pentesting this, I think it would not be very interesting. In my opinion, it is still holding on to this
scope and not giving awards for autoscoping findings. On the other hand, we all know that the pentest world is small, as you will probably gather here and at the second conference you will be 70% of pentesters who are in this country or 60%. If one person says the second or third at the beer, it will be solved quickly and one vulnerability will make more. That's why I think that rewarding inappropriate behaviors will never be an option. We would rather address this problem differently. I also mentioned it on one of the slides. What we don't tell researchers is that we actively try to expand the scope. We actively try to add new networks, new URLs. The fact
that it remains the same for a year does not mean that we do not have a lot of meetings and do not try to establish it and sometimes overforce it to make it happen. As I say, we saw a big benefit from it and we would like to expand it to the entire infrastructure and apps. both API, mobile and everything that is connected to it. I have a question. Where did the idea of doing this process come from in your organization? Was it that the business was scared of some news about breakdowns and so on and they wanted to do something in this direction? I don't know the answer to this question. I tried to find the answer, but I
haven't found the answer yet. We have a CISO, who is a former pentester, and maybe it came from him, but I never managed to determine it. I heard that it came from a senior management person, It was supposed to be in two months and you were driving with coke and everyone was like "Noooo!" But they implemented it anyway. And nothing happened, as I said. Yes, but as I said, we are still trying to improve it. So now I'm looking at how to increase the scope significantly. I can reveal a secret and we will consider the internal responsible disclosure, which is for employees. It's a step further. I have a question about security incidents. I will be digging, trying to hack something,
and the police will knock me out. Because it was reported as a security incident. That's why when you type in RBS Responsible Disclosure, it's well described what is allowed and what is not. And we give... immortality, a person who acts accordingly, because then we really have to look at ourselves and if you, let's assume, did everything according to what we wrote there, but it still fell out, then we have to wonder if we defined it well. Because it's coming back to us, not to you. And from the process side, we have to think about whether such simple thinking, url, IPs, or specific types of attacks, or subtypes of attacks should not be outscoped, or maybe limited to some domains, or maybe we should do such
a "creview" topics, which I mentioned, and comb through the whole estate. Just out of curiosity, does anyone know how many external IP addresses does RBS have? Or how many should it have? Less than that. How many? Does anyone know? How many thousands? I'll tell you in thousands. 25 thousand. Ok, we have 274. This is a pretty big estate, so that's why this work takes a little longer. Yes, I don't even know how many internally. Less than that. Have you thought about an extended Responsible Disclosure for, for example, another report or only pay for the criticals? Or some, for example, Better locations, because I suspect you don't have any vouchers. Better locations. Coins. This is one of the ideas. When Department of Defense was doing
its CTF, I think a year ago, they were giving out such ocasional coins, which are now unique in the United States. I will tell you honestly that all cards are on the table in this discussion. We are thinking and as you noticed when I approach these topics, we will see what we implement and see if it relates to the effects. If not, we will still be looking. I will not exclude any option. Bug bounty is still distant to us. But I do not exclude any means to get there, because we see that some researchers find cool things, they justify it nicely, communicate nicely, they are very good pen-testers, but their interaction ends on one finding. And we have to change
it, I think I even have it written down in a very specific term, when we have to present some options, consider and evaluate. I heard that the donors of blood have stamps and little books. No, I'm joking. I'm joking. Chocolates, but without palm oil. I don't know, we have some options, I don't want to talk about anything that we haven't covered yet. If we approve, we will fund and put it on the website, then it will be official. For now, it's all about caring what will be done. Any more questions? Thank you, I hope you liked it.





