In Search of a Silver Bullet: Malware Detection Strategies Past and Future
Show original YouTube description
Show transcript [en]
[Music] anyone for heard of us before so fast stands for final and ultimate solution to spam problem so this was happening every time people will come up with a brilliant idea said why don't we charge people for email but why don't we spend a lot of CPU cycles on the machine to send an email and of course you tell them well do you know about all the botnet computers that are used to send email or they will say why don't we send the challenge challenge response every time somebody tries to email to you and you tell them well do you guys know about emails within a blowback problem and all those things then they come and
say well let's use machine learning I was like 10 years ago right let's use Bayesian filtering and and that worked well for a period of time until spammers figured out that they can just inject whole bunch of pad masters or keywords to fool the system so that was fun and what was strange to me is that never nobody ever used the same acronym for final and ultimate solution to malware problem so that's essentially what my talk is about today and spoiler alert such a thing does not exist but the important part is not the goal right as well it's not about finding the finding for a final ultimate solution to malware problem the goal is you know it's all
about the journey the steps that we make trying to get there right that's what that's what keeps the world secure so in the good old days just to take a step back a little year 1992 I was still a student in the russian university that was my first encounter of the computer virus so computer viruses back in the days look like this some of them look like that right if the referrals look like you still remember matrix printers right so I put a picture of the picture there because that's what they felt far is that I encountered it right it was injected into the printer driver and my my roommates they were trying to print
the their final diploma work to present to their professor later in the day and they come right into this entry after every coma in the document that I printed there is a swearword right like I cannot give it to a professor well you know what's happening well in the Russia like I'm sure I was trying to come come up with an example here on the screen but the thing is in Russian they're actually swear words that you can put you know capture every comma and still have a few in conversation some some people do that so so that was my first encounter this is like the mottely viruses back then they were just a form
of digital graffiti right they can do damage but obviously not at the level where it happens today back in the day I thought well the guys who do antivirus software I think I tried to use dr. Webb and clean up that machine pretty well work perfectly those guys a super-smart writer just can't believe that company can go and reverse engineer the virus software right the signature and back in the days it was big news every time you see a new virus at the big news right so the labs will bring it in they will analyze that they will write the signature they will fold their customer and they will dictate the signature right now as pocket on the
floppy disk you may know about the iCard have sample right the I car is actually a software that uses for virus testing or anti virus theft and you can also you know dictate it over the phone because it's so ASCII so if you fast forward a little bit and this is the slide that I often use in my presentations I steal it from the company called a details of work and this is the antivirus testing organization so to test antivirus no matter whether you like the mythology or know what they need to attract a lot of malware and then they measure how much new malware they get every year you can see this literally a hockey stick type
curve that shows the growth of the problem we had over the last decade and this slide doesn't really do justice to what is happening out there right because you can easily and it's all about malware families which obviously there is a thinnest number of those packaged and repackaged in so many ways so you end up with millions of millions of samples right doesn't really do justice but illustrates the problem that we face so obviously the security industry needs to respond to that it needed to adopt so we had a lot of diversification so the anti-malware protection what we started with 20 years ago so here it's still very very relevant but from the endpoint on the network but
