(Amplification) Attack Of The Clones
Show transcript [en]
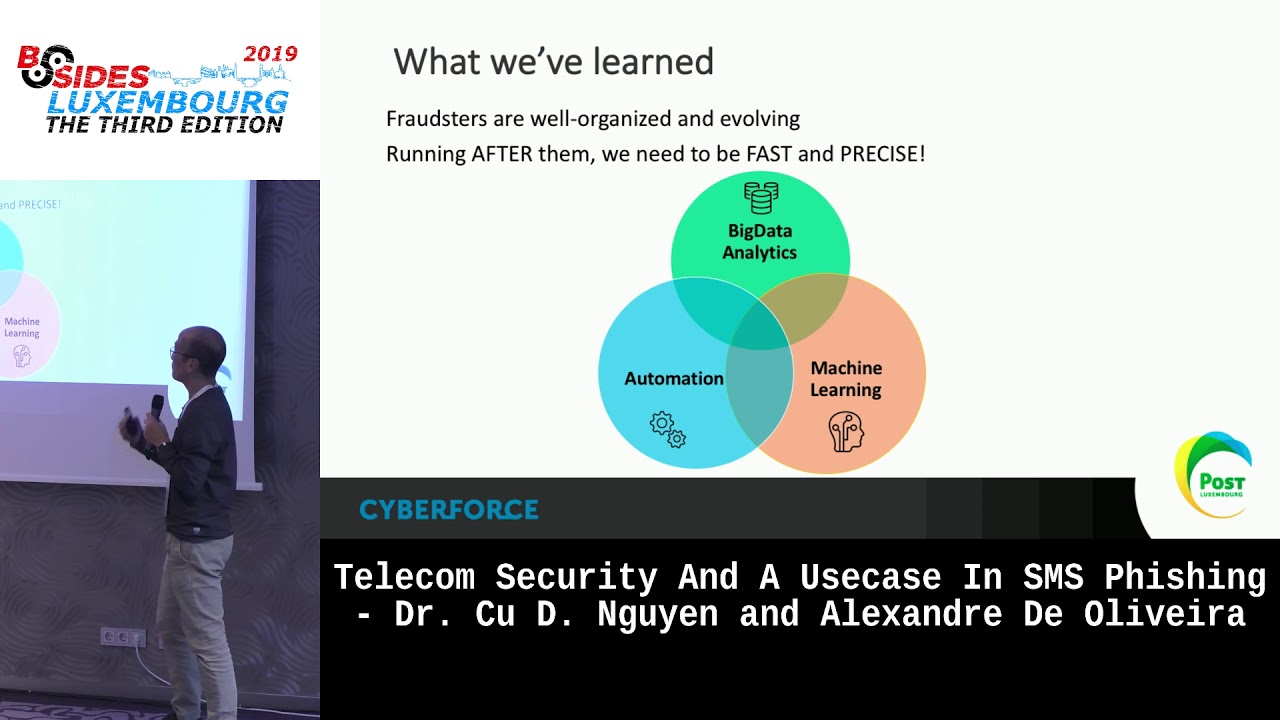
hi I am Pepe McKenzie is giving you my bio I'm presently doing my PhD in IOT and blockchain security hey Scott hi I'm Mackenzie working the industry for fair bit over 20 odd years across lots of areas lots of areas of unix security infrastructure architecture pretty much just a general there technophile many so yeah today we're going to talk to you about and others about Delilah service about district another service how its evolved the techniques and the various mitigations we'll look at some of the case studies probably just look at for Louis which is shows a number of very very interesting mitigations that can be applied and and then we'll move on to a question answer towards the end so and
to start off with looking at the protocol distinct ocean most denial of service attacks can be grouped into m2 you've got your network based layer three and four and star the tax and then you've got the slightly more difficult to deal with them less they have an application level attacks so just to run through the concepts because these are fundamentals to what a lot of the other attacks are based on reflection essentially the attacker would then would choose the IP address of the victim they would spoof that IP address and they would fire a request with that spoofed IP address at a number of different resolver services which would be able to then reflect the data back to
the victim amplification as the name sounds the concept behind it is you send a small number of packets into one of many services and they respond with a much larger response and obviously these concepts can be scaled up I find this very nice table that shows some of the amplification factors of the different UDP protocols here so as you can see commonly used are the DNS and NTP and attacks things like have found a Model S to NTP which talks back a fair bit of data interestingly memcache gives an almost 50,000 increase in response so it's quite desirable your flood attacks essentially are basically just chucking large amounts of data and to target and normally launched from their botnets so
what is the DOS attack well if dos came for DDoS and that's where it all started thank you so the DOS attack is quite brilliant um what it does is it's booths usually but there are some new techniques which doesn't require spoofing but usually spoofed and IP address and it gets an amplification attack or reflection attack where you get loads of reactions from hosts either to a broadcast or other mechanisms back at the spoof address all right so let's go back to the beginning the Smurf attack and faculty tack that started in 1997 from a guy called T freak which I assume is not the name his mum gave him and he was the first person to launch but DOS attack
and the first one was labeled a smurf attack and it's quite cool because what they did as you probably all know is they use echo they use ICMP echo packets they threw those at the broadcast and they use a spoof IP and it was the response from the others getting back to the broadcast message that triggered the first boss attack a variant on that was UDP packets used in freckles I'm Paul here right so the mitigations and they're quite straightforward closed down UDP port seven in your UNIX and Linux don't leave demons that you don't need running close down all your demons in your Windows environment closure services you've also got don't allow more cost in unless you need it
echo replaying echos I'm close those down if you can but they are network Diagnostics so and keep a few open you've got you've also got a request for comment request for comment which is actually tsipras stipulated that the one of the easiest way to stop dos attacks is to for ISPs to stop allowing a little illegitimate packets leaving their network and so if you've got an IP that doesn't actually exist in your network don't allow it onto the wider world network another thing is if we all as host in the network don't allow illegal illegitimate package to float around I forgot private network IP we drop it we don't pass it on simple things like
that can't stop dos attacks and if you think dos attacks are over think again you have companies such as the power tech in net scan who are actually providing the service to script kiddies and crackers and the service they provide is if they scan networks that are not implementing the correct security and then they put that information up so it's alive and it's well and it's still growing so jumping on to slowloris as a case study now interestingly this is one of my favorite DDoS methods if you can have a favorite really it's it's named after a rather cute little primate that moves really really slowly and the advantages at all this with very little input an
attacker can create quite an impressive amount of air damage so his primary effects thread based web servers and the most common of those is Apache so it's based around the concept of standard 8 we get requests which we all use on a daily basis now within the HTTP 1.1 protocol you're get where guests will be for your header will be terminated with a carriage return line feed and then another carriage return line feed and what's the lowest does is sit there sends the first carriage return line feed and then only a carriage return and leaves a web server waiting for that final line feed now am i patch for you or set a lesson for
