BSidesAtlanta 2019 - Ray Kelly - Mobile Apps - The Good, The Bad, The Worse, and The Ugly
Show transcript [en]
all right welcome everybody I'm Davis I'm a KSU student here we have a quick thank you to our sponsors Kennesaw State Department of Information Systems the NS a coal fire and ku now ski security so pregnant reduce our speaker Ray Kelly
great job Davis yeah so welcome to B sides and thanks for coming to see my talk hopefully we want to see some really bad mobile vulnerabilities that are out there so we'll definitely have some real examples of those we'll take a look at this a little about me so I've been developing for over 20 years than just normal developer so I've written plenty of honoring felonies but in internet security for about 15 years and I got my start of the company called spy dynamics that was founded here in Atlanta and and my mother I was the lead developer of weapon spec so I was like one of the early developers of the web espheni wonderful web inspector fiddle
hmm so I wrote most of that product and they into the early days and kind of went through a whole ton of acquisitions from HP HP enterprise now to micro focus along that route and along that route also let our mobile pen test team our fortify on demand areas we're going to do cloud-based services pen testing so we test mobile apps and so some of the examples we'll see here are some of the horrible things that we see that we saw coming through our testing process just couple of considerations so everything we're in it I'm going to show you today is already publicly known or it's been anonymizer scrub so no zero days for you
guys today the other takeaway here is that these vulnerabilities that we're going to look at they weren't intentional these are malicious actors that are trying to hack us right these are actually developers that are just writing code and not giving a lot of thought to security and we'll go into some reasons why as well for that so yes so these developers have the best of intentions they're not trying to harm us but we have these vulnerabilities talking about just insecure devices this really has nothing to do with anything but love telling the story I was watching The History Channel a long time ago and actually have stories on history and they had a story about this paper
shredder and it was back during the Cold War era and what they did was they there was a hotel in Washington DC where an important dignitaries would stay so presidents kings what-have-you they'd stay there when they were visiting the the president and in each of the hotel rooms there were kind enough to provide them with a paper shredder right you have to shred your important documents while you're traveling so the interesting thing about this though is this paper shredder was made by some three-letter acronym of our government and what they actually had done was built in a pace painting device at the top of the shredder so as you're reading it and scanning the document and
actually sending it over the electrical line through like old school pulses like the electrical pulses like a modem of dude and then reconstructing the document in another room and then in the hotel and I was like that is awesome
so the mobile landscape I imagine most of you have mobile devices at your company our mobile apps yes and I'm just curious how many pen testers we have in here how about QA folks d QA man I want to see QA people these security conferences how about developers straight-up developers great so as most of you know Mobile's hot everyone every company wants their mobile app they want it out there now right instantly if anyone's going to put features over security it's unfortunately mobile developers where it comes to and there's a couple reasons for that one is they're not trained in security typically and the reason is because sometimes mobile apps are so easy to make look at Cordova and all these like
drag-and-drop apps right you're just thrown together mobile apps me and this is great I'm putting this thing together and it's done and they ship it out without really any regard to security so training and security for mobile developers doesn't happen that much so those are some of the challenges that we have with mobile the mobile landscape are looking at devices they are growing just insanely write read like five billion mobile devices in 2019 and that's just going to keep growing so the number of apps are out there think of that threat service on all those devices that you have your apps installed on we did a case study where we took 120 mobile apps and we analyze them for
vulnerabilities and we found that 66% of them contained a critical or high vulnerability and and when we say high we're saying it either disclosed some PII that we found personal information so for instance if you use your mobile app elog know if you use named password or filled out personal information within the app we were able to get that from the device and pull it off because it was normally not encrypted so clear text storage or we were able to compromise the back-end system and that's sort of like the where I have the most fun is on the back-end systems because another thing when you're making a mobile app the developers are put it together and they create some back-end
