Red Teaming The Board

Show original YouTube description
Show transcript [en]
[Music] right thank you for coming everyone today we are going to talk about red teaming the board or bringing red teaming principles mindset etc into senior executive service so this is not necessarily a technical hard skills hack your hack your way out of a box kind of talk it is about winning political capital in order to do the important things that we have security teams and practitioners need to be able to do so first things first Who am I so I run the security and compliance teams at nuna and we are a health care analytics company based out of San Francisco I used to run the Red Team assessment services at a consultancy called digital and I used to
break a lot of things myself I was a former pen tester and red teamer I spent a little bit of time on the digital forensic side of things and a massive Batman fan I've got sleeve I've got a suit anyone in my life will tell you that I'm I'm a fanatic and so kicking things off our agenda for today basically I know everyone everyone here probably understands the benefits that red team testing or penetration testing has on a business or a system or a team that's never really gone through the process of you know engaging with with security professionals and you know finding a lot of issues in what they're building and so it's great for just
blowing the lid off of things and calling a lot of attention to to the problems that you're trying to solve but as practitioners we end up having a nasty habit of plaguing ourselves of shooting ourselves in the foot and I believe we do that through through many we through many ways but two through two primary mechanisms and that is we end up talking a different language than a lot of the other counterparts a lot of our other counterparts and colleagues across organizations do when it comes to risk management and then on top of that we tend to hyper focus on one with a little bit of splash off dimensions of this big complex system that we're trying to fix
that is security and so throughout this talk we're going to focus on three primary things and that is figuring out what in the world is actually important to your business so that way we can talk the same language when we're when we're communicating about risk management you know we can't just come to them always and say you know you have to fix this because the security team said it's important you know they may not care about what the security team has to say it might not be relevant it might not be a moneymaker for them or they might they might be willing to accept the risk of having a cross-site scripting in a marketing app that nobody really uses or
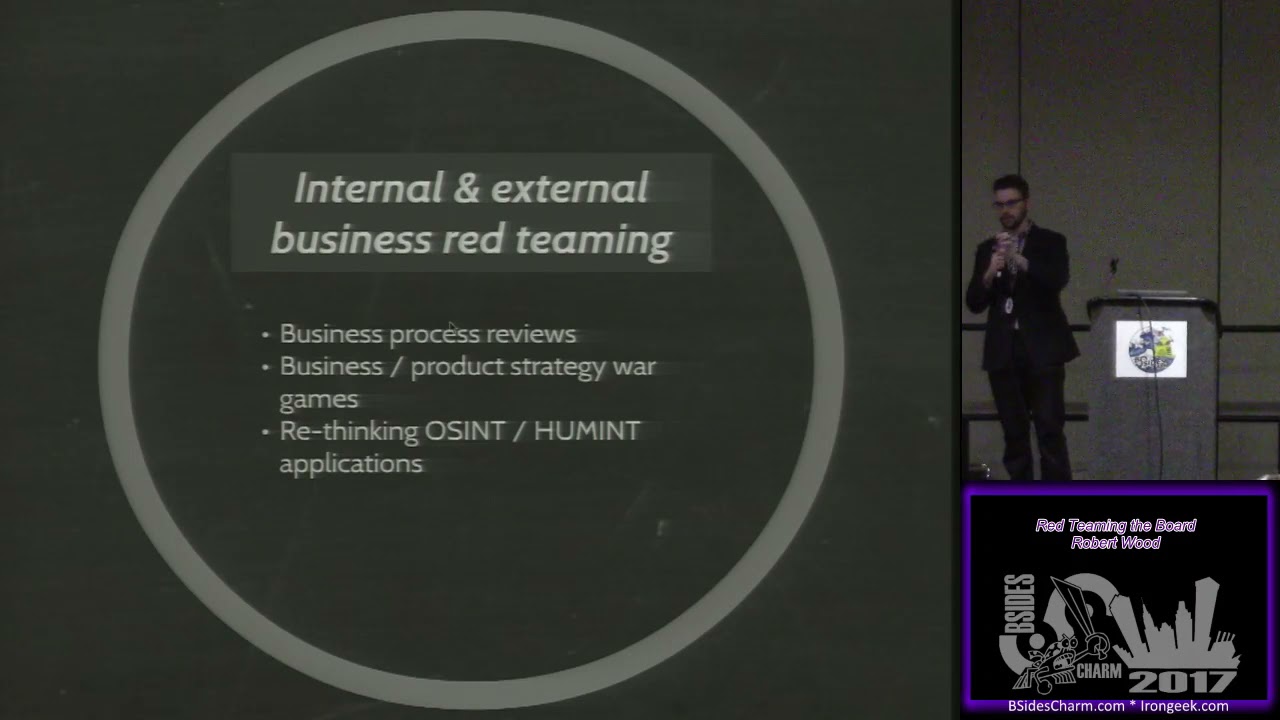
where there's no real engagement something to that effect you end up seeing this all the time and like entertainment studios and stuff like that and so figuring out what's actually important to them so that way we can connect the dots that we need to connect the next is actually bringing some of the techniques in the mindset that we have as security professionals particularly on the on the offensive side into those those business oriented circles and so we can do this through three main ways first being looking internally at ourselves at various business processes that are running the organization the next being looking at how the the organization or how business units within your organization interface
with with the market around it with its competitors with its adversaries and then the third is building goodwill within your organization by teaching teaching others to think like we do or you know spreading spreading the love if you will and so all of these things are really geared around what what can we do to better align ourselves with our with our partners throughout the organization build goodwill that we can use down the line and then if the last part here is reframing the narrative around why security is important at an organization so of all the big companies that have existed over time that have kind of fizzled out and gone away we I don't think we've ever really seen an
organization pop up on the radar be a massive fortune 500 organization and then just get wiped off of the map because of a security incident you know we have a we have a tendency to the claim to make these these statements that you know security is one of those things that can just completely derail and destroy a business but we've never actually seen it caused more than Blitzen stock markets blips and revenue drops things to that effect and so in order for us to really get people to listen to the things that we're doing you know we have to reframe the narrative around actually adding value to the organization's we're working with and so you know I believe that when we do that
we can start to reduce risk at a more macro level and not just on these these very focused point in time you know patching servers getting people to stop clicking on links things to that effect so stepping back before we zoom in in order to figure out where we want to go I think it's important that we take a little bit of time to reflect on how we got to where we're at where do we stand today a little bit of a history lesson so as many of you probably know security is considered a cost center in many organizations we end up investing a lot of time energy resources money on products on tools on headcount etc and
then we ask other organisms through out our organization to do similar things you know to fix security bugs to patch systems to to reinvent their own processes so that way we can we can all be more secure as an organization and we end up being hyper focused on the issues that are right in front of us so you know that that sequel injection is present you're in this web application you know I'm able to do pass the hash attacks in in your in your enterprise I can run you know I know that some malware will trigger on will execute on this endpoint you know those issues are very very important to us but they may not be very
