Malware Exploits Avast Driver to Terminate Processes #shorts
Show transcript [en]
What else can you do? Um, and what I'm showing you here is just a few examples, right? But there are some logic bugs. And this is one one good example. And this is from the from the code that I showed you before. And this is uh found with a tool called IOCTL lens. Uh, and you can also find it with a driver body. Uh, that is a plug-in for IDA. And this is just arbitrary process termination using C sitw terminate process. That's the control code system buffer and all of this has been found directly from static anatic analysis uh using this tool. You can also find it with driver body. I think I have a screenshot
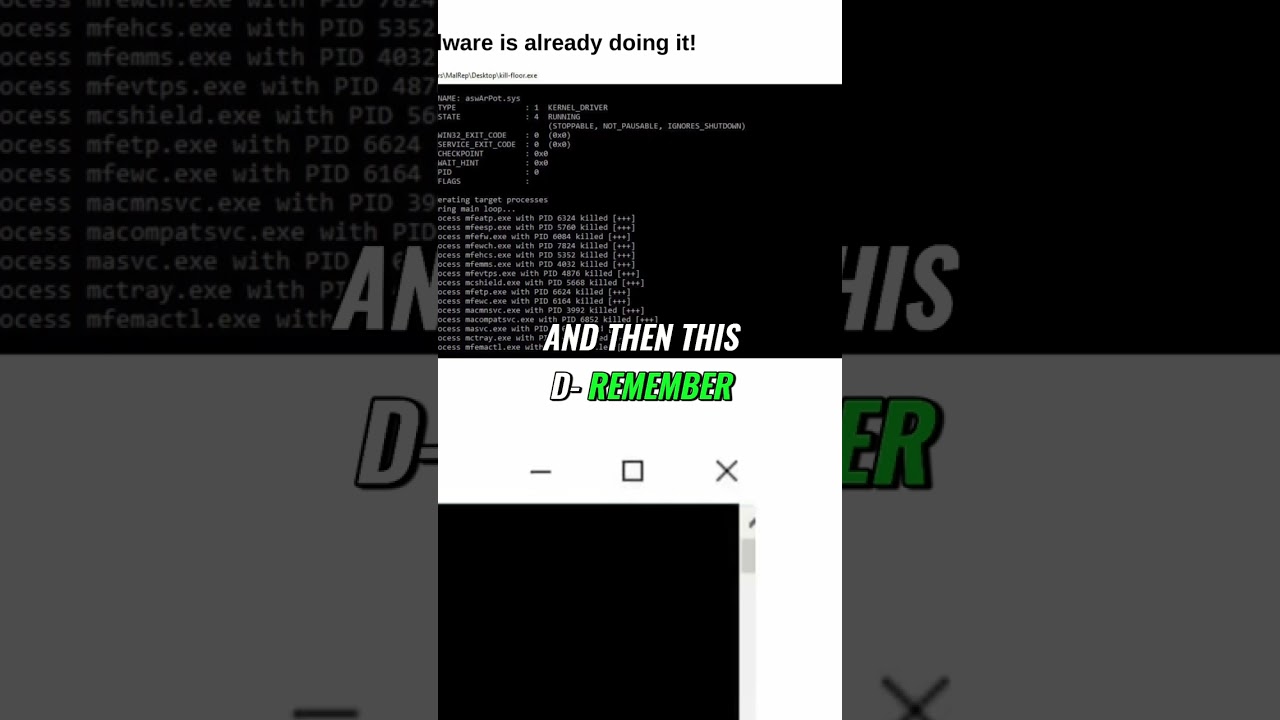
of that. Um and who is using it? Malware is already using it. This is like six months, eight months ago. Um and it's going for long. It's not just now. Uh this is from killf flooror.exe. This is not my screenshot. I I stole it from the from from the researchers. Um this is from the Abbas uh anti-rootkit uh driver and you see that is the driver and then what this malware does. So basically it's a malware that you get infected and then this remember I should say that you can only load trusted uh sinet drivers. All right. Well, the Abas is trusted and is signed and it's installed in a lot of computers. So that's why they they bring
their own driver. It's called bring your own driver. Uh that's a technique. So basically the malware would load that driver. Yeah. And then after loading that driver, it's going to use that driver to look for well it's going to create a tool snapshot to basically create a snapshot of the all the running processes and then from the running processes it's going to try to use it's going to use that malware that that malware well it's a it's a little malware the aust but it's going to use the anti-root kit from Abas the driver to run terminate process from the kernel using the Abas driver right And right so it's uh the list here's just a
a a snippet of the list but the list cover all the antiviruses. So it's going to load that and it's going to it's going to do that. And here's a a quick uh screenshot from the from the code of the of the aust driver itself. If the process name matches the malware creates a handle to reference this solid ABS driver as as as you can see that's the name create file then create a creates a creates a handle with it and then once the handle of the driver is created the mwell calls the dispatcher that I mentioned device IO control and then it's going to call that IOCTL with the process ID that I already Hot.





