BSidesATL 2018 - Oh the POSsibilities (Anthony Sasadeusz and Fabius Watson)
Show transcript [en]
welcome to our presentation or the possibilities today we will be discussing a point of sale software and their insecurities so my name is Anthony SAS news and I work as a security worship researcher and firstly they currently listed in support of our security reverse engineering communication protocols and low mobility search my name is Fabius I also worked for their spine as a security researcher and I'm interested in reverse engineering vulnerability research and exploit death and first off we're both noobs at this this is both of our first real research cake and this was our first research project we were tasked with point-of-sale research basically because of its large scope it'll give us the freedom to poke and prod and actually
get creative with it yes Anthony said we're both new this is our first presentation so we have to kind of figure out which tools resources and techniques work for us throughout this project so I'm certain everybody here knows what point-of-sale system is it's Burton it's ubiquitous in daily life where you just end every day whether we are going to the grocery store whether we're picking a hotel room yeah so at the beginning of our research we investigated on some of the high profile security breaches that happened and we noticed that a lot of them were due to point of selling securities earlier than earlier this year and Alba is French I see by the name of our NHIN Holdings
software no security breach in which they discover POS power on their security systems and late last year forever21 also discovered some point of some malware that have been on their systems for about seven months before detective wait and we thought looking at now where it would be actually a good place to start so we decided to download different families of malware actually reverse engineer and understand what kind of capabilities they were actually using so we're going to talk a little bit about POS malware so what a so malware is a very different from your traditional malware the primary difference is their objective point-of-sale malware has the sole objective of stealing your credit card information now the Guderian systems the same way as
traditional malware through phishing or brute force attacks however as I mentioned they're just they just like a credit card game so like maybe I said the main goal of this malware is to get your attractive your credit card data and this is a formalized standard from the international standards organization so the criminals already know what format this data takes and they're able to use this knowledge to Parsons and extract your primary account number your car color name expiration date your security code and everything they would need to actually make purchases so the attack surface 4.0 so malware is sort of familiar to what we usually see most of the point of applications that we saw
are supported by the Windows platform we also discovered something called Windows POS rain which we didn't know about before we started this project which is a POS focus Windows distribution a lot of applications are also supported on Linux or Mac however these are much less common than the Windows supported applications now there are a few big players in this space namely Oracle and NCR but there are a lot of small guys it's a very diverse landscape when we looked at it there are over 3,000 applications and this makes it very difficult to verify each and every one to sure that they're doing them securely so we're gonna start talking about some cortisone our the first one we'll talk
about is black POS black POS n it scores the command line utility for scraping the process memory for track data as a bundle Trojan lactulose includes exfiltration methods apps such as email and FTP and black POS was actually discovered during the forensic analysis of the target range of 2013 next we'll discuss Dexter what make Dexter unique with between instead of the other pieces of malware that we looked at is its ramp scraper actually utilized a white coat a bite Y scaping algorithm which made it more efficient the other mammoth malware families used regular expressions this also ducked dropped a key logging library which if the data wasn't swiped if it was just pressed in to a key to a
keypad don't actually capture that to the leaked the source was also leaked online which newer variants of Malheur actually took and incorporated some of their capabilities so we're gonna talk about magic pls it gets its name from the magic panel which you can see here the attackers actually choose a network rank and scan them for B and C and RDP services attempt to authenticate to them with a brute-force attack after they authenticate they installed a malware which is a adopt net application and then access its capabilities through the magic panel we also looked at something called you post what may beauty post your week is that masquerading as a legitimate program this little legitimate program once logged me in it