endpoint right so your mobile device is going to talk to an endpoint and people think that well this isn't this is just a a restful service it's not going to be indexed by Google no one's going to know about it or I guarantee you the bad guys are going to know about it they're gonna find that mobile backend and test from things like sequel injection cross-site scripting as a open web server good thinking use to upload anything you want and I'll have an example that to that we actually saw there's a so when you talk about normal like application security and mobile specific security there's two important differences one is you have a magnified Network vulnerability or
threat service and what I mean by that is I mean you think about your mobile device you're in the airport right or you're in a hotel you're traveling now and you find some Wi-Fi right and you go find there's something they cache ad free Wi-Fi click here to join right and you know and you do you have no idea what's happening after your data leaves your device you get on to it and then you saw the talk just before this one right someone's got the pineapple running if they're doing man-in-the-middle so you join that Wi-Fi and all sudden they're sniffing all your cookies your credentials everything you're sending over that network so the idea of how
easy it is to connect your mobile device to any network makes it all that more important the other one is the physical vulnerability so and this one's pretty easy you leave your device somewhere right I left it somewhere you forget it well then if the nefarious person finds your device and they actually know what they're doing who knows what they could get off your device if those app developers didn't do things properly and again I'll have examples of that and so this is kind of embarrassing for all friends here right so I can't I gave this talk to a user group for a company and I got to this part I said magnified physical vulnerability
and I go to pull out my phone and it's not there looking around and it's playback in the room and I'm where I was sitting to watch a talk before this one and I had left my phone back there on the table nothing yeah you know that's an example there guys of how that could happen and they decided he either good then so when we assess a to do a proper assessment of a mobile app there's three areas that we're looking at we're looking at the client what we mean by that is the mobile device what are we looking for there so if you have an app installed the biggest one that we're looking for is unencrypted data so when
you type into username a password and you hit go is that app properly encrypting or protecting that data on the device poor certificate management what type of data is being stored so those are some of the things that we look for on the device the next one is the net player so the things we're looking for their simple ones are they using SSL right are they encrypting the data to and from the endpoint we're looking for backdoor data leakage you know so say like you install a in your application you want analytics right well if you install some app analytics library say crashlytics or what-have-you where's that data going and is that encrypted and what does it include
you know because you don't always know right you just need analytics it's easy enough to throw in a firebase or what have you but what data is that actually grabbing from your device and sending to the back-end server are you leaking PII from the user so that's an example there and then we look at the server side and I talked about that just a few minutes ago we're looking for injection flaws authentication privilege escalation sequel injection all the normal web at the type owner abilities that everyone's familiar with all of those apply to mobile backends as well nothing changes there so when to do a proper test you want to look at all of these layers to
really ensure that your the entire app is safe any questions so far good so let's start digging into vulnerabilities now this is an example here so again we're talking about server-side vulnerabilities and we did a test of a mobile application and they had a back-end API just like I was saying it's not it was just a restful endpoint there was no content there it was just API endpoints and what they have found is they had enabled WebDAV on there so they allowed the put method and so basically it turned their server into a open file share we can put anything that we wanted there and upload anything so the example here is we actually did this
as a real screenshot where we uploaded an HTML page that had a hyperlink to evil link which would contain most likely now let's say that if you click on it so what we would do is open this upload that file copy the URL because actually has the company's names right company.com slash our page that we uploaded and then what we're going to do is take that and then span that out via email to you know it's a million people through whatever service and it looks like a legit link now in the email but yet it's our page that we uploaded so you get an email you go click on it oh look here free tickets absolutely click
on that now you just got infected on your device or on your computer and so the important thing though again this was specifically for a mobile API had nothing to do with anything else but we were able to utilize it to exploit other users
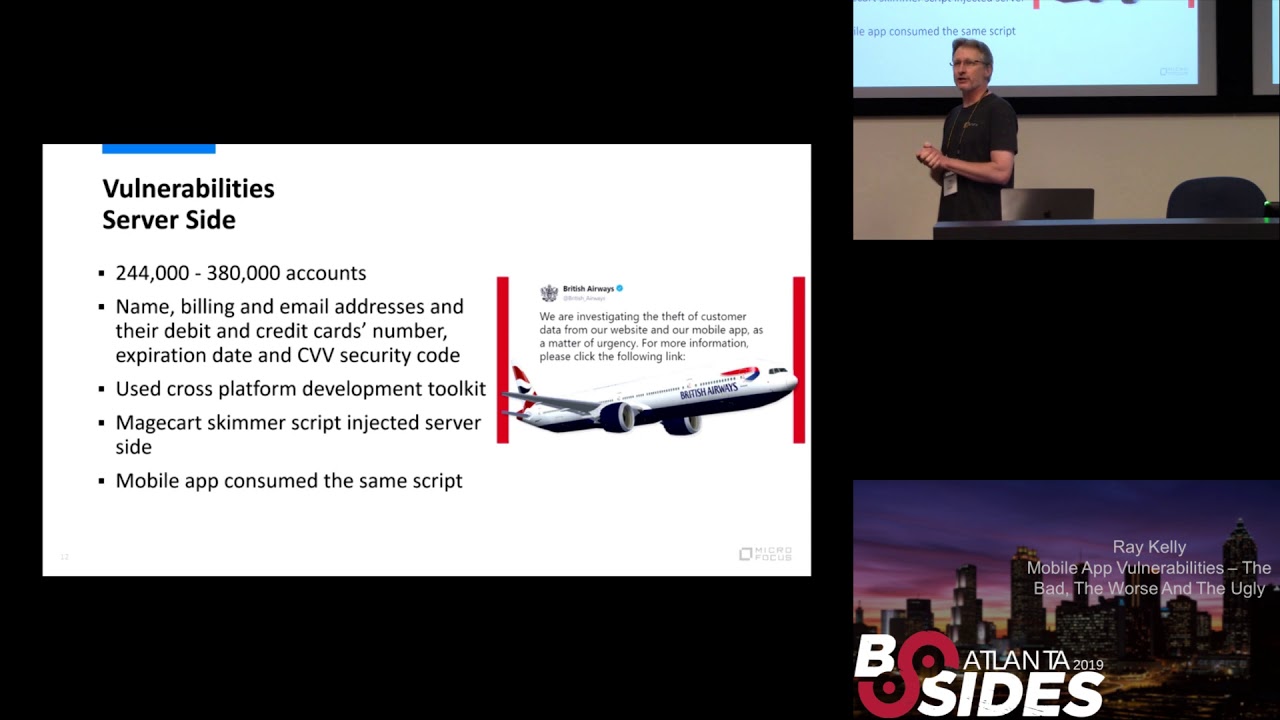
and we hear about the British Airways hack happened last year that was a big one so from a quarter about a quarter million accounts were compromised and will be being compromised if this was a bad one they got billing addresses emails credit card numbers the CVV code your secret code then you type in when you purchase something and this one was really interesting this one was pretty fascinating because it was originally an app for their website okay so their website where you want to go buy a ticket for British Airways you'd fill out this information well they were compromised and the page that collected that information had a mage card skimmer stripped and stolen so nothing anyone
