BSidesATL 2018 - Current State of Phishing - Old Bait, New Tackle Box (Nick Powers and David Tulis)
Show transcript [en]
like you said we're talking about the current state and fishing and basically same old tactics but new tricks back though moving on I meant to take me poured out but it seems like that stated from University of Tennessee at Chattanooga a little over two years ago previously worked at fertility and I did a lot of compliance work PCI HIPAA and I also worked in ass off for several months so got some awesome experience I'm currently penetration tester rapid7 working out of our Austin Texas office and I enjoy bringing things you guys to us senior penetration test opportunity they're about to a fuse at the photo of the office I also graduated from anyone else
lead stuff alright sorry so this time is kind of geared towards penetration testers I'm not a flew team here he's not looting rare we don't know a whole lot about the defense but we just kinda want to talk about some steps that you can take in your fishing in vain to increase the effectiveness of and obviously none of these tactics are going to be working 100% of the time it's going to differ on any network it's going to be different on the technologies on the network these are techniques that have worked for both of us in the past with a lot of success so the game is kind of changing lately I think it's changing in favor of the blue
team yeah so you're as the blue team increases layers of defense yes penetration testers have to practice offense in depth so each stage of the issue can't have you know there are detective measures releases are measures that would block the payload in place of you as a penetration test you have to buy the best each one of those for a successful campaign often not knowing even what what technologies are in place you know tailor your campaign for the network you're targeting yes it's really just an endless game of cat and mouse you know especially with you know cloud mail providers like Microsoft Office 365 G suite mail sharing threat intelligence between certain industries even metal
attached with sandboxing static and dynamic analysis of tax office macros browser protections cloudy advisor solutions that sort of thing is really shifting in my opinion in favor of blue team yeah I know if you follow these two guys on Twitter tuning out fishing campaigns everyday I've had my fishing campaign to adopt by these bass before which i think is really cool because smaller organizations which may not have the resources for a full routine or a full-time team are getting these protections without even knowing it like I can send out I can send official campaign at 10 a.m. and I know it's argued on Twitter and the client didn't even know you know that they had this
convention with office 365 yeah it's protected place this is kind of generic Microsoft ACP how it works like that evil goes in and good stuff comes out but they are doing a very good job in my opinion so kind of to start talking about beginning of every good fishing campaign we're not going to talk in depth about Osen building pretext but we didn't want to touch on it because it's obviously a huge part of a phishing campaign so here you see we we just did some basic stuff the far-right slide we're using something that we call Google dorks so basically you can do semi advanced filtering for websites subdomains and you can see they're all
I've done is I'm searching for Atlantic Gao and I'm filtering out all the WW so maybe you find some interesting subdomains this is part of when you're building what you're looking for in terms of the pretext maybe cloning a essentially portal some other very useful things for some domain enumeration packet target as a search function also a very useful API as you can see as well as virustotal for the past few years has some awesome subdomain numeration so another reason I put this is not just for your ocean or your sub domain enumeration whenever you're starting a campaign but it's also about evaluating the maturity of who your target is David discussed I'm talking about the Vincent death but
something that you can tell very quickly about an organization when I'm starting an assessment I can visit some of the some of some of the sub domains that stand out the most to me like Citrix or OA and if they have multi-factor authentication implemented and that tells me something about their maturity just to make general assumptions when you're starting your campaign so the first thing we're going to talk about is domain categorization and just to give a brief summary of what that is it's a third party solution that is going to filter resolution of domain names based on a pre signed category or an association with a pre signed category that you don't want your users viewing