default of 300 seconds for the HTTP had a request to have to complete and then then it will reset that counter again and since the client sends any additional data so when basically if the malicious user sends multiple requests it'll quickly flood the system it also evades most of your firewall ids/ips systems because it's not a malformed request which makes it an interesting one to mitigate so looking at apache first of all those forms of mitigation there's a three common apache modules the 10 i would recommend you can mitigate with so firstly Modric timeout that's really quite useful because that allows you to set a a bytes per second rate for delivering the HTTP headers and
a time to do it for the whole had a delivery to complete and any failure and to complete within that time span whoever's up the surf fishing for a write request timeout back to the client it's also got similar configuration options for the body message so it's quite useful and across the board not just for slaw lovers but it's a mitigation for lots of other DDoS and then slow attack methods second one would be to use mod QoS this allows prioritization of your HTTP requests allows you to set limits on the number of connections from a single source IP which can be quite useful and it will also monitor how your servers performing and under above certain threshold it
will disable you HTTP keeper lives and also allows you to then set a and the throughput rate as well and the final recommendation for Apache modules would be mod security now this is a complete Web Application Firewall so this mitigates them not just them and the DDoS but also things like cross site scripting Scott COSO reflection same origin and very some things and just keeping the focus here on slowest mitigation what it does also is to monitor how many air for eight hours have been returned to a client and if there's a certain number within a particular period that you configure and any future requests coming from that client will just be stopped in their
tracks by sending a TCP fin packet so additional mitigations for slowest which again work for lots of other m dot and DDoS type attacks depending on your budget has to go HTTP load balancer in front of it and for example an f5 big IP I don't work fair five just successfully used them a lot in the past and basically that would sit there and listen for a complete HTTP request before that's forwarded on to the web server you could also look to use a non flooded web server like engines I know there was a case where someone coded Galeras is a similar slow attack for engines but that's since been patched so don't use the old versions friend jinx
and also if you're running on Linux then iptables allows you to set connections per second you can also exclude proxies as well because obviously if lots of people come from one proxy address that could be blocked and that's not something you don't want either so a few other tools and if we've got time it then we can go back to some of them that there's a few tools out there and we can run through some some of the methods of how you can mitigate those so looking at one of the largest DDoS attacks it we had in recent history there was a case of spam house versus cyberbunker now cyberbunker got its name because they operate out of an old Cold
War nuclear site and Dutch hosting company and our policy is generally anything goes as long as it's not child porn or terrorism now spam has her basically identified that they were hosting a large number of internet spammers and so they blacklisted them the result was the biggest at that time a DDoS attack occurred against Spamhaus which peaked at just over 300 gigabits per second now they were able to mitigate this because they utilized them CloudFlare CDN and their anycast routing systems so the IP address was presented for spam house by CloudFlare and then that was distributed across their 23 data centers worldwide and so quite mercifully they were able to absorb the full impact to that 300
bits DDoS so they are following on from that because that used a techno technique called M DNS amplification and buying the later versions of find a patch to introduce her feature called them RRL the response rate limits that allows you to basically tweak your DNS servers to avoid the the use of them for one of these amplification attacks so yeah this always crosses almighty so basically CD ends are a really useful tool to open the toolbox depending on the company some montt may want to set up themselves running multiple systems worldwide or IDs one of the free ones or purchase the commercial service of them but yeah this basically can act to mitigate a larger number of
DDoS attacks so this is flashings another thing that we don't see very often that is potentially very very dangerous because anywhere where you can do a network firmware update on a device and if that's a malformed firm firmware you can essentially break the device now the context is very important here because if this is a smart meter across an electric grid then then the consequences could be extremely major black holdings another mitigation technique that we will come across is to mitigate basically tweaking the BGP routes and you can channel your traffic your Beados traffic down to basically the Devon all type location or off to a particular location so traffic can be examined and forensically interrogated so we come to
IOT dos they does attacks which are quite new the first one occurred in 2016 but before we go over that there are two types of IOT DDoS attacks you first have attacks on IOT devices which we haven't seen very much yet there's been a couple of cases and we'll go over those and then you have IOT devices being used to attack other host knows within a network now IOT devices if you don't know what they are are small form computers that are embedded in many things too many things you've got them in your fridge your router your insulin pump you've got them in your kids toys and it's been estimated that in the next two years