heard of mage part it's a script that basically when you fill out that information there's some JavaScript that parses well what it would do is it would take that information and send it over here to your server and to British Airways server so the bad guys were getting copies of every single credit card transaction that was happening so I don't know if the people that did this knew how much how effective this was going to be because the mobile app developers said oh I'm going to use Cordova or some cross-platform thing and I'm just going to drag and drop hey there's that script that does credit card transactions already on our server so I'm going to just pull that same
script down into the mobile app and I'm going to use that a piece of cake well that pull down the same mage cart script the credit card skimmer into the mobile apps now you went from one endpoint that's been compromised to hundreds of thousands everybody that had the British Airways app and bought a ticket had their credit card information stolen that Hoth are taken through there because they were sharing code from the server room so that one was kind of neat how that could happen another interesting thing too is this is one of the first instances of gdpr that was this was like two months after GDP armours enacted in Europe and I just googled before this talk to see what the
find was they were still they were kind of blown away by oh my god this has already hit us I still have not seen a fine or what they got hit with but if you look at the rules and how many you know they charge per defined as per how many affected users were there this would be staggering and everybody that had the mobile app so I still haven't seen any info on what the penalties were about here's another one this is a simple account enumeration okay so this app was called bright city and it was apparently a popular app for local governments so let's say I live in the loganville it's where I live so the city
would say hey you know we're helping you protect your property you know there's been a lot of break-ins what you can do is use this app to catalogue everything in your house and it sounds crazy but in a way you know if your house ever burns down I've kind of heard these before you know you want a catalog you want pictures of what you had so you have a record of what's important in your house that's worth money so these governments were pushing this app onto everybody saying hey there's really helpful for these cases we get robbed or if your house burns down you have this evidence now what's in your house you can go to your insurance
company well they had their back-end API for the mobile app didn't actually validate when you make calls that you're the actual user that logged in to make those calls and it's kind of hard to see but here's a call here to their API that says get user and you put in your ID let's say it's one and it comes back and it says well that's Ray even though you're Joe or your Davis it would say well you're Ray and here's everything that came back which included your phone number your username and your password to your account to write city now I'm going to go get number two number three number four I can own everybody's account
through this do this mobile API back-end and so I thought it's kind of fun it's kind of Amazon for criminals right man I need to look for a flat screen TV fifty too much I'm gonna log into here and see one house and then I'm gonna go and try to break into their house and go get into silence oh and something else to notice too this is using SSL itch so it's HTTP so the problem is that doesn't protect you from accounting numeration right if I'm on the back end if I'm the one hacking you going thing SSL do is doing is helping hight me actually from the company that that I'm attacking you know because it's going
through the web a firewall it's still encrypted so that's a sell actually didn't happen it doesn't help in this case so now won't work a move our way now into the network layer so now we're on to the next one this was an example here that we had in this mobile app was for a big time boy damn know so think of like New Kids on the Block any new kids fans in here I know we got one up there my wife so if you think by this the target demographic for this app is like 12 to 16 year old girls probably for this boy Dan and we're testing the app and our testers so a part of our testing
process is watch Lee install the app on a device and run it through a proxy and watch what you know we're looking for data leakage what's what's happening we're stuff going to and stuff flying by and all of a sudden the tester notices a request go by it has his home address in there down to the street number one two three here Street I mean it was dead on and he never typed it into the app never even put it in there and so what we were thinking is they're just using GPS or Wi-Fi location you know just to figure out what address in my app but the this company that made the mobile app or the