so it basically it's like whitelist blacklist I think if domain has been visited and has a reputation of being for news than its categorized as business or news and if you want to allow your users to visit business websites then you can let them do that through domain categorization and filter out potentially on one of domains but the next thing I want to notice with preparation categorization for your fishing domain easily be obtained prior to the assessment for categorization a lot of third-party solutions tell buyers the companies that this is manual process somehow we have tons of employees that are sifting through all of these sites to verify that they're okay for your users that's 100% not the case it's a lot of
third party solutions do this in an automated fashion they're filtering for keywords so I can clone a website throw it up submit it to the ten popular domain categorization solutions and then get it categorized as finance or medical and also we'll touch on in a second specific solutions and often be determined prior to the assessments well here's just a list of some resources that you can use to check categorization of maybe a domain that you're currently using for phishing or something like that but a lot of the third-party solutions have these online resources where I can just go check remind me of x-force right now what my efficient domains categorized as or with blue code
or any of those where you can get it categorize yourself like I mentioned you can just sort of it a categorization request like normal people do with their sites that one may confuse filters so you can do a simple recursive W get clone somebody else's site obviously remember to take out all the copyrighted material or anything that's going to get to the trouble that's the tedious part or you can just build your own template that's probably the safest way to avoid legal issues and if it has the right keywords and it's kind of pre it's probably gonna get categorized and then it'll make it through to make atomization feel free also something that's important is age of the domain
I'll talk about that in a second so if you're kind of lazy and you don't want to do a little work ahead of your campaign you can just use expired domains that are categorizations so domain that's existed for maybe 1 5 or even 10 20 years this resource expired domains keeps track of all that and will aggregate this information and you can you can see there's some super useful search search functionality and filter based on the TLD you can output this however you want to do it and so basically this might not last forever but if you're doing a quick hand pane you can buy their maintenance expire that already has a large amount of presentation based on age and content
that they've posted and use this for your campaign so there's some more search functionality and also it'll give any an Alexa ranking or also search similar web and give you statistics on that so some really useful way to filter out expired domains that might be interested in so this is this is what it looks like whenever you're looking up what the categorization of your potential fishing domain might be whenever you purchased your domain that you've thrown up a content of you purchased your expire domain in there our new category categorizes something you're gonna want to go find out what solution your targets using often you can find that on LinkedIn just look up the security people and see what
experience they have often will say I'm experienced an implement implementing blue code technology so then target Symantec's blue coat solution and this is actually a phishing domain that I've used on several engagements so I've learned some of it out but you can see this probably took an hour about very blessed than that and I recursively Club recursively on the site that's financial related scrape out some stuff that's copyrighted and three days later on categorizes financial services and one thing that I want to touch on really quick about categorization is specific categories is more than just bypassing domain categorization prevention methods if you could categorize it as financial or medical there's a really good chance that you will there's something called
HTTP inspection and often there's rules that can be implemented that break HTTP connections to do content inspection and based on your categorization often they will omit breaking that connection because the informations financial or medical related and that breaks a ton of laws most likely so if you are lucky enough to be categorized as financial or medical there's a lot of benefits that come along with that as well and just like I'm into the second ago we have some this is literally a screenshot from LinkedIn you guys know this is need to see some super useful information we see the quite a bit nine technology so I know to look for stuff that carbon black does because they were acquired Cisco
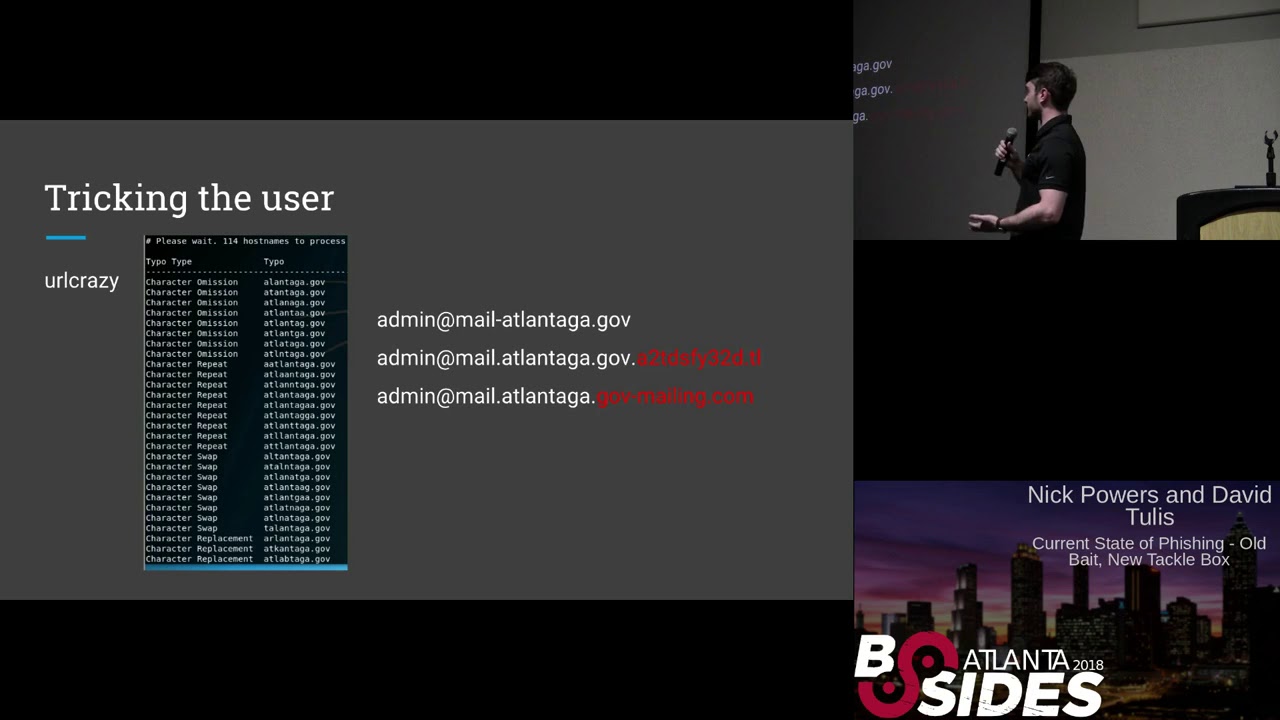
ISE we see by our eyes so when I'm testing my payloads I I have a sandbox or something that will run against fire I off automatically go to bet and also I see web since email and web security gateways so I know immediately how I need to tailor it when I deliver so idiots actually first purchasing your domain one of the oldest but still most popular is just tricking the user with something that's often referred to as type of squatting I think it's pretty self-explanatory so I'm not going to spend too much time explaining it but you can see this tool called URL crazy is just doing super simple things like character omission character repeat