there will be 21 billion IOT devices in our homes and our lives and one of the problems are there several problems with them but some of the major problems is that they exist within their heterogeneous network there are really poor interoperability between different companies they fundamentally suffer from integrity confidentiality and authorization issues and we saw the IOT cases were kids toys being used to have his information including kids photographs voices address and likes and dislikes via IOT devices and we can see where that goes we also saw one well two and three letter organizations harvesting information via a Weeping Angel an attack using IOT devices so the early runners were the early runners were quite small but quite scary but then we
started to see changes and in 2016 we saw the first change the Mirai bug.toss attack the DDoS attack came along then we had the paseo which hasn't actually happened its harvesting and it's being noted and it's scary and then we've got the the Moose which is kind of funny sad and a bit scary and I'll go into those so let's start with Mirai this happened June 2016 and this was the first time people became aware everybody outside of IOT became aware of its potential and what it did was it took they recruited any IOT devices in the network and what the botmaster did was then got those devices to send lookup queries to German ISP and it flooded it flooded the
network to the point where you had a network storm and traffic couldn't come in or go out and it was kind of a good goal for them insofar as that they stopped they affected companies like Netflix as well as taking down the actual ISP so it was um a proof-of-concept in many ways and it proved what could be done then they released the code out there on github so anyone can get I've got a coffee that seemed to be as bad as it got until pronounces as you like is Arabic and in 2017 a company called trend noticed unusual activities taking place in cameras IOT cameras and they documented it logged it and watched them and what was happening is I am
these cameras have a plug-and-play mechanism which allows easy acces for us or you just want to get them and do what we want to do but the downside is is not secure and this was actually brought to the industry's attention and they supposedly patched it but he still exists in many devices and this was a is being exploited at this moment by this new D dos and these devices are basically we're we're believing are going to be used because of the way they send their SSD packets out they don't actually need to spoof an IP so these devices will be up to 120 thousand cameras on the network are protected to be infected and we're still waiting to
see what their target is and what they're intending to take down so this is one to come some time and we believe it's originating from the Middle East due to some of these data and stuff views within that that could not be true or it could be true and then we've got the line it's moves not quite a DDoS a bar is using and command and control it's used in all the the fingerprints of a DDoS attack and it's actually monitor eyes dit for the ego market I like it because it's funny and I don't use the ego market and I'm amazed of what these people will do but it's actually going out there and taking over routers and
then hijacking packets which relate to social networks and then allowing people to do those networks into allowing them to have more views or whatever you do on those networks so that's the indication of where monetization of this technology is actually going to go you've got two players or two actors you've got the monitor ization and you've got government actors that seem to be dominating this market so mitigation is the same old same old patch in 2015 you had Fiat had to do a mass recall 1.4 million of their cars had to be recalled because dried by dust which is a DDoS attacks were taking place the first type where cars security was so flaky that
people could take over the steering wheel engine management the engine of the car while it was on the road and they had to do a quick recall to patch their systems up so patching is your first line of defense you then got a small growth but a growth nonetheless of anti-malware taking place in IOT it's been a network-based m2m networks because of the interoperability Andy a genius nature of IOT device is difficult if not impossible at this stage to design an anti-malware to go on devices plus you've got hardware and memory size problems change the password I mean where that's possible it's very difficult to change a password on your network fridge because they generally
don't give you the ability but where you can change the password closed ports down if you've got a plug-and-play device it don't allow devices on your side of network to use the plug-and-play dis activated don't allow it to happen in the case of Mirai you can actually flush that by just turning your device off on on again because it's held in memory within with respect to a purse it foreseer I that's not possible it actually will you can turn it off and turn it on you will still be can't native more to the point you can actually change your password and because of a zero-day exploit which is known of it will come back it's literally I mean we're looking at