boy Dan thought it was a great idea just to take that from you and send that to their servers so that one was pretty scary is that a vulnerability maybe not certainly a privacy issue as if the user never agreed you know to give that sort of information by using the app another example so I had written a tool I was trying to make something for our testers make testing mobile apps is painful right there's a lot of setup involved you have to you know try to get in the middle you know if if your developers doing things properly actually pinning the certificate and everything's done properly just makes a little more difficult so it's painful so I was
trying to find ways to make this easier and I had taken the Android operating system maybe I'll just make my own Android operating system right that we can install the app on so I took the source code and made some modifications where I would intercept things from it like any time a network request is left for the device I'm gonna grab it before SSL encryption occurs and login so that way we can install the app and just see what's happening as far as the network traffic goes so I install a popular social networking app I'll say which one it is but it was social networking related and I'm testing it I just started testing as like cool man there's
some stuff going also and I see this chunk of data go out I was like oh my god something just happened something blue something must have gone wrong and I started looking through this chunk of data and I know you guys can't read it but to read some of the things I got highlighted in red Wi-Fi info home screen mode is your Wi-Fi enabled screen brightness key card type for instance is your are you using what kind of security using to get in right you are you using a pin code how much free space is on my SD card let's see what else is in here what kind of camera configurations are on the device so by
using this app they just pilfered all of this information about my device and someone to set up and just took that you know without my knowledge so again that was kind of an example where they're just taking information developers thought that would be a good idea and maybe their Terms of Service allows it but I certainly didn't care for it care for that to see that happen
Bose headphones so this one came out and what they were doing is so all these newfangled your headphones right they have mobile app so you can do the EQ you figure things well apparently the other thing to do is steal your listening habits and what songs you're listening to and take that information and send them up to their server also so again you don't it clearly doesn't show that in the app but yet they are doing that in the background yes
I they certainly could my first thought though for the last note for the social networking one my first thought though was marketing you know selling information you know or even think of advertising right so it sent up how much free disk disk space i had on my device you know i'm scrolling through my my profile you know post also here's an ad for hey you need a new SD card here's you know blah blah so they can actually target me directly from that kind of data you know or tell that i'm at an older device and all of a sudden I start seeing ads for new phones that are coming out so or just selling that
information to other marketing firms or even device me factors how many people you know what user base is using Android versus iOS I could sell it's just money you know all that information that was kind of my first thought I could certainly see finger printing as well easily
ok so now we're going to move on to the client side so now we're talking about the device itself Starbucks mobile app users so this one's quite a few years ago but it was kind of a big one that maybe it was crazy there's like four big mobile horner abilities that came out in a row and this was one of them does anyone remember this that they the announcement about us the Starbucks mobile app had some issues well say Starbucks coffee I'm a Dunkin Donuts coffee man myself so the crux of this issue was that the developers used crashlytics most people do that right so they add that so they can into their into their project and
but what they chose to do so crashlytics you can log anything you want you can you know it's there to track issues and such so they were recording the screen where you log in so when you would hit login after you type your username password it would log what that HTML page looked like at that time so unfortunately it included the account news mate and the account password and that was actually being sent to crashlytics you know unintentionally I mean they probably never even thought that that was really gonna happen they were probably trying to log stuff and they unintentionally grabbed usernames and passwords and started sending that to a third party now I'm sure no one there was looking at
it but just the idea that that got me down so it was kind of funny so the press whoever put this out issued a release you know when reached Wednesday crashlytics a boston-based firm that specialized in crash reporting solutions couldn't comment on the specific customers but did reiterate that the firm doesn't recommend developers log sensitive information so that's not our problem the solution is don't do that
logging so this is a great one our test reviews we always see all kinds of stuff so if you're doing a debug logging console right that sort of thing in your mobile apps a lot of the times developers don't take those messages out before they ship them up to the App Store and so you can find lots of good information there and this is an example of one here where we actually saw a user name and passwords being written out to the device to the console also so it's sort of a developer stuff that they just don't think to take out so that's an easy target there so this was a good one this this issue's been pretty much
