The World Of Cyber Deception - Joshua Wardle
Show transcript [en]
all right brilliant okay right good morning everyone so thank you very much for coming to my talk this is going to be sort of a Whistle Stop tour of what I like to describe as the world of cyber deception so hopefully this is interesting hopefully you might learn a new area you might your interest might be peep this is something you can do at home if you've got the time and and dedication so before we get started properly let's do some introduction so my name is Joshua I am a graduate consultant at a company called logic where just down in Bristol we do a lot of work for defense or one of those kind of middle-sized smmes uh I did a
computer science degree at Southampton I have a Microsoft search but perhaps more Salient for today is I have a certification in deception from a company called countercraft uh we at logic are partnering with countercraft try and deliver their product across the UK so if you've got one a big enough organization and you're interested in this maybe can hit us up if you so choose I've spoken about deception before I spoke about this at bides London but that time I only had 15 minutes now you're stuck with me for 50 so we're going to go into a lot more depth this time and hopefully we'll get to really dig into how we do deception so before I even begin to
explain what deception is we've got to take a step back and we're going to start by considering cyber attacks there's a lot of models out there for how people describe cyber attacks the one I learned first was the locked maret model model okay which suggests that an adversary will do some reconnaissance on you they will come up with an exploit they will try and send that to your systems and get it to be run somehow using that they will gain persistence they will get some kind of command and control capability they will call home and using that they will try and action their objectives now a lot of very traditional security tooling engages with our
adversaries so that is it detects their presence and it tries to stop them on the right hand side of this red line and that's because a lot of traditional security tooling is really focused on trying to stop some kind of infection or stop some kind of intrusion so for example antivirus software clearly kicks in at that point on the kill chain but that does beg the question can we engage a little bit earlier on the left hand side of line and with some types of tooling yes okay with network intrusion detection systems you can detect Network reconnaissance fair enough but there's a lot of different types of reconnaissance and weaponization that traditional tooling can't pick up and this is
particularly important because adversaries are constantly evolving right the tactics techniques and procedures or ttps for short that they are demonstrating is just so different from what it was even a couple years ago preo but this is also really Salient because of Insider threats such as your Rogue employees who don't necessarily follow this kill chain in quite the same way they usually follow it in a rather compressed manner and so it gives you even more impetus you've got to try and catch them out as early as possible and so this is where Deception comes in so deception at a really simple level is tricking your adversaries by putting fabricated assets into your network or out onto the internet so this
could be fake servers fake laptops entirely fake copies of real systems that's all valid different ways of doing deception the presence of deception it is supposed changes how your adversaries make decisions as they run along this kill chain as they do as they encounter deception and it leads to what some describe as cognitive and emotional responses in them that can impede their ability to perform their objectives now that doesn't mean they curl up into a ball and start crying in the corner but that would be great what it actually means is usually one of two psychological effects overload and tunneling mental overload is a bit of a strange one to imine so imagine for a second that you
were an adversary okay you're a nation state adversary you've got political economic and social factors all around you which means You' got a lot of pressure on you to get the job done otherwise I know government might you kill your family or something flippant example but an example nonetheless now you've got to not only all those factors you've got to deal with you've got to avoid being detected youve got to avoid triggering traditional security toing and now an adversary has to avoid deception falling for deception assets that can be a lot to handle it can be a little bit overloading a little bit over stimulating and that can disrupt attacks as we'll see in a second but the other
effect is a little bit simpler mental tunneling depending on the personality of your adversary some might see that something is deceptive and get hyperfocused on trying to figure out if it's deceptive and lose complete focus of their actual goal and that can again disrupt attacks so we've mentioned disrupting attacks and indeed they has a good number of benefits across the kill chain overload can stall adversaries okay if you've got fake Assets in the way of real ones and if adversaries are overloaded it's going to delay how long it takes until they hit your real assets giving you more time to prepare and more visibility over the early stages of the kill chain but if you have a whole bunch
of fake assets if you put monitoring and logging on them if you analyze the indicator to compromise ioc's and those ttps you can generate threat intelligence you can see what they're doing and you can try and respond but the difference here is the word in front of it real time threat intelligence unlike threat intelligence from Microsoft or misp or any other threat intelligence provider you can create this in real time as soon as you see an adversary do something there's your fret intelligence you can act upon it immediately and if you've based your deceptive environment on your actual organization which is a very common but admittedly not exhaustive use case then you know exactly what you need to do to