ways of trying to stop this but the devices that are affected are affected you can standardization I'm a strong believer in standardization you've got 6lowpan which is IP version 6 application for small form I Oh T devices combined with 802 14.5 and there are security measures that are contained within those that could also help but the bottom line is a lot of companies are going for their security by obscurity and this curtain office said this is no security at all so I'm a strong believer that the industry has to come together we have to come up with standards we have to implement security I remember Microsoft when they first came on a long time ago and the security
was flaky then they're now really secure they've come in line and if we as an industry can actually get standards in place we can up our game so just looking at some of the things that happened this year we've had teams from your Europol a combination of the Dutch police and the UK's NCAA and they shut down their web stresser which was one of the largest stressor sites responsible for basically selling DDoS as a service and their web stuff so allowed you to run out his service and for various fees his admin was spread out in various locations and around the world and in different places I've been taken to custody that they could be it they were basically charging
fees that were as low as 15 euros a month for a DDoS capability so basically looking at meters and stresses in this stressing service husband spun up over the last few years the services are being sold to subscribers and some of them are happy to call themselves boaters some of them think it's better to call themselves and stress us because they're testing the limits of your network you're on flaky legal ground either way so very quickly just having a look at the motivations and there's probably five different ones finance always comes into play you've got the revenge case which is normally amongst em kids and them arguing over online games in a lot of cases or
pranking them in some cases there's I thought your core belief or hacktivism that there is some motivation that's spun up a lot with a lot of us and the lower than the high orbit to iron cannons for some people's intellectual challenge and there's nation-states but looking at it as a potential for cyber warfare so it's an example of some of the adverts that we've seen out there for them feed us as a service so yeah some of our takeaways here patch everything up to save all your UPnP and love to put buy balances in and maybe CD ends things like that disable DNS and NTP access queries to everyone out there on the Internet otherwise you're complicit and there are
RC guidelines out there is how you can do a lump of the mitigations interesting one and somewhat controversial because people do use tor for legitimate reasons because depending where they are in the world if your reason if your users of your site in your application have no good reason to be connecting from tor for example they're doing internet banking why you would want to do that and going through tor in the first place I'm not sure giving the bank already has all your details then just block all the Tor endpoints you can download lists to find out where they are because an awful lot of the attacks will come through the Tor endpoints so sleeping here open up to some
questions I don't agree with a toaster here I think there are lots of reasons to use tor and I mean blocking people who aren't part of this world our Western world and stopping them having access by blocking tour there are other ways of actually stopping dos attacks DDoS attacks which don't involve actually excluding people who aren't in our world but anyway we're opening it up to questions so if anyone's got any questions go ahead oh no you just to say that thank you for the presentation I think you have a lot of information the only thing that was missing is talking from an expense I add in the price company if for example on that
your company has one gig of 10 gigabit network interface to the internet and you receive for example a 70 you gave it to us on your company which usually come on now so I think the biggest record is one that 4 terabyte for it much the thing that we were missing back then I was needed to know is to know the phone number of the ISP because sometimes the ISP can sustain the attack you can always contact him say you can block this bot because luckily for us those are scary but where you are usually focused on whom as you mention UDP ports so if you can report to the SP please block copies of our company that's a
good thing to know as if you don't know the phone number or the game you know the number is not available yeah I think I I'm actually I used to seven is two zero zero seven what compliance oh yes and your disaster recovery plan you should actually have the various numbers and ISP would be one of those to basically shut down the attack and that complies move I'll riff see I am calm as a number but that also request that ISPs are actually the front line so yeah thanks for reminding me any more questions
you mentioned the tour is now a popular entry or a start point for attacks besides I can recall tour was always pretty slow and not very efficient in delivering time back to a single end point just curious if that if tour is actually not powerful enough for that okay I would view it more in the case of if you're looking at some of your slow type attacks your layer 7s your things like slow loris really that sort of thing where you're sending packets very very slowly in multiples of those if you can do that from multiple tour endpoints scattered all over the world you're still opening I've been using up all those requests it doesn't require