we also learn the hard way that a patient in determined that hacker will eventually succeed in breaking your defense system yada yada yada so there was a lot of additional products and services that came apps so going from the intrusion detection to remediation of the attacks security analytics Incident Response Unit right what a long long list and this is great but the important part to note here is that there is most of all this technologies they come after the protection piece right so it starts with protection when protection fail you need to deal with the incidence and the reason I will focus on protection part today does inform us and the reason is because that's what you know that that's the
ultimate kind of the holy grail of security right because if you yeah you may have all the intrusion detection systems in place but how many introduced you really want to deal with we're going to look at one incident that's a protection failure or if you want to look at thousands a day right the answer is obvious the other reason is if you look at the protection don't play games much but this one actually like so this is the most like a tower defense game with plants vs. zombies so you put a lot of protection layers on the way to keep zombies out of your house and and most of the time it works great when it
doesn't you deal with you know it's up to the detection this is the song video house but in a lot of cases for each elate is only a t-brain right so when we talk about ransomware it's already encrypted you false what are you going to do when you talk about you know banking Trojans it might have already siphoned a few of you know money from your bank account or to key passwords so a lot of cases it is pretty late you just do damage control that's why we have this real length of store needs to keep the protection levels out okay so if you know another analogy here could be the castle walls right so if you have big
and strong walls they don't need to be beautiful just big and strong right then you know you can keep the attackers away and that's what we do essentially we just make those walls begin strongly every day so if you talk about best protection requirements what is it that we're looking for so first of all it needs to be as proactive as possible because it's not proactive you fail in the until the detection of remediation stage and it is proactive from the users point of view it may not be proactive from my point of view necessarily may be you know we take the example into the lab and we look at it like well we didn't detect it let's
not detection but as long as we do it before the you know how are you the user is our customer base has a TEFL good no false positives of course there's no such thing as no false positives but in the protection industry labs the target we set for ourselves right you don't start with a let's build a technology that will detect all the malware it will have 10 percent false quality for 2 percent like no when you built it technology we do build protection you do not knowingly produce false positive CEO they happen as an accident it also needs to help acceptable performance impact you cannot sell all the CPU cycles on your machine just scan in every single
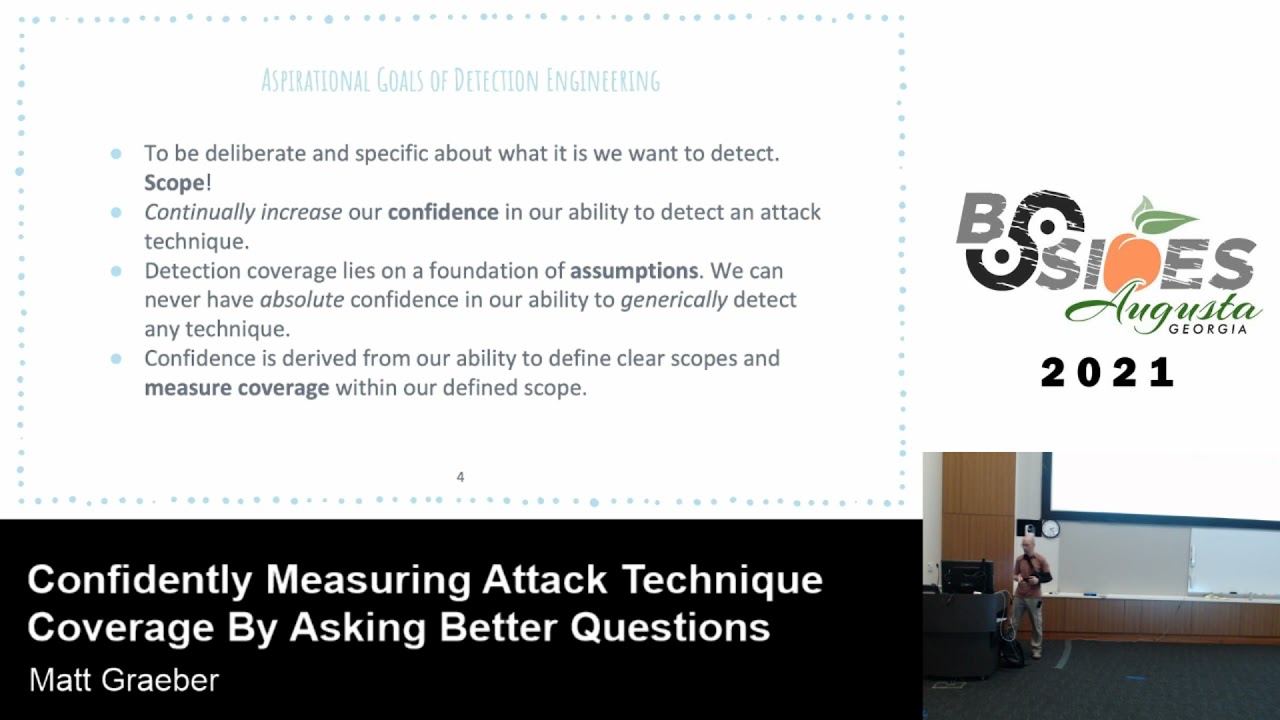
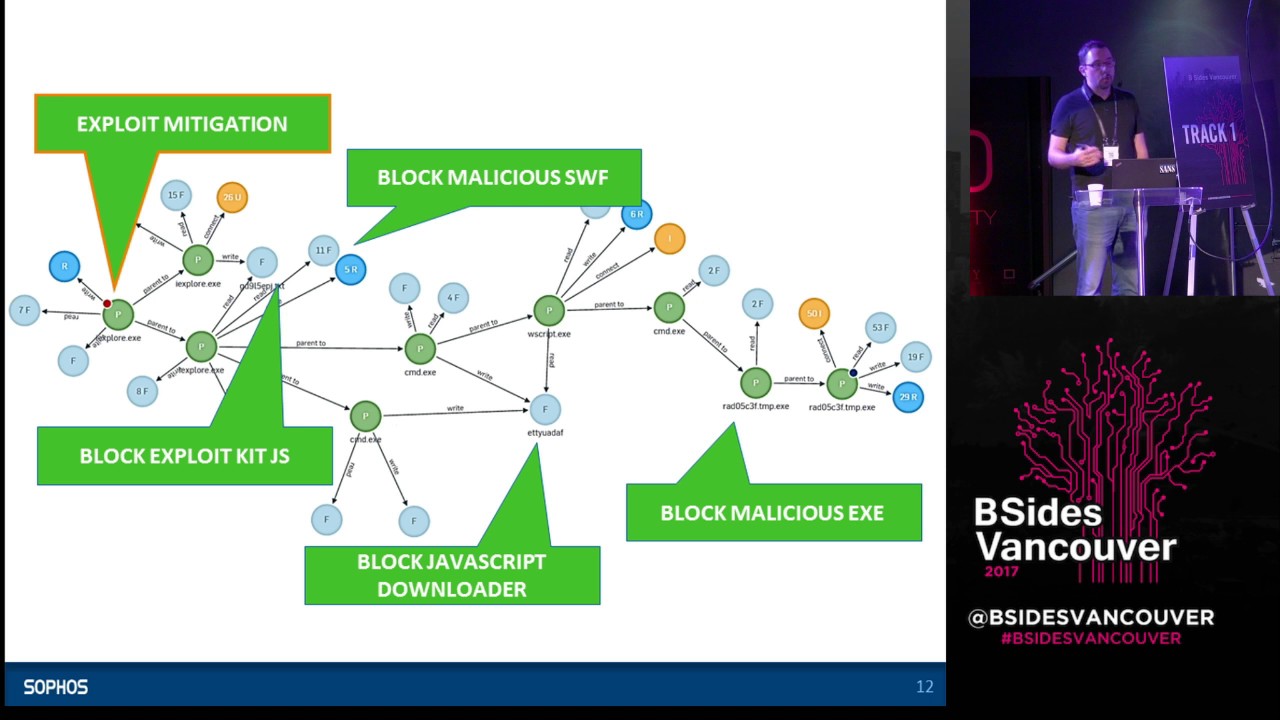
file for you know matching the bytes no you need to you need to optimize it pretty well and also needs to cover low management overhead now you don't expect to you know offer services to an organization that will have an anti-malware you know large entomology some big companies do but a lot of small and medium businesses they don't they just expect the technology to work so if you look at the attacks today and they look quite complex so this is the graph to illustrate the server ransomware deployed over the so-called weak explicate and we I believe the green circles they represent processes and there's a file activity registry T medium you know processes launch and
spawn other processes and things like that so if you zoom in so the most of the web exploit gate attacks they start with the user in visit infected website that's pretty straightforward and then it runs the JavaScript often obfuscated that tries to bring a whole bunch of exploit components and in this case slash exploit was was one of the most prominent the exploit will spawn shell the shell will drop another piece of JavaScript on your computer and it will actually run it with the W script Aleksey which will download it and keep the payload over the HTTP right so not just an exec I'll but an encrypted blob and it will decrypt it to this and then it will run