defend against a similar attack you're not getting any irrelevant threat intelligence and so that can really re reduce the cost of triage a future instance and as I've alluded that overload can disrupt attacks there's a greater chance that someone might accidentally for instance forget to turn down map or click somewhere they're not supposed to because they're mentally overloaded and so it this basically deception reinforces the kill chain it gives you a bit more visibility and preparation on the early stages and gives you a little bit of extra defense in some of the later steps now deception isn't new right deception has been around for a while not even just in a military context but cyber deception itself comes from
honeypots most of you've probably heard of Honey Poots they decoy assets you put near a network boundary so for example we might put a honey pot here in between the internet and this external firewall the the military zone the DMZ these are inspired if you didn't know by Cliff strolls 1989 book The cooku Egg which describes how he tried to find a hacker I think he was from West German in the end I think by deploying fake systems which is exactly what we know honey pots to be the problem with classic honey pots is that they're often deployed and then just completely forgotten about you get them off GitHub you put them on a container and then you go to bed and you
call their day so they're a very very basic detection capability in most cases but in recent years we've kind of seen the growth of deception platforms we've seen the growth of actual products meant to do this thing properly and there are two particular things these platforms do that has evolved deception from honeypots into something more sophisticated we've got proper automations we have proper cloudbed automations now which means you can actually gather FR intelligence properly rather than having your CIS admin at 10:00 at night logging in and checking the logs so you can actually gather frat intelligence in real time but because of the cloud everyone's favorite buzzword of the cloud the economies of scale of
the of infrastructure as a service means you can now deploy infrastructure really cheaply and so you can now create proper campaigns lots of honey honey pots in Tandem and you can change them in response to adversary Behavior so you can actually now engage with them if you see them do something you can change the environment accordingly and that's really powerful and that's being the trend over time it's no longer machine forgotten about in the DMZ it's proper engagement with your adversaries now deception isn't simple there's no sort of one siiz fits-all approach but as I see it there are kind of three main steps in order to do deception the first is that you need to
have very clearly specified deception requirements because if you don't you're going to deploy a campaign that's ineffective cost ly probably be a waste of your time and it might actually imperil the operational security of other campaigns if you're not careful it's at this point as well you really need to be cognizant of some of the operational concerns around deception so we're going to come on to entrapment in a minute for example you need to make sure you think about these now before you go off and start designing your campaign pretty obvious next step after you've designed and deployed it you need to make sure it's going to work again pretty obvious and so we need to do some security testing
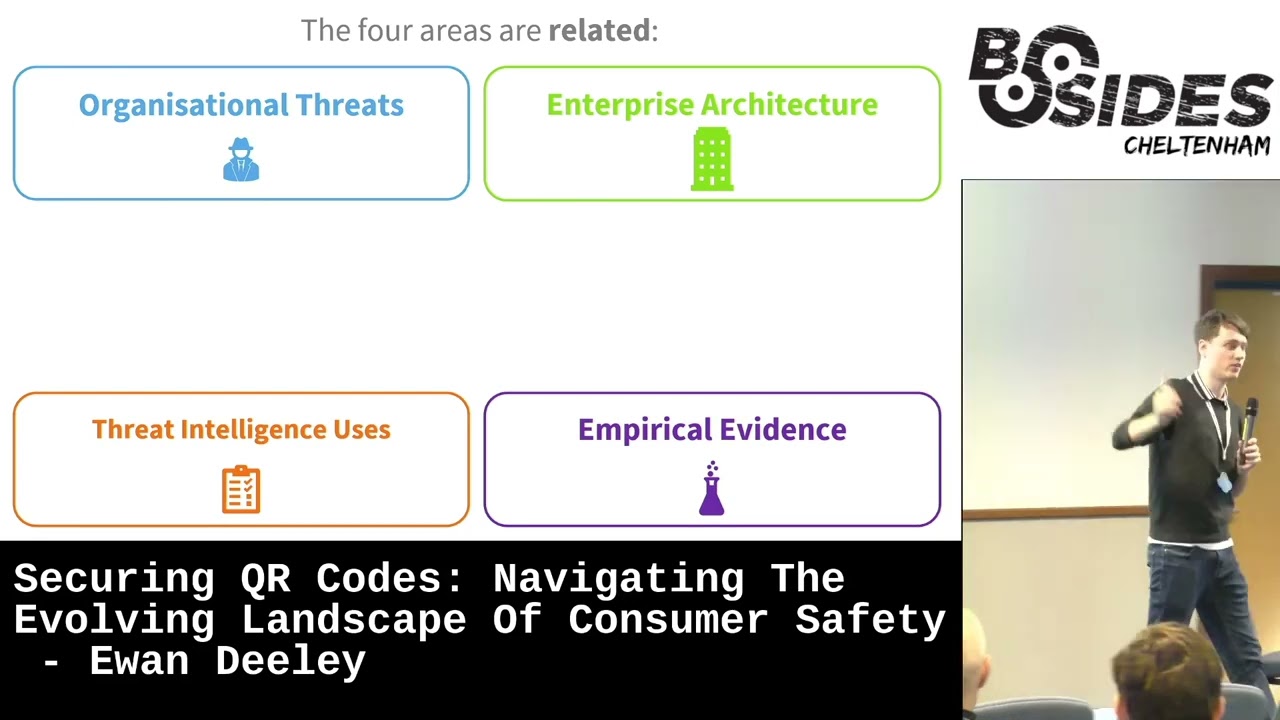
and when you've done all those things you're in a reasonable position to go live and put your campaign out there and start Gathering threat intelligence so requirements design testing these are the steps to deception in my eyes so we're going to start with requirements requirements can be a little bit dull I appreciate everyone here is probably not a product owner type role but it's really important you're well prepared for deception because otherwise it will just fall apart so as I see it there are four main areas you've got to consider to get your proper well-rounded requirements the first is that you need to really understand what the threats to the organization you're interested in are what do they think really matters to
them what do they think will really impact business as usual is it the loss of their IP is it the loss of some service they're running if they're in mssp is it the loss of personal sensitive data is it financial fraud all those things they need you need to know what they are the next thing you need to know is what does their Enterprise actually look like it seems pry obvious but we'll come on to a second why that's important but you just need a high level understanding of the Enterprise you just need to know the kind of networks they have the main servers they're running that kind of thing you don't need 20 pages of network
diagram not at this level the next thing you've got to consider is what the hell do you want to do with the threat intelligence you gather because you're not just going to put it in some kind of I know Azure storage account and forget about it what do you want to do with that frat intelligence it normally tends to be things like vulnerability management so you takee the findings to harden systems uh supporting your effectual risk management processes so feeding into like an ISO risk register Horizon scanning a fret you may not have known about so like IPS en rich with geolocation data or just supporting instant response and triage taking it putting it into your sem tool and
alerting when you see those same IPS or same file hashes again the last thing is we kind of want to know a little bit about the organization more widely have they been previously breached do they have previous alerts that they thought were a little bit interesting do they have a pen test result this kind of gives you a bit of a wider picture that might just help you when designing your campaign what's really important though is you don't just ask those questions in isolation the these are linked and there's a reason why I've sort of put these four down if you know what Frets matter to the organization and if you know what their Enterprise looks like you can map