says secure remote desktop software it also incorporated some anti analysis functionality which it was installed in a virtual machine or detected antivirus you know eliminates capabilities and the last piece of a point-of-sale malware we're going to talk about pink a pink art relatively new discovered in March of 2018 it's a successor of the pattern malware family it's really small at six kilobytes it kills itself after 12 hours it's sort of the quick and dirty POS malware just to steal card information and remove its tracks this is as I mentioned there's one of the more recent variants so this gives was like an idea of where the point-of-sale malware landscape is now we've talked a lot about little some of
those samples of point-of-sale malware that we've looked at and now we want to talk about something a planarian by these pieces of malware as well as security problems that we have identified in the first point-of-sale application that we want to talk about is called possum Evo possum Evo is a fun cell and inventory management system it's a written Java however when you actually run possum Evo it triggers a C++ launcher that calls the Java code its back-end is uses a Murray SD beam which is a fork of my sequel and when you install pasta and bundles its own Java binaries and my sequel client abilities since possum is written in Java we have to figure out how we wanted
to reverse-engineer Java applications so Java is a programming language that was capable of running on many different architectures due to its write once run anywhere nature and the way it does this is by compiling down a byte code instead of machine code and we discovered that by cooks actually possible to decompile them to a relatively accurate source code representation so our tool of choice for this was my code viewer I like Vidya says it allows us to take the byte code and turn it into a source code representation quite easily and this is this makes it easy to look at source code look at the flow of the program to search for security vulnerabilities and logic bugs
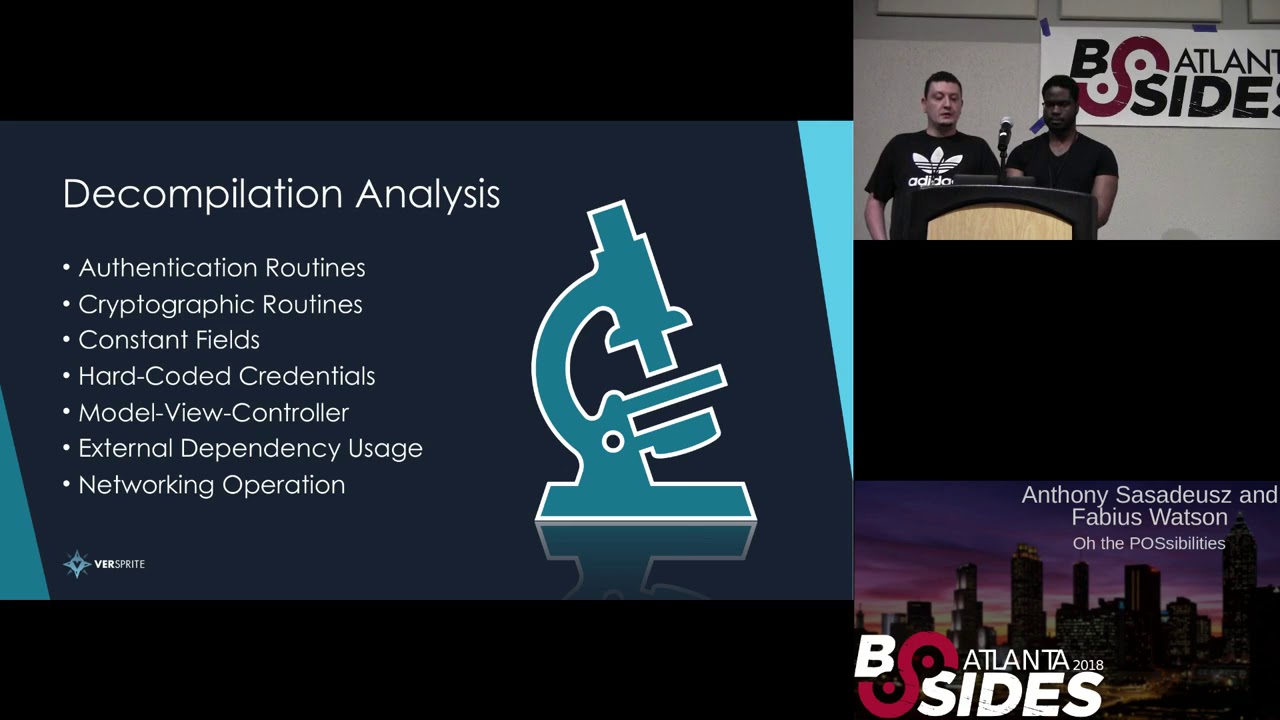
so given this source code representation we haven't sit down and think how do what do we want to look for and the data that we have so the first thing you want to look for in the code is authentication routines because let's see if there's any way we can potentially bypass authentication next thing we looked at was for two graphic routines and see if there is any keys we have access to as low prep users or if they were using a weak cryptographic algorithm next one look at constant Phillips worked which are just collections of variables such as usernames port numbers etc that might give us an insight into what to look for during our analysis and in that regards
we also want to look for in your hard cutter credentials that we could possibly use we wanted to analyze how the model-view-controller code was set up because we wanna see we can take a graphical look at the graphical components of the application and they're said how its underlying functionality was implemented well look at the use of external dependencies because I have an issue with the dependency will be inherited by the application and lastly one's looking at Network operations because as we all know the network attack surface is a very juicy target for attackers so now we're going to talk about some of the things we found with posted Ebola Pasadena our first finding was the use of
hard-coded credentials these were sprinkled throughout the source code of de compilation we were able to use these credentials to login to the Morea database with this with this capability we're able to create user-defined functions which we were able to use to achieve code execution one thing to note is that Reggie beat is started by the to be Evo service and that runs as local local system if we're able to get code execution we're able to execute code with those privileges and here is a demo of us doing that so first off we are going to upload the netcat binary to be later used as a manager we upload our shared library that is IDF our usual flight
function we're going to log in to the database we are going to import the SIS exec function from that shared library and then we use that function to the launch net cap and here it's going to show us logging in to that vine show we're getting that bud shell and we're gonna have those privileges system privileges our next finding with passing eval was what we call override so initially when we were looking at this we looked at the login screen and went to the bottom left corner we saw an override button we thought well this seems interesting what does it do you click on override then you find it'll give you an override code which it then
I expects you to contact an agent and they'll give you an override key to bypass login so we investigated the override code was actually generated pretty quickly and easily but we weren't interested in this we're interested in how this is used to generate a real key so looking at the algorithm to generate the real key we noticed it wasn't very complex at all no crypto involved just some paper basic mathematics so we thought let's write a key generator at least try to and that's basically what we did reported the logic over to Python wrote up a little key generator and this will basically allow us to bypass small volumes and here's a demo of us sorry
