Criminal Cooperation: Lessons From The Dark Side
Show transcript [en]
you laa okay can I just bring the fact I only left Microsoft three weeks ago and G slides just doesn't like me I miss PowerPoint and I haven't used a Mac in 22 years so it's not a great combination the first time presenting with the reasons uh welcome to criminal cooperation lessons from the Dark Side H I don't think I have to explain Darth uh but I will explain um the donut in a second so what uh what we're going to talk about today I'll briefly look at who I am I apologize for it not going full screen after great on um why lessons from the Dark Side why was I even thinking of looking at it from that angle uh Legacy
a tale of the creation of the nesis so and present day clad iot we're all individuals oh come on someone no I'm not no no um a very I feel like this is really bad cuz Heather's talk was amazing and I feel like this is going too L um a very brief tour of the evolution of cyber history cyber criminal cooperation look at a case study and that wasn't me tou um what is the key to their success and what can we do and the only thing more dangerous than the developer is the developer conspiring with [Music] security uh just quickly who I am um my name is Lara Sunday uh up until three and a half weeks ago I was a tri
solution security architect Microsoft um I'm now a product manager at rapid 7 I'll try to remember this we'll get through it um so yeah so our recently change product management for the inside Cloud seor which is the management tool um thank you awesome I don't work in I okay so yes so this is me that's me the reason there's a wave there is when I'm not at work or looking after my kids I'm usually out or in the water and that's me now where's next try this okay why lessons from the Dark Side so earlier this year I was at um a session one by vendor and they put a slide up and it was like looking at the business of how
criminals work and I kind of obviously had told about it before but it got me thinking I was like that's a great like that's very functional isn't it look at those workflows and processes um if we think about it so there's been some sort economic studies it's the third largest economy after the US and China that's a lot someone is making a lot of money and it's easy money right do you want to rob a bank what way do you want to rob it do you want to go in there with a gun and maybe get hurt or do you want to go with the computer you're just going to have to listen to my voice maybe we'll
see so in our midor threet report people are still not patching people are still not doing their hygiene um 40% of incidents are still to things like not having MFA implemented R some Mor gangs I think this is pretty conservative um but first half the year 1,500 victims were wide could be a lot more of that cuz that's just we tracking and dark web marketplaces are thriving have you heard that term thriving being applied to any other sort of business in the past year like we're all feeling the pain especially might at the minute but dark web marketplaces are thriving so I just want to speak about so this all got me thinking about how we
work together I'm an anthropologist that was my degree I'm very interested in people one of the things I encountered when I changed career four years ago and joined Microsoft was that we're sometimes terrible at working together um and it because Soo is a as Silo it's an isolated instance of something um but it's comes under the physicality of Legacy right you used to have to walk down the hole to get to your sack to talk to Jane down there or The A Team over there or the endpoint team and for a long time there was this image of the cast and we're Defenders you know and then we all had our little castles independently within
that and you had a big firewall and that's what kept everybody safe now the world is very very different you have the cloud you have iot we're all individuals within that we're all doing our own things but we're all interconnected like we talk about air gap now is anything really really truly airgap really and the challenge we have as a community is we took the Legacy mindset of this is my team you do security over there you're developer there you're a ba team you're a governance person and we took this mentality with us into this new world of technology which quite frankly is not really working um and we still keep telling ourselves the same
dialogues that from what I've read I kind of thought it was a cliche when I joined security that we were perceived as boring at that and developers were exciting and didn't want you know they didn't care about security it is not true on either side of that is my experience so I'm not going to dig I try to dig into this but there's too many um for the time that we have but this is a very very brief tour wow it really keeps clicking on I should just like share and turn my laptop around and um very brief T of the evolution of cyber I'm not actually going to go um through each of these and I know I've
missed things and I do apologize but I wanted to point some things out so Tech Model Railroad Club anybody shout out I'll buy you a donut later uh what they're kind of famous for yes who is that why you later or whatever you find so yeah so the tech rail World Club MIT the was your model uh drinks but uh you have the signals and power subcommittee to thank for hacking so the each committee some painted trees and things and some to the trains and there was the signals you know guys who were into creating signals um so yeah so I wanted to point that out I'm going to skip to the 70s creeper virus Rob Thomas 1971 so AET had
