voodooKobra - When Frameworks... Don't
Show transcript [en]
my name is Scott arisi you can call me vo Cobra and this is a journey through the ecosystem of PHP Frameworks oh oh battery's dead or maybe not okay so a little bit about me I'm a PHP developer I'm not really into um well I don't have experience with penetration testing and advanced exploitation and all the other really cool sexy fun stuff that you probably heard a lot about from everyone else at this conference um my interest in security is that I believe that if you're a developer and you don't have any knowledge of security you're irresponsible and your liability I'm also a big proponent of Open Source I run Linux on my laptop um
I've run Windows at home just so I can play video games with my friends but every virtual machine that I use 90% of the time is Linux all right so what is a framework well a framework is a a library usually standardized classes and stuff um it's meant to get applications off the ground really quickly um without having to reinvent the wheel 100 times obviously things like database abstraction you probably only want to write that Library once um some software uh engineering patterns follow thing called MVC model view controller separation so that way you can have your database guy and your PHP guy and your uh web designer all working on different parts asynchronously without having to you
know stop one thing and start the other without them like really stepping on each other's toes um templating for the designer then you have routing for like rest URLs those are the kind of things that a framework gives you but is security one of them so these are some Frameworks I looked at through the course of this talk um not all of them I'm going to find bugs in that I'm going to tell you about today but these are just some of them code igniter it's a really old one um their uh development thing seems to emphasize backwards compatibility over security and that's been a problem uh Cake PHP larel I mean if you ever
working uh if you ever program PHP and look for a job on like Craigslist or whatever you're going to see some of these show up especially codeigniter Lille andand Symphony so which one of these actually offer a security class and that doesn't necessarily mean it's named security um it can be named security it can be an encryption Library it can be a password hashing thing generally these are the ones that give you some kind of security feature uh some of the other ones don't some of the other ones might have had one but I couldn't find it when I was looking to the library to put together for this talk so I that's probably not
comprehensive but those are the ones that I was interested in so these are the ones that I'm going to actually go into so let's talk about uh some of the problems that you'll find in these libraries the first one is weak randomization um I don't know if anybody's familiar but there's uh several talks at black hat and papers out um about black hat or sorry blackbox testing of random number generators and I believe with just 32 bytes of information they can predict the next number with absolute certainty with things like uh Rand and MD Rand and you're going to see a lot of this in a lot of Frameworks um Cake PHP when you use their
um it's I don't know how to pronounce that honestly uh re deal whatever the AES guy um they use mcrypt Rand as their uh flag for mcrypt create IV to generate um initialization vectors for Cypher blockchaining mode now I don't know if you know the um uh encrypt Flags but you have three of them you can choose from you have Rand which uses the Rand function which is not cryptographically secure you have uh mcrypt Dev random and mcrypt Dev Ur random which use the dev random and Dev random uh files on Linux which are cryptographically secure and this is what the actual code looks like with the offending piece of code um highlighted in red
interestingly enough um it also uses Mt Rand in the um uu ID to generate authentication uh codes or authentication Keys e is a different framework that also makes the same mistake however in a different part of the library it actually uses deie random correctly but when it comes to initiation Vector they fall back to random andoh and I forgot to copy the source code into that they have a weird exception that if you're running Windows it only gives you the option to use Rand um internally with PHP if you specify Dev random on Windows I believe it goes to the crypto API and you get a secure random generator anyway even though slev SL random doesn't exist on windows so
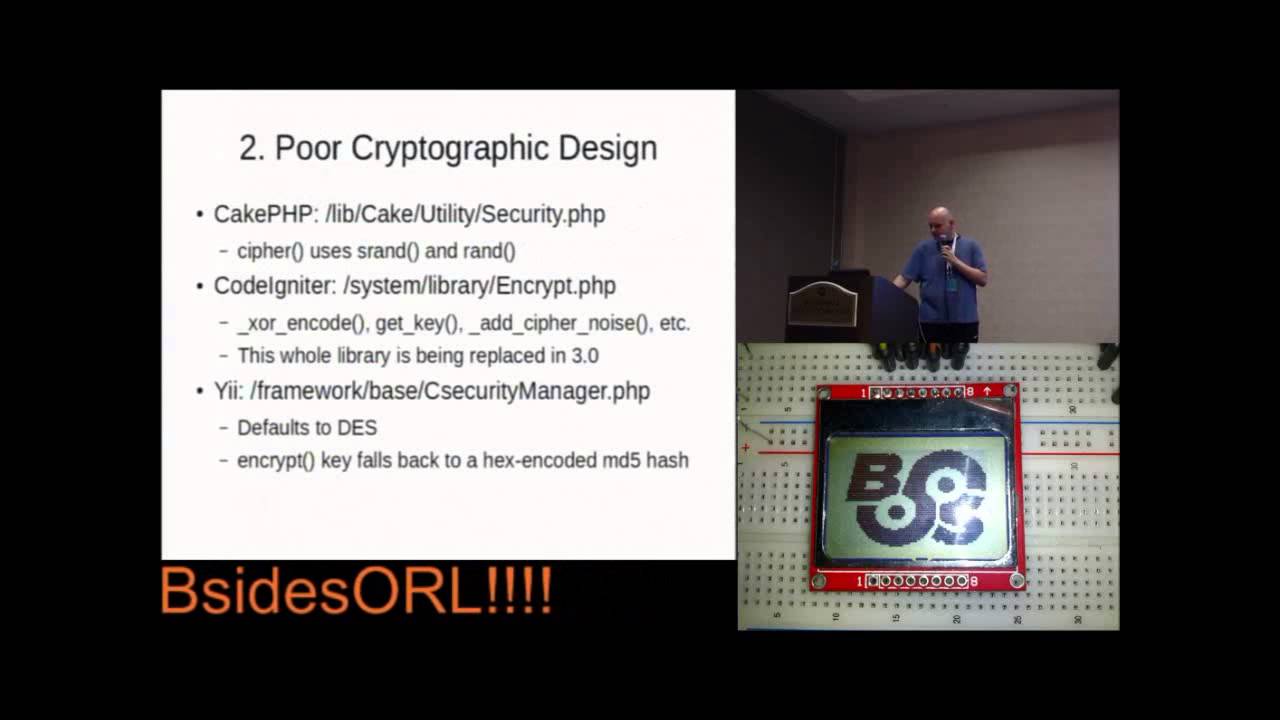