another shell to take that decrypted eggsy and and execute it and that's when you when you effectively have the server runs on your infection so it is it is getting pretty complex it's not like the you know the virus that will just run from you floppy MBR as it was in the days but it's also you know in some ways it is it is good because what you can do you have a lot more opportunity to put the defenses in place so we can obviously start with a traditional approach which is to block the malicious it is available but we know that they pack impacted repack so many times that eventually you know they will break your
defenses by just trying it or virustotal well then you can take it you know step back and look at the malicious flash files can we detect the malicious files and a lot of cases we can and it's great if we do because we can we can stop it earlier we don't need to worry about the TP load we can just stop it at the exploit I'm and we can look look you know we can go up the JavaScript downloader because it does something dodgy a lot of case which is office gated and a lot of you know these are ways and you can you know you can pick it up one of the most successful techniques that we
tried is actually blocking the exploit gate JavaScript so this is when you look at the at the very first thing that comes into the entry point end point trying to try to load all the malicious components now that works really really well except when it when it breaks right and then and then if you take it all the way all the way up to the to the part where the exploit is happening that's that's going to be bleeding edge of the technology that was introduced in more recent years which is called exploit mitigation so you're looking at the you know trying to detect a specific exploit or you're not trying to detect the specific JavaScript because you will you
know inevitable fail and of course you will have other layers to pick it up but sometimes doing so with excellent mitigation you're looking at the ways of how malware behaves when it when it actually were you know when it exploits vulnerable code inside your browser or your blog in or over or Java and there is a limited number of techniques that we exploit user if you know those techniques and if you inject inject your defenses on the right place of the operating system to monitor for those behaviors you can end up with a very very proactive exploit mitigation technique so it's roughly about twenty techniques that are out there and the successful attacks will use some of them
and if you can recognize them as it happens go problem solved one hundred percent is a signature left like you don't need to worry about updating new signatures problem is if there is a new technique that you don't recognize if there is a variation of that technique that is also not bulletproof it works really really really really well except what it does okay the other problem with this approach is that not I'm not going to read all the different you know exploit mitigation techniques that exists just some of them listed here so to give you an idea if the other problem is a lot of malware these days spreads doesn't spread by exploit kids but it spreads by
social engineering attacks and email spam you'll familiar with it but just to put things in perspective this is what this mam tragic looked like over the last year so you can it might be hard to see but you know the colors represent different types of attachments so whether it's a visual basic script or if it's the JavaScript or maybe JavaScript in the form of the wsf file window scripting format or framework or maybe it's even zip file with an egg inside ourselves tablet and you can see that you know on certain days we had what almost 45% of all spam are sent out to be often this malicious nature huge huge huge problem so what what are you going
to do there so this is what this Hamit act looks like in case of the attack we observed last year that was bringing the walk around somewhere and the culture at the same time so if you zoom in san email received by Outlook LED process an attachment is open of course why would understand attachments of delivery see build zip that runs Explorer which approximately file and and then there is adult LMK file inside which is the windows windows shortcut shortcut file and of course users do click on that file as well why they would and that launches a PowerShell and the PowerShell loads captured eggsy's loads the Lockheed xee and it also opens up Microsoft Word with with it open like