important to the to the stakeholders that we're trying to interact with and and as a result of that we you know the narrative that we end up being a part of or that we end up setting ourselves kind of dictates that our issues are more important in some cases than the than the issues that other teams are dealing with and that may or may not actually be the case and I think the reason for that is that language disconnect I mentioned earlier and so when I started off my career in security and I know this is true for a lot of people who end up starting their careers in this in this industry is that we we end up thinking
that you know our our technical prowess the things that we're finding are going to are going to woo the B team so the people that were reporting this stuff into fixing them they will listen because the issues are that impressive and what actually ended up happening was you know you start bringing these reports to clients and such and it ends up kind of backfiring around you backfiring on you if you bring a solution to a team it's way too complex to implement they're going to laugh you out the door or they're going to say yes thank you very much we've checked our box and we're going to go away you know you can go away now and we're never
going to look at that again and so we obviously don't want that situation that happen because it doesn't really help anyone except for the box checkers that that exist in the world and so to actually think about the language disconnect so has anyone here ever gone to a foreign country and not spoken the native language of that foreign country yes so I recently went to Italy and when I was when my wife and I were traveling around some of the more established areas like Venice and Rome and Florence they're very heavily very heavy English speakers over there and we had a very easy time getting around when we made our way down into naples and pompeii it
was not so much in english-speaking part of Italy and I ended up making a complete ass of myself as I as I kind of wandered around the the city trying to find certain things trying to we got disconnected from our from a tour guide at one point we're like sprinting around the Sprint's around the pompeii ruins trying to find where in the world we're supposed to be going not really being able to communicate with anybody and so we have certain terms in our industry that that we use a certain way and we don't even really agree on these things across our own industry like for instance when I say something is high-risk what do you think of when I
say something is high-risk yeah
okay so the answer was there's going to be a potential for an attack towards that thing how about you what do you is it okay so financial impact how is it going to cost me you know what it what about you know the time to remediate what about the likelihood that something might happen you know so there's there's very specific terms or ways in which like financial financial risk modelers think about terms like this and you know they're very quantifiable they're very easy to understand but the way that the way that our industry tends to think about these kind of terms is in a more subjective qualitative fashion and I feel like that is one of the one of the
reasons it's a little bit more subjective in the sense that when I say something's high risk it might mean something very different than if a colleague of mine says something is high risk and so we end up confusing people and so I mentioned before we end up tending we tend to hyper focus on things and so what I meant by that is we end up hyper focusing on technical issues that impact security so you know go to any security conference this one included and it's not necessarily a bad thing but we have a lot of research and a lot of effort and emphasis being poured into the technical issues that are actually you know that are enabling security
issues to to be a thing and then we we tend to focus a little bit less on the social aspects of security ie you know humans keep clicking on links social engineering is a thing that continues to plague the industry it kind of there's a there's a nice little feedback loop that exists between the technical dimension and the social dimension that people are focusing on but there's not nearly as much research and this is starting to change slowly but surely but there's not nearly as much emphasis being placed on some of the other factors that can go into influencing the way that people might care or think about security such as mapping it back to as this gentleman
over here said financial risk so if it's going to cost the business more money to not fix something than it is to fix something then it's a wise investment for them to make you know if we can start to think about legal factors if you can connect the dots between something that might be a regulatory requirement or a contractual requirement that you're going to be out of compliance with and that you use that as a driver then that might be something that that you can use to gain better leverage on the stakeholders you're working with and then I mentioned this before but security is a business problem so we've been talking in recent years about
wanting a seat at the senior executive table wanting a seat as decisive or you know having our sizes and our sea levels have a seat at the executive in the in the boardroom and the executive strategic discussions all of that however you know building on this you know a lot of our a lot of our research and our efforts doesn't really support reward and cultivate that kind of that kind of thinking and so that's another thing where I think we need to start thinking outside of the vacuums that we currently operate in and maybe start maybe start going after and trying to speak trying to engage with trying to to involve you know developer developers IP