doing this is just a really really bad decision not that I really know anybody who runs PHP on Windows all right so poor cryptographic design um generally when you design a cryptographic library you want to use the standards that have been tested and vetted by cryptographers um the reason for that is that cryptography is not hacking cryptography is mathematics and Engineering um you know it can be fun to roll out your own code that does something really cool and share it you know with your friends but if you're going to put in in something people are supposed to use in production for their websites and for businesses you're going to want to follow the standards that have been
hammered on by the experts so cake php's Cipher uses a combination of s Rand with a constant um seed and the Rand function and uses it like a stream Cipher it actually XS uh the bytes with the plain text um there's another weird thing in code igniter where they have a thing called xor and code which is extremely similar um there's also some other problems with uh C igniter their G key function instead of a randomly generated key or anything like that it just does an md5 hash and outputs heximal as a key whereas you're going to want you know a binary value so that's really stupid I reported that to it um they also have a weird thing
called ad Cipher noise to try to stop against um attacks like beast and whatnot that attack the um the uh cyer blockchaining weaknesses it's really sketchy I haven't really analyzed if it will work or not but just gut feeling tells me it wouldn't and we address uh me and a friend of mine in Canada and a couple other people address these problems on their GitHub and they have a new library that's completely replacing this one and 3.0 problem is they are dragging their feet on releasing 3.0 go figure and then you once again framework based e security manager that's a typo it should be capital S um by the default the class def um defaults
to desk encryption which as anybody who's heard of e uh deep cck back in the 90s will know that that's not adequate for anything and once again it falls back to a hex encoded md5 hash if you don't specify a key when you call it now here's the more interesting thing this is a problem I can't just say is in a handful of Frameworks it's not necessarily a feature you might run into it might not even be enabled but there is a problem with core session design in several Frameworks I found in code igniter and kohana I also found it in the leaked source code for PHP Fox which I don't know if that was
legitimate but somebody uploaded a PHP Fox uh with modules to GitHub and I looked at it and found that they did the same thing so this is my understanding of what motivated them to do this and I'll show you the mistake in a second um I believe they wanted to keep track of session state in a way that didn't involve the file system so if you have like a multicast environment or you have like a bunch of cloud servers and you something goes wrong with one you switch the users to the other you'd want to be able to not have to everybody you know log back in or if temp gets wiped because of a reboot and
somebody was on 5 minutes ago then they click it LO doesn't log them out cuz by default PHP store session stay in attemp folder that's what I suspect the motivation was the problem with that is um as you'll see in a second it stores everything everything in a cookie now two things are bad about that one cookies are limited to 4 kilobytes of data so you really cutting yourself off the ankles if you need to do anything fancy the other thing is that cookies are completely controlled by the user you know you can change the cookies you can send false cookies with every request and they recognized that so they decided they were going to authenticated
with a hash of the message being the default cookie or serialization of all the session data and and a key usually stored in configuration and they usually just appended together as the hash which from my understanding leads to weird things like length extension uh length extension of Hax but that's not the Avenue I want so let's take a look at code igniters this is the actual code to verify a the MD md5 hash of a session variable from the cookie now does anybody see a a bug here vulnerability
want a hint they're comparing it using the not equals equals feature which yeah that might seem fine but there's a weird Quirk with comparison operators in C PHP probably every other programming language and that's that it will start with the first bite and keep going until it finds one that doesn't match the two strings and immediately return now that might not sound like a big deal you know that might actually sound like an optimization something to be desired but when you're doing cryptographic hash comparison the sooner it fails the sooner you know um if it you know how far down the hash you got correct and this leads to something called a remote timing attack and how it