a decoy document so that you know when you click on it on a document that have mm-kay extension you kind of expect the documents you show up on your screen and that's what it's doing so again we can inject different levels of technology here and it will work great except what it doesn't and then you look at this whole graph and think white you know can I just for late all this activity and and have this kind of behavioral based detection so you know I just wrote I don't try to to compile it because that's just the logic that I I was in my head that I translated to the pseudo language so if the filename has you know
has a dot LMK extension and it came from Outlook that exists it was dropped by outlook process and it tries to launch command shell [Music] lost audio consulted at the command line actually might just on the PowerShell don't agree which is great and then the PowerShell actually you know download an executable file how often will that happen in the legitimate cases case scenario probably never right so you describe this this logic and it works really well to solve this attacks problem is you soon find out that that great match that you had on the command can see dmdd watching PowerShell you'll start seeing it spelled like that with lots of obfuscation and it's in great
they have to skate and stuff that's a good sign I can make my detection stronger but that means that you need to update your detection nevertheless and then you notice that all the detection that you've created for for PowerShell and CMD and Excel detection all of a sudden they switch to the JavaScript or they no longer use Excel and word they now use Microsoft Publisher some people still use it for some reason or they will use MF HT 8 or XE to briefly to bring the JavaScript payload through maybe they will switch to video so Jarrah but there's so many different combinations like one of the one of the interesting cases we observed was when
the commando degree doesn't even have this no PowerShell ring but it comes from an environment variable that was written into by the JavaScript at the earlier stage of the attack so and works really really great except what it doesn't and you still need to update your new protection logic so why don't we take it all a step back and look at the behavior of the malware by putting it into the sandbox and get I made it so you're familiar with the concept detonated malware in the safe environment observe the behavior makes the decision right there woods brilliantly except when it doesn't so there's a big increase in the malware that is sandbox aware and there's a lot
of limitless number of techniques that they can employ to recognize that they run it inside the sandbox and ever refused to to reveal it behavior so simple example so how many CPUs do I have a lot of people start their sandbox and just like okay I'll have a VM with one pp you almost machines you have multiple CPUs word and malware will be like oh there's only one CPU it's got to be here with an interesting case when we try to detonate a Word document in a sandbox and it doesn't really do anything for hey this is malicious document it should go and connect to the internet downloading Z file and then we realize that the VBA
code that it has inside is looking at the recent recent menu and trying to see how many recent documents you had on your machine right and if there's none means there's no active real user on the machine right it's like refuses to work or there is a concept called fingerprint so because you don't have infinite number of VMs when the malware malware actors spread their their attacks they can fingerprint the hardware they can sync the different the network that you're running in and they collect all this information and they can say oh we feel a lot of definition in the in the network or environment that looks like this so when we see it again that's
embedded in the malware code or embedded in the network response that we said then don't don't do anything right just hide yourself is it running in the right country we see malware that is target in Europe specifically targeting Germany Europe if it seems been detonated in North America Network it will refuse to do anything don't make a Geo ap look up to determine where it is and all bets are off am I in a targeted Network so it's a targeted attack and it attacks us to sitting company it expects you see a call back from that company's network not from from the security provider so a lot of a lot of different mechanisms for sandboxes to bypass them and it's good