quality things to that effect so conferences that and this the spans way beyond conferences but as an example you know talking about our research in those settings might help to you know stir up some interest in those circles and start to bridge some of the gaps so the best way of course to predict the future is to create it and a management consultant slash author called Peter Drucker named Peter Drucker one who said that originally if you guys have not read him or anything that he's written I highly suggest it especially if you're interested in maybe the nerdy business stuff and you know basically what that ends up getting at is you know we are
working in the organizations we work in we're a part of this big massive ship we're helping to steer the ship where they're helping to man the ship when things start to go crazy we can inform the direction that our industry and our organizations end up going and so this this talk is going to primarily focus on fixing things or improving things rather from a political and an organizational perspective within your company within your organization not necessarily as at the industry at wide level and so three dimensions that I'm going to focus on along these lines the first being that look in look introspectively look internally and so for anyone who has ever read the simple sabotage field
manual which is a Declassified doc from the CIA there's much more interesting things from the CIA to read as of a couple of days ago is this this document basically describes the mechanisms that the CIA would use to to inform destabilize foreign entities such as terrorist cells or foreign governments and things to that effect and what it basically if you read through the short guide it's basically modern bureaucracy its knowledge silos it's it's red tape and ironically a lot of that exists that are in our own in our own government system but but these are the techniques they try to instigate in order to cause cause entity governmental entities to go awry and so in order to stop falling
victim to some of the same some of the same issues I feel like we can as security professionals look objectively at business processes and streamline them and I'll dig into that a little bit more and the second one as I mentioned before bringing our red team hats into these senior executive circles and so show hands how many people in this room can think about or can conceptualize a adversary other than a hacker that could just completely destroy their business or just completely throw them off caused them a whole lot of dollar value loss this one shows of hands so things like an adversary could be something like a competitor it could be something like a
driving market force it could be something like like a government so for us in the healthcare industry you know we are as I'm sure you're sure you're kind of putting together you know we work on health care data we work in federal spaces and of course some of the governmental changes being proposed right now could potentially negatively impact our business and so that's something that we need to think about from a from an adversarial perspective we need to look at entities or organizations etc who might negatively impact us and try to foresee and plan around them and so you know we as security professionals we're very good at conducting simulations around when bad stuff happens and how it happened
and demonstrating that to other but other people our colleagues in our businesses might not be as well equipped to actually kick off or plan or think about some of those simulations and so I think that's another area that we can potentially bridge a gap in health and then the last one as I mentioned spreading the love and so I'll dig into that a little bit more in the dedicated little section so starting out first things first we need to figure out what is actually important to the organizations that we're working with we need to figure out like any good security assessments begins we need to start doing reconnaissance surveillance intelligence gathering thanks for that effect we need to figure out who the key
players are what the key processes are where the money flows what's making money why we're actually doing what we're doing what we're spending money on thanks to that effect and so you can gather some of this data by looking at things like your org chart reading company memos are all you know all all at emails things of that effect but just because somebody might be in a certain place on an organ org chart does not mean that they may not it does not necessarily mean that they have all the influence that they're making all the decisions or that they're the ones actually determining what's important to the company and so some other ways that you can think about figuring this stuff
out it's like who's talking at All Hands meetings who's who's most frequently you know circling or bubbling up in these in these social venues you know who is who has a large following of individuals you could probably spot them if you you know if you sit back and think about it especially in a smaller organization and then the last thing is to try to try to check yourself in and see who of those people are outside of my normal purview who is outside of engineering or IT or you know whatever whatever department security is slotted in in your organization and then when you have those when you have that list you can start to map it to things like what's