the two together you can identify where certain threats are most likely to appear in the organization so for example if the threet was a loss of Ip intellectual property that's probably going to materialize in the dev Network that's got all the code all the secrets all the design docks that kind of thing and what this tells you is the kinds of infrastructure you might want to mimic when you do a design because as I've said a lot of deception is motivated by copying real systems so doing this mapping tells you what systems you might want to copy you also need to consider which use case of intelligence is best suited to which kinds of frats so for example
right let's consider that I'm a s an mssp and I'm really worried about the loss of my service so a Dos attack that takes it down okay I've got slas you know all that kind of stuff in place clearly using threat intelligence to support the security hardening of systems vulnerability management to protect them against being dosed is clearly the most important use case for that threet and what that begins to tell you is kind of an outline of what your campaign mod might look like so knowing in that previous example that systems being Tak taken down we want to use the front intelligence to harden them our campaign May well involve getting an adversary to
take down a fake system and in doing so they'll get the right kinds of frat intelligence to support that use case following on from that you do actually need to know what kinds of frat intelligence you're interested in right is it IPS file hashes command line activity Etc otherwise it begins to fall apart when you don't know what you're looking for that one's pretty obvious you've got to put all of this together I appr apprciate this slide is very complicated but there's a lot of questions you have to ask but if you put all of these things together you now know who you're interested in where you're going to Target your campaign you know a little bit about what it might
look like both in terms of infrastructure to mimic and that kind of narrative that kind of overall goal and you know exactly what type of FRS you're looking for and with that you can actually properly create requirements you can bullet point out exactly what you want from your campaign doing this methodology of sorts helps you draw out that information pretty systematically as opposed to being scattershot and just kind of praying you have all the information by the end product owners love these kind of methodologies and that's why we built one the logic to do that I don't have an example of requirements yet but later on I do and I would encourage you to think back when
you see those requirements to how they could have been derived following this as I said it's at this point as well you've got to consider your operational concerns and the really big one is what is called entrapment entament in the legal definition is when you induce someone to commit a crime they otherwise weren't going to do and that's fairly illegal I I'd say You must avoid doing it particularly deception is used I'm not going to say in the UK but deception is used in law enforcement and defense sectors where that is really important the line is fixed you cannot cross line of entament you've got to go you've got to avoid passing the line and that
normally involves really careful design of the lure the thing that draws your adversaries in it's what's known as a breadcrumb we'll see that in a second where you put them and how they're designed is really important if someone incidentally comes across them and they if without the intent to commit a crime or attack that breadcrumb mustn't suddenly make them go oh I think I'll go hack this and make money if it does that you've caused entrapment the other a little bit simpler isolation should be pretty clear you don't want people to be able to laterally move from deceptive environment to Real Environment and you also need proper playbooks to deal with what happens during the life cycle of your campaign
if it's attacked who do you tell what's the lines of communication how do you report that you don't want your sock team to start having a panic because they think the real systems are being attacked when they haven't but you do want them to be stood up so they're begin to analyze the threat intelligence so we've got our requirements we've gone past the product owner role now we get into the fun stuff which is actually designing a campaign there's a couple of key things you have to put together to make a deception campaign you can't just deploy some machines and sort of have fun for an evening as I've alluded the first kind of building block of deception are your
breadcrumbs as I said it's that initial lure that kind of draws your adversaries in okay and these can be anything so long as they're just relevant to the context can be credentials certificates QR codes a USB stick I kind of just leave on the floor in the office that's also a valid breadcrumb honey tokens are a really important one and I want to highlight them now they are documents that when they're opened send an alert to a sem or a sock team and you can imagine how powerful that is and useful for deception if you want to mess around with them online Canary tokens you can make them yourself pretty fun overall to mess with breadcrumbs Point towards your
deceptive assets your actual campaign and Assets in this case just refers to the actual infrastructure okay so these can be laptops servers virtualized equivalents whatever key thing is though is that if you deploy windows don't modify it at all and put the creds online that's not deception no one's going to fall for that they might hack it anyway cuz you know fun but it's not deception so you've actually got to make machines look look like they're being used and got to make them look like they're real so you've actually got to install programs on that machine to generate an interaction with your adversary you've got to put stuff on there for them to interact with and so deceptive Services