when we see it is in a lot of cases that is a it is a malware sign and we can put it in but you still need to respond you need to respond a lot less frequently that you do with the binary signatures that you know the traditional antivirus world but EC still need to do that so October 2017 we've got so many technology on the network and I'm mostly talking about the endpoint here but so many different protection technology only on the end points side we have run time detection we have reputation systems where we just have a lot of automation looking at me or is it a bad sign that you are Elvis
put it in the cloud and when we see it again we'll all get is that a malicious traffic emanating from your machine doing the generic exploit mitigation there is there's this really good technology that exists right now that the ante ransomware detection so it looks ransomware behavior specifically run around somewhere you know gets on your machine it opens you Word document and it encrypts it and writes another you know as a picture that encrypts that we're document and you can look at it like well it's not a Word document any more so it must be around somewhere attack and you detect it and then run to learn apps to that as well and instead of writin until the same documentable
right and you document the new file on them they delete the old one and you have to adapt to that technique or they will you know what they will use the file system API anymore they will go straight to you disk right or they will go into the aim the MBR and we'll do it there so you keep trying to keep keep improving things so some of you might have wondered like hey why don't we just turn the problem I side down why don't we just only let the good files to run now that's a brilliant idea and you know there are some products that's exactly the absolute they can look at the digitally signed
applications you design programs so defined by Microsoft you can verify the digital signature what else you need right please come in you can look at the trusted installers it's a Microsoft installer you know sulfur's Google just you know trust whatever they bring in or you can you know this is there is a long tail problem and you can build your huge database of whitelisted hashes so you can you can eat them let them Adam well the problem with the approach that is also not bulletproof they will there is this long tail of custom and legacy applications that you have to deal with and you will always be a little bit late there there is this
one time apps and nisha apps that you will not have a reputation for so you're going to deny their entry into the system digital certificates we know they can be lost they can be stolen there could be exploits either in the application level on the Left level that bypasses this as well and you in case of targeted attacks you can compromise the admin tools you can compromise the and windows management phases and you can still get through the white listing system but the one that's most probably more interesting as the emergence of the script malware but it's not even the executable file that you can have a reputation for but it's a PowerShell that comes in and does whatever it wants
on the computer and file less malware doesn't even touch the disk right there is no exede just injects into existence but also some stays there on top of that huge usability impact right so you need to come in and have a high maintenance cost whenever you have an alert about somebody trying to install a new executive Oh file that isn't trusted you need to go and figure out what it is is it really keen can I bring it and you might have work hide you know total cost of ownership as a result but you know that it's really really good for certain use cases so when you talk about servers right you know we want to deploy a
server out there with a with a specific set of software that you want to run and keep up-to-date you don't want anything else on that server where it's great yeah or if you have a key of or maybe a school environment those environments this works pretty well the other thought I would offer here is that as the of the Microsoft Windows platform follows the other platform specifically on the vial and moves everybody to this app store model where everything aside everything needs to come from the marketplace then the whitelist of solutions they will either grow in importance because of stuff essentially everything is signed so it becomes easier may even become redundant because Microsoft is going to
