Modern Endpoint Security: Understanding Exploits #shorts
Show transcript [en]
know how to do a buffer overflow of you did your OCP everyone says yes I take control of the EIP it's not like that so first why is this important you might be aware of also I seen uh some of the vendors here as well they are going into this direction basically uh the golden era of uh exploits and exploitation doing basic uh buffer overflows and so on is gone long gone so but the the threats are evol evolving now and as well the protections are evolving. So we have a bunch of uh uh uh here a bunch of uh vendors names so for you to understand how is this happening and as you can see the mon endpoint security is
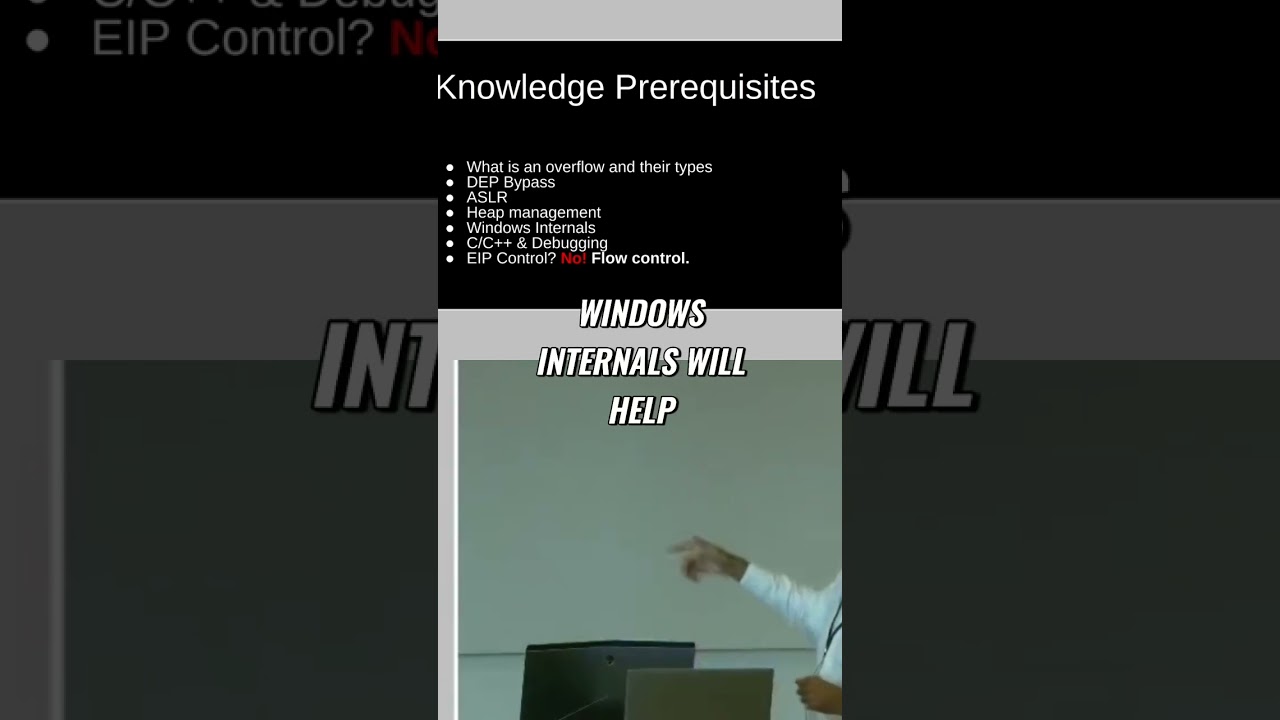
getting a lot of coverage on that right so uh what I mean with this in a long story short is like everything is moving into aristics into edrs into sensors into telemetry right if you want to understand it's not for this talk is this is not a prerequisite for this presentation, but it's a prerequisite for uh uh doing Windows kernel exploitation or developing rootkits. Uh so you need to understand first what is an overflow and their types. How do you do depth uh bypass? How ASLR works. A little bit of HIP management because there is a lot of a heap uh in kernel. Windows internals will help to get the Windows internals books and also the Windows kernel
programming book. Uh and if you have some knowledge on assembly that doesn't help you. We also need to have knowledge on C and C++ because there are a lot of pro security professional that is skip dur during the whole career uh um uh understanding programming the programming side of it and they go straight into assembly. But when you look at the the compilation of the in this case a driver it will help you to achieve results much faster if you know how to program in C or C++. So the last one is EIP control. If you know how to do a buffer overflow, if you did your OCP, everyone says yes, I take control of the EIP. It's not like that.
What you take control if of the flow, right? And that's quite important for Windows SC exploitations.