as they're described are just regular programs okay office engine X git MySQL whatever you use in your organization are usually valid targets for services when your adversaries interact with those Services that's when you get your frat intelligence that's what kind of pull keeps them pulled in it's that dwell time as it's described really important don't just deploy Windows VM and forget about it CU that's a really crap honeypop basically but another really important thing is they've got to look like they're being used and this is where what we call pocket litter comes in so pocket litter is just artifacts you put on the machine to make it look like it's the environment's lived in but aren't
necessarily intended to draw a reaction from your adversaries because breadcrumbs draw people to to another asset they move you know that's what gets them to do something these artifacts don't are not intended to elicit a response they're just there to make it look real company documents Excel spreadsheets at random numbers that don't add up photos of friends and family you know whack out your chat GPT that's the kind of thing you use to make pocket letter what underpins all of them what underpins all of that is telemetry and your automations just like in a real organiz ation where you'll have an EDR tool that collects data from your from your laptops from your endpoints to see if
something bad's happening you need to collect your indicates the compromise like your IP um data command line data change to the registry file hashes all the typical same things you need to collect from your machines but you've got to do it in a slightly hidden way because if an adversary logs onto the machine and sees deceptive service.exe running probably there going to think that it's not real so commercial tolling will often use rootkits and your typical process hiding techniques which I'm happy to talk about at a later time just not now because they're complicated to reflect adversaries away from trying to discover the agent when you get your data just as you would in the normal C tool you also need
to set up alerts reporting automations to do things in response to different events really important because that usually forms the bedro of actually creating actionable threat intelligence as we'll see in a bit but that's it red crumbs machines Services pocket litter and then some sort of backend technical work that's all you need for deception but of course what really matters is how you put it together now there's a couple of methodologies out there for how to put together deceptive campaigns but the one I I think is the simplest is something called see think do what what an adversary sees makes them think in a certain way therefore they'll do something now that might seem a bit sort of silly because that's just
how our brains work but it's true an adversary will do something in response to what they're seeing and what they're thinking but the problem is if you follow this this methodology in that order your campaigns won't be very effective because you framed it in the wrong way because you've started by thinking about what they see rather than what you want them to do and what they do is really important because that's what actually generates threat intelligence and if you followed it in this order they'll do things on not expecting you'll gain random crap from your frat intelligence and it won't be helpful and you'll have wasted your time so instead we follow it in reverse Simple Solution we start by
thinking about what we want an adversary to do and that question has already been answered for us because we just derived very good requirements that explicitly Define what we want them to do that's why we have that slightly onerous requirements capture methodology so that question is already answered using that you know what the end objective is you can use typical red teaming resources like attack trees and like to formulate a path of lease resistance for adversaries to follow effectively you can start to determine what you want your adversary to do to start reaching the end objective you've got to make sure that the adversary takes the action you want where possible you've got to manipulate
what an adversary is thinking so what they believe is their next logical step aligns with what we want them to do and so that's making sure that the attack path you pick is credible it's clear is realistic it's not made up that kind of thing so again if you're good at red team and ethical hacking you simply start basing campaigns off what you've done in the past if you've hacked act active directory make a campaign that's based off of how you manage to compromise the domain controller and exfiltrate data off Services right that is really really key the last step then is to Simply put the right Assets in the right places to enable that you've got to make sure that
an adversary sees what they're expecting so if they're in an OT environment that's operational technology that's things like plc's and power plants and the like don't put a printer and a scanner in that Network because that's just a bit weird and that might throw them off make sure what's in your environment is predict as it were it should be what they expect to see now I appreciate this probably still sounds a bit weird anded it took me an attempt or two to actually understand this methodology so I'm going to move on to an example which hopefully might make it a little bit clearer I'm going to introduce to you the Cyber Broadcasting Corporation I couldn't come with a
proper slogan so I just came up with that they make television shows about cyber which people watch for some reason and apparently they think they're part of a very competitive industry right they've got some very Cutthroat competitors the problem is they're a bit of a crap company from a security perspective ironically because they don't actually really know who who's targeting them so they want a campaign that will help them understand what threat actors are interested in them but they also want to understand what types of data those threat actors are interested in how they find it and in what they with it so they can therefore improve their security posture in that respect a little bit of additional