going to do it for you basically so a comparative slides with Rafi but I noticed that other robots on the I was lied to actually look very similar you you might have heard all this news about the rise of the machine you know they're going to take our job on strength robots will destroy our jobs ready Fred yeah this is my favorite ball like this is the reason right Goldman Sachs automated trading replaces 600 traders with 200 engineers yeah we have come in for you overpaid bankers that's what this that's what it says there so I read all this news and I have kids right on my kids this is really important but what I'm gonna tell
you is really important so they will be robots and they're going to take out all the jobs away but there is one job that will level stay right it's software twelve somebody needs to program those robots so my son obviously he gets most pressure for me and I bought him an Arduino board he wakes it effects on here's the Arduino board you really need to learn how to hack things right you're Russian it's a now blood and you know and decide that will be the only thing that you know it will be the demand twenty years from now so I thought that we'll have like worries about job security right you just the new antivirus work needs human brain and
then another thing happened and I talked to the guys from the from the company that built it deep Loden antivirus which is now part of sulfus handling like it's a very brilliant dina scientist and again stop thinking that they are working on algorithms that you know essentially automate what we do it and my second thought was that is actually great right because you know it's not going to solve the entire problem right so it still it would still be a demand for the experts to kind of work on the hard robes right so we let the machine we let the robots to do the difficult part so if you look at the like myself impression of what i see they're
proactive by design so you train your model so that it's proactive you know need to update signatures you build it on the known sets of malware and clean software it works really really good at picking up new stuff it actually shows very high efficiency rates okay so it detects a lot of stuff which is great and it also lets you configure your true fault trip all the different false positive saying so you can choose power dress if you want to be on malware versus how much how much you can do with the dollar rate on the false positive side but where it really shines is solving this long tail problem so if you look you look at this you know the
number of malware samples out there or how many gets uploaded to virus total every day that that's just great you cannot have humans looking at each one of those files and creating signatures of dating signatures you really need to have reason you know smart automation behind it and that that works beautifully on the long tail on the problem except twenty Belvin so first of all there is this troop all the different false positive trainer so you have this thing called ROC curve ROC which shows you the dependency between how good your detection rate is versus how you know what what is the expected ft rate and you really need to decide where you know where you're going to put
the dots right so if you can tolerate false positive co detection rate is going to be lower so it we'll be very creative in how you mitigate ugly false positives and how to how to optimize those trade-offs it will be slower to respond to new malware right so if you update in your data model and frequently and you don't publish updates every day any change in the problem domain that you know that impacts your technology will be slower to react to and the side we already see the cybercrime is adopting to it right there is a number of players and machine learning antivirus industry and they already been attacked by the cyber criminals well there's a lot of things
you can do you can obviously go and you know take the legitimate applications you can to organize them in a way that machine learning system looks at it's like hey this looks like elegida right it doesn't analyze every single byte dozen thousand annual aid and doesn't reverse it so it just looks looks good on the surface it has challenges with obviously with non exec of of course you can try to apply machine learning to your script malware and a lot of people are working on it right now but it's not there yet Philo's attacks what are you going to do about those there was this interesting case that I saw just a couple of months