been created 1969 he sent R worm um that said um I'm creeper catching if you can um it was excessive it replicated excessively was the word they used and he felt really bad we haden't intended that um what is interesting is the name creeper comes from a scoobydoo robber character which I thought it kind of thought was quite pathetic for what it's used for in the future freeing there's a load of names and people but it's telephone lines 2,600 Hertz is the same as the telephone lines you can replicate and do free calls um but that really created a subculture that then infused 8s '90s 2000s where we are now briefly the 80s the cooko egg
really great book um if anybody hasn't read it a story of C I think it's boss told in 1976 to find a 75 cent discrepancy um in how their computers are and he hunted but he actually like kept a diary it's really interesting like from a forensic point of view of hunting this agent D um it was Marcus Hess um situated and he was actually selling the data he was getting to the kgv so it's kind of early State CR sponsor type thing why sort of I mention it hack the planet 9s best contract of film ever um 2000s and ' 90s you know the accessibility internet the accessibility to technology is much more available to everybody where are we
going um Anissa the European uh cyber security you can look at their threats fast forward it's depressing but it's good to give an overview of what 2030 might look like Ai and Quantum so that was a very brief CH so I feel really bad about this I do apologize like I'm not touching um how do cyber criminals cooperate um so it's broken down and I'll go into that in a bit of detail of services distribution motivation and have kind of touched on some of those elements that you can see I'm promise not Tok but I wanted to bring it down to an individual team ini issue so m k at the time in 2017 when he produced this
report he was the security Ops um n so team leader is kind of pretty much what you imagine they that George G otions 11 they come up with the plan they get everybody together sounds like a bit like a product manager when I was reading this coders malware creators um I'm sure there's a lot of interested people who would be very confident maybe sitting in the Audience Network administrators this is scalability so not every team would have a network administrator but this is if want scalability and can ta and things intrusion specialist um once you've gained access they would like your Global ad and they would like to actually move and find interesting ways and find out as much as
they can and as fast as they they can and maybe do it quietly maybe like say for 2 years I actually have like nation states I would reckon are in most people's systems for a very very very very long time um data miners so you actually get a load of data right but it's messy it's not cleaned how do you make it send you know how do you make it a product that anybody wants to buy so their job is to kind of clean it up and then they move it to the money specialist which is yourell they're identifying their markets who you want to sell it to it's all it's a very business it's
very you know the roles are quite straightforward it's [Music] function so Cataline Sano in 2021 wrote a great article based off C strikes 2021 threat report it's got a great infographic I'm not going to drill into any of these but it BR on the services distribution and monetization um so you've got things like credit Dev C testing you know is it a valid credit card that you can use distribution um SP complains you actually well I'll not read the this slide but if you want to you can look up his article and it kind of breaks the mold down it's very [Music] interesting okay so I could have picked I was thinking like like who could have
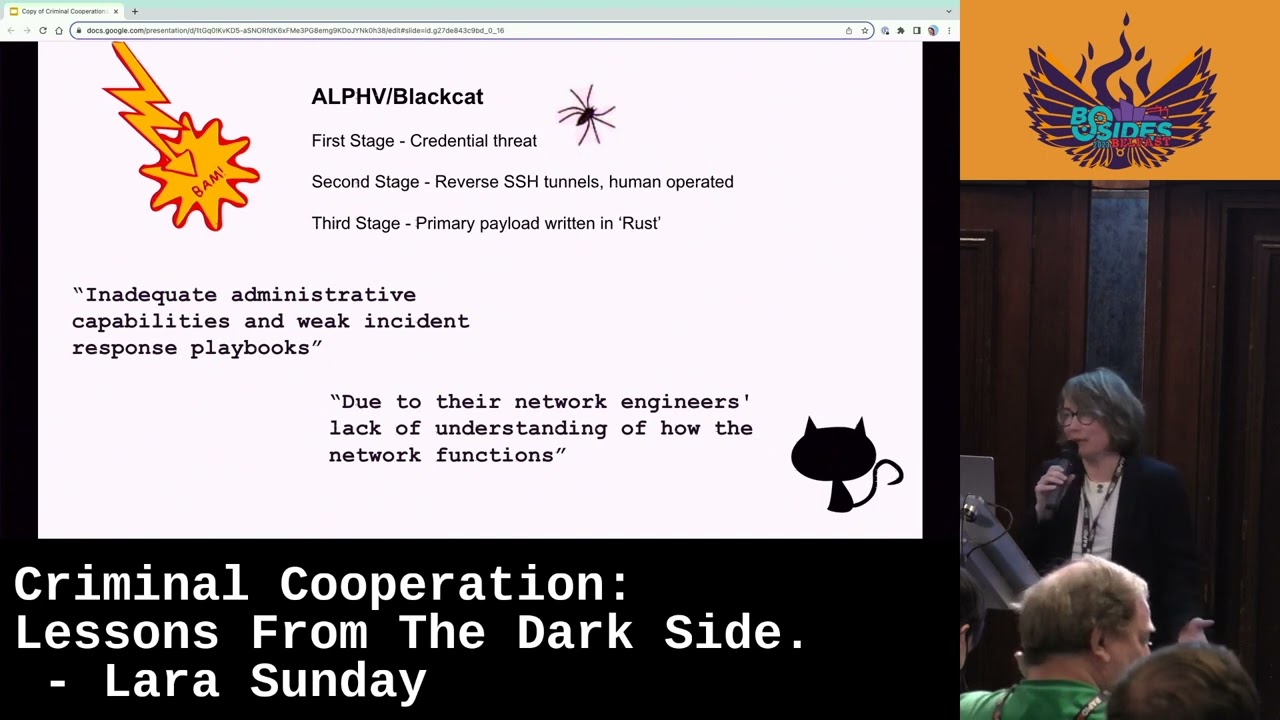
pick as a case stud has anybody been keeping track of the past week of and they bab baby oh so yeah I was like do I do but I just thought it was a good example um because they put out their statement and that just got me there so Alie black cat for know as dark matter Dark Side Colonial pipeline turn that was messy it really impacted the the world um they provide so this is their business model they provide great incentives if you affiliate with them like you you will get 80 to 90% of the ransom if you work with them like that's take them right um they use their recruitment um when we think
about how they're recruiting new people enthusiastically and exploit Forum round five places like that and it's kind of like this tricky Road of like I don't know you start moding your game and then suddenly you're involved in a a cyber criminal organization but it happens you talk to some of the kids you know teenagers that have been caught out and like I didn't think I was doing anything really bad in the real world um they're quite R they use rust it's a highly High performing language program that um works on both L and uh they first yeah 2021 was when first came about also known for three stages of like like three stages of extortion they like to be multi-talented
so the first stage they get your credential thft the reason I have a spider and I just just want to put a caveat in with all of this nothing has been verified I am not going to talk about slot machines in case someone gets angry like none of this is just but it's just a thought I've been thinking about um so the first stage CR credential death possibly scatter spider who do social uh fishing engineering phone calls and such have maybe possibly been involed in this nothing good I don't know like I don't I'm not saying just this is what people are [Music] uh working with Alie black hat uh to take time um so I just wanted to put that