information about this fake company we're going to assume they're hybrid Cloud so they have on premises active directory and enter ID in the cloud don't worry if that doesn't mean too much to you it just means there's going to be some infrastructure that we have to do in order to support that assumption and their definition of sensitive data in this case is they're worried about things like you know edit scripts a roll B Roll Show that still being edited like Final Cut projects contract uh Talent contracts that kind of thing they're not worried about personal informational data in the scope of this campaign so those are requirements they want to know who's interested in them
and what they do with any sensitive data they come across so what's really important about see think do when done backwards is you've got to start from the end so on this slide in the second as we fill it out we're going to start here on the right and we're going to work backwards to the beginning on the left okay so we know what we want them to do we want them to exrate some sensitive data so at the end of our campaign will be some fake servers hosting fake data so we're going to have a NAS network attached storage hosting fake footage scripts you know get the interns to make some crap you know you wouldn't air it anyway
don't you use it for deception why not and on another server we'll have things like contracts legal papers maybe some ransomware insance documents for example that kind of thing just as on the side I know docu sign can't be used on premises anymore but it illustrates the point a bit more easily rather than some tool no one's heard of so let's pretend you can use docy sign on premises it's a sass product now only unfortunately okay we got to think how do we get to those Services well we're on premises so we're going to have some kind of employee workstation okay we're also going to have the underlying active directory stuff behind it because again
that was our assumption so this workstation we're going to put stuff like office and teams on it because that's what regular people unfortunately have to use in terms of breadcrumbs that are going to lead them across we might have an active browser session to one of these like tras for example we might have some personal documents with a password that they've you know forgotten to delete it's pretty common those kind of breadcrumbs will draw our adversaries to these Services however it's worth noting that adversaries are unpredictable no matter how hard you try to kind of pen them in so you normally have a backup attack path just in case they really go off the rails and so in this case active
directory if anyone here's done active directory pen testing a lot of people will go in think it's called blood hound they'll start enumerating everything on the on the domain controller they won't even bother looking at the machine they'll just startop running their scripts so we will enable that use case because we can have adversaries compromise the domain controller compromise the authentication and get to the services that way that's still useful for intelligence but frankly we prepared for it so there are two clear and credible ways that we can get from here to here okay what do we need to do to get into that workstation well it's going to be a VPN right that's how you usually access
these kind of networks so there we go server open VPN on it pretty simple but what's really important now is how how do we get people to come here knowing that we want to Horizon scan different types of threat actors we can't just deploy one set of VPN credentials and the certificate it's https CU they're good security kind of we can't just deploy one because that won't really necessarily tell us enough different types of threat actors it will tell us that maybe one person has tried to use them but it won't tell us much more than that so we're going to deploy multiple sets of credentials across different dark web forums because they're the kind of threat actors that
are usually external we'll have different forums with people the different kinds of people gather on with different intents different types of threat actors and what's really important is that we set up the alerting and the reporting around this if for example we have one Dart web Forum that attracts people that like to extort companies let's say their credential set number two if we set up an alert that triggers when they log into the vpm we can then track what they are doing across the environment so we know that for example people who want to extort us are going to come in they're going to use the credentials they're going to do this this this this this and they're going to
exfiltrate these kinds of data and they're going to do whatever with it that's enabled particularly because these breadcrumbs are going to be honey tokens so we'll have alerts when they're opened from somewhere outside the Network that's that's actually very important a lot of people forget to make they'll create the right types of breadcrumbs but won't enable the the reporting from them which is quite a a bad mistake to make so that's really it to be honest the other thing I'll mention is that commercial project uh products will have proper monitoring visibility across this so you can see the network traffic and C file system activity Etc but if you've done this manually you'll need to set
that yourself otherwise that's it for this campaign I appreciate this might look like a complicated slide but in reality we've got what four machines and maybe five or 10 breadcrumbs that's all you need you got to keep it simple because there is a principle of diminishing returns with deception let's say I wanted to flesh out this active directory I'll make hundreds of workstations I'll Network them together I'll have lots of subnets I'll make it look like a real big Enterprise but there's no point because that isn't going to really give you any relevant intelligence to this end objective most likely and in doing so you really run the risk of making the environment not seem credible enough and