here's the login screen we hit override we're given an override code we run our script input our code that was given get our key
enter our key override and we basically log in without any credentials and this will basically give you access to actually open cash register or whatever so the final component of Postum that we want to talk about is something regarding the auto update feature so possum stores a copy of the installation binary for itself inside of the database whenever our costume is launched it checks the version of the application that's lodged to the inversion that's in the database if the burgers are equal opossum lunch is normally if the database is version is higher they'll prompt the user to update their version of possum to the newer version and what's interesting is that the databases versions lower than what the user is
running who actually upload the users installation binary to the database so it'll call DB backup get software state in order to determine the databases installation binary version and as I mentioned if the software version that the user is running is newer than the software is and that's in the database it will replace the binary in the database with the one that the user has so whenever leaves are actually lunched awesome and it checks to see are it checks to see on the version that's newer or older and then the user decides to update it'll look at the database for a file called possum evil GRC so we thought about this and I was a minute
and given our access to the database from the credentials that we got earlier we decided to try to exploit this feature by foraging and installation binary so important to trigger this routine we have to meet two requirements the first is that in the database our binary has to be named possum underscore Evo GXE and secondly the file version hash which is where the application gets the databases version number has to be higher than the version number that was clients so whenever the binaries is downloaded by the user after they decide to update possum test triggers that ex-student launches it so as I mentioned we're gonna use the credentials I've got previously that's hard code inside
it's an applications Largent database create a binary that's to be used for installation and trigger the auto update feature here's our demo of that in action so first we log in to the database server and then we switch over to the possum database context after that one we want to do is want to get the actual version of that store them database and you can see here it's one point fifteen point five you want to update that so that's newer than what the cloud you're running so we're going to change it to one point fifteen point six and then we're going to upload a binary to the server and we're going to name it possum underscore evil dot exe
whenever that's uploaded with a newer version after the user actually launched this application it prompts the user to update it'll say hey you want to update for fifteen point five to fifteen point six after the user clicks a download update it'll download it and execute it in the binary we upload it as a calculated application so instead of actually launching possum it launches calculator instead so our next point of sale system that we would speak on is an eco POS this is basically basically used in the hospitality industry this was a little different than a possum as it was written in the dotnet framework and it also did your sequel server express messes backend so amigo comes bundled
with several different application one of the interesting ones we looked at was called the back-office application so there's some black box testing of this application we discovered that it accepts some interesting command-line arguments and two of them are particularly particularly interesting first one is Tim user if you run back office with attempt to use argument it'll just create an administrative temporary user for you that you can use to log into the POS application or to the back office who's going above the application and perform administrative tasks the more interesting argument is the BBA argument as you can see in this picture here gives you access to the sequel settings allows you to modify and delete database entries
and most interests most interestingly it gives you access to the sequel query window where you can just run sequel statements so for those of you are familiar with MS sequel or sequel server expressed or something called XT command shell that allows you to recommend whenever an email POS is installed it actually installs his local system if they license installs local system which is interesting because you do a standalone install typically the privilege level is lower than that so that was a choice made by the Amigo developers so as I said we're going to use the X people national procedure to actually run commands because it's installed this local system we can use a sequel query window it's actually run