character swap and if you look at that list of domains on the right from the original Atlanta GA gov like you really have to squint at it before you realize what character it's missing replace submitted and at first glance when somebody gets an email from like your boss at that debate or dog work or whatever you might not look twice at it you might just be like oh my god my boss just emailed me and I'm fired if I don't do this thing I need to do right now typos Bonnie's still super popular there's a lot of awesome tools to do it so now I'm going to talk about something called puny coding which is a solution
for internationalized domains and when I say internationalized domains basically all I mean is a domain that consists of a character that's outside the ASCII subset so like a through Z its standard characters that you see every day so if you have a domain that has like a Mandarin character or a Latin character or a Cyrillic character that would fall in the category of ID and rematch last domain and the weight DNS works you have to be able to represent that and just ASCII characters simply use either so their solution was something called puny coding and you can see right here on the 30 bullet I show my character in red which is a Cyrillic I advocate
server like and it's PD coding County counterpart so the the X in - - Bank of America b5b that's the community coded representation of the international last commit which is on the left and I put the regular Bank of America site right below that just to show how similar the Pugh decoded of the regular version look so you can see here like you can create it with your characters you can buy some pretty terrifying domains with cutie cutie so P decoding isn't all just like black magic there this is a very for a while and there are a lot of there's a lot of protective measures already implemented that you might not know about I have
links here to of chromium where chrome uses and muscle of Firefox is algorithms to try to protect against this but basically those algorithms just consist of character combinations like chromium assumes if you're using a Latin character in a domain that also has regular English characters you might be doing something suspicious so basically what they're going to do is you can see here in this if when you type in the domain it's gonna on what I call what most people call and raveling to the full page coated format so there are some some protections built in a few mill clients do the same thing but not often like the outlook regular client like a desktop ride unnoticed doesn't unravel a
lot of domains but a lot of web basic lines do so it's hit or miss something yes
not some of the infrastructure that you need to set up or a successful campaign to make sure that your your mail is getting delivered and then if the phishing campaign is detected that it's not going to affect previous or future phishing campaigns so when I'm setting up campaigns I'll have to follow you know segregating the assets based on function you don't want to have once over doing all your sending mail hosting pretty low as we see you in callbacks you want to segregate it based on asset to make sure that you know if I'm mail is detected by the blue team that the rest of the campaign can go on you can continue to campaign and you're not
going to lose any access you've obtained for previous campaigns it also oppose the idea of sending up a redirector between what the what the target is going to see in that on in their lives and your back-end servers so that you only you only need one back-end server and your redirect users can be spun out their spun down throughout the fish' campaign so requirements for infrastructure to make sure that we've got the best chance possible in our mail delivery we want are our mail server to work as legitimate as possible so we're going to implement some protections where some cement configurations such as send a policy framework dkim he wanted to make our mail server look legitimate
you know we're gonna need to set some reverse DNS records we're going to say any make sure are that domain we're sending them and I P address of the mail server is in good standing not on any black lists and of course we also want to make sure that all our data to and from these servers is encrypted what I want to make sure that the servers are locked down the firewall to make sure that no one can know inspect our expect our servers and pivots in trouble so the back into fishing sermonize usually run some kind of framework like I used to fish was fishing frenzy yes social name toolkit even can use I just prefer go fish the