eradicated in that with sandboxing and some some things that have been done over the past couple years but we used to get a lot of banks right back when mobile apps were just coming out for banking for banks and they had that feature where you can take a picture of your check right in the positive well we tested the app and we may sent it to said hey hurry up man we're putting this thing in the App Store let us know you know we're gonna hopefully do this today okay we gotta test it so we end up testing it what we found is when you take a picture that's checked it was story it to the global camera roll not
the sandbox or the the applications directory so any app had access to these checks and things that were being for the pictures that were being taken so we sent it back and said well you guys have a vulnerability don't don't do that and so like oh yeah okay we got that so they sent it back the next things that we fixed it by the way we're submitting this to the App Store right now tested you know cuz we're in a hurry and again that goes back to that pressure that developers were under to get their mobile apps out you know so I said okay so we tested again did it show and they did they fixed that issue but what we
have found is when went into another feature you can actually go into an area where you could see what's been what has gone through your your bank account and you can swipe through deposits and such that have been in there so you just keep swiping and as you're swiping it each one back to the global camera roll again so it was storing everything back there so you're like no don't so we sent that back again but the kind of an example the again the pressures that they're under this is pretty hard to come by now it's actually kind of hard to get out of your sandbox these days when you're storing data for your application so much more rare client
debug screens so this one's interesting you know with different tools there's one called flex for iOS where it'll let you wrap the any application basically and get into certain aspects of it it'll it'll tear apart the memory it'll look let you look at variables or stored within the application and one of those is you can actually trigger activities or storyboards or screens within the app that aren't visible always so a lot of the times for to be helpful the developers will put in a secret so if I log in this admin in the app there'll be an extra menu item let's say that says debug where I can get in there and look at look at certain things
and some of the ones that we were able to find it had come through it's like you know disabled sir pinning it for this one upload log file incentive and what we found on that particular one for this application is the back end didn't validate at all what was being up limited so we we sniffed that we uploaded a log file we say okay here's the end point and we uploaded a JPEG anything and it accepted it so kind of like earlier it became it became an open onedrive for us or Dropbox because of this feature so and we had another one over here with this one had this one here it allows you to change between
production staging or canary or like QA well that just tripled my threat surface for this application now I got three servers go attack and find vulnerabilities or not so being able to find information in these debug screens is a big one and one of the big ones that we do help me tell people is you know don't ship those and these are in the App Store versions of these apps or they were at the time that you know the food before you build for the App Store take those screens out or make it a conditional compile statement that removes that activity so they don't get a shift with the application so this one's one of my favorites that we didn't
run across I saw a talk this morning and it was mentioned where they were talking about Alexa's and voice recognition and such and so he kind of touched on this vulnerability as well so we had an app and this app was so secure use voice recognition to login it and so you would go in and say login and say hi my name is Ray because I had recorded that and it would let me into the app it actually worked other people would try it you know we couldn't get around it seemed pretty legit that it was working so one of our testing procedures that we do is when we use an app we'll take a snapshot of the
apps directory on the device ok here's what it looks like there's let's say 20 files in there and then we'll use the app for awhile I'll record my login I'm going to use it ok now I'm going to take another snapshot oh look there's 25 files that exist well those 5 files interesting now so I'm gonna go look at each one of those and we ran across one file that made no sense it was like zebra XY see the file name the extension none of it makes sense and so we open it up into a hex editor or just some notepad just to see what's in it and it's all garbage it's just completely binary mess I thought
okay well either it's encrypted which is great or you know there's some other uses for it but it doesn't look and then wait a minute let me see here at the near the top of this file and we start seeing clear text words like genre you're made title anyone mp3 files so movie thing so what the tester did is he took the file copied it off on this computer renamed mp3 hold the phone I hit play hi my name is Ray got into the application just like that so an example of where security to obfuscation right I'm gonna rename it to something that doesn't make sense and no hacker will ever find that vulnerability so I