system commands theory so we just click on the sequel query window first we have to enable actually command shell because a lot of settings is disabled by default but due to our privilege level within the database we can easily reenable it after we enable it we can run XP command shell and we're just going to call that cat to startup bike shell on port 4 4 4 4 and then we're going to click a run query after that we're going to open up a command prompt and then using that cat to connect to the local host on that same port which should give us access to a second shelf so the next application want to talk about is called a queue POS
actually pls is another point of sale an inventory management system it also includes time clock options for employees to clock in and clock out it's written in Java so we're going to take a sort of same approach that would possum and its database back in is actually in the cloud so we didn't touch that because I was strictly out of scope for the sake of our research so reversing iqs is very similar to possum as I mentioned we just use bike over here to decompile application and took some of the same row that we discussed earlier when looking at it however a lot of that didn't work it took us a little bit longer to
actually find anything interesting inside of a cute POS we have to think outside of the box so yeah we we couldn't find anything initially so we kind of had to get creative and how we were looking we have to take a brand-new approach basically and now I'm going to run through some of the rabbit holes we fell through and what we were trying to do so first off we noticed there was a java key store installed with a Q POS now we alongside that we found using static analysis that the password for this key store was basically put in there Clark coded so we tried to extract the contents we were able to do that we
got a certificate we got a key material then we tried to basically decrypt the communication traffic going to the cloud we tried to do it but we failed so what next we looked we want to look at the network attack servers now we did notice that the Java process was listening on a port so we wanted to look at the code and look what what was actually doing and how was it using it we found it being used and not just one instance class and this basically only checked to see if there was something listening on 4 1 2 3 4 5 if there was it would assume it's a Q POS and it wouldn't want some
of the process and this basically got us nowhere also next we wanted to look at final Karissa's what file permissions were giving to active POS in LaFollette was install we used a utility called I cackles that is bundled with Windows and it revealed that all authenticated users who are provided with modified access and we figured that we can actually backdoor so we did some research that we consider dealt with so given that we're able to essentially modify jar file we come up with something called jar jackin jar file for those you don't know is basically a zip archive and they contain the class file as well as other resources for the application the class files actually contain the code so our
ability to modify this file allows us T essentially reprogram the application and recite to look more into jar jacking from a post exploitation perspective and this led us to the idea to develop a Java implant that we wanted to put into the jar file so an implant is basically a cobra piece of software that gives someone access to define capabilities some of the basic of abilities that might exist are push and pull and exact which allow for file transfer and code or command execution this led to the creation of something called runaway rep sorry so we decided to build our Goa framework for this we wanted to actually emulate what a real attack or a real
criminal organization would actually do and what that would look like so a little repertory is our framework it's basically an effector and implant not a command and control server or a Student Center our tag plan was basically injected implant code into the application jar from a little frivolous context modify the class in the jar to actually launch our implant demonstrate capabilities that we want like you know being able to grab our credit card data you know X fill it and whatnot and you know make some money right of course it's actually a joke we reported all the things that we found to the vendors and some of them responded appropriately but they they got all the information they
needed in regards to anything that we discovered so I basically architecture for one repertoire was the effect it was written in Ruby and as a post exploitation module we used Java for the implant with a little bit of C++ that leverage AAA and also a Python for the command control server with plasterwork so the C 2 that we designed that gives us equal life for database back in halves of the web interface they see here for operators to actually operate on the implants and it includes web endpoint so you can see that the implant actually communicates back to in response to any commands in order for the in flex even communicate to the c2 pesky register