there and they're actually still using tactics like social engineering tactics that Susie Thunder was using in the 70s so it's quite interesting how that's kind of evolved but what really interested me about Alfie and this attack is they put on th last Thursday night they put a statement [Music] out mm paid for the most expensive pentest in the world unsolicited but they got they got critiqued and I thought it was really unusual how many crimes can you think of where the attacker or the extortionist feels like they can critique you on how bad the victim or good a victim you are this is what they did so they said things like inadequate administrative capabilities and weak incident response
playbooks that's very professional that's very like I would expect that you know your CEO went to PWC and go to reporting or something and they came up with this um I don't know I have no idea of the details they might have good playbooks they might have bad playbooks I don't know due to their Network Engineers lack of understanding of the how the network functions and I thought a this was pretty shaking to you know pick on the engineers also how many of you in sort of like are really confident that you know every bit of your environment you know everything that's going on in your organization and I have a show of hands can hand in heart say I know everything
everywhere on Prem Cloud we're all totally confident in that no I mean I know I'm not you know I've seen customers environments I wouldn't like you know I don't blame a network engineer for not knowing everything and the Very going back to like right there is real people impacted by this so they're given their critique and being annoyed because the victim is not you know cooperating efficiently with them there's a young person who started a job recently at that casino hasn't got his first paycheck that's sometimes the difference between you know buying food and a week right this is really I joke and I will make more jokes but it's really not funny people die people are
abused people lose their jobs it's not funny it's not but what is interesting what I really find interesting is they think this is a deal they call it a deal it's not extortion they are doing a deal they are doing business with you this is a new type of business you're going to pay for the business not sure what the services a really expensive pest but it's easier for cyber criminals right so we kind of tell ourselves in security Zone but they got easier than us right they have clear key performance indicators they know exactly what they're going for you know what the amount of money is they want whatever they look at it they don't they
understand their role and functions do you like does everybody feel really confident sometimes like who's meant to be responsible for what part of Cl security Foster management it can get interesting they can be really much more agile than sometimes we can uh with who they work with easier to adopt technology if it doesn't work you won't use it and you'll probably give someone a really hard time or whatever for you picked it up and an enthusiastic and talented pipeline right it's exciting the huge Kos you know it's and it's coming through there's like they're making Journeys it's the third biggest economy so I was thinking when I was cuz these are stories I've told it's so much
easier for them than it is for us we have to everything they have to think of one thing and I was telling myself that quite a lot over the past couple years and I was like what is the key to their success why do they find it easier than we do and this is just like me thinking so pleas this is not like this is just like me ruminating I would love to like discuss this and have thought um it's collaboration they collaborate more efficiently and more effectively than us so earlier this year I attended cyber UK it was really I've never been to inperson cyber supp really um I I was standing at the thing
my friend Angie came around she said L there's some psychologists around the corner you're an anthropologist they're psychologists and speak to them I'm quite excited about this so I went around and I met Daniel Dr Daniel sha and Zach brafield they've been working with the US government and Military and NK in UK looking at how cyber security teams can work collaboratively together you know together to be effective successfully um Daniel very kept in touch and he very kindly said that I could speak what that work here with you today so in their work um they found a number of misconceptions about collaboration collaboration takes more time than it's worth yes it does especially at first because you might not know someone
you're going to buy a donut for I will come back to the donuts so we explain the donuts um but they actually found that once collaboration was ongoing it actually generated more creative um and effective soles collaboration requires specialist digital tools the reason I put Don up there um I am famous I will buy you pints or Donuts or at least we say you will until I'm in person with you um food is a great leveler if you know someone in another team and you sat down and had a cup of tea and a donut and chattered you might be much more willing in the future to actually work together to maybe think to ask that person something before you do