server is not supposed to be visible to the defender so there is they're not ever going to see this server it's going to be static throughout the campaign will be redirecting all our mail in any ways to mask the origin of this Ingrid it's I need that script right there to set up do a lot of another thing it'll install the post fix and cost amenities it will install go fish it gives you the brown cube and I recommend web interfaces for managing the mail server and sending the mail and just makes the whole process really easy because if you've ever configured a mail server it's not fun so we're gonna be sending the mail from the back end to this SMTP
directory and it's really just hooray it needs to make sure that you're stripping certain headers from the messages that could indicate the location of the back-end server to the expiration date IP the XML or the minor chat are all tells of where our back-end server could be in this way through your M expected a wreckage campaign you need to make sure they're all put into this redirect you don't want them go on accidentally plenty to the back end fishing server and I said easy to spin out easy to spin down you send five messages with one redirector killing you spend on another your messages and they're not gonna be able to easily correlate the two campaigns just based
on where they came from and I've actually found that when you're targeting cloud mail providers like office 365 or G suite that they're you know they're not if you just spin up a server on AWS and start sending mail to people with office 365 it's probably not going to make it through because the office 365 is obviously receiving a lot of mail so if they see mail coming from an IP address they've never seen before they're going to assume it's spam so I like to send it through third-party readers I like the tiny bit amount done let you send thousands of messages for free you don't even have to pay it provides really cool rewrite the links
for you to like a sender or a middleman link which you can track who actually clicks on the links it'll track who opens the mail and it's just it makes it pretty easy to me yeah the Senate policy framework and the new record should all be John went to the third you're not redirected because the mail is coming from the relay and this is you test the legitimacy in your mail server to make sure that you can be heard everything properly that makes an extra box and mail tests are the two right going to make sure that I didn't accidentally miss configure anything that would indicate that our server is not backing tape and it can also be
helpful sometimes to just send a test message to a non-existent address at the target if you get a bounce back you can sometimes tell I know if the message made it to a mailbox that was filtered upstream or maybe you know sometimes even protective technologies they have in place so we have the infrastructure we've got the demand I know need a failure to send you know capturing login credentials with long pages is cool it works a lot but with wide implementations of multi-factor authentication it's getting more and more difficult to try and capture tender potentials into internal network access so you can get you somewhere but usually we really want to send a payload to the
target that's going to give us execution on that machine and you can't just send you know resume t-80s if you send then the executable email it's you're gonna have a bad time
yeah we're talking about all about office documents some these other special payloads that we've been experimenting with I'm not only talking about like what we're going to get to came here you know this is kind of like to use is kind of up to you know what kind of protective measures are in place the motor is the classic a lot of within our Empire which is under seven powerful nation to run access to rural if you have a reason to suspect that you know execution of PowerShell is being blocked or heavily lagged is chromatic jscript we're at access tool we've gotta run money you've got one strike doing important thing to know here is that
whichever of these issues change the default configuration because security your vendors are very good at seeing the default launcher they're very good at seeing you know the default or trigger an executable template so make sure you choose configuration so have a summer time when the new regime does not go to waste I'm a lot of success with pre-fishing pants so it's where I'm sending the payload I'm not actually achieving code execution or remote access on the target but I'm gathering a lot of information that will be later in more targeted attacks so if you said infrastructure with your directors that you can easily spin up and spin down you could send a hundred emails to the client it's
probably gonna get flagged blocked but it doesn't matter because you've already gotten this information such as the anybody's that using software that's assault gathering the demand username that you could use for some kind of encryption very helpful testing different exfiltration methods you know if you can actual trade to button categorize the minions with the DNS that's all very helpful when you're playing the next phase of your attack and it's we don't for me when I use you can serve up these payloads with the patch smartly rights to serve a random payload so you can build you know five or six different payloads to gather certain information about these machines and if you're sending hundred messages