prior to registration a client can really communicate to the CCO just responds with an empty response and the way an implant register of the c2 is through the effector which provides the c2 with information such as a Geo ID a registration key of abuse for cryptography and a copy of the original jar fell for future disinfection after an implant is registered with the c2 and then is able to authenticate it does this by sending a packet authentication packet that's encrypted with the registration key and all the c2 pact agenda is basic support coded prior to being encrypted next let's talk about the design of the implant that I've made it follows the singleton design pattern
which prevents what more than one instance of an implant for running at once all of the classes that the implant uses our threaded which prevents the impact from affecting the POS applications functionality in any way and all the commands were chosen to demonstrate or list ik attackers so this is based on a lot of stuff that we talked about earlier regarding the POS malware that we invest in it and the primary thing that we wanted to emulate and improve upon was the Rams great being implementation now it's worth mentioning that our reps great burger different cuz they're different from the rep scraper that a lot of malware looked at uses because ours is much more
targeted we are implanted inside of the job application we share the same Java heap so we can form a much targeted ram scraper because we because we share that heap and we know where the track data is being stored as job objects now has to in order to do everything we wanted to accomplish we had to learn a lot about low-level Java in particular we had to learn how to use unsafe class over to the week and address that's on the JVM geek now we also have to learn the cow Java represents pointers using optical ordinary corners or compressed oops and also we had to learn how to use Java to access to leverage some see from our Ram
scripting code so first off we wanted to leak an address on the JVM deep we could use unsafe for this but it's usually used as a for Java internally slowly we are able to use this by jumping through some hoops by using a reflection and we are given access to the methods possible was important for us is because we wanted to be craft cross-platform we wanted to be able to run them all on 32-bit systems and 64-bit systems and we can address we had to understand when and where they would give us back a native pointer or what when it would compress that pointer what we actually had to factor it back and do some
manipulation wanted to actually get a correct address and also we wanted to use the Java native access to leverage G code we decided on C code because the win32 API has a very powerful process memory functionality included in it but in order to do this we had to take a few steps to actually set up the process to be able to get the JVM heap to send it to our native side first we had to get the process ID of the Java process that we're actually living in latina handles to that process clearly the information about the memory region that we're interested in and then primarily copied that memory region which was the JMP to a buffer and then we basically take
that book we have passed the to Virginia Jane a side to our C code and then you know scan firm tractive and basically our tracks are fully written in C basically was modeled after what Dexter did likewise tracks hers nothing except like we said our method was more targeted than their approach so next we're going to talk about the vector component of burning red fire so initially when were playing around with modifying jar files we're using a jar archive tool which is included with the Java developer tip however it was limited it didn't have the functionality that we actually need it so we actually use our vector to pour on any jar jacking now in order for the vector to
be built we used Ruby and built it with Metasploit at the post exploitation illogical the way it works is it actually picks a class within the jar file and replaces it with a modified version that triggers are implied code as well as performance original operation in order to choose an ideal target class to inject they have to meet two requirements the first one is it has two blocks relatively soon that are so that our implant is Luxan and secondly needs to be able to be re-implemented with accuracy because we didn't want to change the functionality of the actual application so and the infector is initialized the operator is able to send four different options since well since
you support callback which determines how often the implant actually calls back to the c2 and jar pad which is used to change the target jar path in case the application is an installment of default location so whenever the effector begins it first generates a key to be used for communication initial vacation to the sea to the vector also happiness the implant class so whenever I compiled the actual implant class I included these hard-coded values of integers in the binary and I replaced it with the values that the operator provides through Metasploit for ctoc support call back so that i have a sort of modular implant component after this happens the effect actually registers the implant on behalf of the target host