actually important to them so pull together documents that those people have publish or their departments that published and start you know meet with them talk with them listen to things that they've said and start to figure out what execs are they tracking what KPIs or key performance indicators or okrs objectives and key results are they tracking what is it that's going to make them successful or deem them unsuccessful at their business and if you can figure that stuff out then you can start to systematically put together a plan of attack for how you can for how you can help them how you can start to connect dots alright so next thing looking internally so the business process
analysis you can think about this like threat modeling but applied to a business process and a business process might be something like I'll use our own security team as an example in our in our process or in our case it was something like putting together an S DLC for how we engage with engineering teams you know what controls do we want throughout that SDLC where where are there certain decision points that need to happen around whether something gets released to production or doesn't or goes back to tests or goes back to to an engineer to fix you know where can we insert certain automation tests or manual code reviews or manual pen tests or a third-party verified test
thanks to that effect and so if you if you can enumerate based on based on all of this what those critical things are happening and where they're happening throughout your organization you can go meet with those individuals and actually figure out how these how these business processes map out it might be something as simple as a flow chart you could just whiteboard it you know take an hour whiteboard it talk talk through all of these things and you know map out the attack surface of that business process figure out who the players are involved who the players the key players that are either you know sending things in or taking things on the way out or you know
influencing them in between that and then you can start to dig into how and where risk creeps into the end of the picture and what that might look like is where you know where you have might have certain break points ie a process could go completely off the rails and there's nothing there to stop it and if you can enumerate ten break points and you only have one control and that controls as a policy with nothing to back it up then that business prend that business process is responsible for you know a lot of money or a lot of efficiency or you know brand reputation things to that effect then then you could probably consider that to be
something very very sensitive and you know worth some additional follow-up and so when we did this at nuna we started internally to our security team we mapped out all of the critical business processes that we had and what we found is even as security practitioners we ended up having a lot of things that were designed poorly that you know were not bought through extremely well you know they were missing certain certain controls when we when we broke them out like this and and we were just kind of wasting money and time you know whatever whatever way you want to classify resources but when we started to branch this out to other to other departments you know we started on a department to
department basis we just basically broke out our org chart we said who are who are the most critical P people and departments and teams within this organization and we're going to start at the top of the list and we're just going to slowly but surely work our way down and that's exactly what we did and when we started to actually do this you know we're helping people map this stuff out what we found is or was we didn't actually end up having to own a whole bunch of things which is fantastic because you know as I'm sure your own security teams are they're probably over stat or overtaxed understaffed they've got a ton of stuff to do your backlog is
probably months and months long or months and months out and you have no idea how you're going to catch up without with it all that's pretty difficult for many many security teams out there and so we did not want to take on more ownership but if we could spend you know ten percent of our time doing things like this doing some of this business focus stuff and we could get a whole bunch of other people let's start pushing on certain change levers with a new organization on our behalf then we can get a lot more done we we start to leverage the power of scale throughout the organization and so thinking about how these things are maintained after
you build them this is more just for just for reference but we ended up just breaking new things out into very basic diagrams we gave them to the team throughout that diagram very similar to a threat model you'd have the process annotated on top of that or overlaid on top of that you would have breakpoints controls decision points users involved data close that would happen throughout that or you know what data aligned with a certain classification was was happening within that process and and then we could extract that or extract from that the overall risk associated with a with a business process and then what we ended up doing is after we would end up
mapping all of this stuff out we just have very candid conversations with the people who owned it and talk about like what you know what things should look like from here you know we've mapped out ten business processes one of them has as the potential that's just completely derail your department or it's connected to or it might influence you know ten other departments and there's almost nothing being done to make sure this happens the right way so you know how can we work together to to change that to make things better because ultimately it's going to it's going to impact me it's going to impact you I want to help you you want to help me and so you know