works like this you start at let's say zero and you keep trying until you um go through F and you keep doing it and you see which one takes longer to fail and then you assume that one's correct and you keep moving down and you know you keep doing that until you have a hash together and it looks something like this you know zero all the way down fails immediately but then D800 takes a little bit longer and then this one's slightly slower to fail and then you keep going and you get your hash and this is the thing you can do to the session State stored in a cookie with a hash pin it at
the end with code igniter kohana PHP Fox and probably a number of other systems now if you're going to do a timing attack you have to know one thing it's very noisy you're sending lots of requests in order to see which one takes longer this is not something you can just you know um you know start Metasploit run this payload and have a shell immediately um on the other hand compared to uh hash cracking it's very fast you don't need to know the key you just have to know what message you want to send and then play around with the values until you get one that works it's like um the movie The Hollywood St type
of Steve cracking or you listen to see which one actually you know oh I heard the click I heard the thing that's essentially the same thing if you know the first one's 23 you can keep start from 23 and try the next one and keep doing that until you find it and just some back in the envelope calculations if you wanted to break an md5 hash um kohana from reference uses sh1 so it'll take 20% longer um if you only are able to send 10 samples a second but you wanted 100 samples for each bite or for each hexit depending on you know how you wanted to cut that it would take you about 22 minutes of
running this in order to brot force it now that's 100 samples you probably could get away with a lot less it might take a lot more it depends on the environment you're working in so the takeaway um many Frameworks offer security as a feature um people who actually use this to develop applications are going to depend on these features in their applications and unfortunately they're often very unreliable for people who are actually framework developers these problems are fixable I've actually submitt a poll request to a lot of these problems not all of them but they're coming and finally use the source Loop if you want to use a framework check the source code see if it does everything
correctly and that's all I have any questions yeah um I have a question about the timing attack you just described I mean is that is it micros the difference I mean when you're trying to you know figure out the actual you go a little more yeah um you might actually because it's just a string comparison right yeah actual because the return is already happened from right just the actual computation of the is already happened yeah this isn't attack on the hash operation this is Attack on the string comparison between the hash and the um what is calculating from what you're passing it and what it expects it to pass and the other thing is that
there's no actual failure when this happens it just happens kind of transparently it just destroys the cookie and says hey generate a new one um the timing difference is going to be yeah it's going to be micros seconds it's not going to be like a you know oh a 10 millisecond difference for each character because hatch operations are extremely fast that's why you need a lot of samples to actually detect it but that depends on your environment if you got two virtual machines next to each other 100 might work if you're an Internet site somewhere out in like Russia where you might have anywhere from 70 to 1,000 milliseconds latency that's going to take a lot longer um
there was actually a um I think it was was it deathcon or Derby con there was a talk about um remote timeing attacks I think it was last year um I don't have a reference to that on here but um crap if I had inter I probably would have embedded a link to that U when I post these online I'll reference that so that way everybody can cross reference that um any other questions there was originally a demo plan but um there was a lot of complications not having Internet tried to hook up to Raspberry Pi and it was just not working um um yeah I'm going to have to work on that before I publish that so any other
questions okay well this was a lot shorter than I intended it to be but thank you for coming