something that doesn't cost much uh collaboration takes away your autonomy this is a really hard one um because I suppose in some ways it does and it takes us to do something uncomfortable and let go of maybe perceived things we maybe think we can do better um but actually you're driving Collective effort you you can and take a load off yourself in some ways and learn and grow and I don't know how to collaborate buy a donut for someone you do not have to be an expert at this you don't even have to buy done that you could maybe just next time you're going to do something you think maybe it would be good if I asked security back or
maybe I should ask the developer before I put this going thing through that's all it takes so they came up with um principles of collaboration so these were principles that they found worked were successful with the teams that they worked with they kind of try to pute it down um oh by the way I went to the mid Journey learning experience it is safe to say I'm never going to be a a PP Rider poor Josh forever Josh is had to enter it like put up with my ramblings um while I was doing these um so established clear expectations okay Ollie was talking about earlier we're not very good at you know being definitive we do best
practices um elevate your individual goals okay so everybody's clear like what I'm you know what am I aing for within this team articulate your technical expertise that's fair enough I know I'm responsible for this this is my area commity whatever it might be approach with curiosity I hate growth mindset if we hear training and growth mindset one more time but it is kind of true but the Curiosity thing and I want to keep those principles in your head right for this next slide is can you even see this is horrible this is um so you'll note in the orange I the color things orange and yellow so if you go with the orange clear kpis understand
roll and function HR is easier easier to adopt technology enthusiastically turn the pipeline and then you look at the principles that they know theyve worked with teams and these principles have worked with teams you establish their expectations clear kpis elevate your individual goals figure I we can kind of fit into understanding R function articulate your technical expertise right that kind of goes into adopting technology you know what you are and new R and functions what got me with this is how similar like they're doable like clearer kpis understand Ro and function easier to adop technology enthusiastic and tal the HR ones may be difficult can't it's not always easy to get to the of someone or someone might be terrible
at their job for this but there's so many similarities between the perceived ideas of what we think cyber criminals have an easier life than us and what has been established to work in teams of people in [Music] collaboration yes do you know what I honestly don't like just I've lost screen it's fine right I feel like I should turn around at this point I was going to talk about managing information cyberis architecture honestly right is everybody happy with me just waffling on and we'll try and get I apologize it's not your fault it's not your fault sorry Google and Mac the Mac I love Microsoft um I love mic I this is ironic the next slide
is a Microsoft um architectural like I'm going to start holding my ma up and going like this it's very heavy though um so yeah so what I was going to show you do you want to just show like what I was going to show you is anybody familiar with the security architectures that Microsoft produced anyway there's a an aka.ms security roles and it's really cool um I like the specific one may or may not appear for you depending this is like every night um anyway that architecture it shows operationally how different teams move like the workflows and the process it's vendor neutral right I'm not doing some it's vendor neutral and I used to really like taking customers
through it because you could see like if you're involved in CL Security poost Management where that sits and who you connect with who the information should be going where you should be picking up information and data from what should be pling to this is this is interesting I have to remember what the next SL after that was okay we're going to buy you yes I need donuts and P and with me like no I have to get to the big donut PR but I kind of made my point about how we collaborate but I'm going to get to the big Don there's a bigger Donut oh wow this is [Applause] stressful okay so the next part we had
architectures what was the next part after architectures oh James Duncan so James D A friend of mine yes in Microsoft but I should say that like I have so many good friends and and amazing people in Microsoft so um he created a slide on SE deos we can get into a whole I know there's going to be people there's no such thing as SE Dev there's only death psyops and all of this stuff but I really love the slide that may or may not appear for you in a minute that delates the difference between um yeah that one I feel like this should be like what's going to happen nothing it's not there anymore it will be promise I haven't got
any notes now this is going to be hilarious right James dunan created this beautiful slide deck if you can imagine it says set devops security is everybody's priority oh there we go let I want R oh no it's com in can I like I'll just try and remember my notes this I will try remember
