A Muggle's Guide To Security In The Cloud

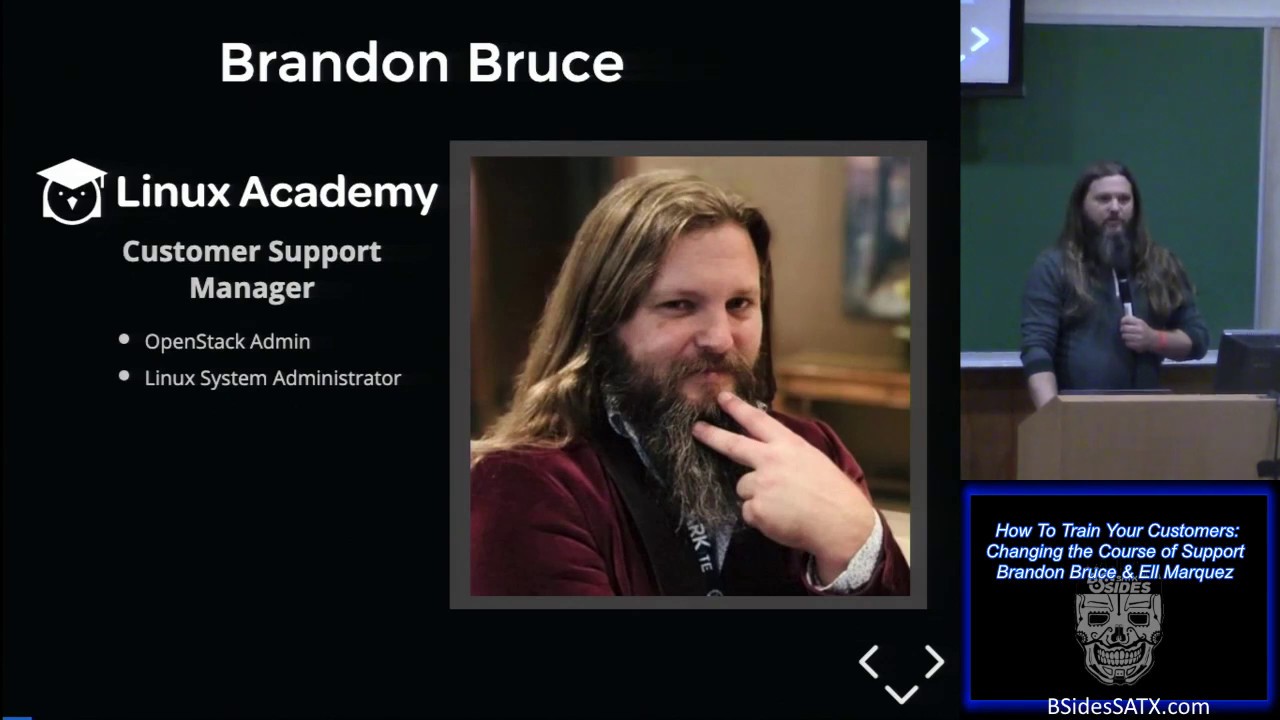
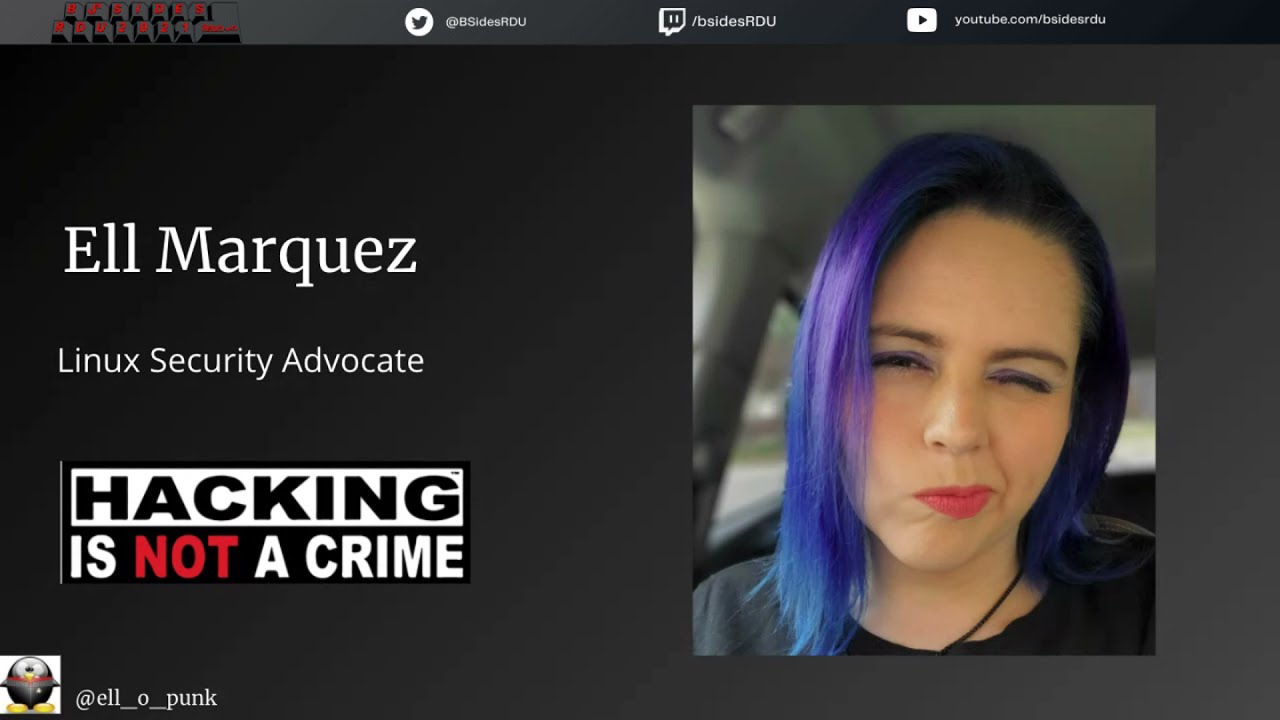
Speakers
Tags
StyleTalk
About this talk
In the security and technology world, we rely so heavily on buzz words to explain our work that others feel like we are magicians working spells that they will never be able to do. Saying: “Due to issues with our security posture, the APT manipulated a well-known CVE to breach our cloud-native-applications.” might as well be: “The Death Eaters were able to use a portkey to enter our environment and effectively cast the Avada Kedavra spell." Instead, we could say, “An attacker used a known flaw to gain access to our environment and brought down our servers."