Cybersecurity: Investigate Suspicious Sessions NOW! #shorts
About this talk
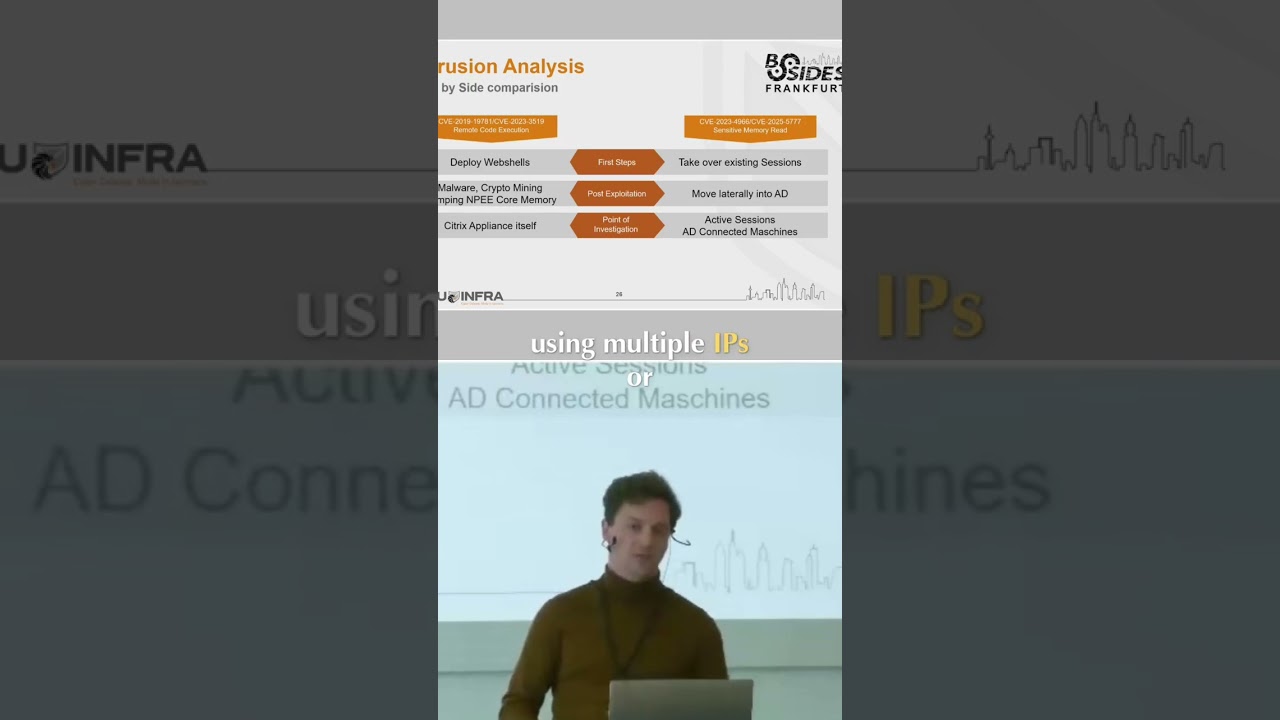
When an attacker is already inside, forensic teams need to investigate suspicious sessions. Identifying illegitimate IPs and unusual activity is crucial, but context is key. #Cybersecurity #IncidentResponse #DigitalForensics #NetworkSecurity #AttackerInside
Show transcript [en]
on the right side as the attack is already inside your machines and already has those sessions we need to investigate those sessions we need to investigate are there any suspicious sessions are there any sessions using multiple IPs or sessions using weird IP something like that and that's a bit hard for us as from a forensic point of view sometimes because we can't really know is this IP legit for this company or is it not legit obviously if it's like 3:00 a.m. and it's coming from Russia. It's probably not really legit, but we need some context and we don't have it.