to the c2 and it does this by sending jeju idea the key in the original jar file to the c2 through a post request to the registration endpoint next all of the resources are bundled into a copy of the original charm all the DLL resources needed for JMA as well as the class files needed for the implant are added to this jar copy and all of the class files are actually modified to include the version number of the target system so that's compatible with the version of Java that's running on that system lastly the effected copy of the jar file is copied over the targets application jar file now completing the process of infector and any subsequent lectures of
application will launch our implant code this is the completion of the runaway Reptar interaction process and I'm going to demonstrate that here so first I want to show you guys the original state of the actor toast jar you can see it's 331 megabytes approximately and the shop c-56 starts with zero seven one one we're will go over to attacker machine to show the infection process so I'm going to just set some options inside of the next point and launch the infector after that simply run away Reptar is started you can see that the acting pls jar file has changed as it cleaned a different hash and that's approximately 380 megabytes so this is the runaway
repertoire c2 interface this is where the operator will perform all their c2 tasks and this is me actually the implant list right now we just have this target you can see there's a JavaScript command-line interface for anyone to type in commands UPS type with who am I to demonstrate that as well as I keep them fake to show the network settings next one I demonstrate the push capability which is to upload a file to the target we're going to upload the hosts file as an example soon as a target desktop mindin II don't mind any typos in this demonstration so as you can see on the desktop there's almost fell and we open it up it'll have the
contents of the hosts file that our c2 has following this I want to show pulling a foul from the target we're just going to pull wind I and I just common foul on Windows systems and I'm this a looot button which actively takes us some loot page now the way the loop page works is it identifies the target based on the machine geo idea so the implants restarted and has a different registration code that doesn't matter because the loot is based on GID and all the files pulled from that system will be in this folder click on this and download I'm just going to open it with them and show that these are the contents of the targets win ini file
next we're going to show the more interesting component which is CC Dom so there's just dump our page which is empty originally because there's nothing dubs however as things are added they'll be added to this page so what we're gonna do is we're gonna go over to the go over to the target machine run a queue POS and log in and we're gonna buy meatball sub just about 5 bucks which is we're going to end our credit-card number which is the visa one of these says test numbers and random expiration date and click process card now we're giving this error code doesn't actually set up so the back ends actually work however the application at this point
has loaded the card information into the process so it's in the Java heap so our CC double still work your click CC dot and then we go over to dumb file and after refresh we can see the test card number that was loaded into Java process actually going to show you the the persistence component of a runaway direct target so the way it works is actually uploads about to tactical file location and then creates a registry key that actually copies the persistence foul over the application binary you can see here it sends an 80 megabytes just as was the the infected version of the jar file and if we open the registry editor you can see this are our key in
the registry which has the command to copy the file over now after persistence is enabled you'll see this persistence true turns green at this partner is going to demonstrate cleaning up so first we're going to disable persistence and then as we know we probably fall over to the desktop or our move at home so we're just going to run dirt on the desktop path and then delete that hosts file that we uploaded earlier next we're going to actually verify that that has been deleted as you can see here it's not there anymore so then we're going to clear the command gives so that no more commands are loaded and we're going to click disinfect whenever a disinfection is
complete it will actually remove itself from this implant list and here we're going to go back over the target machine and show you that the original jar file has been recovered from the sea to database and you can see here it's back to 331 megabytes with 0 7 1 Schatzi 56 hush and you know that concludes our demonstration of the runaway reps our implant that we design
now we're going to talk a little bit about future research so we're honoring Reptar it's cool at least I think it's cool but we want to actually implement a universal jar jacker we add into the knowledge of a kewpie lesson is jar file a new wood plastic target but if we took a look at the manifest file identify the main class for the jar file and modified it to my code with a runner and run away reps are stuff then we can potentially implement a universal jar jacker also we like to upgrade our xor cryptography scheme to SSL because that's a more robust and secure and lastly if we implemented a pure Java version of runaway Reptar would be