let's all be friends because we have the same objectives at the end of the day so the next thing a little more on the fun side is wargames so this is more where we start to bridge the gap between Red Team simulations and what the business is actually planning and so this is as you might as you might expect actually crafting a scenario where you might take a business strategy a tactic that the company wants to do whether it's building a new product rolling out a whole new set of features going after a new market segments things to that effect and and actually run through a simulation so pull together a bunch of people pull together stakeholders and
map this out you know like role-playing game style and you know you can start to figure out how you want to answer these questions like who are where the adversaries relative to this strategy or this department what do they want and what are they willing to do to cut us out like will they start a price war will they slander us will they you know what will they do market wise to you know to to combat us attempting to achieve this strategy and then lastly what are we going to do about it as a business so that way we all make money or we all walk away achieving our objectives and so in doing this I would strongly
recommend picking a single strategy the model at any given time it is very difficult to to start thinking about these big complex systems that have many many strategies interest and an interweaving with one another playing off one another you know pick one strategy one business unit to model at a time that way you can minimize your prep work and maximize your your outcome and you know pick a diverse team participants the like role play if you want to do a full-blown live fire simulation or maybe you just get together like a tabletop exercise lay out the scenario and then just kind of provoke in and instigate a whole bunch of thoughtful discussion around if X
then you know what happens like what is y following that and actually executing this so so we ended up taking when we did this the the role-playing game approach where we would roll out a particular we would roll out a particular scenario or pick a scenario that we're going to do pull together a few stakeholders and we would have the home team ie the the team representing nuna and it's and the business unit rolling out the strategy present their present what they were going to do you know you have the floor for five minutes what does your move look like on the chess board and then each each of the other teams that were involved and in
the room they they would sit back you know they would go away for 10 minutes put together counter strategies you know maybe a little bit longer depending on how much time you have and they would they would bring together their counter strategies based on them getting into the mindset of the the competitor of the adversary or that situation and you know they would present their strategies and then we would all regroup we didn't do too many rounds because we didn't want to get too abstract but basically we went through one one or two rounds and then we sat down and we just collectively as a group talked about how all of this could overall be improved
and you know make sure that we're optimizing on what the moves and countermoves are and just basically all of this is about reducing risk reducing uncertainty when we're doing this kind of we're doing this kind of work and so the next thing spreading the love so when we start preparing for a security assessment particularly a red team in many cases we end up doing a lot of a lot of reconnaissance a lot of intelligence gathering a lot of open source intelligence gathering we find data and information about people about companies about prophecies and one of the things that you know that we oftentimes say in this in this context when we're talking about being in an engagement working
through an engagement is that we're going to break into an account we're going to break into a computer we're going to break into an organization a company a business and office etc but what's interesting if you if you ever talk to marketers salespeople etc and they're talking about business development efforts is that they'll use the exact same terminology that the exact same vernacular they'll say I want to break into a new account I want to break into a new market thing things that effect and so we've done this a little bit at at nuna with our business development folks talking to sales about things that we would do if we were in their situation about gathering data on
what you're going after how to find people's email addresses how to track people down how to position yourself and your emails to be maximally effective think about the way that we the amount of effort that we put into crafting a spear fishing campaign so that way it is as effective as it can possibly be when it lands on that one to two people into those into those one or two email inboxes and it gets opened and our intended action is followed through you know salespeople are doing the exact same thing if they are if they're targeting senior executives at an account that your company is trying to break into and so helping them craft these kind of narratives helping them
think through the things in the way that we would think through could be a really interesting way to just at least get get a conversation get a dialogue going across across team boundaries across departmental boundaries and and this of course this of course allows you to end up opening the door and open the door and find out what is actually most impactful what's most important to those people to those departments to those to those individuals or roles working within those departments and so you know one of the biggest takeaways that we had is as we started going through you know business process reviews through wargames and through things like this where we're helping other people get