if some of them are going to get through and done omitting information need to really hone in your attack make sure that it works as alerted on so office macros is definitely my favorite and I've had the most success with it I'm going to talk about a couple of different ways of how you can actually execute arbitrary code but yes how easy is for defenders to see you know this has been useful she'll just open operating executables very suspicious anybody that's seen any contents of macros of vanilla gateway it's gonna see this handler that this is the second method of executing processes using WMI I don't know when I go into too much detail about what this code is
doing but that's not important the only thing I wanted to show you here that we see the contents of these strings this is what this is what they look like and it will spin up my trading processes with W my is suspicious so what I do and this really is I thought I'd out of the macro and I store it there you can store it in a document variable been stored in the body of the document and you can pull it out and this will his notice achieves the same thing but without all those suspicious things in the in the macro there in the body of the document which obviously is not going to stand by the
Milky Way our shells very suspicious you know even if you don't have the word PowerShell inside the macro in the body of the document the fact that you know the office vaccine is spawning now short that makes me suspicious so there's a lot of different you know Microsoft binary said you know every system that will happily execute your code these are just some a proc your ones with MS pill you can actually write some dotnet code compile it and run it all within the macro MSHDA which I think we talked about in a moment and then you know getting a Windows 15 object to the register 32 to execute very amazing some of these you know so
many fighters will actually go out and get the table for you so you don't have to read anything to disk I've had mixed success with this because I think that America didn't dynamically analyzed it's making network connections that's immediately suspicious so I usually have better luck and some of these local methods where that will actually you know write that HD AAA or that file got SCT to the file system and then call it because these are I mean these are this is XML like the file that ICT is an XML file baby doesn't know what like it's not going to find anything bad with with XML simple I have been a little word is writing that to disk this this is
probably my favorite method of executing code inside macros because it's not actually calling W stop calling any WI it's not funny PowerShell lets you strap arbitrary code and paste it or if it's good this is kind of the macro right as you can see this down there that Sara that's the serialized net object up there is where it's being called you're not seeing any of those suspicious strings that a lot of providers will alert on this is yeah so for this like you need to have some a learn and dotnet so what I've done it's worked very well as you know you just work up the PowerShell run space and you can give it just a 64 hard shell and it will do it
will do that fun stuff but they'll do that powers will give you access there's some links here just to kind of walk watch the process of how you actually build these payloads because it's a little more in-depth than just you know generating amateur big launch it you're actually have to write a little bit code for this yeah just wanted to kind of show you guys how to generate JavaScript object using not meant to Jason if you've got to download it you better compile it but once you do you can have these 50 vjj switch and generate these scripting objects which which can store in the body of the document and then you can this is just not some concept code
for storing these feelings inside text fields in a document and as India the z1 is just concatenate all those strings and they're used to execute this payload and this is yeah this when I when I tested this and a little bit dividers total it's usually it's usually undetected macroalgae station can be helpful depending on the bit of executed I found that often just the presence of you know occupation is alerting and unit the macro is benign just the fact that it you know it looks like this it's going to be flagged by some providers and may not get through but macro pack is when I usually use - Mac - uh - back and obfuscate the macro and
you just gonna have to test it and find something that works so additional protections that are waste let's remain undetected that my servers my control servers don't get found I've had a lot successfully with Kindle so you've got you know your first stage of the launcher which will you can heat it environmentally so on the name of Active Directory domain the name of the current user if you know that or you know going out and getting a DNS key or HTTP key decrypting the payload that way that if you know John Lambert or Microsoft it's only payload he's not going to be able to tell where your fact and control servers are and your campaign can