cross-platform we would rely on the j.j stuff or do else we would also be interesting this actually look at the payment terminal hardware itself and we were first engineer the protocols that are used between the point of interaction device and the terminal and can we actually lever just maybe men in the middle attack or what not also is memory card memory crompton bugs thing on these devices but that would be interesting to you know attack the Hat attack the stack attack the heap and gain a game some bar code execution that way or are we able to run unsigned code on these devices and if we're not can we can we fool the device to fake a signage
of the code so we talked a lot amount of a POS malware and faculty most applications and this cos gave us some attacker perspective gave us inside the two possible indications that could be implemented to fix these things first thing is code signing a file signature if that was implemented run away wraps are wouldn't work we shouldn't have the ability an attacker should have the ability to run untrusted code as the application and you know make sure your applications who are running with the least privilege necessary you know a few of those demos we were actually leveraging their privilege getting code execution and getting higher privileges because of that next we want to make sure that excessive confirmations aren't
enabled the fact that any low privileged authenticated user can modify a core application of a terminal is foolish to say the least and please don't include part coda credentials if you're deaf even if you try to obfuscate or do whatever it's you know a researcher is gonna find that it's pretty trivial and you know unless you're a PhD in mathematics don't roll your own crypto there are plenty of third-party libraries that are vetted to be to be secure so some takeaways from this talk and some takeaways from the research that we did leading up to this talk is exploits aren't always necessary for a runaway Gravatar we took advantage of a Mis configuration that could have
been avoided and it was purely a post exploitation exercise so X plates are are always necessary to cause damage and reverse engineering Java is pretty nice because you get the source code representation rather than dealing with native binaries and staring at assembly code all day also we found out that credentials and clear text it's actually a pretty common issue for instance with opossum we have the credentials that were in a job of binary blood Java is decompile boy and with amico although we didn't know their credentials they were saved and stored and loaded by a low prep user and never trust point-of-sales software with your data so there's a something called PHP or point-to-point encryption which actually
encrypts the data at the time of actually swiping your card or entering your chip and entering your PIN before it even reaches the payment terminal if this becomes a more widespread than the application doesn't even get a chance to access any sense of information and that would no matter how vulnerable the app is they'll just never get your track in in that way any questions so so it encrypts that swipe down right away right as the swipe happens yeah it actually works there's an application or its application layer on the point of entry or point of interaction device depending on the vendor where it's Vera phone or Ingenico they have a API that the developers can use to encrypt the
data at the application layer of that device prior to actually sending it across the wire although in my belief I think nothing is 100% so yeah we'll see yeah well nobody can so the data is encrypted we did use a we did use an endpoint such as register and c2 we're trying to be stealthy at all because it was a point of a proof of concept but not I was curious on the unsafe usage of how you did the main memory scraping I know that there is some protection around memory scraping and whether or not we haven't checked if it's a behavioral detection work and you can memory scratch how do you work on we have been working on it
so we haven't looked at any done at Sakura Sakura street implementation and the inside of Chios applications the amiibo help us which we talked about earlier wasn't in dotnet but we didn't see it use any secure strings to like hide any admittance of information well that is something that we could look into bro to be honest most of the applications we dabble it looked at we're written in Java yeah it's very about 90 90 plus percent it was very unpopular yes so muslim' didn't really have they didn't care but some of them did respond and we're in communications with them for updating some of the more serious things have been fixed us but some of them were marked as won't fix
because I guess they don't see it as an issue but the more serious things were addressed well we disagree that's a yes so so we've already published basically our work on this or not on our blog and we can now give everybody information on that at first right calm basically the additional questions alright well that concludes our presentation