much input also if you're using tor at that point to come in as your starting point for then an amplification and reflection attack it takes place after that you're masking your origin to quite a high degree and then still performing a significant attack so if you can cut that if you don't need to use it for your site and your services you can block it if you do that's a different matter but it's just one of many mitigations you can't I'm a strong believer in defense-in-depth and you can't rely on just one magic bullet that fixes everything so thanks thanks for the talk sir I noticed one thing you didn't talk about was services like Akamai and cloud fair
or maybe I missed it I was sleeping from but um I
okay I must have missed it sari was hidden away and do you think that I mean those are very good for layer seven like you said right it's layer seven protection you're protecting your application if you log on organization you really this is probably what you need do you think we need to take that concept down another level and actually start looking at layer 3 protection are the same in the same methodology or do you think we'll never get there because networks are inherently distributed and you don't want to go through a single point of failure I think level you could take it down there it depends again on the size of your organization so you would still
look to do things like blocking controlling a lot this traffic at your editors at your firewalls depending on the size of the organization you might run your own internal BGP between multiple sites multiple data centers so yes at that point you could do implement this a lot of these services and block things like broadcasting and people who tried to send spoofed IP addresses at source if you're in there I actually had a follow-up question but different question if you had something to add as I said you can add various requests for comments I actually asking people if we if you could implement some simple things like not forward in illegitimate packets there are IDs and other things
like that are coming along a long way since blocking in network but you have problems with so you could block say your internet but what about Wi-Fi what about all the other networks how do you jump over and you've got 6lowpan I have you've got a problem there where encryption problems with they symmetric or asymmetric encryption of for IOT devices asymmetric beam to a much data but symmetric how do you do your handshake can stop Alice from admit sorry from listening to it so you've got problems the ideal would be your layouts network clone block him but there are problems which relate to the various different types of technology but I think we should aim for
the ideal it's just because it's difficult doesn't mean it we shouldn't try to get there so my other question is do you think about large organizations I mean a lot of times nowadays you're outsourcing you're probably hosting your data centers and collocations like if you actually looked at the potential impact of having multiple customers in a colocation site where one customer is the target of an attack okay in that case once again if you're running something like anycast rating or a CDN service at a point in your coalos you can distribute that traffic around between your different sites you can almost isolate it because you've put I assume you're using them with different customers in that case they're different
parts of the cloud model and they're so essentially you're different talents and they've isolated off so you can actually shift tendencies and migrate those to different locations to handle that everything you need to maybe be a little bit creative and look at your logs as nothing and have them in network admin and security admin who are on before but yes that can be done I think it's covered most things the only thing I would say is you should have redundancy and failover so if you're having traffic coming to one site try and failover that's what it's there for and that will help there are other things that you can do higher up in your design but throws
into a lot of information maybe we can talk about that afterwards but I submitted the paper that's gonna be talked about in South Africa covering an awful lot of that from various different layers so maybe later so thank you for mentioning response rate limiting but I have two observations and could use help from this audience in both the first is it's not the default either for bind or for NST Norfolk powered DNS the vendors are waiting for you the users to insist on the it being the default and the second is DNS is not the only service which must be open in some cases and so it turns out a lot of other things need
some kind of rate limiting and in the perfect world that is along that path everything has rate limiting which means we have maybe a billion times more state in the network than we have today and that state has cost in both CPU time and RAM and complexity and diagnostics in other words that path leads to hell and RRL is very much a band-aid until we can find some way to get b/c p-38 the source address the filtering at the far end where there is no economic reason to do it so we're pushing on a rope and I I would love it if we could push harder Europe in particular seems to be willing to use prior restraint in regulation you
might consider what Finland does done where it is illegal to not have source address filtering and possibly the rest of Europe could adopt that also thank you thank you that's actually a very valid point that the push for legislation cashy force change so yes that's very useful and anyone else
okay thank you very much