continue without recompiling your malware I like to put same tax cuts and there it is again you know these documents that you're sending over to office 365 they're going to be executed in a sandbox and it's it's pretty easy to know when you're executing the sandbox like there's not a lot of computer running on one processor when your target usually have Microsoft Word installed so even just checking for the presence of Microsoft Word and then you know not continuing execution they don't find it can we do a lot to protect you later to make sure you don't have to keep recompiling every time and depending on how you send document whether it is an attachment or a link I
prefer sending as a late more control over the weather you're doing district the ip-based files or if you want to go with the Apaches market right and actually you can look at the the user agent the IP address is coming from and you know if it's an IP address that belongs to Microsoft or a pre point it's probably not going to want to give them the file that you're sending so yeah look at that that right there that's an example my Apache HD axis file that it's got the IP addresses for lady in denying the mail security gateways and if it's coming from that network it just sends into a table okay so David talked about some
awesome stuff with payloads and I'm going to talk about a couple more payload options we have as attackers and also one other thing that I absolutely love SME breast testing why though so basically first just to touch on what David was talking about the you payload key you could call it or a patch of Audrey rice by itself it's all pretty simple stuff but it's so essential because David and I both have had but I've been in testing for less than two years and I've had payloads tweeted by guys at fireEye by guys at Microsoft and I'm like I'm one person I've been pen testing that long like why why would they care about my payloads but they do
and they will tweet it out to the whole world the preventive measures are very very important because defenders so before we get into the next couple options we have in terms of payloads I'm going to talk about something called SME egress testing it's super simple and I put a little gift here just to show you you can see on the left I'm doing a TCP dump of my interface just on core 4 4 5 which is SP it's on TCP port 445 so what Windows Windows does this fantastic thing where if you go to a UNC path which stands for universal naming convention it's like a file share location you can do it in a browser you
can do it in your Explorer like your your file viewing window anywhere in Windows it will try to resolve that UNC path to an SMB share and this glorious thing it does along with that is attempt to authenticate automatically for you with the user you're currently authenticated as whether or not you're on a domain local workgroup whatever it is all you can see here is that I'm going to that UNC path on the right and chrome then you're seeing it hit port 445 on my listening machine but as we go to the next slide you can see some super cool stuff we can do with this there's limitless options the first the first thing we like to do when external
testing is if the client will allow it we will just simply embed an image tag an email and it's just as simple as you see the little broken image there for proof-of-concept purposes but it's that line and the third bullet image source by UNC path a gift that doesn't exist and I throw up there's a ton of SMB capture services we have one in Metasploit their responder does that tons of services do it and basically all it does is listen the sesame authentication and if you guys allow SMB to egress from your internal network which you shouldn't but tons of people do then you just are grabbing patches and you even better on internal networks if you start man in
the middlee it's almost always going to be loud because you need that traffic internally but I see it often on externals as well when I'm testing it just as a client external network I'll invent an image tag and the first 10 minutes of the assessment I have domain hashes detailing format so you can do that in emails you can also embed it in the landing page of your phishing campaign same effect image tag whatever haven't resolved to UNC path start grabbing hashes something that's also really interesting and I think would apply to more like Red Team stuff is doing this with documents so within the last year or two there's been something called template ejection and basically