just couple of resources so oh so what this is all related to application security you know we're talking about social networking networking security my favorite of course cuz a web inspect and is app security so this falls right in line with that so oh waswas a great resource for that they have an oval top-10 for mobile apps specifically so if you want to go see what's the hottest you know what are the top corner abilities right now you can check out it'll us for that
this one here actually so this one's kind of out of date but I think it still works is called goat droid so penguins heard of web goat for testing web applications they have goat droid which is actually a vulnerable Android app and so you can install it and there's a course where you go through and actually hack the application and go through the different steps to identify things so that's a that's a good resource on that and I had mentioned the OS mobile security project which has the top ten listed on it and a whole bunch of resources and tools as well for testing mobile apps and that is the end of the presentation you can follow me on
Twitter its BB is best there goes the rest of my credibility of the window but I'll be there and I'm open for questions since we have plenty of time I think anyone yes that's a I get that question all the time and that's that's tricky so these vulnerabilities that we're talking about here today it doesn't matter if the developer is not encrypting your information on the device it doesn't matter what device you're using so these developer mistake issues isn't really specific to any one platform what it what I do find different though is malicious actors people that in uploading Angry Birds of Melissa's malicious version of it I think you'll find plenty of research that says
Android is definitely worse in that case that there's much more malicious apps out there it just seems that Apple's review processes to be more thorough so I would say in that case you know iOS for malicious activity is a little bit safer but for these type of developer mistakes it doesn't really fit that put that whole let me there's there's what there's some libraries that would be a little more into making it easier for people who develop secure applications either Android or on iOS we're not yeah I know you kind of grab what you get I'm not familiar with any libraries that make your app secure off the top of my head you know you're just
using java eclipse render interviews in Xcode you're you're writing your app yeah and there you go right and and by the way you're including a whole ton of open source probably which has its own right a set of issues as well yeah they don't catch those I believe they do catch things like blacklisted websites and anything they can find in that case but again if a developer makes a bad decision and stores an image to the global camera roll or your you know your your camera roll in general they're not going to fly it they don't know what the users storing right it's sort of it's unknown at that point so these are much harder but for malicious apps that they
can scan and look for you know fingerprints or signatures of now where they will flag those and remove those but not for developer bad decisions I'd say or for instance the crashlytics example where Starbucks was sending the username password you know apples not going to see that or care about you know they don't want they're using the app example right yeah they will not apply that because that's legit it's not a great idea that you certainly couldn't do that so they wouldn't remove that flag a pretty reason yeah how can you test these for these vulnerabilities for example the SAS tools or anything like fall if I cannot test for these like for example your app sending data to several
rack you shouldn't to test the backend server that one's pretty easy actually so basically you can use anything Berg web inspection take your choice right weapon of choice for for web application testing and basically just proxy your app through that tool now awed it right and it's gonna go find sequel Junction process parameter injection what have you for the device itself those molds that you're right that is tougher and that's a much more of an annual process and it is for us to we've written some tools to make that easier so we all we work on all jailbroken or rooted devices that we install the apps on and we have tools so as we're using it we're capturing
information things that are interesting to make it easier but yeah there's no like so those tools you sense all your company custom tools you have correct on the cell device the gathers nothing you son right and you will see the network portion as well with on your own that you can do again if using Berber web inspect or app scan or whatever you'll be intercepting that traffic you can see data going to crash legs or to the target end server and see sensitive information there so those sort of things you can do yourself pretty easily yeah I think we're worried about mostly on the logic flaws right not the security security flaws are easy some of
the SAS tools can find what any of these logic flaws somebody manually has to look at it that's correct that is right a hard part yeah there's no easy solution right