if that happens adversaries are simply going to leave and move on there's always a point in a campaign where an adversary will think it's deceptive and that's fine so long as it's here after they've done all of what you want them to do and after they've given you all the Frat intelligence you need I have a colleague at one of the companies we work with that describes deception as a stage play where it looks completely fine if you look at it head on but if you look at it from the side you begin to realize that that tree is actually a poor boy from year seven that Castle's being held up by a little wooden rod
there those clouds have got strings it looks real to a certain point and that point is enough to get the intelligence you need I'm going to I'm going to show you a different scenario now let's imagine for a second that all this organization wanted to do was understand the threat actors that are interested in them that's it this second requirement is now gray out all we need for that campaign is the things on the screen breadcrumbs the VPN and the reporting of of valid logins that tells us who's interested in us that's it because we're not interested now about what they do after that and so what this actually exposes is what I describe as the sliding scale
of deception design because you can have those really big complicated multi-step campaigns that are across it and OT environments you know hundreds of machines fine but also you can have something as simple as that because that will give you useful frat intelligence based on the requirements in fact at logic we're going to deploy a campaign that might even just be a couple of breadcrumbs that are highly instrumented that's all completely valid so long as what you're doing satisf your requirements so we've now seen how you kind of build a campaign we start by thinking about the end objective we worked our way backwards we made sure that everything had a clearer you know link to a
requirement but now we need to test the campaign to make sure it will work before we go off and blast it out into the internet and this is where security testing is really important so I advocate for using purple teaming for this say purple teaming is a combination of blue and red teams just in case you weren't sure that does make purple I believe the blue team is going to be interested in the defensive testing of a campaign the red team is going to be interested in the offensive testing of a campaign so the blue team is going to be concerned about whether the campaign produces the Frat intelligence they were expecting have they set up the rules and
the reporting correctly have they integrated it with other products like their their s tool correctly that kind of thing if you're interested in IP addresses are you getting valid IP addresses what's sort of tangental to that is the notion of visibility which is a very important network security concept and it's very important here you need to make sure that at every moment you can see upon me what an adversary is doing if they do something and you have a blind spot invis visibility that's a problem because if that's a crucial step and you don't see what they've done no threat intelligence for you if you're using a commercial tool they'll cover that for you but if you've
rolled this manually again you need to doubly check that to make sure it's true on the other hand the red team are focused about whether the campaign is credible does it look like it's of appropriate value to an adversary is it realistic is it enticing does it follow a credible and clear attack path that kind of thing so they're interested in making sure that it's actually adversaries want to reach the end of the campaign and then tangental to that is simply whether they can um because the amount of times that people will create a campaign and then not configure firew Wars or network security groups correctly and then you can't reach the end because you can't see the next
machine is quite common so there's that kind of also banale aspect of just testing whether you've actually networked it all up properly for example but what purple teaming is in particular is doing both of those in parallel so you you stand up a blue team writes your sock okay and you stand up a red team so people who ethical hackers who haven't seen the design instead of running this and this separately what you do is you get both to do their activity at the same time so you'll have like daily standups where the red team you know talk about what they're doing The Blue Team talk about they're seeing and at the end of every
week for example you have a wash up where both teams talk about what's happened they share their insights they share their knowledge and in doing so you draw out proper Camp uh proper insights about whether the campaign is working as it or will work as expected purple teaming is common in Enterprise now I know government do it hmlc does purple teaming so long as you do it properly it can be really really valuable to testing a campaign but if you think back for a minute if you think about this tiny little campaign here in our second example do you really need to St stand up a whole red team to test that probably not you do need to stand
up your blue team or some of them at least but you probably don't need to hire a team of seven pen testers from KPMG to do that so here automatic testing with tours like M Caldera is actually really helpful so Caldera is a tour by MIT it's open source just like the rest of mit's things and what it lets you do is basically create fake adversaries sort of programmatically so you create an adversary which does a series of things each of those steps is like an attack path so um enumerating over files finding a machine to Lally move to running an exploit Etc you string them together you put an agent on one of your machines and you run it done
