SAP Security: Uncover Hidden Exposure with Nuclei Templates #shorts
Show transcript [en]
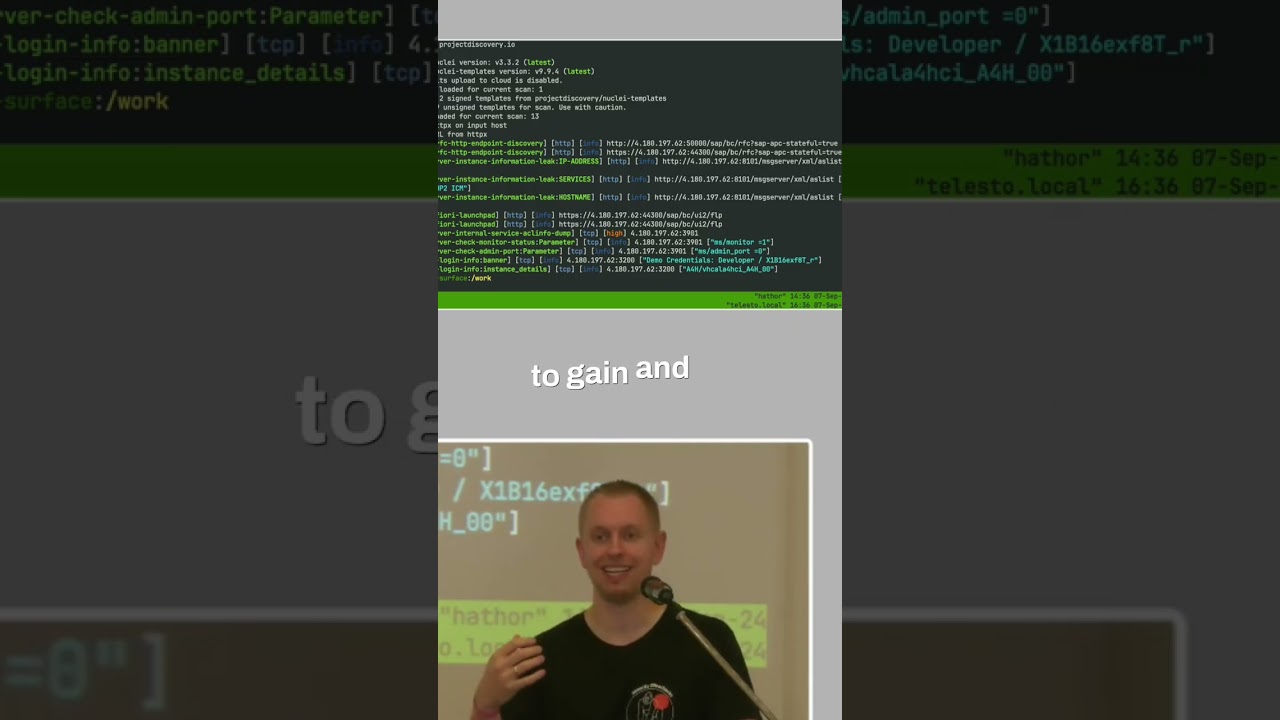
What we you can do, you create for each service or what you try to detect in nuclei template. We are not intrusive, so we are not flipping any parameters. We are not really breaking anything. It's more like just looking around, getting visibility what's enabled. We see for example host names, internal IP addresses, those weird UPD BTC SPO whatever. Um but if you go a bit down, you see we can dump the ACL on that system. We have the the monitor service enabled. Super interesting what you can find because sometimes you know then which company that system belongs to. And um yeah, some famous Russian companies by the way are also running SAP. Um it's quite interesting.
Anyway, getting those information and getting that visibility is just that what is exposed on my systems, either to the internet or maybe if you try to run that through your internal network to gain and see what do I expose there? We had various Yeah, I wouldn't say companies, but yeah, it's coming over and say, "Hey, I didn't even know that we exposed our system and by the way that we saw that it is exposed, we also recognize we have a brute force attack ongoing." I say, "W- Why did you not see that?" No one looked into that. And even if I ask the firewall guy why it's exposed, he said, "Well, I don't know." It's just happened. It's like,
"Okay, >> [laughter] >> please monitor your stuff."