into the mindset that we are getting into is that it ended up opening up a dialog where we weren't just scheduling a bunch of time wasting one-on-ones we're trying to do something productive but at the same time we are having a very open and honest dialogue around what's most important to those those individuals and as we're having that dialogue as we're having that dialogue we can map it back to what things we might want to change and so so we're going to work through this last one in a little bit of a of an extended thing of time but basically concluding remarks so the big thing that I want that I'm then I'm hoping everyone takes away from this
presentation is that as security teams we think about and we do a lot of really cool things but traditionally of course we are and probably always will be cost centers to our organizations we spend a lot of money on a lot of things we have multi-million dollar budgets and you know we are we are protecting and trying to keep our organizations on the rails and so with you know by applying some of these techniques and this list is not exhaustive by any means you know we talked about three three techniques you know business process reviews wargaming and just spreading the love or teaching people things you know you can do a lot of other things in order to partner with
different entities or different people throughout your organizations and so the ultimate goal there is to start getting into those getting into those circles getting into those conversations that way you can reframe the narrative around you know security is here to tell you what to do security is here to dictate security is here to enforce and all of that to something like security is here to help you do your job more effectively security is here to help you do your job faster safer you know it's going to help our customers see us in a better life it's going to help you do your job in a more in a more impactful way and help you move up the career ladder etc and so
the ultimate goal from that is of course thinking about you know if we if we want to apply red teaming to our organizations and our ultimate goal is to reduce risk and help protect our organizations which I hope it is at least it is in our case then we can think about how change ends up actually panning out and working in these companies it can happen if we are pushing on something you know we're pushing certain teams towards enforcing or you know kind of mandating or sticking to a policy that we've written towards sticking to some kind of governance that we've that we've outlined are sticking to time to remediate objective something to that effect or
you can end up creating or or instigating these pull change mechanisms where you have other stakeholders throughout organizations actually asking actively asking and requesting change from the places that change needs to happen and so where we ended up actually seeing this was by going and talking to the people who were who are heading up business lines so the people who are out talking to customers dealing with customers on a day-in day-out basis working through their issues you know trying to get more sales more accounts in the door by working with them and figuring out what was important to them we not only got them on our side but by talking through the things that could
potentially put their deals at risk things like compliance things like brand reputation things like you know a system not being stable enough to apply patches to apply fixes to apply you know any number of improvements that might be worthwhile that they would want to sell we actually got them going back to and speaking on our behalf it was really their behalf but it had some of our messaging weaved in into places like engineering into places like into places like data science and other groups that were they were building the structure building the processes building the code building the building and maintaining the infrastructure that was running our organization and so we had we had our messaging going out to
stakeholders who are the pulling pulling change pulling you know engineering and pulling other departments to actually make things better both on their behalf with some of our messaging kind of peppered in and so you know moving forward from here I would think it's important to kind of leave people with them some action items or things that they can they can realistically do it's the first start to set up some time with people so you first have to figure out who is important within your organization's let's start to set up some time with them you know get outside of your normal organizational silo and just set up a you know a monthly or weekly or you know
whatever depending on how much time you or they have one-on-ones with people in different departments at different levels and just start to pick their month pick their brain on what's important to them you know take them out for a beer take them out for lunch take them out for coffee whatever it is and you know if you can prioritize those that are in some kind of critical path for the organization then you may or may not get a lot more get a lot more insight for instance if you talk to somebody that's too abstract like you know I want to go right to the CEO and figure out what's important to them they may not actually understand all of the