ago there was this famine with ransomware and it used the NSA F installer and you take that installer and it's clear that it's malicious because it brings all this you know run somewhere a law and you unpack it and it's just an archive your packet and you don't see anything malicious inside that archive it's just some random images random text files like where's malware i note malicious words malware turns out that an NFL fire and sis installer can be scripted right of all the logic all the malicious you watch if you can find a script so the file looks pretty benign until you go into that scripting layer and you need to be prepared for it I think yeah
all infectious we might actually see them coming back again trying to bypass the machine learning technology you know compromising legitimate applications in an automated way why not so if we look at the attack complexity and how it grew over the years this is just just my random thoughts of what it might look like it's obviously very hard to measure and if you look at the like a technology status codes like hey but let's not really do anything and just keep keep things the way they are with the growth of attack complexity you're going to have this big gap created by this big protection gap so what you really need to do is they need to
constantly innovate in the protective 8 on the protection technology you need to have this in relentless technology advancement that is trying to bridge this gap sometimes get ahead of the criminals sometimes and I'll land behind but then get ahead again it is just inevitable you have to do that right that's that's that's our only choices just keep keep inventing new technology keep bringing it in not not to get the final to a point where we have fine allowable solution so the malware problem but just to stay in the game just to stay to stay relevant so to wrap up the winning strategies continues technology advancement relying on the modern fact so whatever technology can offer you today on the protection side
you can you just need to put it in you need to retire the stuff that no longer works and you need to brain and execute the media really well on the stuff that is helpful you need to have a large amount of overlap in your protection technology because if you don't nothing is bulletproof family you know they actually have actual gear proof and you also need to retain this really fast response to changes things all the timers side world the cyber threats world things are not going to stay the same they will evolve and you need to have this ability and you need to have smart guys working for the security companies to recognize when there is a
shift to understand what is happening and to be able to build technology that responds to it the risks to the strategy is yeah I think what what is happening would be platforms generally like if you look at the mobile lounge or I do our labs on your Mac OS you start looking at the window where Windows has had him you know the platform owners they do try to restrict them and a lot of cases to do it for security reasons right if you can only install applications from from our store and we've validated everything and it's good then I know there will be no malware in my on our platform that's great but we know that that isn't always
true while we're getting did you find there ways to get malware into the Android store into the Windows Store as well eventually also means lack of security API so if if the platform is restricted your protection technology is unable to see what is actually happening what is going on so you kind of at the mercy of the vendor to protect their platform and you know because they've always be targeted they will always will they will always miss if certain attacks right thanks like in the internet of threat internet internet of things right like you know have you guys seen an antivirus running on one of those IOT devices no it doesn't exist right and we see the
result of that so the worst thing that can happen is you have unit so say you're having a mobile phone and you trust you or your vendor with security and the secure platform and these patches frequently but you cannot have an anti exploit technology onion welcome from from another security vendor you kind of need to trust I'll trust your trusted platform vendor so how would you know that you mobile phone is exploited so if you use Android and Google doesn't tell you that you know you have an exploited phone how would you know if you don't have all the day of all the inspection points available to your security security vendor so that's the end of my talk
like I did well for time there's a few things most of you probably don't care for that stuff but if you if you like free software then then we have a lot of it and questions