yeah I know I'm trying to be correct right the flashing is very forces you to pay attention I like it that's what we're go with okay okay do you see the diagram no ah right it's okay it's okay it's okay I actually don't need my notes if we could just get a pretty pict so I can do without my notes I can do this I can do this okay it's there yeah okay managing information Serv I used to love this oh great I'm G up see quickly there coste did you see it slightly different from security operations do you see how important to the heart I do like that security and sponsor management right that was what I was explaining it's
worthwhile it's Fender neutral but it's good to kind of think like I would recommend taking a look at it if you have to get a chance oh this is like oh no okay you kind of seen it shift left um so it was a really nice clean deck and James was very kind of let me use it um silos a Dev OPC I I haven't ever said that word that often a kind of traditional waterfall where you created a product and they went I need to do security and you have to start again or you just put it out cuz you didn't care and I know somebody's house got created or something um Dev SE Ops and that's where
you're doing pretty good you've got security built into your pipelines uh using whatever tools you like s get um SEC devops is when security is everybody's concern right it's not just in your pipeline it's you being in a building and you're a developer but you know King an in in the in team mind steps okay it's everybody's responsibility it's leadership actually carrying possibly ping C on the board I don't know that's also terrible like discussion again to whether they should be there or not but it's leadership because it has been proven and we find this um with secure scoring things people were more accessible when successful when they had uh leadership supporting their Endeavors right now the
point I want to make is security and people security is not everybody's concern do you think that network engineer in MGM is thinking about security right now do you think all the tellers in the casinos are having to like write manually do you think they're thinking about security like it is in some form or other security is everybody's priority but it doesn't have to be this like miserable thing um that we're all working together and going to end soon but so we did cover with flashing images why criminal Corporation why came up into my head a brief it was incredibly brief terve the history of cyber how do cyber criminals cooperate a case study um
collaboration is not a gimmick it's a very doable thing uh security jobs to be done I would have talked a bit more about that but I got a bit sidetracked uh SE devop it's everybody's concern really is it's not even fny the world we're going into and donut am I going to explain the donut and I promise sign for so here read the phoen Phoenix project J 2015 yeah so anybody who read it would know that the only thing more dangerous than a developer is a developer expiring uh with security is actually a negative in the book Joes like he just wanted to put something in and he just hassled the dev team remember and they put it in and
then it was a disaster um I kind of wanted to reframe this sentence and utilize it in a different way donut I explained why I think Donut's a good right it's easier if you know someone be open to communicating across teams and this goes to everybody not just security it's not about blaming like I hate this oh someone blame the dev like that's really annoying because I've worked with developers and yes at the start they wondered why I wanted to talk to them but eventually we worked together and they truly needed like we needed to work together to secure the thing because I knew some parts of it and they knew other parts of it and
between us we were able to do it but on our own we maybe wouldn't have done it so well so next time security comes to you and you're really busy and you've got your canine board and it's like oh take a breath they're not trying to be they're just trying to work like make the time and the same goes for security or governance people compliance people the death team might not understand like what you're trying to do the reason you're trying to do it so actually do not throw it over the wall and expect someone El to just do it because that was that you know the Legacy thinking it's not my problem I identified the problems and
now some out that that's not the world in which we live anymore I'm sorry it's not and you know that book was released in 2013 and we are still from like I thought it was a cliche when I joined this community like security bad it's like we're telling ourselves this dialogue that we can't work together criminals are working really well together we've proved like Daniel and Zach's work has proved that like teams can be really effective and use the same things so it means there's the possibility of us like people tell us there is not enough of us we're not good enough at our jobs we don't know our environments right I would kind of like
and it's not come by a right I'm a very anybody knows p i a very Frank blunt person I but I don't like it's happy very it's not like that but it means to me that we have an opportunity to actually work we just just have to culturally change our mindsets on how we work and that's the donuts and if I could have got a donut sponsor I would have and I apologize but I'm not getting thank you for your time being very patient