so in this example we would simp we put a an agent here that tries to log into the VPN that's it and then we check if the blue team can see that activity so if you've got a small campaign where possible you should consider automated testing it saves everyone time and money cesos love money so that kind of begins to bring me to the end and I hope that this has been fairly interesting deception is we're quite a multidisciplinary area because you need people who are good at Blue Team stuff you need people who are good at Red Team ethical hacking you need good product owners to um derive good requirements you might even need a bit
of a criminological aspect okay so I I studied one criminology Crim criminology module it's very complicated word at University so you want those all those different kinds of viewpoints and insights but before you can run off and delve head first into deception there are a couple of prerequisites okay as I said at the beginning deception reinforces the kill chain it doesn't replace it so you need to have a good security posture before you run off and start doing deception right you want defense in depth across all those different types of areas you want to have good auditing of controls risk management governance all the things that any of the Consultants here in the room are probably going
yes you need all those things and they need to be in good shape the analogy I like to give it' be like if the kid in Home Alone right he puts all those traps around the house to get the robbers attention you burns the the door handle and whatnot it'd be like if you did all that but then you left the front door and the windows open what's the point they'll just get in that way you need to make sure your security is as robust as possible before you run with deception but the other thing you need to be somewhat good at is dealing with threat intelligence if your organization can't handle frat intelligence if they don't
know what the hell to do with it once your deception creates it you your use of deception will be a waste of time and money and as I said cesos love money so it's really important that your organization can deal with threat intelligence before you run off and do deception otherwise deception turns into like a really expensive early warning system you know you get an alert when someone touches the the VPN but you don't know what the hell to do with the information after that but of course what do I mean by being mature you know at an entry level right an organization they'll have a Sam tool they'll automate analysis they'll maybe ingest tactical intelligence
that's things like IPS file hates Etc an organization really good at threat intelligence will have they'll generate and ingest lots of types intelligence from lots of sources they'll have a clear risk tolerance they'll have a clear set of objectives for their use of frat intelligence hence if you recall we ask about their use cases ahead of time they'll have proper analysis both manual and and automated and they'll always be improving their you know that sort of CTI program of sorts cti's cyber FR intelligence an organization needs to be somewhere in between these at the very least before deception is recommended and that's really because there's an issue of proportionality here this is completely out the realm of of interest
for something like a small charity all right small Charities it's going to be cyber Essentials and cyber Essentials plus but if you're a large organization you've got good security you've got good frat intelligence processes deception May well be up your alley I'm going to take a brief minute just to talk about a slight tangent since I've got the time this entire presentation so far has been focused on Enterprise use case so organizations seeking to improve their security in some way with deception but it's also completely possible to use deception in a law enforcement environment to use it to deter cyber attacks the way you do that from a technical perspective is no different you will deploy campaigns in the same
way the difference really just stems from where your requirements come from because in a cybercriminal context there's no organizational threats that you need to consider what organization is there likewise you don't have an Enterprise architecture because there is no Enterprise you're doing it for so in those cases your organizational threats are instead going to be the cybercriminal landscape what groups do we want to Target and why is it because they're really prevalent is it because they're using zero days and we need to understand it really quickly and then an Enterprise architecture is actually going to be instead a mockup it will be an archetypical architecture for the kinds of businesses that those threat actors are
targeting otherwise the rest flows through the use case of intelligence will normally be you know deterrence they'll want to for Gather things like IP addresses they can go off and do takedowns or try and arrest them rather um futile effort but you know try and arrest them that kind of thing otherwise in a cyber criminal context deception is pretty much the same entrapment becomes even more important though there and that's it we've come to the end of my kind of Whistle Stop tour of deception so I want to thank you all for for putting up with me for 42 43 minutes that's very impressive some extra resources just on the on the right just of Interest
miter engage is a proper like miter methodology for this there's a lot of emphasis on the prepare phase in miter engage hence why we spent 10 minutes on requirements capture joint publication 33.4 that's where Deception comes from in a military context so that's where CD is derived from that's a US publication you can just Google that because it's quite old now and then at the bottom I've listed there a couple of commercial projects so I mentioned Canary tokens there is an ongoing effort to try and use honey pots better and that's the Honeypot project and then the bottom two are some commercial projects which may be of interest if you want to do deception for your