nitty-gritty implementation things that are happening on a day-in day-out basis and they might not actually be able to help change any of those things they you know they can understand and talk about where the company is going what's important to them at that level but maybe you want to focus on the directors the managers thanks to that effect or maybe even from time to time somebody in a critical department that's actually boots on the ground that would be actually writing code that would be associated with an issue that your team found and of course the focus of these conversations is for us try to understand what's important to them why it's important to them and you know how
can you potentially connect the dots on how much how your team is how big your team is how many resources it has what it focuses on what their experiences are in everything like that and what is important to them so that way you can hopefully find small ways to help and just to be clear I'm not advocating that we just drop everything that we are currently doing and you know spend a hundred percent of our time and all of this business e stuff so for us I ended up spending maybe thirty percent of my time with with the rest of my team spending very very small bits and bytes of time doing things to this effect and we ended up
paying like seeing huge dividends payoff from that so the next thing actually plan some kind of game and you know that might be a simulation that might be a tabletop exercise is a really great way to ease into this kind of thinking and you can even do that within your own within your own organizational silo so you might involve something like the people who are the people who are responsible for your company's social media accounts or the people who are responsible for maintaining the infrastructure around a certain a certain critical product or essential product that your business has and you just present some kind of want monkey situations like you know this bad thing has happened somebody hijacked social
media accounts or something and started spewing a bunch of crap or you know some subset of Twitter accounts went on a hashtag hijacking rampage and just started spewing a bunch of crap in our company's name with a hashtag that we're using you know what do we what do we do and by pulling in a bunch of stakeholders you're going to prompt them to think through situations they've probably never ever thought through and then you can start to open the doors for doing more and more of these on a regular basis and so you know for us at nuna we try to do at least one technical of war game or simulation per quarter and one more business-focused simulation
per quarter and you know it doesn't always have to be these big grand things it can be something like getting some stakeholders in a room and just tossing some completely off-the-wall questions to them and just getting them to all argue and bicker about what might actually happen and as they're doing that they're going to glean some useful intelligence and some some useful things are probably going to come out of that and you know some ideas for situations that you could use in your own setting is like you know a new product is being pitched and how do we actually want to go about getting that to market you know regulatory changes are coming so this
was very relevant for us or something is just going to fall over so you know think about these things are these are very very obvious in many cases you would think but think about disaster recovery and business continuity situations you know some some teams some departments have an understanding because of all the marketing shenanigans that ends up getting pumped into like cloud environments that just because you're running in AWS means you automatically get disaster recovery you automatically get security of some sorts which is not actually true so you know opening up the doors for those for those dialogues is really important and the last thing I want to focus on as we as we wrap things
up here is setting goals for yourself so I'm a big big fan of the what gets measured gets managed mantra and for any security professional you know even though we do have a lot of stuff going on I would urge you to think about the 80/20 rule like where you can spend 20 percent or potentially less of your time and get a whole lot of benefit and that might be you know applying all of this stuff towards a single department the end up carrying a lot of weight and throwing a lot of weight behind it in terms of organizational change but you know for you as you kind of move back into your work week next week you know
or next quarter or whatever whenever you're going to set your own your own objectives your own goals you know set quantitative number driven goals for yourself you know whether it's having one conversation with somebody each week outside of your normal reporting line you know doing one thing per quarter that is in line with this you know teaching somebody something like holding a brown bag or a workshop or something around a certain topic and marketing it not to people on your security team marketing it to people who are who are completely outside of the world that you usually work in and you know of course as you as you work through actually trying to accomplish these goals you
want to frequently reevaluate them so don't just set them once and expect them to be perfect until the end of time you want to take that iterative improvement approach towards your goals you know assess them assess them frequently see how they're doing see what things are working what they they're not where you're getting benefit where you're not and then you can start to you know tweak and mold and guide your and inform your shape your goals over time that way they're the most effective for you and your team moving forward and so with that does anyone have any questions and thank you no questions all right well cool Thank You Arun