all that is is you take all the office documents you guys know about Excel Word publisher whatever it is they all have templates that can be applied and you can just have the template be located at a UNC path that Microsoft does that awesome thing and gives you all the hashes so that simple injection but recently if you guys have heard a checkpoint before they had an awesome disclosure last week had to give them a shout out for it where you can do the same thing in PDF documents and literally just about every PDF viewers vulnerable to this well it's really Windows that has the owner ability but the PDF viewers allow it so same thing
simple PDF that's nothing really malicious is going on it's just to reach a bottling a hypothetical biosphere and giving me the hashes in the process okay so we're going to talk about just a couple more options in terms of payloads one that's really cool called HTML applications HT HT a poor sort and basically all this is is HTML that can execute on your local workstation interpreted by windows script host but it doesn't have any of the constraints that it would have been executed in the browser so it's like imagine writing code to manipulate things on the operating system but you can do it in HTML that's HD a pretty much and the only difference between
HTML and HTTP one header tag everything else is very very similar and it runs in the same process model as ie Internet Explorer but just without all the sandboxing and constraints that IE has just two people will wreck that ground on HTA's and then so in this quick two minute demo that I'm going to do I'm going to chain HTA's and des so we talked about HTA's to briefly explain what a DD attack is it stands for dynamic data exchange and it's just a protocol on Windows that allows applications to communicate with each other so if you want order to do something and access information from an Excel document you can use the e to pull
that information from Excel and interact with it in Word vice versa so targeting specific office products word when this first happened everyone uses word where it was hugely targeted so Microsoft pushed a patch in December of 2017 and if your operating systems up to date to exploit this you're gonna have to make a registry modification which is an ideal for us as attackers we wanted to just work when they get the document so that registry modification can be made once you've got code execution you can change that use it to move laterally whatever but it's not ideal for an additional football so moving on Excel it still does work there's no registry restrictions and you
can still execute ddu payloads you see the string that looks a little intimidating but things probably look familiar so that all this is going to be as the contents of an excel the actual cell so you literally go to paste this in a cell and it's gonna execute atomic loss of code for us you can see ms excel this is a kind of a stealthy way to basically if you type run in Windows and type ms excel it's the alias to execute Microsoft Excel similarly to CMD for command prompt all of that but basically we say ms excel what we're actually piping that to execute command prompt which can be done a little more stealthy
but this is just for proof-of-concept purposes I used circa till so basically David was talking about something called lol bins living off the land but it's just binaries that are needs us on Windows all the time or that we can use to do bad stuff for us and it's a trusted Microsoft binary so it's probably not made caught this is somewhat suspicious but much less likely than like a macro downloading something from the internet so cert util is this thing that exists on all windows and it can download files for us so I do Surrey titles and flags downloads and stuff and you can see a CPD attacker IP and the file and I'm downloading is just a
base64 encoded HDA so it's a bunch of an ACH HTML and it's just been basically for encoding then insert util can also decode that for us locally and then I just execute the HDA and a quick note Microsoft Publisher there's an even cooler way to execute DD if you have to specific DVD restrictions there's a way to bypass a lot of those restrictions by embedding an Excel document in a publisher document but that's probably unnecessary for this presentation but it's a really cool thing to look into so here's another sort of gift I've been showing you what I've used this video on engagements and it's very very successful a variation of this but I mean I've also seen this from blue team
learns that they've sent me like payloads that have actually been sent to companies for like actually trying to compromise them just put a picture and people that are you know people that are not security focused or technically inclined they open an Excel document that's like if they already have the inclination like I really need to see this this is really urgent and there's a picture that matches the color and it says hey Microsoft Office you need to enable content they're probably going to do it but you can see me put the DD only exists of the string that I showed you previously none other than that cell so going forward if I completed