Enterprise and with that that's it so feel free to reach out on LinkedIn I'll be around for the rest of today so you can obviously come and find me if you have any more questions but we've got about seven minutes I'd say so far away right you there yes
Absolutely I'll repeat the so it's visible in the in the recording so person was asking about what if an adversary is tipped off to the presence of deception you know they've got reasonable you know Reasonable Doubt and they start making noise to kind of throw off the campaign throw off monitoring and basically cause problems so that is always a risk okay there's always a risk that theary will detect deception early and so normally in the prepare phase in mitro engageed is a really important bit about the The Rules of Engagement the red line that when it's been crossed you call off the campaign because you think it's no longer effective in that you will consider technical risks like that
campaign is turned into a bot net and people start being attacked by us and it doesn't look good but in there what we it's called validity checking right and as part of that noise is a relevant tactic in that a lot of the commercial projects will have aut automated rules and reporting to deal with that use case when they when the tools think and adversary has detected the presence of deception and is starting to try and subvert the campaign I've not seen seen it yet personally but it's not say it's not it's absolutely is a reasonable use case and in that case if you've got a properly defined campaign where you've got the proper monitoring around it you
can still see what they're doing it's at that point you're going to need to really stand up your sock team to really start filtering out the noise but in any case if you got a proper campaign they can try and add noise but what they're doing should always be visible and if it isn't we've got a problem as we said from The Blue Team side so very good question anyone else you the red shirt down
left okay yeah cool so person was asking how do you get buying from this from the dreaded seeso I've mentioned um I love seeso as you can tell it's about demonstrate generally cesos are interested in value for money right can you for example if you deploy decep could you save two or three so analysts the deception itself very rarely presents an additional technical risk if unproperly so that proper isolation of campaigns Etc but poking the bear is an interesting one because you don't want if your if your organization's a bit kind of on the lowdown and not really well very well known if you start spamming credentials online then yeah you're going to start making
noise the it depends on really whether the risk outweighs the benefit so depending on the requirements and of that campaign are you going to gather really use frat intelligence that would outweigh the possible risk of drawing adversaries to admittedly a fake environment but to you know your organization it tends to be the case for a lot of big organizations where this is relevant because again for small ones out the question they've already made enough noise that people know who they are so you're not really poking the bear as S as such because the bear has already been poked as it were if you're a very big organization like Microsoft everyone knows who they are everyone's already
trying to Target them putting up another deceptive campaign to try and extra intelligence isn't probably going to present additional risk at that point because everyone their dog and their dogs already out after you so it really depends there's also that related risk of entrapment where again if you're not very big you don't make a lot of noise you don't want to draw people in and entrap them but generally it's whether the risk outweigh is outweighed by the the cost savings and whether or not you are drawing people to you who you may not otherwise have been interested in you but in most cases you're big enough to use deception you're probably already aack okay do we have any time for one more
yeah we'll one more you at the
front yes there's a question iting to be asked I was asked you at bze London so this is about the playbooks that commun lines of communication if you are hit by an attack in a deceptive environment and it starts Making Waves you do have to deny it okay you do have to say look this was a simulated environment you know setion whatever you want to describe it as you do have to obviously discredit those reports because otherwise you'll start suffering reputational damage or even if you've got an accreditation that might be imperiled right you do have to dis discredit those those claims but that it's actually a good thing and it doesn't really have much of an impact
because there's an interesting sort of debate in terms of like paper on this about whether if you tell someone something might be deceptive whether it's actually going to have any impact on its Effectiveness generally you can you could for example on on on on buntu you know you can log in and have the bash login message appear you could put this system may be deceptive we are partnering with X and that will generally have no impact on an Apper Behavior or if it does it'll be positive I.E they'll begin to make more mistakes that kind of those psychological effects you mentioned earlier so generally if you're hit by an attack on a ceptive platform you should acknowledge it it
generally won't be too adverse and actually it may be positive of course you will have to rotate out that campaign new IP addresses and the like Etc but it doesn't mean you can't do deception anymore you should absolutely not let yourself get bullied online you know you should absolutely own up to it and the Ben there are benefits to doing that I think that's pretty much it so yeah so thank you all so much for listening I'll be around for today if you got any more questions I can show some examples of specific campaigns on specific platforms forms if anyone's interested but yeah thank you all so much for listening and have a good rest
of the conference