there was they would build different vulnerabilities in each they all came together I have not heard of that one sounds legit though right I do not oh goodness okay go across yep you're capturing network traffic they will install a root certificate for you on the device and I know when the spectra do so when you start a mobile scan for instance a mobile backend scan you just hit a QR code that we show and it will download our certificate and then we can man in the middle in that case and Burke has the same thing I believe that you can install a root certificate on the device to get in the middle writings beginning this one is happening
that still works because when you install the rooster to different bones for instance middle go through that correct yeah and the fingerprint right it could be the finger one correct and then that is tougher there's yeah and that's a good trend it makes our job harder right when you actually pin the host for instance that is validating that you're talking to the right host there's a couple of things about that one is you can disable it from the device if you have a ruiner jailbroken device there's tools out there to disable certain pinning for apps but yet that will read it or jailbroken device for that and the other one is that's really rare that we see
that and it's interesting that they actually pin the cert and the reason for that is because they're QA teams it's a pain in the ass right because for every QA server you have to have another ticket and others don't get developer goes let me help you out I'll just allow any cert and and then they don't put pinning back before they put it in the App Store and so that is a rare case for us that we do see certificates being properly in coming across that you find correct kind of momentum with that all in the application code or configuration itself or with some of that and like failure cupcake when new third-party software is available like
open SSL or something like that so it was actually calling coming in through I don't think we separated based on that that's a good question though so yeah open source will get you for sure I don't think we just parse that out in that in that research just one source and yeah that's it that's a great question well I I would say well it's kind of weird we need you say encryption I mean with our mobile apps were just want like SSL if you're talk about encryption is but I don't know is data storage received it most people don't do anything on top of what the device provides you know so Apple and actually that's pretty good right especially on
Apple where it's actually secured to your user it's encrypted for your user on a device so we don't see too much where people go out of the way to put their own encryption on top of that because that's sort of by default I need that for free so yes
we haven't done any research on that yeah we haven't done research on that but I don't know if I would see a big difference in that other than just once easier to make mistakes you probably believe that if you're working in Xcode and you know objective-c writing that yes so I was doing a research I got a application which was saving its username and password in an encrypted form in the device so what I did is I booked for a vacation and when I was seeing for the logs the application was decrypting that username and password at the run time when we were entering performing any of the transactions in the application so I just wanted to know
about them what scheme they do be added as to be unique high low or medium because the data is properly encrypted and stored and I'd be only able to get when I'm looking down like a choice you're doing like a memory dump of the application together how are you getting the device yes so I just connected it with my laptop I'm doing the rewards injury and checking for the locks any of the runtime screen locks and all what it is doing yeah looking of the function like they weren't a function which was decrypting it at the runtime right like to string and all from other encrypted value to the constraint value and they were writing it unencrypted to the device
after they not to the device but via I was able to hook the function and the function was giving me that yeah if it's just the body should've him yeah it has to be decrypted at some point for the app to use it and that that sounds legit to me I don't I wouldn't see that as a vulnerability I mean I mean look at how would you exploit that right you'd actually have to lose your device somebody have to get into it hook up the tools to inject the functions or to wrap the functions and then use it so you know as far as exploiting that would be really tough I think but again it has to be decrypted
at some point we are stored in the decryption taking the user name will be username and the password in is stored in the device yes and we are decrypting there there is a function which is decrypting that in the device so if I get any of the files where it is being stored like for your I can say like your username and password I get that file from your device I know what algorithm can't I decrypted to the other users I don't think so if you grab it out of the apps sandbox yeah I mean I that should be encrypted if not they're doing something there's an exception and boy if I'm in the application itself right so I can just
provide them your username encrypted it down and try can try to decrypt I don't think I'd have to know more about that scenario
we're hiring by the way we've got like 30 open auditions unreal so we're looking for sales engineers we're looking for developers so also if you guys are looking for something hit me up because so yes that's it [Applause]