okay so we have our milk right here and I receive an email something that I want to focus on kind of kind of tying some things that we talked together previously or talked about previously you see admin at Microsoft calm the reason it's rendering like that is a like I said outlook doesn't typically unravel P decoded domains and B I have a Unicode a domain for Microsoft you can squint at it if you want but you're probably not going to be able to tell which letters puny coded and I'm also not going to tell you guys I don't wanna burn my domain so but I will tell you that the puny coded character renders exactly like the ASCII character so
there's actually no way to tell physically which one's the picota character quite so we got this awesome domain and everybody would ban from all the things and we're gonna download an excel file showing this why we've been banned from all things
so it's just a link directly to the Excel document we open that up there's the image we saw earlier and we're like oh my gosh were banned we have to open this so we enable it you click through to in so here on the right just to give a brief summary we didn't talk about like different see two options or ways to receive referrals but basically I just have a I have a web server on the far left of the screen that's serving honor malicious excel document and then on the right side of the black screen is my Empire listener that's what's going to catch the reverse shell so that's listening we click through the warning
because we really need to see this and all that it's something that makes this a little more believable is because we pipe that content from instead of using just the CMD alias we're using ms excel it says excel needs to actually do something which doesn't look that suspicious so we're like yeah that's fine we need to see this and you can see the the W get that received survey about the Excel document and also the reverse connection so now we have code execution and we can interact with our original so that's basically it just just to read summarize what happened there so we had we've received the excel document from our Pugh decoded domain which looks very legitimate and don't it
wouldn't have to come from Microsoft before I start an assessment I can buy one for your company comm or your company dot whatever so it would look almost identical if I know you're using the outlook client we could figure out a recon we would know what would unravel and then we do it your CEO at your company calm and say hey you did this bad thing you need download this for some relevant reason so we download the excel document when the code executes it hits the base64 encoded HD a cert utility code set and then just execute sit and we get forever shell okay so and just this is the last payment we're going to talk about but
this one's pretty unique color click once and just to give a brief summary of what click one says is something that deploys an application in an expedited fashion when you're using the OEE or edge browser it's been implemented since about that framework 2.0 and a quote from Microsoft Intel says core principle is ease installation of Windows applications so that sounds pretty awesome for us as attackers the main focus is to update applications easily that's it could be something you're interested in but we typically disable it when we're disabling or when we're delivering a Louis not something we're interested in you just want to get our foothold and then yeah who is the next item and so I have a quick proof of
concept just to show you guys what it looks like so think like you have a c-sharp project or like your your binary that's gonna execute malicious code this is like a manifest that would wrap that and deliver it very conveniently if they're using IE reg this is what my web route would look like my application that's been execute is called totally trustworthy so when you when you actually are presented with Kayla this is a very unique prompt which might make it a little more believable also if you can invest in code signing started make it incredibly believable but we did this product and basically it's just like that you can see where ni e and you could reference some stuff
that David already talked about about those cool attaching library rights you can do select if you go to in Chrome or Firefox you could give a little promises this isn't compatible with Firefox please bhasayate view this page then when they use IE they're presented with this unique prompt for a click once application and here's just actually execute the binary which is a little less suspicious than when you get like downloaded some file to disk and now run it and then you can see code execution of just this super simple dotnet code so that is a very brief summary diploma click once consists of in the like like I mentioned what David talked about for htaccess Apache mod rewrites this is a
quick example of how you could do that redirect for forcing like not allowing the presentation of that click once application unless you're using a browser like ie your edge that will be compatible with it and that's all you got thank you guys for listening [Applause]





